Comcast, the nation’s largest residential Internet service provider, announced last week that it is expanding an initiative to contact customers whose PCs appear to be infected with a malicious bot program.
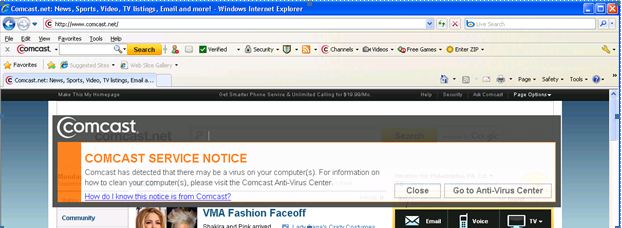
The Philadelphia-based cable Internet company is expanding nationwide a pilot program that began in Denver last year, which automatically informs affected customers with an e-mail urging them to visit the company’s security page. The system also sends the customer’s browser a so-called “service notice,” a semi-transparent banner that overlays a portion of whatever page is being displayed in the user’s Web browser.
Customers can then either move or close the alert, or click Go to Anti-Virus Center, for recommended next-steps, which for Windows customers includes:
- Downloading any missing Microsoft security updates.
- Making sure the customer has some kind of up-to-date anti-virus software running.
- Downloading and running Microsoft’s malicious software removal tool.
- Downloading and installing Secunia‘s free Personal Software Inspector tool, a program that periodically scans the user’s computer for missing security updates for commonly used third party applications, such as Adobe Reader, Flash, and Java, and QuickTime.
Comcast also is offering free subscriptions to Norton Security Suite for up to 7 computers per customer — including Mac versions of the Symantec suite.
For customers who receive a notice but are running a wireless router behind their cable modem, however, figuring out which computer is infected may not be so easy. That’s because while wireless routers plug directly into high-speed Internet modems — and allow multiple computers to use the same Internet address and connection — Comcast’s Constant Guard cannot isolate the infection beyond the Internet address assigned to the customer’s modem. Comcast users who have trouble with that are steered toward the option of paying for help from Norton Live.
Comcast spokesman Charlie Douglas declined to offer statistics on the number of customers who responded to alerts generated during the company’s pilot version of Constant Guard, but said the response has been “very positive.” He said customers who chose to ignore or close the service notice without taking action will be re-notified every few days until the problem is resolved.
Douglas said the bot intelligence is coming from Damballa, an Atlanta-based security company that monitors botnet activity and identifies botnet control networks. If Damballa spots a Comcast Internet address that is phoning home to one of these botnet command centers, Comcast’s system flags that customer’s address for a service notice.
“When we see instructions are being sent from that known evil [Internet address] to one of our customer addresses, we know the instructions from that address cannot be good and that there’s something not good happening on your network,” Douglas said.
Comcast has started rolling the system out on a market-by-market basis, and expects to have it deployed to most of its 16 million customers by the first quarter of 2011, Douglas said.





How does the user distinguish this from the fake AV that’s all over the place?
That was my first question, too. How is a user supposed to distinguish this legitimate notification from a bogus message, especially if there is an embedded link in it? The bad guys are probably already now creating a bogus email from the legitimate one.
Can customers opt out of this type of notification? Or can they at least go to the Comcast website and run the fix from there instead of clicking on a link in an email or popup message?
It’s a legitimate criticism, and there is really no easy answer to it. There is nothing you can do to stop criminals from spoofing your brand, which they’re going to do anyway (phishing emails constantly spoof ISPs). Does that mean this is a bad idea?
It is a good idea and if all it manages to do is get one bot identified and cleaned up it will be worth it.
However, having supported thousands of end-users over the years I can assure you that they are guaranteed to do exactly the wrong thing most of the time.
In this case, they will believe a FakeAV warning and get infected and take one look at this legit warning from Comcast, and confidently dismiss it as a ‘scam’!
I doubt that mistaking that page for a fake alert will be the biggest problem. The biggest problem are IMO the proposed solutions – most of them seem to suggest securing the computer without removing the malware first. Especially the proposed antivirus package should have fairly little effect on a bot infection, this is just a common way for ISPs to earn additional money. I hope that the description in this blog post is misleading and the actual page puts downloading malware removal tools first. Everything else are just good practices once the computer is clean.
Well, at least if the customer keeps getting this warning from Comcast and keeps thinking it is a scam, then won’t they act on that? That is, they will probably have or pay someone look into it and find out what is causing this warning from Comcast to keep popping up?
If legit companies aren’t doing this, we can tell people to ignore security warnings in the browser. How effective is that? Open to debate. But this adds a mandatory level of nuance to the instructions people need to understand to stay safe.
Is that worthwhile? Depends in part on how many Comcast cleans versus how many more are infected.
While your points are true, they are irrelevant to the questions that were asked. You have simply restated what many of us already know.
We also know you are not Comcast’s spokesman, and cannot answer for what they may or may not do, but I think your comments section is better used for (hopefully) constructive dialogs, not platitudes.
I’d rather they provide a single phone number instead of website.
Preferably:
“A computer accessing the internet via this Comcast service appears to be infected by malware. Please call +1 800 COMCAST (1-800-266-2278) for help fixing it.
While a computer is infected, your personal data is probably being stolen, and you will probably be subject to identity theft, possibly have your bank account or credit cards abused.
You should not browse the Internet from any computer which has been connected to this network until you have fixed this problem.”
Something like that. Only one phone number, no links.
Links are bad things. We’ve been trying to teach people *not* to click on links in email — http://krebsonsecurity.com/2010/09/fake-linkedin-invite-leads-to-zeus-trojan/ anyone?
Comcast doesn’t want customers to call them because it costs them money. They especially don’t want to provide anti-malware support, since they don’t have any good way to monetize it.
They do all kinds of crappy tricks, including a surreptitious install of “Desktop Doctor” with every self-install CD or download, to avoid providing phone support for the simplest issues. Providing the phone number instead of a link will never happen.
An ISP that is altering/injecting HTML code into my HTTP requests is invading my privacy (what ever is left of it). I find this completely unacceptable.
If Comcast really wants to inform you, they should send you a snail mail. If that’s too expensive or too inconvenient, then i guess its not that important after all.
I suppose if you do fall for the fake AV scam, then you will get the real notice from Comcast.
Honestly I don’t know how well this will work out in the end. I would like to hope that it will make a dent in the problem, and if it does, other providers might try and emulate it.
Allow me to answer my own question: I think it’s incumbent on ISPs that have the resources to do this kind of notification. To my mind, there are several questions that can’t be answered without more data and more ISPs having tried (and abandoned or continued) this approach. Most importantly, does this type of alert system scale and make financial sense for anything but the largest ISPs?
Some other Q&As.
Is it foolproof? No.
Will the bad guys spoof these notices? Probably, eventually.
Will the scanning tools and whatever else users are asked to download and install to fix a bot problem actually make the customer’s machine completely squeaky clean? Almost certainly not.
I guess my experience is that short of a reinstall, the only way to really clean a machine is with a LiveCD that has some up-to-date AV product installed on it. Malware authors have all sorts of tricks so that they can hide themselves from any running AV products, but if you boot from a CD their counter-measures are ineffective, and the AV programs have a much better chance of success.
