Adobe and Microsoft today separately issued updates to fix critical security vulnerabilities in their products. Adobe pushed out fixes for security issues in Acrobat, Adobe Reader and its Flash Player plugin. Microsoft released seven patches addressing at least a dozen security holes in Windows and other software, although it failed to issue an official patch for a dangerous flaw in its Internet Explorer Web browser that attackers are now actively exploiting.
Two of the patches that Microsoft issued today earned a “critical” rating, signifying that these vulnerabilities could be exploited to fully compromise vulnerable Windows systems without any help from users. Microsoft called special attention to two critical bugs in its XML Core Services component; the company said it is likely that malware or miscreants will figure out a way to exploit these flaws in active attacks sometime within the next 30 days.
Unfortunately, Microsoft did not offer an official fix for a critical Windows flaw that malware and miscreants are already exploiting. In late December, Microsoft acknowledged that attackers were using a previously undocumented security hole in Internet Explorer versions 6 through 8 to break into Windows PCs. Microsoft later issued a stopgap “FixIt” tool to help lessen the vulnerability on affected systems, but researchers last week demonstrated that the FixIt tool only blocked some methods of attacking the flaw, leaving other ways unguarded. Meanwhile, a working copy of the exploit has been folded into Metasploit, a free penetration testing tool.
Wolfgang Kandek, chief technology officer at vulnerability management firm Qualys, said the zero-day IE vulnerability affects 90% of the IE install base at this time.
“Microsoft is not providing a patch today, though they have provided a Fix-It for the issue,” Kandek wrote in a blog post. “The vulnerability should be tracked closely, as a large percentage of enterprises still run the affected versions.”
Users who wish to continue browsing the Web with IE should upgrade to IE9 if possible (IE10 on Windows 8 also is not vulnerable). Users still on Windows XP will not be able to update to IE9, but may be able to derive some protection from the FixIt tool and by using Microsoft’s EMET tool. XP users may be better off, however, browsing with Firefox or Chrome with some type of script blocking and/or sandbox in place. More information on how to use EMET and script blocking options is available in my Tools for a Safer PC primer. More details about today’s updates from Microsoft can be found at the Microsoft Security Response Center blog and in the security bulletin summaries for each patch.
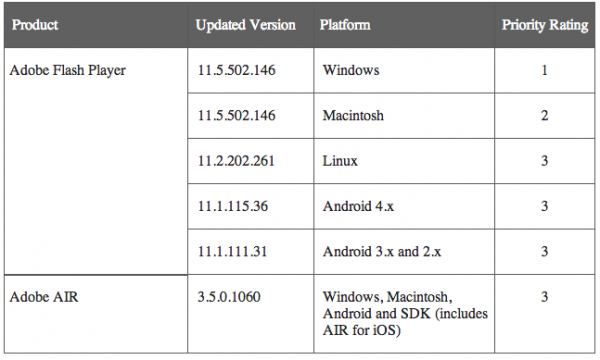
The Adobe Flash patch fixes at least one critical vulnerability in the media player plugin. Updates are available for all supported versions of Flash, including for Windows, Mac, Linux and Android. See the chart below for the latest version number broken down by operating system.
To learn whether you have Flash installed and which version you may have, visit this link. Adobe urges users to grab the latest updates from its Flash Player Download Center, but that option pushes junk add-ons like McAfee VirusScan. Instead, download the appropriate version for your system from Adobe’s Flash Player Distribution page (I long ago stopped waiting for Flash’s auto-updater to kick in). Adobe says that Flash Player installed with Internet Explorer 10 for Windows 8 and Google Chrome should be updated automatically (Chrome shipped a beta update today to address this in Chrome version 24.0.1312.52.
Adobe also issued an update to fix this flaw in its AIR software. The latest version of AIR, v. 3.5.0.1060, is available here.
Finally, Adobe released updates that fix at least 26 security problems in Adobe Acrobat and Adobe Reader. Adobe has released security updates for Adobe Reader and Acrobat XI (11.0.0) and earlier versions for Windows and Macintosh, and Adobe Reader 9.5.1 and earlier 9.x versions for Linux. If you use these products, you’ll want to update them.
As always, if you experience any problems downloading or installing any of these updates, please leave a note about it in the comments below.




Speaking of Firefox version 18 was released today. Has everyone tried the “read out loud feature” in the later versions of Adobe reader? It really worked.
I downloaded the new version of Reader. When I tried to install, I got a saying that the download is “not a valid Win32 application.”
