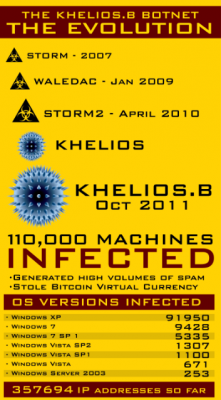
Experts from across the security industry collaborated this week to quarantine more than 110,000 Microsoft Windows PCs that were infected with the Khelios worm, a contagion that forces infected PCs to blast out junk email advertising rogue Internet pharmacies.
Most botnets are relatively fragile: If security experts or law enforcement agencies seize the Internet servers used to control the zombie network, the crime machine eventually implodes. But Khelios (a.k.a. “Kelihos”) was built to withstand such attacks, employing a peer-to-peer structure not unlike that used by popular music and file-sharing sites to avoid takedown by the entertainment industry.
Update, 11:07 a.m. ET: Multiple sources are now reporting that within hours of the Khelios.B takedown, Khelios.C was compiled and launched. It appears to be spreading via Facebook.
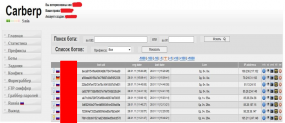
 Original post: The distributed nature of a P2P botnet allows the botmaster to orchestrate its activities by seeding a few machines in the network with encrypted instructions. Those systems then act as a catalyst, relaying the commands from one infected machine to another in rapid succession.
Original post: The distributed nature of a P2P botnet allows the botmaster to orchestrate its activities by seeding a few machines in the network with encrypted instructions. Those systems then act as a catalyst, relaying the commands from one infected machine to another in rapid succession.
P2P botnets can be extremely resilient, but they typically posses a central weakness: They are only as strong as the encryption that scrambles the directives that the botmaster sends to infected machines. In other words, anyone who manages to decipher the computer language needed to talk to the compromised systems can send them new instructions, such as commands to connect to a control server that is beyond the reach of the miscreant(s) who constructed the botnet.
That’s precisely the approach that security researchers used to seize control of Khelios. The caper was pulled off by a motley band of security experts from the Honeynet Project, Kaspersky, SecureWorks, and startup security firm CrowdStrike. The group figured out how to crack the encryption used to control systems infected with Khelios, and then sent a handful of machines new instructions to connect to a Web server that the researchers controlled.
That feat allowed the research team to wrest the botnet from the miscreants who created it, said Adam Meyers, director of intelligence for CrowdStrike. The hijacking of the botnet took only a few minutes, and when it was complete, the team had more than 110,000 PCs reporting to its surrogate control server.
“Once we injected that information in the P2P node, it was essentially propagating everything else for us,” Meyers said. “By taking advantage of the intricacies of the protocol, we were providing the most up-to-date information that all of hosts were spreading.”
The group is now working to notify ISPs where the infected hosts reside, in hopes of cleaning up the bot infestations. Meyers said that, for some unknown reason, the largest single geographic grouping of Khelios-infected systems – 25 percent — were located in Poland. U.S.-based ISPs were home to the second largest contingent of Khelios bots. Meyers said about 80 percent of the Khelios-infected systems they sinkholed were running Windows XP, an increasingly insecure operating system that Microsoft released more than a decade ago. Continue reading