Now the question is, can you get a LiveCD all set up so that it is ready to go for your average user? You are already recommending that people use a LiveCD for banking purposes, so the general concept isn’t really that much different. The only thing that is different is what you intend to accomplish once you have the thing up and running.
The LiveCDs that I have used for malware cleanup are all able to update the AV database over the network before a scan, so in theory you shouldn’t have to worry about how stale the CD image actually is.
It doesn’t mean it’s a bad idea for Comcast to try and limit bots on it’s network. But ultimately I think it’s just another attack vector that bad guys will exploit.
I for one think it’s a good idea, might not be a bad idea to throttle the internet bandwidth.
Might get them to call tech support of get someone to look at their computer.
Hi Brian ,
I reckon this will be a major breakthrough in fighting
cyber criminals. By the way few friends of mine from Ukraine asked if you could enlarge the screenshot of the Comcast message – they have trouble with few words and aren’t sure about the grammar 🙂
Cheers
Yuri
Have you tried sending an empty mail with subject: “Do not open it” to see how many follow the instructions ?
That’s pretty funny, Yuri. I’m sure you’re right in some respects.
Sorry for double posting , it is just for the fame you know …
On a serious note , I work for the largest ISP in Israel and we’ve witnessed waves of complains from the end clients that got fake email message from “us” stating that all our password databases were corrupted and they immediately have to change the password , then mail about virus hitting only our clients , I guess list will be updated in future . And in all the cases we became aware of this from clients AFTER they followed the links and compromised their PCs. So we (ISP) actually had to send emails on such outbreaks warning the clients NOT believe any unsolicited mails from us and call Support if any doubts. So my view is that such campaigns are not effective to fight cyber crime but probably do better on PR scale for the company.
Yuri
If Comcast wanted to get serious about limiting bots, they might change their standard practice of connecting customers’ PCs directly to the Internet.
Verizon DSL and FIOS devices usually act as a router, giving connected devices “internal” IP addresses in the 192.168.x.x range. Comcast business Internet also includes a NAT device that assigns 10.1.x.x addresses. Only residential Comcast provides an always-on connection to a public IP address at the customer’s network card.
I’ve installed cable routers for Comcast customers, then checked the device’s log five minutes later… and found Chinese addresses trying to break through to the PC that used to sit at the router’s IP address.
Also, Comcast allows ANY computer to be connected directly to the Web, regardless of age or condition. They simply don’t ask. Imagine how long a Windows 98 machine (yes, they’re still out there) will remain uninfested when jacked directly onto the Internet…
Their job is/was to deliver packets. That’s it. They are not supposed to babysit you.
It’s bad as it is that many ISP have restrictions on what servers you can run (if any), but you want to take that a step further – make private IPs mandatory. It’s not even wrong!
It is completely unacceptable to not give the end user the option to connect his computer directly to the Internet if he wants.
A NAT is not a firewall. A NAT is a gross hack that shares a single public IPv4 address (of which there is a limited supply) among a set of computers with private IP addresses. An unfortunate side effect is that, without special arrangements, computers behind NATs are unable to accept inbound network traffic even if they want to. That’s a bug, not a feature.
The Internet originally became a success because any two computers that wanted to talk to each other with a protocol and application of their own choosing could do so. It was the network’s job to facilitate communication, not to censor or babysit the computers attached to it.
If NATs had been around in the early days of the Internet, you probably never would have heard about it. If people want to cripple their network connections with packet filters, that’s their choice. But like hell will I accept an ISP that forces one on me.
Does anyone have a link to the list of `evil internet address` that they refer to?
If this appears on every web page you visit, it’d be pretty clear that either you’re already infected or it’s comcast telling you you’re already infected.
Absolutely ridiculous. They are injecting shit into your streams. Should be illegal.
Injecting shit! No way! Tell you what. You accept legal responsibility for the spam your infected PC injects into MY stream and then I’ll take your bitching seriously.
His PC isn’t “injecting” anything into anything of yours. If you make your systems reachable by hosts on the Internet, then you don’t get to just decide who can and cannot send you traffic. There’s already a legal responsibility for attacking systems, and otherwise targeting them with malicious traffic, and that legal responsibility rightfully falls on the person committing the crime, not on the owner(s) of the system(s) that it was perpetrated through.
Well, at least they are warning their customers. Better the inconvenience of a pop-up than to lose all the money in your bank account to a Zeus trojan. Also, the fewer bots proliferating on the network, the more bandwidth is available. You can gripe that they aren’t supposed to mess with packets, but firewalls and proxies mangle packets all the time. I certainly wouldn’t mind if they mangled more malicious packets going outbound to Romania, Russia, or China. Good for Comcast for looking after their customers.
Yes, firewalls and proxies do mangle packets all the time. That doesn’t mean it’s right, or that it should be done to an even greater degree.
As bad as firewalls, NATs and proxies may be, at least they don’t modify the application data. Until now. You don’t seem to appreciate the danger in all this.
The network layer of the Internet was designed to be simple and transparent because this promotes flexibility. Anyone could come along and innovate at the edges without having to beg permission from those running the network. And many did — until NATs and firewalls became widespread. Now it’s practically impossible to introduce a new transport protocol into the Internet architecture, at least not without a lot of klugery.
Maybe you don’t care. Maybe UDP and TCP are enough for you. Maybe you don’t even know what “UDP” and “TCP” mean. But then again, not long ago most people couldn’t imagine why they would ever need their own computer, much less a worldwide network designed to allow those computers to talk directly to each other. I mean, why would you ever want to type when you can talk on the phone, right?
This is fairly disgusting. The act of peering into the data payload of customer IP packets is little different from having a postal worker opening letters and reading through them. Injecting data into these packets is little different from handing that postal worker a red pen and instructing him to correct spelling mistakes.
This is the kind of problem that is only susceptible to attacks at the root. Injecting data into customer traffic does nothing but destroy what little trust these customers might have had in Comcast. Monopolies like Comcast must be regulated to protect customer privacy, and inspection and alteration of user data must be strictly prohibited.
I was about to make the same comment – the details of exactly how Comcast sends you that warning matters a VERY great detail.
If they’re sending you a separate message that is read by an application running on your computer designed for that purpose, that’s fine. But if they’re modifying the packets they’re delivering to me from other sites, that is completely unacceptable.
A few years ago a small company in Canada advertised a box that would sit at an ISP and inject advertising into traffic addressed not to them but to their customers. That is exactly like having the Postal Service open your private mail to insert advertising. It just isn’t done. If the ISPs think they have the right to do so, then the answer will be to stop them by encrypting as much traffic as possible with keys they do not have. EFF has helped by providing a Firefox plug-in to encrypt, with SSL, as much of your websurfing traffic as possible.
Some people have funny ideas about what’s acceptable in the US mail. Perhaps you don’t remember the Anthrax scare. I’m sure Brian does. I know I do. http://www.usps.com/news/2001/press/pr01_1106njemp.htm
http://pe.usps.com/text/pub52/welcome.htm
http://pe.usps.com/text/pub52/pub52c3_010.htm
Every hazardous material is assigned to one of nine hazard classes as defined in 49 CFR 172.101 and 173. The nine hazard classes are as follows:
Division 1.1: Mass Explosive Hazard
Prohibited
Prohibited
Prohibited
Roughly speaking, if the USPS thinks you’re sending an explosive hazard through their service, they will /somehow/ peer into it. And they will not deliver it.