Unfortunately, I had already uninstalled the older version of Reader for a clean install. Any suggestions?
I’ve never had a problem with an Adobe download before.
Hi Elle,
You can visit http://get.adobe.com/reader/ un-tick the box asking to install Google Chrome and download Adobe Reader XI (i.e. 11.0.1). Simply double click the file you downloaded to install Adobe Reader 11.
The error ““not a valid Win32 application” usually means that a 64 bit file is trying to run on a 32 bit version of Windows or the file you downloaded was somehow corrupted.
If you have any further questions or concerns, I would be happy to assist.
Thank you.
You could also try Sumatra, a simpler PDF reader that works well without the Adobe security concerns.
While on the subject of Windows Updates, users of Eset/Nod32 should take a look at this: http://www.wilderssecurity.com/showthread.php?t=332920
Basically there’s an issue with two Windows Updates and Nod32 that causes downloads to be corrupted. People have been waiting for a fix since last September but it seems it’s not in this Patch Tuesday either.
Just a follow up. It seems it may be fixed with this hotfix: http://support.microsoft.com/kb/2789397
My advice to anyone having this issue is to keep following the thread I posted above.
i tried downloading flash player from the adobe distribution page and i was also getting google toolbar and chrome. i canceled the installation. i went back to the distribution page and could not find that i could decline those add-ons. i then went to the flash player website where there was a box i could check that i did not want either of those. please note: i am not a computer expert.
The following mini system works for me.
1. Adobe Flash Player version information.
https://www.adobe.com/software/flash/about/
2. Adobe Flash Player Distribution Downloads. I download the EXE installer. Here is the best part, no junkware is downloaded.
http://www.adobe.com/products/flashplayer/distribution3.html
If you only want the Firefox (Mozilla) plugin then use this link: https://www.mozilla.org/en-US/plugincheck/
3. The Adobe Flash Player Auto-update should update the IE support eventually. Follow this blog for auto-update stories.
I think for the first time ever, my Flash auto-updated, and on the day of the release!
Good morning!
correct me if I should be wrong here, but I would not subscribe to the statement above, that vulnerabilities rated as CRITICAL “could be exploited to fully compromise vulnerable Windows systems without any help from users”.
For most of them in the past (and even for the mentioned MS13-002 one) user action is needed
Hi Claus,
Allow me to correct you.
http://technet.microsoft.com/en-us/security/gg309177.aspx
“Rating: Critical
Definition
A vulnerability whose exploitation could allow code execution without user interaction. These scenarios include self-propagating malware (e.g. network worms), or unavoidable common use scenarios where code execution occurs without warnings or prompts. This could mean browsing to a web page or opening email.
Microsoft recommends that customers apply Critical updates immediately.”
While I don’t use this as my detection system as work, I do suggest my friends/family put https://browsercheck.qualys.com as their default browser page. I find this as a great way to keep a majority of their browser related security risks minimized.
Is it legit? The Qualys® BrowserCheck User Agreement is pretty lengthy.
Brian recommended it some time ago and have past that to a number of others. That Brian recommneded it was good enough for me.
I have had no problems
NB. I just run the scan without installing the plugin.
Brian
Thanks for the update news Brian, particularly the Adobe updates. I always use your pages to check the version and download their updates. I’m missing something if Adobe has an auto-update feature similar to Windows auto-updates. I haven’t seen it yet. I have Windows 7 Professional
Adobe Flash Player Updater is documented here:
http://forums.adobe.com/message/4723788.
Note that there is no browser specific information on this message.
Google Chrome for Windows has not auto updated its built in Flash. Chrome is showing Flash version 11.5.31.5, which is not the latest version. However Chrome say it’s up to date. Not good
SF, you must have overlooked Brian’s sentence noting that “…Chrome has shipped a beta…”, so a production version (including a Flash update) will be coming along directly.
Steve W, thanks, I’d missed Brian’s comment re the Chrome beta update. It’s now 2 days since Adobe released the Flash update, yet Chrome’s production channel has still not been updated, only the beta channel has been updated
I asked Google about the delay, and they just replied now that the production channel version of Chrome has now been updated
http://googlechromereleases.blogspot.com/2013/01/stable-channel-update.html
ALL THIS IS “pakasuhha” to fighting against to cyber crime-pakasuhha,cybercrime-pakkasuhha
so its all nice theater “reptile theater”
and remeber shield have to hands blue and red they are connected with green,so that easy how it is,guy IF the banks really wanna stop the cyber crime they can just make few changes and few rules,thats it….
