A machine equipment company in Texas is tussling with its bank after organized crooks swiped more than $800,000 in a 48-hour cyber heist late last year. While many companies similarly victimized over the past year have sued their banks for having inadequate security protection, this case is unusual because the bank is preemptively suing the victim.
 Both the victim corporation – Plano based Hillary Machinery Inc. – and the bank, Lubbock based PlainsCapital, agree on this much: In early November, cyber thieves initiated a series of unauthorized wire transfers totaling $801,495 out of Hillary’s account, and PlainsCapital managed to retrieve roughly $600,000 of that money.
Both the victim corporation – Plano based Hillary Machinery Inc. – and the bank, Lubbock based PlainsCapital, agree on this much: In early November, cyber thieves initiated a series of unauthorized wire transfers totaling $801,495 out of Hillary’s account, and PlainsCapital managed to retrieve roughly $600,000 of that money.
PlainsCapital sued Hillary on Dec. 31, 2009, citing a letter from Hillary that demanded repayment for the rest of the money and alleged that the bank failed to employ commercially reasonable security measures. The lawsuit asks the U.S. District Court for the Eastern District of Texas to certify that PlainsCapital’s security was in fact reasonable, and that it processed the wire transfers in good faith. The documents filed with the court allege that the fraudulent transactions were initiated using the defendant’s valid online banking credentials.
Troy Owen, Hillary’s vice president of sales and marketing, doesn’t dispute that the perpetrators stole their online banking credentials, but said Hillary is still investigating how the information was taken. Owen said the transfers appear to have been initiated from computers in Romania and Italy, among others, and sent to accounts in Ukraine, Russia and other Eastern European nations.
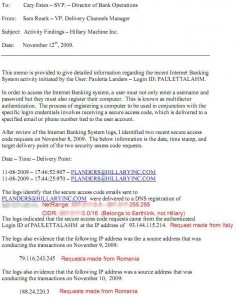 According to a Nov. 12 memo that Owens said PlainsCapital shared with him, the institution’s commercial banking platform requires that each customer not only enter a user name and password, but also “register” their computer’s Internet address by entering a secure access code sent to the e-mail address on file for the customer.
According to a Nov. 12 memo that Owens said PlainsCapital shared with him, the institution’s commercial banking platform requires that each customer not only enter a user name and password, but also “register” their computer’s Internet address by entering a secure access code sent to the e-mail address on file for the customer.
The bank’s memo states that on Nov. 8, secure access code e-mails were sent to a Hillary e-mail address, but that the request came from a computer with an Internet address in Italy. The memo further states that the actual wire transfer requests were made from computers with Internet addresses in Romania.
Owen said no one in his company received any such e-mails on or around the date of the break-in Nov 8th and 9th, and that it is likely whoever stole the company’s banking credentials also intercepted the e-mails.
“It’s pretty ridiculous that the bank is saying their security was reasonable,” Owens said. “The people who run this bank are from an area that still leaves their doors unlocked at night and their keys in the car. These security measures were probably very up to date 10 to 15 years ago, but they’re not in today’s age.”
PlainsCapital declined to discuss the memo or other details of the case, citing the pending litigation. The bank’s president Jerry Schaffner said in an e-mailed statement that “It is evident that the loss incurred by Hillary Machinery, Inc., although regrettable, was not the result of a cyber attack on PlainsCapital Bank.”
Transaction logs shared by Hillary indicate that the majority of the unauthorized transfers were international wires for roughly $100,000 each. But at least $60,000 of the money was sent to more than two dozen money mules, willing or unwitting accomplices in the United States who are often recruited through work-at-home job scams.
A copy of the bank’s complaint against Hillary Machinery is available here (PDF).
Update: Since this blog post ran, the story of Hillary’s fight with Plains Capital has been picked by several mainstream media outlets, including the Dallas Morning News, Forbes, and Fox News.




A good rant on this can be found at
http://radsoft.net/news/20100126,00.shtml
including more information about how the “compromise” was effected (emailing the account credentials to Earthlink in response to a request from a computer in Italy?) and how the fraudulent transfer requests were entered (from Romanian IPs).