I do not want to receive a genuine bomb in my USPS delivered mail. And I believe most people expect essentially the right to safely open their USPS mailbox.
http://pe.usps.com/text/pub52/pub52c3_016.htm
341.2 Mailability, Packaging, and Marking
Explosives are generally prohibited from mailing under 18 U.S.C. 1716. The following conditions apply to the mailing of explosives:
341.21 Nonmailable Explosives
Nonmailable explosives found in the mailstream must be immediately reported in accordance with POM 139.117.
341.22 Mailable Explosives
The following specific types of explosives may be mailed only when the applicable conditions are met. Full responsibility rests with the mailer to comply with DOT and Bureau of Alcohol, Tobacco, and Firearms (ATF) regulations before mailing.
# Each mailpiece containing approved devices must be prepared for mailing following Packaging Instruction 1A in Appendix C. A shipper’s declaration for dangerous goods is required.
http://pe.usps.com/text/pub52/pub52apxc_001.htm#ep100120
http://pe.usps.com/text/pub52/pub52c3_013.htm#ep898574
3.
334.3 Packaging and Marking
Hazardous materials eligible to be shipped under the small quantity provision permitted in 49 CFR and 334.2 must be prepared following Packaging Instruction 10A in Appendix C. Each mailpiece that qualifies to be sent under the small quantity provision must be clearly marked on the address side with the following words: “This package conforms to 49 CFR 173.4.”
How is this relevant?
A computer network delivers bits. Nothing else. Any meaning those bits might have is solely given them by their recipient.
To expand on your example, I can encode the anthrax genome as a bit pattern and send it over a network. But it’s still just a bit pattern. It certainly can’t infect a human being as an actual anthrax spore can. And that’s why it’s perfectly legal to send the genome to an infectious disease over the Internet. The same applies to the chemical formula for, say, cocaine.
Even if a particular bit pattern happens to represent a malicious program in some computer instruction set or source language, it will have absolutely no effect unless a program already running decides to execute those bits as a program. Otherwise they remain merely data. And data certainly can’t force anyone or anything to execute them.
The underlying problem is simple sloppiness on Microsoft’s part. Operating systems and languages that, unlike Windows and many of its applications, maintain a rigorous distinction between “program” and “data” simply don’t have the security problems that have been endemic to Windows for quite a few years now.
I was responding to:
“The act of peering into the data payload of customer IP packets is little different from having a postal worker opening letters and reading through them.”
I skipped over the part about the red pen….
People seem to think they have the right to send dangerous substances (viruses, malware, crimeware, botnet traffic,…) in the electronic world and claim there was a similar right in the world of classic mail. However, it is illegal for people to send dangerous substances through the mail – a law enforced by the USPS (which involves some checking of content).
That was my entire point.
As for whether people are reading packets thoroughly… In the case of the USPS, when white powder spills outside the envelope, they inspect more thoroughly. If the Comcast behavior is similar, then that seems like a reasonable response [1].
It’s probably possible to implement a system which doesn’t really involve much poking into packets (probably just counting packets and ip range and port checks — perhaps done via statistical analysis), and whose method of notification involves:
1. Sending a DHCP Lease Expire (or something like it) — it seems that Comcast tends to provide 1 week leases anyway, which means expiration is pretty easy.
2. Sending a new DHCP Lease where DNS is slightly different.
3. Having the first couple of A record lookups for www.* result in temporary non authoritative responses which trigger a simple redirect to a Comcast server which shows a message (with no user visible content from the originally requested server) — similar to how guest WiFi networks work.
[1] https://www.comcast.com/MediaLibrary/1/1/Customers/Customer_Support/Legal/Acceptable_Use_Policy_for_Internet.pdf
I. Prohibited Uses and Activities
What uses and activities does Comcast prohibit?
In general, the Policy prohibits uses and activities involving the Service that are illegal, infringe
the rights of others, or interfere with or diminish the use and enjoyment of the Service by others.
For example, these prohibited uses and activities include, but are not limited to, using the
Service, Customer Equipment, or the Comcast Equipment, either individually or in combination
with one another, to:
Conduct and information restrictions
• undertake or accomplish any unlawful purpose. This includes, … transmitting … data … in any way constitutes or encourages conduct that would constitute a
criminal offense, or otherwise violate any local, state, federal, or non-U.S. law, order, or
regulation;
…
• transmit unsolicited bulk or commercial messages commonly known as “spam;”
…
• initiate, perpetuate, or in any way participate in any pyramid or other illegal scheme;
• participate in the collection of very large numbers of e-mail addresses, screen names, or other
identifiers of others (without their prior consent), a practice sometimes known as spidering or
harvesting, or participate in the use of software (including “spyware”) designed to facilitate this
activity;
• collect responses from unsolicited bulk messages;
• falsify, alter, or remove message headers;
• falsify references to Comcast or its network, by name or other identifier, in messages;
• impersonate any person or entity, engage in sender address falsification, forge anyone else’s
digital or manual signature, or perform any other similar fraudulent activity (for example,
“phishing”);
You don’t get it.
Physical materials can be inherently harmful. Think explosives, for example. That’s why we have laws against sending them in the mail.
But bits cannot be inherently harmful. Bits are just bits. No computer “worm” or “virus” can have any effect at all unless some computer receiving it as data decides to execute it as a program.
This is not to say I wouldn’t cut off a user who’s deliberately using the net to break into other systems or spread malware. It’d even be okay for an ISP to scan a customer’s incoming traffic PROVIDED that it’s done with that customer’s explicit permission and it can be turned off if the customer doesn’t want it.
But it’s completely unacceptable for an ISP to scan and even modify traffic against the customer’s explicit wishes. And I, for one, will enforce that with encryption if it becomes necessary.
From Comcast’s policy:
“…falsify, alter, or remove message headers; […]
• impersonate any person or entity, engage in sender address falsification, …”
Apparently Comcast sees no problem in doing itself what they prohibit their customers from doing.
I’m sorry, but you’re making an incredibly weak argument. The articles cited prohibiting the shipping of hazardous materials and explosive materials exist to ensure the safe and proper operation of the postal system, and only serves as an ancillary measure in protecting the physical wellbeing recipient.
Thankfully, in all but a few insignificant instances, no threat to a service provider’s infrastructure arises from an exchange of information between two customers. There is also fortunately no threat to the physical wellbeing of a recipient of a spam mail, or any other “bad” traffic that might traverse the last mile.
A point that wasn’t brought up yet: I would guess that at least Zeus is already capable of monitoring and altering web traffic, it is necessary for its primary goal of harvesting banking account data. How long until it will start removing that Comcast message?
Comcast must be sending their customers monthly bills via regular mail already, why not use this as an opportunity to inform users about the infection? Why use the questionable approach of injecting alerts into the web traffic which is bound to cause collateral damage?
All of my utilities in the US were auto-pay. Some utilities on the east coast offered discounts to people who stopped receiving paper bills.
For things like phone service, or bank statements, the number of pages often varies and I think customers are like me in that they ignore all the pages except the one with the bill information (in the cases where they haven’t switched to autopay).
Sometimes there will be a letter with “We’ve changed our terms of service”. Most people ignore those letters too.
My mail here (outside the US) goes into a pile at my entryway which I do not read (it’s generally in a language that I don’t speak).
