A man arrested in Thailand this week on charges of stealing millions from online bank accounts fits the profile of a miscreant nicknamed “bx1,” a hacker fingered by Microsoft as a major operator of botnets powered by the ZeuS banking trojan.
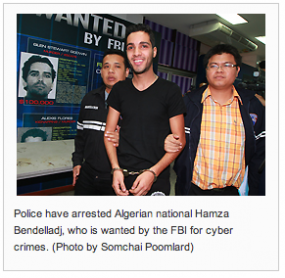
As reported by The Bangkok Post, 24-year-old Hamza Bendelladj, an Algerian national, was detained this weekend at Bangkok’s Suvarnnabhumi airport, as he was in transit from Malaysia to Egypt. This young man captured news media attention when he was brought out in front of Thai television cameras handcuffed but smiling broadly, despite being blamed by the FBI for hacking into customer accounts at 217 financial institutions worldwide.
Thai investigators told reporters that Bendelladj had amassed “huge amounts” in illicit earnings, and that “with just one transaction he could earn 10 to 20 million dollars. He’s been travelling the world flying first class and living a life of luxury.”
I didn’t fully appreciate why I found this case so interesting until I started searching the Internet and my own servers for his email address. Turns out that in 2011, I was contacted via instant message by a hacker who said he was operating botnets using the Zeus and SpyEye Trojans. This individual reached out to me repeatedly over the next year, for no apparent reason except to brag about his exploits. He contacted me via Microsoft’s MSN instant message platform, using the email address daniel.h.b@universityofsutton.com. That account used the alias “Daniel.” I later found out that Daniel also used the nickname bx1.
According to several forums on which bx1 hung out until very recently, the man arrested in Thailand and bx1 were one and the same. A review of the email addresses and other contact information bx1 shared on these forums suggests that bx1 was the 19th and 20th John Doe named in Microsoft’s 2012 legal suit seeking to discover the identities of 39 alleged ZeuS botmasters. From the complaint Microsoft submitted to the U.S. District Court for the Eastern District of Virginia, and posted at Zeuslegalnotice.com:
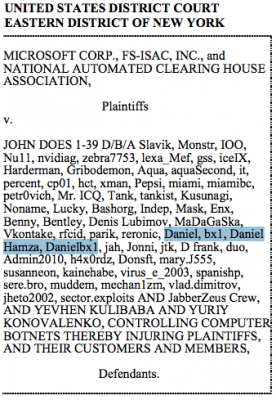 “Plaintiffs are informed and believe and thereupon allege that John Doe 19/20 goes by the aliases “Daniel,” “bx1,” “Daniel Hamza” and “Danielbx1” and may be contacted at messaging email and messaging addresses “565359703,” airlord1988@gmail.com, bx1@hotmail.com, i_amhere@hotmail.fr, daniel.h.b@universityof sutton.com, princedelune@hotmail.fr, bx1_@msn.com, danibx1@hotmail.fr, and danieldelcore@hotmail.com. Upon information and belief, John Doe 19/20 has purchased and used the Zeus/SpyEye code.”
“Plaintiffs are informed and believe and thereupon allege that John Doe 19/20 goes by the aliases “Daniel,” “bx1,” “Daniel Hamza” and “Danielbx1” and may be contacted at messaging email and messaging addresses “565359703,” airlord1988@gmail.com, bx1@hotmail.com, i_amhere@hotmail.fr, daniel.h.b@universityof sutton.com, princedelune@hotmail.fr, bx1_@msn.com, danibx1@hotmail.fr, and danieldelcore@hotmail.com. Upon information and belief, John Doe 19/20 has purchased and used the Zeus/SpyEye code.”