I hope Hillary’s lawyers have the good sense to enter discovery motions for all the documentation around the design and operating procedures of Plains’ security systems. They should get some tremendously entertaining reading, and might well induce the bank to rethink their legal strategy based on what would come out in open court if they proceed.
It will certainly be interesting!
What happened to Hillary Machinery, Inc, also happened to a friend of mine. So many similarities, it sounds like the same perpetrators. The bank is a regional TX bank. I am not concerned with assessing blame at this point. I am concerned with protecting my business cash!
Lessons learned, as taught by Secret Service Investigator to my friend during the course of the investigation:
(1) No wireless PERIOD, no smart phone internet banking.
(2) One and only one computer used for internet banking.
(3) No web surfing or email use on dedicated internet banking computer
(4) passwords changed daily and cache, history and cookies all cleared after each session, even if you don’t think there is content to erase.
(5) Robust virus protection geared for networks, with automatic updates EVERY 4 HOURS (SS Agent said having just one company’s security software may not be adequate—yikes!) Another expert on the case reported that protection may not be 100% even if virus definitions are updated every 15 seconds.
(6) Most likely, the wires that were recalled successfully were held up in larger banks which have better security. The wires were were suspicious to them.
(7) Money was transferred over a two-day period during holidays in less-than-$10K amounts so as not to arouse suspicion by receiving banks.
(8) Use firewalls.
(9) Investigator didn’t say it directly, but hinted at using an Apple for internet banking, not a PC.
I’m sure there is more, but this is all I can remember from our conversation. Please add, subtract or append. I just want to be solution not blame-oriented.
Dave
Dave,
In Authentify, Inc.’s view, this problem should be resolved via legislation rather than litigation. Congress needs to extend the protections currently in place for consumer accounts to SMB accounts. We will be bringing this issue to the attention of the House Committee on Financial Services / Subcommittee on Financial Institutions and Consumer Credit this week. Please put me in touch with your friend who was victimized in the same way Hillary Machinery was.
Thanks,
Jim Woodhill
Chairman
Authentify, Inc.
jim.woodhill@authentify.com
Re: Authentify’s Recommendation for More Legislation
That’s all we need. More laws restating what security pro’s see as obvious. In the end you get a detailed list (limited) of methods that will no longer be used by attackers and a plethora of unlisted techiques that won’t be prosecutable.
Holding the customer accountable for their in-house security is as valid a point as holding the bank accountable for their’s.
The real issue I am concerned about is the increased pressure by banks to go completely on-line or face fee increases while at the same time watching these types of crimes proliferate.
> That’s all we need. More laws restating what
> security pro’s see as obvious
Check out Brian’s reporting on S.3898. There is not a word on *how* the banks should stop this new and fast-growing crime. (Note that this is not the bill I would write. But it’s a great example of what happens on the Hill when an industry fails to get out in front of an important problem with a sensible proposal.)
> Holding the customer accountable for their
> in-house security is as valid a point as holding
> the bank accountable for their’s
My view is whom to hold accountable can only legitimately be decided by the elected representatives of the people. The banks *say* they disagree. Note, however, that at the FDIC Symposium on Combating Commercial Payments Fraud on May 11, 2010 in Washington, D.C., the banking industry representative who was most vocal about the righteousness of the banks’ imposing commercial-account online banking funds transfer fraud losses on randomly-unlucky small- and medium-sized enterprises admitted that if the name of the organization that was hit by ZeuS happened to be “Barney Frank for Congress Campaign Fund”, he would make good on *that* loss regardless of its size or who was “really” responsible.
> The real issue I am concerned about is the
> increased pressure by banks to go completely
> on-line or face fee increases while at the same
> time watching these types of crimes proliferate.
Be Very, Very Afraid, then. Check out:
http://www.bankerstuff.com/BankerstuffWebinars/November16WebinarJavelinOnlineBanking/tabid/579/Default.aspx
Javelin Strategy & Research predicts that there are still almost $7 *billion* in banking costs that can be wrung out of the system via moving transactions into cyberspace. Given the revenue losses Sen. Durbin has inflicted on the financial services industry in the Dodd-Frank Act, expect redoubled efforts of the kind you fear. I would just like to see the banks disclose the risks their commercial customers are accepting by moving their banking online.