I think the right approach is:
1. some kind of pervasive Internet based warning (phone number only)
2. ramped bandwidth limiting (start slow, ramp toward choking)
3. actual phone calls to the registered account holder
4. suspension of service
Steps 2 and 4 should result in periodic refunds to the contract holder. This could be in the form of electronic chargebacks or a signature-required check via USPS/FedEx.
I think people are more likely to notice chargebacks and they should notice requests to sign for a package.
The package form should include an explanation of what’s happening, a phone number to call (again, 1 800 COMCAST), the same “Do not use the Internet to contact us” warning that I’ve described earlier and an explanation that Comcast tech support wants to help the customer fix their computers and restore normal service.
Oh, if you want to try an innovative approach for notifying customers….
Some Comcast customers have Cable TV in addition to Internet (bundle discounts). I did.
I don’t think it’s possible with analog cable, but assuming the customer has digital cable (I’m not even sure if you can still get analog these days), I wonder if it’s possible to change the programming for the individual cable tv customer so that all channels show a static Service Interruption Message asking the user to call 1 800 COMCAST.
That would certainly be more annoying, more likely to catch people’s eye, is an out of band message delivery, is a *trusted* message delivery, and might actually work :).
First off, their IDS/IPS is detecting the worm traffic signatures and firing. They aren’t catching everything, just packets that have malicious signatures. It’s the network version of the antivirus on your computer, but it runs all the time. An IDS/IPS is not technically a full blown wiretap. Wiretaps capture everything you do.
They are putting a banner ad up which advertising firms do all the time on web sites. You are worried about Comcast monitoring your traffic when you should be concerned about DHS and the FBI grabbing your traffic. Comcast is required to turn over records they have of you to law enforcement upon written request (Patriot Act). Law enforcement can also tap into your communication using builtin interfaces (https://secure.wikimedia.org/wikipedia/en/wiki/Communications_Assistance_for_Law_Enforcement_Act) via a court order. Comcast could care less what you do so long as you don’t hog their pipes using BitTorrent, and wiretap laws prevent them from snooping on your traffic since you are customers and private citizens.
You have to sign away your right to privacy via a consent to be monitored form in order for them to get around wiretap provisions. Think about these things before you get indignant, or click through a form. If you signed away your right to privacy, you have no one to blame, but yourself.
You seem to be entirely misunderstanding the objections voiced against data injection. The complaints center on the ISP injecting data into packets that are part of an exchange between the customer and a third party elsewhere on the Internet. You can’t cite anything that the third party decides to do with the traffic that they’re sending you as being analogous to an ISP injecting data, because it just isn’t. This is an ISP doing something that an ISP should not be doing.
In addition, merely having to sign a piece of paper with certain provisions to acquire a critical service from a monopolistic provider does not justify any and every action this provider might take. That’s why regulation exists, and regulation is what’s needed to ensure the integrity of the data that is sent to you from other hosts on the Internet.
Well put. Currently your ISP is logging every URL you’re going to as per federal statutes. It also has ready made interfaces for snooping by state and federal authorities, and depending on your district and recent rulings, these interfaces can be used without a warrant. On top of that, all your traffic is being shaped and sniffed by an IPS.
I don’t think most “privacy advocates” understand this. They think they have some kind of backbone to the internet and this policy suddenly adds all this infrastructure and snooping. Err, this stuff is already here. Instead of ISPs looking at IPS reports and shaking their heads, they are empowering the end user by letting them know that they are infected. The net gain here is huge. People will know that they’ve been compromised and potentially save them from identity theft and password sniffers. If anything its irresponsible to not share this information with the customer. Imagine if your doctor ran a bunch of diagnostics on you looking for cancer and found out that you have lyme disease. He needs to tell you you have lyme disease.
I also am not buying the hysterical “ZOMG THE BAD GUYS WILL SPOOF THIS.” They are already spoofing everything, there’s nothing to stop that, but that doesn’t mean we cant implement this strategy.
I never understood why geeks were so against managed networks. Seriously, if you want your own unfettered line then pay for business-class service like I do. Meanwhile, residential is a ghetto because end users have no idea what they are doing. Best to sandbox them a little then have them continue to destroy the internet.
You don’t understand. If an ISP has knowledge that a customer’s machine appears compromised, then by all means it should notify that customer. The question is the MEANS by which it notifies. Calling him up on the phone is perfectly acceptable. So is sending him an email, or adding messages to web pages that Comcast’s own servers generate.
What is NOT acceptable is modifying traffic that was originated by someone else, not Comcast, and is addressed to the user, not Comcast. This violates the basic principles of how the Internet is supposed to work.
Maybe you’re a non-technical person so this seems like a subtle distinction to you. Believe me, it’s not.
As I said, if necessary we can block this with encryption so in the end it will be a moot point. But it would be nice if Comcast would see reason and not make a confrontation necessary.
“they are putting up a banner ad which websites do all the time”
No, there’s a crucial difference. A website that puts up a banner ad does so voluntarily. The originating website either sends the ad, or the appropriate HTML or javascript that references an ad server. No ISP modifies the traffic once it leaves the originating server.
Comcast is apparently intercepting traffic originated by other webservers and modifying it. That’s unprecedented and very dangerous.
Suppose Comcast were to do this to a download of a computer program or media, thereby ruining it? (No doubt they’ll claim to have taken measures against that, but I wouldn’t believe them.)
If an ISP wants to notify me of something, they have plenty of ways to do it that are perfectly OK. Modifying my traffic is not OK.
sounds kinda weak to me, The problem I see is the “close” button. So you are presented with an option to either fix the problem or just close the annoying message and continue on infecting everyone else. A walled garden is a much better solution. It forces the end user to do something and makes sure they aren’t out there infecting others in the meantime. If you don’t know what a walled garden is it is simple…you get redirected to a limited web that allows you to get to the major anti-virus vendors but no where else, till you fix the problem.
To anyone that is up in arms that ISP’s do this you need to realize two things
one – you signed an agreement…yes that long legal section that you probably ignored by just hurrying through and checking the box “i agree” spells out what we can do with the traffic on our backbone
two – some ISP’s take the integrity of there customers traffic seriously. the egg on our face would be huge if somehow, someway some home user sitting out there infected managed to contaminate our equipment…or worse one of our high paying corporate customers. It is bad enough your slowing down everyone’s connectivity as it is.
The last thing to note is that these detection processes do not reconstruct your data so some geek behind a monitor can drool over your photos and conversations. Botnets all exhibit certain behaviors and it is those patterns we are looking for.
Can I prove that your data is not reconstructed…no, but I don’t have to cause you signed an agreement when you opted to use my service to get to the web.
Just because a monopoly *can* take my data apart and modify it doesn’t mean that they should.
Fortunately, we don’t have to beg and plead with them not to do this because a very effective technical defense is available. Unlike laws or regulations, it’s based on laws of mathematics that can’t be ignored.
Encryption.
The most effective encryption protocol for the Internet is called IPSEC (IP Security). It’s the basis of most VPN (Virtual Private Network) implementations. Not only can IPSEC keep the contents of a communication from being read by anyone but the intended recipient, but it can assure the recipient that it actually came from the sender and not spoofed by one of the ISPs along the line. It even protects against the ISP recording real traffic and later playing it back.