This came from a reader named Dave:
Issues with Microsoft patches released 01/08/13
Greetings
I have run into a number of issues after applying the Microsoft Tuesday patches that I wanted to share in hopes that it will help others. I do not claim to be a software engineer, but I believe the issues are caused by the multiple .NET Framework patches (5 were released) and how they are layered during installation and reboot
Symptoms –
.NET Framework patches take a long time to install – normal
PC and server reboots take longer than usual – normal, about twice usual boot time
Applications relying on databases fail or show error messages
Microsoft Access
Microsoft SQL Server Express (all versions)
Microsoft SQL Server (all versions)
Exchange Server 2003 through 2010
Outlook cannot connect properly, or no new email, various error messages
The issue is after reboot the above services do not fully restart, or do not start at all.
Fix Method 1 – Try rebooting the server a second time
Fix Method 2 – Go to computer Management | Services and find all the services for Exchange Server and for the databases in the above list – restart the running services, and manually start the automatic start services that failed to start properly
I have already seen this on 5 servers running Server 2003, Server 2008, and Server 2008 R2 and have received over 20 phone calls and emails on these issue from folks needing help, so it’s not just me that is seeing this.
I hope this information helps everyone out – we might all be pretty busy.
I’m really beginning to hate the .NET patches, as I have 3 XP Pro SP3 machines that seem to have regular issues with them. Two of them won’t install the KB2742597 patch from this month (even the downloaded standalone version, which fails to find ‘netfx.msi’), and on the third there are two patches from several months ago which won’t install (KB867460 & KB867461, and likely why that machine wasn’t even offered the most recent one) for the same 0x643 failure code and lack of finding the proper ‘netfx.msi’ file.
I’ve used the netfx cleanup tool to remove everything related to .NET and reinstalled from scratch in the recommended “proper order”, and tried the various Fixit tools recommended by MS in its KB articles and responses in the ‘MS Answers’ online forum, all without success so far. I’m getting really tired of wasting my time with the effort, and simply aren’t using any of those machines for much activity that might expose them to a compromising attack while I work on other things of more immediate importance. Fortunately, neither the Vista or Win7 machines in my office have had any issues with them.
Hi Jim,
I am sorry to hear about the issues you are experiencing. .Net can be very hard to repair reliably.
I can’t think of any further troubleshooting steps for issues with .Net, you have tried everything that I would try.
You should consider re-installing Windows XP if you need the .Net functionality on those PCs, if not uninstall .Net and leave it uninstalled.
This week my 2x XP SP3 PCs each had patches for .Net 2.0 SP2, .Net 3.0 SP2 and .Net 3.5 SP1. All patches installed without issues.
Thank you.
Thanks for the support (and commiseration) about what I’ve attempted in recovering the .NET functionality to install these security updates, and your advice — it’s something I’d almost decided to do but am going to try one other thing first. One of the MS gurus for .NET, Aaron Stebner, has an online blog with a series of running queries from frustrated users in association with various tools and messages he’s posted in relation to .NET problems, and I intend to write up something concise and cogent about the problems and what I’ve already done without success and see if he’ll have any suggestion for something I haven’t yet tried in the way of a fix. If he doesn’t or what he suggests doesn’t work, then I’ll just uninstall all of the .NET versions that aren’t processing a particular security upgrade and be done with it for awhile. One of these 3 machines is a desktop that’s getting replaced soon with a Win7 x64 box, so it will go to the local electronic recycler after everything is transferred and then the old drives nuked/scrubbed of all contents.
Hi JimV,
That’s a really good idea about contacting Aaron Stebner. Please let us know if he is of any assistance to you.
It would be interesting to find out what steps actually resolve these issues. I have encountered them before and have not always been able to solve them.
Thank you.
I have found that Adobe Reader sometimes does not update properly. Version 9.5.2 on one of my XP systems gave the impression of being updated to version 9.5.3 but examining the program files disclosed that version 9.5.2 was still the installed version. The update succeeded on other XP systems. Some are presumably trusting that they have the updated version.
It’s just my personal preference, but there are very few apps for which I grant autoupdate permission on any of my computers, and none of Adobe’s stuff is among them. I use FileHippo to notify me of updates as Brian has long recommended, and for those that I know will want to push an International version (versus English-only or a stub installer) or other partner bloatware that I don’t want, I’ll use the FH notice to go directly to the app vendor’s website and download exactly what I want — for most things, I’ll just download from FH. It’s a very useful app that I’ll certainly endorse.
The XSS vulnerability is still there, I don’t think it is fixed as of 22nd Jan 2013! Spam continues.