The Daniel I chatted with was proud of his work, and seemed to enjoy describing successful attacks. In one such conversation, dated January 2012, bx1 bragged about breaking into the systems of a hacker who used the nickname “Symlink” and was renowned in the underground for writing complex, custom Web injects for ZeuS and SpyEye users. Specifically, Symlink’s code was designed to automate money transfers out of victim banks to accounts that ZeuS and SpyEye botmasters controlled. Here’s an excerpt from that chat:
(12:31:22 AM) Daniel: if you wanna write up a story
(12:31:34 AM) Daniel: a very perfect
(12:31:34 AM) Daniel: even Interpol will get to you
(12:31:35 AM) Brian Krebs: ?
(12:31:42 AM) Daniel: i hacked the guy who fucked most banks
(12:31:48 AM) Daniel: symlink the guy who made ATS
(12:31:49 AM) Daniel: 🙂
(12:32:02 AM) Daniel: ATS = Auto Transfer System
(12:32:15 AM) Daniel: and get his Backups + Pictures and all his details
(12:32:37 AM) Daniel: Recent Job etc etc
(12:33:06 AM) Brian Krebs: what’s his name?
(12:33:17 AM) Daniel: full name ?
(12:34:03 AM) Brian Krebs: yeah
(12:34:10 AM) Daniel: hmmmm
(12:34:50 AM) Daniel: besliu vasile
(12:35:01 AM) Brian Krebs: what kind of name is that?
(12:35:11 AM) Brian Krebs: romanian?
(12:35:13 AM) Daniel: Moldovian name
(12:35:53 AM) Daniel: he is ugly motherufcka.
(12:36:18 AM) Daniel: after i hacked him he said that i destroyed his life (
(12:36:27 AM) Brian Krebs: aww
(12:36:55 AM) Daniel: yea because i spoke to him
(12:37:10 AM) Daniel: i said how much u pay for ur info to stay private
(12:37:19 AM) Daniel: then he said he destroyed his [hard drive]
(12:37:28 AM) Daniel: i said i dont care i got Backup
(12:37:32 AM) Daniel: it tooks me months to download all
(12:37:48 AM) Daniel: his Previous job..ats..proof video
(12:37:55 AM) Daniel: his picture with Zeus botnet showing up money
(12:38:12 AM) Daniel: his car Plate number
(12:38:17 AM) Daniel: Girls Friends
(12:38:23 AM) Daniel: his workshop. he is mechanic
(12:40:49 AM) Brian Krebs: huh. how come it took you months to [download]?
(12:41:43 AM) Daniel: i waiting for him
(12:41:46 AM) Daniel: if he don’t [pay] then i share just his personel info
(12:41:57 AM) Daniel: and videos that proof 🙂 abt his jobs etc etc
—
It’s not clear whether bx1 had anything to do with it, but according to a lengthy thread on Mazafaka, one of the Underweb’s most exclusive cybercrime forums, Symlink was arrested late last year in Moldova. In a post on Oct. 11, 2012, forum regulars said Symlink had been arrested the day before, and that he got caught because he flaunted his ill-gotten wealth with fancy cars (a fully loaded Land Cruiser 200, valued at more than $100,000) and ostentatious lifestyle choices that were apparently considered far beyond the means of a local auto mechanic. As they do anytime a forum member gets arrested, the forum administrators banned Symlink’s account to distance themselves from the former member.
“Economic police came to symlink yesterday. All computers were seized, one was encrypted and two not, all jabbers at the moment of seizure were online. Ban him temporarily, but better permanently. He was received adultly [meaning, arrested seriously]. Idiot overplayed.”
It’s safe to say that bx1 had his share of enemies, and its possible that Symlink and/or his buddies got the last laugh. According to information obtained by KrebsOnSecurity, attackers recently targeted bx1 in a successful hack to break into his computer, making off with many files, email messages, screenshots and images from his machine.