Unlike SSL, which only encrypts the application data, IPSEC encrypts everything past the IP header, the only part of each packet that an ISP has a legitimate need to examine (unless the packet is addressed to one of the ISP’s own servers, of course).
By encrypting everything past IP, IPSEC completely thwarts the kind of packet spoofing that Comcast used to sabotage Bit Torrent, for example. It also completely thwarts “deep packet inspection” and the selective blocking of ports and protocols. Basically, IPSEC restores the transparent, end-to-end nature of the Internet that originally made it so flexible and successful.
The best outcome would be for Comcast to release their numbers on a regular basis, providing METRICS that other ISPs can use.
How many users were warned? How many clicked through to the security site? How many clicked through the ‘cleanup’ process? And most important, after X days or weeks, how many of those users were no longer infected?
Obviously the success rate in their trial was high enough to make it worth a full roll-out. Showing that the process can and DOES work would be powerful stuff!
I go thru about 75 gig of log data a day for bots. I use ip lists from zeustracker and others, then compare site names and other strange data to their lists and others for malware info. Many of those IPs have multiple sites hosted on one IP so this is mostly false positive!
I pull down malware samples and use virustotal to confirm my suspicions. So I wonder how many of these I will get and have to waste time explaining to clueless low level techs my setup and ability to pull this malware.
No it aint not windows.
Ole.
I’ve done testing with Damballa (the technology they are using in the background) and the fact is there will be a large number of false positives that come from this.
Comcast is obviously after the cash and have signed some percentage deals with the product it promotes, security is a business and its goal is money.
Symantec get a awesome deal here, a considerable amount of people with continue to pay for Norton AV, which is quite decent TBH.
Such a way of working however, does have negative sides as it pushes security items which are not always needed, it could promote users to install 2 AV programs supposing they already have one. Norton AV might detect something AVAST won’t and the other way around, not to mention FPs and so on..
Besides if you have malware infection and it is comcast who are the ones to let you know about it, the best advice is to format your computer as installing a Norton AV after you are already infected isn’t very productive, in many cases it wont remove the entire malware and since it is installed past detection its not likely detect rootkits, tis just on example.
On top of that I am not in favor of comcast analyzing all my internet traffic so i am glad i am not with comcast.
Looks like Microsoft had a similar idea and has taken it another step up… proposing “health certificates” for your computer which determine how much access you have to the internet…
http://threatpost.com/en_us/blogs/microsoft-proposes-health-certificates-internet-access-100510
I can see pros and cons to both Comcast’s and Microsoft’s ideas… I think it’s well intentioned, but I’m not sure the correct course of action is being taken… however, that may be something time will tell – naturally there’s always going to be push back, even when it is the correct choice. It will be interesting to see where things go with all this…
Ironic, since Microsoft is almost wholly responsible for the network insecurity pandemic in the first place.
Some claim that other operating systems (Mac OSX, Linux, BSD) are largely unaffected only because Microsoft is much more popular.
That’s a myth. While it’s true that any operating system can be configured insecurely, the structure and design of Windows makes it qualitatively worse than the alternatives. It began life as a single-user operating system with no need for security, and it has grown by accretion ever since. OSX, Linux and BSD are all based on UNIX, which was designed from the start as a multi-user operating system with security as a fundamental requirement. While they can all be improved, the fact is that Windows is qualitatively more vulnerable than the others.
Also, most Internet servers run Linux, and as servers with lots of resources they make attractive targets. But they are rarely attacked as successfully as Windows desktops.
“Trash 80’s” for everyone. There, problem solved!
The banner I see on that screen shot looks like it’s on the Comcast home page itself. They aren’t altering anyone else’s content there.
Many Comcast customers don’t choose a different homepage, often because they wouldn’t know how, and those customers may be exactly the ones who need a banner to tell them they have a problem.
Comcast also has plenty of infected bots to work on without having to analyze the content of anyone’s traffic. There are plenty of services that forward abuse reports about problem IPs at no cost to an ISP.
What data injection? As one person pointed out, it’s an ad on http://www.comcast.net telling you that you are possibly infected. They are NOT altering sessions between you and someone else. They are custom tailoring their own web page to your situation as they understand it because malicious packets with your IP address were flagged by their network monitoring software. And it is perfecting legal for them to drop malicious packets going out to another external IP address. They could be held legally liable for damages to another business even if they don’t own the system because it came from their network, and maybe the last IP address seen was one owned by them such as a proxy server. Though such due diligence is seldom done unless they are notified of the abuse by an affected third party.
If they were doing code injection into your data streams, that would be tampering with communications and is illegal under existing wiretap laws.
There are special specific machines that can inspect all your packages when it passes though the comcast servers.
ISPs might have an interest to obtain such a device in order to better use their existing infrastructure. With the packet analyzer comcast(for example) could know which of their users is using P2P and torrent clients and how the connection of clients is being used.
They could decide that your IP is ‘using’ too much of their line with rapidshare and utorrent and lets say you had 20 MB connection. using emule and utorrent 24/7 means your 20 MB connection is constantly being used to its full extent. Most customers are not using their internet in this manner but some do, the ISP will wish to know about those to limit their bandwidth.
A conservative line of thinking might draw this as a good thing, I do not think so as it is not the place of ISPs to educate their clients and try to change their behavior, comcast present it with security as an excuse, as Speaker said they are in this for the money whether its because they don’t want to buy more infrastructure or enjoy revenues from some percentage deal with security vendors they promote.
There is no need for Comcast to peek into my packets merely to see how much traffic I’m sending. They can simply count my packets and bytes. Whether those packets contain Bit Torrent traffic, email, web traffic, or anything else is simply none of their business.
Perhaps they look into packets because they consider some applications, like Bit Torrent, to be less “important” than others. Well, I don’t. It’s up to the user to decide what’s important to him. His ISP’s job is to deliver that traffic subject only to capacity constraints.
An ISP *should* give the user the ability to mark his individual packets by priority, so if the ISP runs into capacity limits it can begin to drop the traffic that the customer – not the ISP – considers least important.
This feature is already in the Internet Protocol as the Type of Service field. I use it to prioritize my outbound traffic for transmission over my relatively slow outbound DSL link. It lets me run Bit Torrent or any other high volume sender without affecting the latency experienced by VoIP, for example.
Unfortunately, most ISPs don’t look at the ToS field set by their customers. That should change, and it would go a long way toward resolving the adversarial relationship between some ISPs and their users.
Comcast do need to know what is in your packages, ill give you a trivial example, using a deep packet analyzer has legal issues but that out of the point now.
Say comcast have 50MB connection to your apartment build, this building has 4 comcast customers, 2 with 5 MB connection and 2 20MB. One of the 20MB is a heavy torrent uploader, 24/7 clogging his 20 MB and when possible programs like utorrent will use more than your contract 20MB, so it will burden the traffic in this building, other clients will call comcast complaining of lag, they do not have to necessarily call but they will suffer some disturbances due to the heavy torrent use of another client who uses the same connection infrastructure.
It is true that you could in theory use the full extent of a 20 MB connection w/o any p2p program, but surely you agree that those programs tend to eventually consume your line and they often run for long periods of time. If the guy in the apartment bellow you is a heavy torrent user you are going to feel this(although you might consider it some temporary lag or so..) and comcast interest is to limit this torrent user or buy more lines, its obvious they rather not spend money…
No, Comcast does *not* need to know what’s in my packets.
