You’ve seen the emails: They claim to have been sent by a financial institution in a faraway land, or from a corrupt bureaucrat in an equally corrupt government. Whatever the ruse, the senders always claim to need your help in spiriting away millions of dollars. These schemes, known as “419,” “advance fee” and “Nigerian letter” scams seemingly have been around forever and are surprisingly effective at duping people. But where in the world do these scammers get their distribution lists, and how did you become a target?
Some of the more prolific spammers rely on bots that crawl millions of Web sites and “scrape” addresses from pages. Others turn to sellers on underground cybercrime forums. Additionally, there are a handful of open-air markets where lists of emails are sold by the millions. If you buy in bulk, you can expect to pay about a penny per 1,000 addresses.
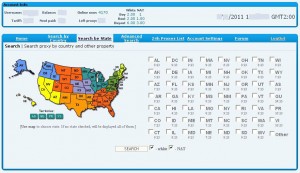
One long-running, open-air bazaar for email addresses is LeadsAndMails.com, which also goes by the name BuyEmails.org. This enterprise is based in New Delhi, India, and advertises its email lists as “100% opt-in and 100 percent legal to use.” I can’t vouch for the company’s claims, but one thing seems clear: Many of its clients are from Nigeria, and many are fraudsters.
 Stretching conspicuously across the middle of the site’s home page is a big green message to the site’s Nigerian clientele: “Don’t waste money/times/resources sending [Western Union or Moneygram], Use local deposit option.” The ad links to a page with a list of payment options, which shows that Nigerian customers can pay for their email lists by wiring the money directly from their bank accounts at several financial institutions in Lagos. BuyEmails.org further advises that, “Due to tremendously high rate of fraudulent payments we do not accept Credit Cards or PayPal. E-Gold has closed, so we don’t accept it either.”
Stretching conspicuously across the middle of the site’s home page is a big green message to the site’s Nigerian clientele: “Don’t waste money/times/resources sending [Western Union or Moneygram], Use local deposit option.” The ad links to a page with a list of payment options, which shows that Nigerian customers can pay for their email lists by wiring the money directly from their bank accounts at several financial institutions in Lagos. BuyEmails.org further advises that, “Due to tremendously high rate of fraudulent payments we do not accept Credit Cards or PayPal. E-Gold has closed, so we don’t accept it either.”
The site sells dozens of country-specific email lists. Other lists are for oddly specific groups. For example, you can buy a list of one million insurance agent emails for $250. 300 beans will let you reach 1.5 million farmers; $400 closes on 4 million real estate agents. Need to recruit a whole mess of money mules right away? No problem: You can buy the email addresses of 6 million prospective work-at-home USA residents for just $99. A list of 1,041,977 USA Seniors (45-70 years old) is selling for $325.