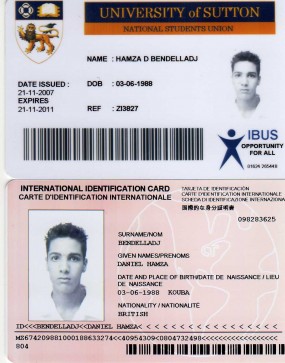 Among them were scanned copies of two identity cards, both bearing the name and likeness of Hamza “Daniel” Bendelladj; one from a “University of Sutton,” and another that appears to be some kind of international ID card. It’s not clear whether these documents are legitimate or manufactured, but probably the latter: the domain attached to bx1’s MSN email address — universityofsutton.com — is registered with the following contact data:
Among them were scanned copies of two identity cards, both bearing the name and likeness of Hamza “Daniel” Bendelladj; one from a “University of Sutton,” and another that appears to be some kind of international ID card. It’s not clear whether these documents are legitimate or manufactured, but probably the latter: the domain attached to bx1’s MSN email address — universityofsutton.com — is registered with the following contact data:
domain: universityofsutton.com owner: Daniel Delcore organization: VIRUS & Malware Scanner email: bx1_@msn.com address: 522 8th street city: Columbus state: IN postal-code: 47201 country: US phone: +1.7573011758 admin-c: CCOM-1611324 bx1_@msn.com tech-c: CCOM-1611324 bx1_@msn.com billing-c: CCOM-1611324 bx1_@msn.com




“Begging for arrest” syndrome? Or just another example of “if they were all that smart, they wouldn’t be criminals”?
” ostentatious lifestyle choices that were apparently considered far beyond the means of a local auto mechanic” They don’t know our local auto mechanics.
Google “University of Sutton” and you get lots of results for fake ID services. Looks like Hamza might have gotten his here:
http://www.fakeidentification.co.uk/fake-id-cards-Student/fake-identification.php
I would just like to point out that Microsoft had nothing to do with this arrest and all the information they got on him came from other sources.
Thanks, but the story doesn’t say Microsoft had anything to do with his arrest. It just states that it appears to be the same guy as Bx1.
Also, I’ve included a link to the whole dust-up over Microsoft’s publication of the online identities of the top alleged Zeus botmasters. But here it is again:
http://krebsonsecurity.com/2012/05/microsoft-to-botmasters-abandon-your-inboxes/
Thanks Brian, hopefully more information on this will be available soon.
BTW, have you talked to the FBI about this? Just curious.
Yes, they declined to comment about the case, except to say that the Thai police’s characterization of Bendelladj as one of the FBI’s most-wanted was not accurate.
Brian,
I know you often ask the FBI for comments; how often does the FBI and other law enforcement organizations come to you for comments about cases you have reported on, and how does that generally go?
Actually, over the past few months, I’ve been contacted by a number of different federal law enforcement folks regarding stories I’ve written. Generally, I don’t mind sharing information that isn’t privileged, but for the most part the government excels at taking information, and is not so good at sharing it back. Consequently, I don’t spend a lot of time talking to federal investigators. The few times I have decided to share information it always resulted in reduced visibility and access for me going forward.
Thanks Brian!
This business they quote of him getting “10-20 million dollars” with “one transaction” is dodgy. I’d like to see any details or evidence that is true. I suspect it’s the usual law enforcement hyperbole because I’ve never heard of any hacking efforts which generate that kind of money from ONE source.
Anyone who can acquire 10-20 million dollars with one hack doesn’t need to hack anymore. They can retire. 🙂
If you look at the below quote from Brian:
“except to say that the Thai police’s characterization of Bendelladj as one of the FBI’s most-wanted was not accurate.”
I think the Thai police blew a lot out of proportion including how much money he was stealing.
“I think the Thai police blew a lot out of proportion including how much money he was stealing.”
As a resident of Thailand I can tell you that the Thai police & media usually does this. But then again, so do many other countries law-enforcement & media aswell.
:/ i think he was a greate guy, he gave me free stuff such as love,friendship and memory’s OSC from there i remember him <3
For me we was not a bad guy…
Another BS story from Mr BS . 20-30 mill per transaction YE Right What ever . In his dreams , maybe .
And FBI’s most-wanted list was not accurate either .