Any justification for deep packet inspection based on network loading fails for at least two reasons. First, a packet is a packet; it doesn’t matter whether it contains Bit Torrent or email, each byte places the same load on the network.
Second, as I said there are perfectly good mechanisms for the user to flag their own packets according to their importance. That flag is part of the IP header, the “outside of the envelope” if you want to draw an analogy to the physical mail; there’s no need for an ISP to look inside to find it.
It is up to the network operator to ensure that each user gets the grade of service that was promised to it. Although the Internet is a shared network, it is nonetheless possible to make guarantees about service levels. The ISP is perfectly entitled to drop traffic when necessary to meet its service level commitments to others, but at the same time it is crucial that it not oversell those commitments.
Let’s take your example of a 50 Mb link into an apartment building that’s shared by 4 customers. If the carrier guarantees 10 Mb/s to all 4, then it can obviously meet all those commitments simultaneously, but not if it guarantees 25 Mb/s to all 4.
Bandwidth should be managed and priced by guarantee, not by peak rate or even by actual usage. In other words, if I’m not willing to pay much then I may still get high speeds at off-peak times when the network would otherwise go idle, but not when the network is heavily loaded.
If a carrier arbitrarily limits a customer’s traffic rate even when there’s idle capacity, as many do, that’s an indication of insufficient competition.
In theory what you say is correct they do not promise you any more or less than what you signed for.
But issues like what I described is on the mind of any ISP mangers in the business, they are very aware of how those p2p programs effect the infrastructure but w/o inspecting your packages they can at best suppose what you were doing, if they inspect your traffic they know that it is you *boris* that is causing this with torrent for example. It is not that they promise more than they can manage, it would be retarded of them…it is just that elements of the infrastructure are essentially being exploited by p2p programs in a way that is beneficial to the p2pers, and in some cases due to the way cables are laid in the ground will hurt other users on the same close area.
So while there is not really a need to confirm the use of torrents, the ISPs are aware of this problem and in the case of Comcast here they IMO want to solve this on the way and present it as security campaign against bot-nets, they surely intend to inspect the packages, they have to otherwise they also cannot confirm malicious packages..
Other ISPs are following how comcast manages with this, also the deal with symantec is something of interest to any ISP. Packet inspection is form of spying so there are legal issues here too..
What are you reading to know that this is a non-injected feature exclusive to comcast.net? The story suggests otherwise.
“The system also sends the customer’s browser a so-called “service notice,” a semi-transparent banner that overlays a portion of whatever page is being displayed in the user’s Web browser.”
Kudos to Comcast for trying to be part of the solution and looking out for their customers best interest (even ones that are being negligent in their apathy towards security). Will it be full proof, clearly no. But its another step in the right direction that can not really hurt. Anyone who would fall for a spoof of this service would likely fall for any existing phishing attacks already out there.
I have Comcast and have received their notice. It showed up in Firefox (not on the comcast.net page) on two Macs on our home network. I did my own scanning of the boxes and also monitored router traffic and found nothing. I contacted Comcast and asked them to identify the bot that they saw that led to the notice. They could not and said that it’s probably just a false positive and if I don’t get any more notices then just ignore. I did not get any more notices after that. I hope it was legit but seemed more like an attempt to get me to download the Norton tools.
Rob, I am going to be in a world of hurt real soon. But read this to the bottom to make sure the problem isn’t your machines but maybe is your WAP if you use a wireless rotuer. But the reason for my trouble is that I create filters to filter out this bad Internet stuff and I suspect that Comcast is going to get in my way REAL soon unless they have a way of me calling them and giving them my WAN IP and them turning this filtering stuff off for me:
http://www.HostsFile.org
http://www.SecureMecca.com
Both me and Mike Burgess (MVPHosts) connect to the Internet through Comcast.
I work strictly from Linux and one or another version of BSD. I also have Windows on my systems but use it only for Symantec and SunBelt scanning of files too big to give to VirusTotal. I regularly have to do DNS runs of my “bad” hosts that I am adding / removing. I finally stopped using OpenDNS because it said my machines were “infected”. Just because you do a lot of DNS checks on hosts that are known to be bad does not mean your machine is infected. OTOH, analysis of what bot packets look like does hold some promise. For those thinking Comcast is snooping on you that isn’t what is being done. They are looking for something out of the ordinary like that machine in Slovenia that was pelting me every hour with a worm packet. It did it well over four months when I stopped monitoring the WAN port for several months. My machines are not directly connected to the Internet. I wouldn’t even direct connect a hardened Windows 7 Server to the Internet any more without something in front of it. Ditto for a Linux box. My two machines are set to not even trust each other and NetBios and many other ports are blocked in all directions by my firewall. I just look at the malicious packets hitting my WAN port and adjust accordingly. I don’t even one the once off chance they are able to boomerang them off of my firewall.
So what are these heuristics Comcast are going to use? About 1-1/2 years ago, I all of a sudden had one of my POP email accounts stop functioning. It turns out that somebody complained that I was sending them spam. So Comcast without any proof went into my cable modem and shut down port 25 (SMTP). Fortunately, the other email account allowed me to use port 465 but it is awkward to use an account that was set up to answer questions about the filters being used for general purpose use. I finally found the reason using the email account they set up for me (which I never use). They gave no proof of the spamming but finally opened up port 25. It doesn’t matter now because I have port 25 closed in all directions on my firewall now in case of the odd chance somebody was able to bounce port 25 traffic off of my firewall. The other POP email account now uses another optional port. This summer I moved and Comcast fouled things up. My old email account and access is nowgone. The new one on the service order bill doesn’t work and without those little paper slips in my snail mail box I would not have any idea how much I owe them. I tried autopay once only to have my connection shut down. Thereafter I used that online account access and paid my bills with month by month payments online. Hey, it works. Don’t pay for the current month and the month in advance – they make sure they have at least a niggling $5+ surcharge if you do that. I know that because I have had them in the past and right now I am looking at one for $5.60. The new email account they gave me on the start new service bill doesn’t work so I am going to have to battle with them on the phone for more than an hour tomorrow to try to get access so I can pay the darn bill online again. I am getting tired of driving 15 miles up the road to straighten this out.
What is next? Comcast saying that a site I discovered is bad is bad and blocking me from getting to it so I cannot verify that it is still bad? Some people think us security people have some special arrangement. We have the same avenues of access the rest of you have. In addition to the bad web site black-listing my WAN IP (don’t be a newb and hit anything at the same IP without waiting at least 8 hours for the second go-back) now I will have Comcast throwning up things that get in my way!
Okay Rob, now I can give you a possible reason for your problems since you aren’t doing what I do. I highly doubt your Macintosh machines are infected. OTOH they send out those automatic spy packets back to Apple because it is build into the system. Do you use a wireless router? If you do it is possible that somebody else is using your WAP for their connection with an infected machine. If you do use a wireless router you need to do all of the following.
1. Change the SSID to something other than the default.
2. Shift to using at least WEP but preferably WPA encryption.
3. Stop broadcast of your SSID.
4. If you can, restrict connect access to only the MAC IP addresses of the machines you use on the wireless. Here are some write ups on how to do it:
http://www.SecureMecca.com/public/HomeRouters/
To the person that said, how do you find the IPs? Well, I have them but I just make sure they are all PCs in that block of IPs:
http://www.securemecca.com/Downloads/proxy_en.txt
I find them by pulling malware from the affected PC. Once that happens I try to block all of the PCs in that block of IP addresses if I can find it. Search for Comcast. The 3rd and 4th ones are blocks where I have pulled malware from. My reasoning is simple – PCs should not be in the direct connect server business. Does that get in the way of you playing games with your pal in one of these IP address blocks? Not at all. Just white-list their IP address.