@Dave:
You list is part of the picture – I might add that few seem to be aware that Microsoft has a free utility called “steady state” that locks the hard drive to ANY changes in files. Ordinary files would have to be stored on another drive or partition. I’m not sure which versions of Windows that it is available. If not available for your version, maybe a look at Faronics would be in order.
You would still want AV and AS solutions in place, in case the present session were somehow compromised. This would entail unlocking the drive at least two times a day, to update the operating system and/or AV/AS utilities. You would not want to do any unnecessary surfing during these updates; and immediately relock the drive afterward.
Some say a Puppy Linux Live CD would be better; your mileage may vary.
The first thing that’s needed (at least helpful) in hacking Plains Capital is a valid user name and password. If you go to http://www.plainscaptial.com, you’ll see that the bank violates one of the “Security 101” rules — the user name and password are sent in the clear! (http, not https). And they claim to have adequate security measures? Are you joking?
If you enter an incorrect password, it gives you an SSL page. But if you entered a correct password the first time, it would be transmitted unencrypted, correct?
Add: small typo in that URL, it should be http://www.plainscapital.com
HAHA retards!
http://www.plainscapital.com/personal-banking/pages/index.aspx
POST /personal-banking/pages/index.aspx HTTP/1.1
Host: http://www.plainscapital.com
Their homepage account login form uses javascript to intercept the http form submit and then submits it securely. However, if javascript is turned off in your browser, the form submits the password in cleartext.
Game over for PlainsCapital.
Could use of Data Loss Prevention tools from Prevensys (http://www.prevensys.com) help to avoid this disaster?
How? The attack came from outside the customers network.
From the banks prospective this looked like a normal transaction as they let it happen 😉
Second vector authentication like http://www.adeptra.com/ would have I’m pretty sure. Unless the bad guys could edit the contact details online 😉
What does everyone here think of using smart cards issued along with other forms of ID (i.e. built into drivers licences) from the states as authentication to secure sites like banks?
Being a native Bubba, for the last 20+ years at least, I would wonder why a business in a major city (Some think Dallas is suburban Plano, but that’s another issue), would do their banking 300 miles away in Lubbock. Within the last 20 years, “Branch Banking” became legal in Texas, it was not before. It’s likely that this is personal, too, in some way. For the record, 200k would get my full attention, but in the words of a recent President, bad blood too would get my “fuller” attention.
In addition, the U.S. District Court for the Eastern District of Texas is the venue of choice for some, shall we say, “novel” torts. Plano is in this District, Lubbock no. The Bank might be thinking the venue is more of an advantage than the PR hit is a disadvantage.
Gartner issued a report on Where Strong Authentication Fails and What You Can Do About it http://www.gartner.com/resources/173100/173132/where_strong_authentication__173132.pdf that contains interesting reccomendations on how to mitigate from these attacks. We need both banks and the security industry to catch up with mitigations for these cybercrime attacks. Also FFIEC need to update the document on guidelines for authentication in the banking environment since thos provisions for MFA are not adequate to mitigate current threats.
According to a statement released by Town of Poughkeepsie Supervisor Pat Myers, Town of Poughkeepsie bank accounts were hacked on January 12, 2010, and four unauthorized transfers totaling $378,000 were made from the TD Bank account and deposited in banks in the Ukraine. These transactions were discovered the next day and the bank was immediately notified of this activity. The police were called in to investigate.
http://www.townofpoughkeepsie.com/supervisor/PressRelease126.pdf. I am not a computer guy just a town tax payer looking into what happened and it there is any recourse. I appreciate your comments.
WRITE YOUR CONGRESSMAN AND BOTH SENATORS. If you would like a sample letter, send me an email at jim.woodhill@authentify.com.
The banks always take the position that these incidents are a “commercial contract” matter. Nonsense. Your town has become the victim of a *crime*. It is axiomatic in political science that what to do about crime is everywhere and always a political question. If somehow, somewhere, a bank can get a judge to agree that under current law it is “commercially reasonable” for them to allow their customers’ money to be stolen, then “current law” will have to be changed.
Update analysis of the PlainsCapital Bank v. Hillary Machinery lawsuit, especially the intriguing public relations dimension: http://bit.ly/public-relations .
Excellent link Benjamin! Seems like a settlement is already in place.