No surprise here some how i knew it .
P.s Yellow press don`t do accurate .They do what ever .
P.S.S say hello to your rat ALEX
YesMan, I think they are doing not just “yellow” exaggeration but that the FBI and banks involved are probably not being entirely honest with Thais when passing travel information along (I bet a whole story there) — performing more “money magic” when calculating damages and adding in security budgets, legal costs, technical prices to reimage entire machines, etc, etc, etc, the way they usually do. Cost to corporation, not profit no doubt sounds more impressive and makes foreign countries happier to cooperate.
I recently read an interview of his brother in an Algerian daily Newspaper. He said that Hamza quit school at junior high school … and he was rarely sitting in front of his PC. Thus, Hamza ( as his brother stated ) didn’t know how to hack.
Don’t know when junior high starts in Algeria, but in the United States it generally starts at age 13. The accused is now 24. A lot can happen in 11 years.
Also, I know many talented hackers who quit or otherwise didn’t fit with school, only to become technically very proficient at computers and other complex subjects.
It might be true. Besides, his brother said that Hamza was adventurous, he was trading, like he buys goods and sells them in Algeria. He wanted to say that Hamza wasn’t that smart guy, nerd or geek. He said that their family lives in poor conditions ( house, job ..etc ) and Hamza wouldn’t wait a second to buy a big house for his family if he had truly so much money. He denied that his brother was a hacker ( this why some might interpret Hamza’s smile as he was astonished by all the media and police for something he didn’t do ) !
i wish they would rewrite that subpoena because mine got dropped and feel like my nickname being slandered when i see that subpoena picture on website which got dropped by microsoft…..ugh
ironic part of it is i am in bangkok also and seen it on news when he got arrested
http://www.zeuslegalnotice.com/images/Dismissal_Doe_36.pdf took me hours of research then m$ tries to sue me then had to spend hours on phone with their lawyers ugh
This is a problem with the “American justice system” that the majority of civilised countries have avoided by not publishing names of accused — combined with the fact that things never go away on the internet (unless the governments decide they should): One never gets one’s name back, and the accusers do not go out of their way to apologise or even point out that they were wrong — if anything they hide it. There are no repairs to one’s reputation to be had.
Nice slogan with little thought behind it. In most countries if you come out from custody, your name may have stayed out of news, but as a cripple for life and with destroyed health, beyond caring about such trivialities. you can spend long time meditating about your luck for keeping your street name pure. Don’t shit in front of a house door and knock to ask for toilet paper without thinking ahead.
Senyavinski,
We are of similar thinking, here, but I would like to point out that there is a difference between being treated as a criminal by the state and being treated as a criminal by the world and every person who might google you, hire you, or date you. Obviously the experience will have long-term repercussions for one’s health and well-being, but there is a difference between repercussions and an impossible to move forward or find any form of human respite — in fact this latter often leads to reoffending. It’s impossible to start over when you’ve already been convicted by the world even if you have not by your peers.
This has nothing to do with me personally other than a matter of personal conviction, but I have known people who have been ruined by this experience of ‘justice’, both innocent and not innocent (as is likely for many people in a world of expanding laws). The problem with the law, especially as practiced by certain world powers, is that both types of people were treated the same *prior to any outcome*, which then extended past the outcome. While being treated the same until an outcome would be good if they were treated as ‘innocent until proven guilty’, I’ve yet to see this be the case, and given the Western practice of ‘plea bargaining’ it never will.
I’ve never seen anyone treated as innocent, or even ‘not guilty’, once acquitted. Has nothing to do with street names — such things are matters of ego — and everything to do with the chance to have a life beyond a street name.
That said the original poster may have perhaps been overreacting as far as ‘street name’ but my comment was more to do with the ‘real names’ that often come up in places like court documents and blogs such as this one (especially where evidence, which is required in a court of law (in theory anyway), is circumstantial at best).
We should not be treating ‘charged people’ or even ‘suspected people’ as ‘convicted people’.