To who ever said that you were surprised how many packets were hitting you, I wouldn’t be. It was really pretty seeing all of those red flags that Symantec’s firewall was throwing up when GandalfTW was direct connected for Comcast’s initial connect. I feel much safer now that I am using Linux (they have AV as well but more for the local scans than any need of malware protection) and have scuttled behind my firewall. So to the person arguing for direct connecting PCs to the Internet you are either an idiot or a cracker and I don’t care which. Crackers would LOVE to have all of these PCs direct connected to the Internet. For heaven’s sakes I don’t even want to be direct connected and I am running Linux most of the time. ARE YOU NUTS?
Oh yes, the US is all digital now for TV. The purpose of those boxes they give you is to convert from digital to analog if that is necessary. But the advice of the status of your machines on the TV would be better than those emergency broadcasts they do every week. I wish they would do the emergency broadcasts every month instead.
But that isn’t Comcast’s fault, it is the US Congress fault.
Damballa’s recent analysis on most botted ISPs has been criticized a lot.
http://www.h-online.com/security/news/item/Damballa-s-analysis-of-botnet-C-C-servers-criticised-1126699.html
I am a comcast user myself and would not opt for a* bot detection* like this with lots false alarms..I guess they owe an apology.
The issue is much more complex than that article indicates it is. CC servers come and go so fast that you wouldn’t believe it. Here are the changes for MalwareDomainList for the 2010-09-21 to 2010-10-19 time period:
824 removed
1626 added
That figure is approximately 40% larger than what they have since I include both http://www.BadDomain.com and BadDomain.com if the threat is at both whereas MDL will frequently only have one. But it indicates both the tremendous volatility and the fact that normally we keep getting more than we lose. I must hasten to add that these numbers are for all malware problem hosts at MDL, not just the CC servers.
An apology from Comcast isn’t what is needed. Damballa needs to admit they had a partial failure and correct it. There is or should be no shame in getting it wrong. There is a shame in deleting the blog entry or Kaspersky stonewalling and not admitting their web-site got corrupted. You cannot improve something without finding out when something is wrong and fixing it. Damballa just started so what they have needs to be refined. I could go into detail on this but it would take infinitely more space than it is worth. Suffice it to say that it is infinitely more complex than that article made it sound. Just remember that the turnover in CC servers is highly volatile. One time about 70% of the CC URLs at the Zeus project were stale when I tested them But even on that you have to be careful because some of the CC servers are phoenix that will come back to life. Some CC servers have the problem URL replaced with a new problem URL and the old URL disappears. But Damballa does need something to verify a honey-net sever and a way of differentiating it from the real thing that is as foolproof as possible. FPs don’t help anybody.
I had somebody write again the other day stupidly thinking that what I had provided was causing them all of their problems. They have been using MS Windows for 10+ years now and they still didn’t know that there are four registry entries named Run and RunOnce for starting things in the registry, one pair in the user registry hive and the other pair in a system registry hive. They also did not know how to locate the Start folder in the All Users areas to remove the Homer Pseudo Web Server. That is not the killer. They were so dumb they thought that Homer was what was doing the blocking. All Homer does is handle the requests that are redirected its way. So I had to point them to the directions to remove the PAC filter:
http://securemecca.blogspot.com/2010/04/deactivate-pac-filter.html
Then I had to give them instructions for how to replace the blocking hosts file with the original and how to remove the Homer.lnk file in the All Users Start folder. All of this was complicated by Microsoft with “Documents and Settings” (thankfully now replaced with what it should have been, “users” in Windows 7), and “Program Files”, which should have been just “programs”. What is it with Microsoft and all of their spaces all over the place?
IOW, we desperately need something like Damballa succesively refined and improved for users who are some times total idiots to provide them with some protection. These people will never figure out just how much at risk they are. Trust me on this one. Some people are really dense. An example is me on the phone with somebody. Me: “Close the window now.” Them: “How do I do that?” Me: “See that X in the upper right hand side of the Window? Click on it.” They had been using Microsoft Windows for 10+ years. Get the picture? There are at least thousands if not millions of other people either as bad as them or not much better.
Oh yes, here are the hosts I have in one of the 1and1 IP blocks in my hosts file:
http://www.SecureMecca.com/public/1And1IPs.txt
Not all of them are in my add.Risk section and I will have to take some time today to verify if all of those in add.Risk still constitute a problem. Unless it is just adware / spyware they are probably okay now. Please remember that I told you this stuff is really volatile. But that person who didn’t know how to close a window after using Microsoft Windows for 10+ years is on Comcast. I would love to send him directions on how to setup Dambala to protect him. At this point we need everything we can get to protect them from themselves.
That Microsoft big-wig that thinks something like Damballa should be mandatory for everybody needs to see this foul up and realize that at least for now the malware problem is primarily a Microsoft Windows problem. Why penalize people using Macintosh or Linux for what is mostly a Microsoft problem? And it would still get in my way to verify if something is bad and keep verifying if it is still bad.
I wish blogs would not be HELPFUL (not) and prepend an “http://” when none was intended. It is just that BadDomain conveys a meaning whereas “example” does not. Yes, I know about RFC 2606. OTOH, I question why somebody would want a domain named BadDomain.
Can someone explain exactly what Comcast is doing? The comments here give me the distinct impression that they monitor your queries to the DNS resolver they provide. Is that correct?
If so, there are two very simple ways to avoid this “helpful” bit of paternalism if, like me, you don’t appreciate it.
The simplest is to not use Comcast’s DNS resolver. Normally, the DHCP (Dynamic Host Configuration Protocol) gives your computer the IP address of a DNS resolver along with an IP address, but you can override this. (If you have a router between your computer and cable modem, the router will usually pass on the DNS resolver it got from DHCP. This can also be overridden.)
What are the alternatives? There are numerous “open” DNS resolvers around the Internet. Some, like OpenDNS sometimes “lie” in their answers, e.g., when you query a nonexistent domain name and are instead pointed to an advertising server. Other open resolvers give correct answers but their owners haven’t explicitly permitted public use beyond their own customers.
That leaves Google, who has explicitly invited everyone on the Internet to use their own DNS resolvers with the easy-to-remember addresses 8.8.8.8 and 8.8.4.4.
Unlike OpenDNS the open Google DNS never “lies”, and in my experience it has been very reliable and fast. They use a variety of techniques to improve performance, such as anycast routing that steers you to the closest of several servers. They’ve also done a fair bit of work to thwart denial of service attacks and DNS cache “poisoning”.
Another alternative is to run your own local DNS resolver. If you run a UNIX-like system (Linux, BSD, Mac OSX) you can easily run BIND, the canonical DNS package.
I have been experimenting with a hybrid of these two techniques: a local BIND server that forwards most requests to Google’s resolver and caches the results. If for some reason Google’s resolver stops responding, BIND automatically takes over and resolves your requests itself. It seems to work pretty well, and I’ve never felt the need to use my own ISP’s (AT&T’s) DNS server.