Our congressmen need to look at this, and not only change the liability laws, but help the banks with their security concerns. After all we are supposedly in a “cyber-war” with enemies already. It only makes sense for the government to help the little banks out on the infrastructure and costs on this new security,. if they mandate the requirements.
Consumer’s Union has more or less joined the fray, with political action to improve credit card practices and fraud protection. CU is a BIG lobby, I didn’t hesitate to join, and we now stand together to put pressure on congress and the banking industry as a whole!
On the issue of 2 factor authentication; I am dumbfounded as to why banks cannot offer their customers these technologies, when online gaming companies such as Blizzard Entertainment, creators of the massive multi-player online game World of Warcraft, do so for a nominal fee. Surely people’s real dollars are worth far more than in-game gold.
http://us.blizzard.com/support/article.xml?locale=en_US&articleId=24660
Sadly, 2-factor authentication does not protect against having a resident bot infection in the customer computer, and bots are our current problem.
> Sadly, 2-factor authentication does not protect
> against having a resident bot infection in the
> customer computer, and bots are our current
> problem.
The way I described the situation with respect to cyber-thievery from commercial accounts on the Hill this week is that 2010 is to this new problem as 1996 was to identity theft. We just want to get to 2003 (by which time Congress was Mad As Hell and Was Not Going to Take It Anymore) in fewer than 7 years. We need to because the attackers are “destroying livelihoods”, not just inflicting “temporary inconvenience”.
(In The Fair and Accurate Credit Transactions Act of 2003 (FACTA), Congress did an absolute reversal of the burden of proof in identity theft cases, and specified a 4-working-day maximum for the credit reporting agencies to get a disputed account off one’s file. The equivalent action today would be to extend Federal Reserve Regulation E to commercial accounts, *retroactively* to, say, late 2004 when the “Lopez” incident happened at Bank of America in Miami.)
I am happy to agree that network computing and online banking have a serious malware problem. Indeed, modern malware may have the potential to sink the online banking industry. Nor is replacing lost funds an answer, since losses drive up banking costs for everyone. However, simply requiring some form of 2-factor authentication also does not address the problem, because it generally does not prevent bots from doing their work.
Could there possibly be some form of 2-factor auth that would work? Maybe. But that is what the security vendors used to say (and some probably still do) about ordinary 2-factor. They were wrong, wrong, wrong. Alas, that means you will have to be considerably more forthcoming about technical details beyond the usual broad hints with an implied “trust me” smile. The solution must work.
It seems strange that Microsoft, with about 93 percent of browsing occurring in Windows, does not get more blame for not producing a sufficiently secure product. The question is whether Windows, running on the expected hardware, is fit for the purpose of online banking.
The best solution for those who need secure online banking NOW is to learn to run Puppy Linux from DVD. Start from my article:
http://www.ciphersbyritter.com/COMPSEC/PCBANSQA.HTM
> I am dumbfounded as to why banks
> cannot offer their customers these
> [true 2-factor authentication] technologies
Why World of Warcraft takes identity more seriously than, say, TD Bank does would be a great question to ask the executives of offender banks!
But note that RSA token cards were just beaten at FifthThird Bank. So losses are happening even at banks that complied with the FFIEC’s 2FA guidance (though not with “layers” of defenses, apparently). Mercifully, FifthThird did the right thing and reimbursed the (commercial) customer even though they were not legally required to. (Yet… )
FYI the funds were “restored” to the Town of Poughkeepsie accounts “with the assistance of TD Bank and various law enforcement agencies”. See the official press release dated 3-18-10.
http://www.townofpoughkeepsie.com/supervisor/Restored_Funds.pdf
Good news! Was this helped by Brians publicity? & do you know what changes were made on the banks side to firm up security?
It was somebody’s publicity. From the wording of the press release, I suspect that to get their money back, they had to try to undo some of the harm to TD’s reputation.
Wow. Conducted in meatspace, it would go something like this:
Bank Teller: Hello, how can I help you?
Customer: At this time, I would wish to be withdrawing $100,000.
BT: Ah, well, I’ll need to see some ID…
C: Here is passport.
BT: Uh, sir, the person authorized on this business account is Larry Sanderson, but your passport says you’re Ladislau Sandulescu… are you shhuuuurrrre that you’re allowed to withdraw from this account?
C: [quickly consults Romanian-English dictionary] Most definitely, of it I am certain.
BT: You wouldn’t lie to me, now, would you?
C: No, a truth which is not I would never say!
BT: Uh… well… OK then! [hands over $100K] Anything else I can do for you today, sir?
C: [turns and runs for the door, knocking over several people]
[… several minutes later…]
BT: Nice to see you again sir, how can I help you?
C: At this time, I would wish to be withdrawing $110,000.
I read all this. After having court reported litigation my client’s bank client was involved in, I determined banks are your enemy (in the 70s and 80s). After reading this, my decision to do no internet banking is validated. Isn’t it funny how your bank pressures you into internet banking, oh, how secure it is. And your bank has bought your politicians who should be your line of defense after ye bank.
Face to face is the only way if that can be accomplished. Person-to-person international banking exists, or at least it did when I was doing the court reporting.
I foresee a trend of mama and pappa eschewing all large chains in favor of down-the-street ‘people you know.’ Back to the 40s.
The weakest link will always be the end user. There are numerous phish and botnet type attacks designed specifically to harvest this type of information.
With that said—I am disappointed that more financial institutions do not employ simple technologies such as RSA tokens for their electronic commerce/banking applications–even some of the biggest banks still don’t issue tokens to their retail/business customers. RSA type tokens are commercially available and easily incorporated into applications that require login credentials.
Yet when offered, I still find banking institutions that are reluctant to spend the $10-20 per token that would prevent many of these types of fraudulent transfers when their customer’s login credentials are stolen.
The problem is not a lack of login credentials, tokens or verification. The problem is malware infection, which means a live bot may exist in the customer computer between the user and the bank. Any credentials of any form whatsoever demanded by the bank can be allowed through by the bot, which then has full access to the account. The bot can change the screen display so the user thinks nothing bad has happened. As long as the bot is present, there is no security. And there is no guaranteed way to detect a bot, especially if it has been customized. To avoid existing infections, learn to boot free Puppy Linux from DVD with Firefox and security add-ons.
I had a debit card with a major bank that had my picture on it. It fell out of my pocket, and someone picked it up and immediately charged almost $1000 at a convenience store, where the clerk didn’t bother to compare the picture on the card (or the signature) to the person using the card.
The bank said “tough luck” and would not even investigate the fraud.
Now, at least, to use the card I have to enter in my zip code (and since I have an unusual zip code, this offers me a modicum of security).
As a result, I now insist on choosing a bank that requires PIN numbers for credit cards, just as debit cards work.
Debit cards do not have the legal loss protections of credit cards (although if Obama’s banking reforms pass this may change), and credit cards traditionally don’t have PIN security. So it was hard to find to find a secure credit card.
The only company that supports the consumer is American Express, but since they have high bank fees, many retailers won’t accept them. The hunt for an honest, secure, universally-accepted bank is unending.
Most bank staff cannot comprehend network security. Attempts at enlightening them often proves unfruitful. It often takes auditors to compel banks into action. I still know of banks that won’t use Multi-factor authentication. I know that’s not comprehensive but it’s better than nothing at all. (Why position yourself to be low hanging fruit?)
The problem with Debit cards is that once you provide a PIN to a merchant, you are entrusting the key to unlock your bank account with the merchant’s security. And most merchants are clueless when it comes to anything close to Payment Card Industry security. As an example: in 2007 in Southern California, it was speculated that Office Depot Databases were compromised. Hackers harvested Debit card numbers and corresponding PINs. Wamu, BofA, and Wells Fargo reissued 250,000 debit cards in response. The actual breach was never positively identified.
Everytime you use a Debit card and provide your PIN for a retail transaction, you’ve just entrusted it to the merchant’s network security.
I would suspect that using Debit cards with various retailers also increases your chances of encountering Card Skimmer too. Yet banks issue Debit cards to customers by default. Bank staff doesn’t even know how to issue a simple ATM Card anymore.
Since electronic deposit is quickly becoming the industry standard practice, the business model needs to change because the bad guys are adopting more quickly than the financial institutions and merchants. The “It’s too complex” or “It’s too expensive” is no longer an acceptable excuse.