Phil, rest assured of one thing. Comcast could care less where YOU go if it is safe. They do care where you go or even worse where your machine goes on its own, especially if starts pulling packets from bot CC servers. This is NOT a case of big brother.
They can’t be doing deep packet inspection of your packets. As commendable as looking for ZBot config data flying toward your machine may seem to be there is no standardize file format. Even if it was possible it would be almost impossible to do it this way without slow downs. Multiply looking for it by the millions of machines on Comcast networks and the billions of packets and you can see the problem. We have to reduce that volume of data to only what is pertinent some way and ignore the rest to have any chance of success. That is what all filter schemes do. Basically what you want to look for are packets headed to and from CC servers. The problems in identifying the CC servers are numerous. That is why there are people that specialize in doing this. Believe it or not some of them are working at 1and1, Yahoo, and other places.
1. A filter could look for certain patterns. For example, does the file requested end with a “.bin” extension. Something like Damballa could try to identify all the known acceptable files with that extension but how many things use “config.bin”? So does ZBot along with cfg.bin and others. With my PAC filter I don’t care. I black-list them with a rule:
BadURL_WordEnds[i++] =”\.bin”;
and then white-list my way out of that for the ones that are acceptable for the most prevalent host and depend on users to do the less used ones themselves. Will that work for something like Damballa? No. Besides, this rule only works for ZBot, sort of. What about the other bots and their files? Not only that but the mechanism is on the thing it is supposed to protect which is only desirable insofar as YOU are in the driver’s seat. You have to be smart enough to take the PAC filter and fork it in the direction you want it to go. But it still has a fundamental flaw – it lives on the thing it is trying to protect. Basically this is shoving the protection out to the ends and distributing the load to make it manageable. It doesn’t work. I have less than a 15% success rate. But 15% is better than nothing. But the reason it doesn’t work is nobody uses it but me.
A filter could map out the CC servers and watch for traffic headed to those IP addresses.
2. If you try to use static lists ala the Zeus project they are extremely volatile. It isn’t as bad as some of the stuff I work with where the host comes into existence and leaves the world 4-8 hours later but the life-time of a CC sever is still usually measured in days, not months. The instant a CC server is discovered action is taken by many people in the security community in an attempt to make you safer.
3. You still have to discover the bots somehow. One way is to observe a blip in traffic that is out of the norm going some place it didn’t use to go. Part of that is the use of honey-nets.
4. If there are some well known files and folder names you can use automated testing to discover CCs using that. There is a problem there. Many web service providers like 1and1 troll their space and if they discover a CC service they take it down and put it back up to give you nothing. By that I don’t mean nothing at all – they give you config file back of zero length. Choke on that you nasty little vermin! If you use heuristical methods rather than patterns you need some way of determining whether it is really bad. I did finish my analysis of the few 1and hosts I have and they did have two CC servers (two domains at the end) but they are gone now thus proving 1and1’s statement in a very limited way that they act quickly when they discover a problem:
http://SecureMecca.com/public/1And1IPs.txt
Look at my final statement. This is where Damballa went wrong. Their automated testing identified some hosts as CC servers when in fact they were either sinkholes or were just plain FPs. They could white-list their way out of it but that still leaves the problem of why they were incorrectly identified as CC servers in the first place. If Damballa doesn’t have some people like Thorsten Holz and the others that specialize in this they are going to have to hire them or do some pretty fast-track learning. To err his human but 11% of all CC servers are at 1and1? To really foul up takes a computer that has been given the wrong instructions and a human operator to not oversee it and cross-check it to make sure all is well with the world.
If we can get it to work I would still like my friend who didn’t know how to close a window using it. But with this big of a SNAFU Damballa needs to make a short list of people like Thorsten Holz and others to hire at least on a short term consultant basis to get it on track. If they can’t get any of those people they will need to make a long list and try to get other people to help work on this to get it working right. Disclaimer: I am not on either list.
@Phil Comcast have a list of “bandness” from a supplier and monitor if you try and hit those known bad destinations (Honeypots or otherwise don’t matter if you think about it).
Pete, I’m still confused. *HOW* does Comcast “monitor” me? What’s a “bad” destination? Do they monitor the queries I send to their DNS resolver? Watch my IP destination addresses? Snoop on application layer data? And exactly what do they do if you somehow trip one of these mechanisms?
I think users deserve to be told exactly what is being done and how. This kind of thing must not be done on an ad-hoc and secret basis, and the users ought to have the option to opt out if they don’t want this form of “protection”.
You should find out mate. It’s pretty neat & might save you a few pages of DPI rant too :-p
“To to the person arguing for direct connecting PCs to the Internet you are either an idiot or a cracker and I don’t care which. Crackers would LOVE to have all of these PCs direct connected to the Internet. For heaven’s sakes I don’t even want to be direct connected and I am running Linux most of the time. ARE YOU NUTS?”
I certainly argue for direct connection of PCs to the Internet, and I am neither an idiot nor a cracker.
And I do know what I’m doing.
First of all, I run only Linux and Mac OSX, and that vastly reduces my exposure. (I can fire up Windows under VMWare on the very rare occasion that I need it. That happens maybe once every few months.)
I have run my network without a firewall for many years. I watch them closely, and I have *never* detected a successful break-in.
Oh, but they do try! I see repeated attempts to guess passwords on my SSH server. Even if they were to somehow guess my login name and password they’ll never know it because I’ve disabled plain password authentication. (I use RSA authentication when logging in remotely.)
I see plenty of attempts to connect to Microsoft file sharing on ports 445 and 139. They’re always answered with TCP resets (connection refusals) because I don’t run it.
Less often, I see attempts to connect to other random TCP ports. I don’t know what they are but they’re all answered with resets too.
I generally configure each host with a set of local rules that restrict certain ports to local connections, not because I’m especially concerned about those servers but because I don’t really need to connect to them directly from the outside when I can easily use an encrypted and compressed SSH tunnel and gain the added security and performance that provides.
The fact is that my Linux, BSD or OSX machines are quite able to reject unwanted traffic by returning TCP RST or ICMP destination unreachable messages on their own. They don’t need a so-called “firewall” to do it for them. But when I do want them to accept remote connections to a certain port, I can easily do so — at least on those machines with their own routable IP addresses that aren’t behind the NAT.
That’s the big problem with NAT; without extra hacks there’s simply no way to initiate an external, inbound connection to a computer behind a NAT — even if you want to. People think of a NAT as a “firewall”, but it was never intended for that role. It was intended solely as a stopgap to alleviate the IPv4 address shortage by allowing a network of computers with private addresses to share a single, scarce public IPv4 address.
Once again: a NAT is not a firewall even though it may look like one to the naive. There’s no NAT in IPv6, nor is it needed. By eliminating NAT, IPv6 restores the ability of every computer to talk directly to every other computer on the Internet. And if this makes you concerned about security, the correct answer is either good host security or a packet filtering firewall, not a NAT.
hhhobbit, I must have missed something — where are the searches you’re talking about being done? Are they sniffing customer IP traffic? Crawling through websites looking for nasty-looking data?
I don’t have a big problem with the latter technique, but I do have a big problem with the former. I also have a problem with any ISP that blocks traffic addressed to me unless I have specifically complained about it and asked for it to be blocked.
The intended recipient should always have the last say.