In apparent observation of international trade sanctions against Syria, a U.S. firm that ranks as the world’s fourth-largest domain name registrar has seized hundreds of domains belonging to various Syrian entities, including a prominent Syrian hacker group and sites associated with the regime of Syrian President Bashar al-Assad.

The Syrian Electron Army complains about its domain seizures, saying Network Solutions cited trade sanctions against Syria. Source: HP
Network Solutions LLC. and its parent firm — Jacksonville, Fla. based Web.com — have assumed control over more than 700 domains that were being used mostly for sites hosted in Damascus. The seizures all occurred within a three- to four-day period in mid-April.
The apparently coordinated action ended with each of the site’s registration records being changed to include Web.com’s Florida address, as well as the notation “OFAC Holding.”
OFAC is short for the Office of Foreign Assets Control, an office of the U.S. Treasury Department‘s Under Secretary of the Treasury for Terrorism and Financial Intelligence. OFAC administers and enforces U.S. economic trade sanctions against targeted foreign countries, including Syria.
Web.com declined to say whether it had coordinated the seizures or why it may have done so. “We do not comment publicly about specific accounts so we cannot provide details about the websites or domains mentioned in your inquiry,” the company said in an emailed statement. “However, you should know that we cooperate with law enforcement and regulators in order to prevent illegal activity online and take the necessary steps to be in compliance with applicable laws and regulations.”
Under a series of executive orders, U.S. businesses are prohibited from selling goods and services into Syria. While there are a number of exceptions — referred to as “general licenses” in OFAC-speak — domain hosting and registration services are not among them. Although the general licenses permit services that are designed for personal communications, the provision of Web hosting and domain name registration is specifically called out in Treasury regulations (PDF) as not authorized under general licenses.
A spokesman for the Treasury Department said OFAC had not contacted either Web.com or Network Solutions regarding these Web sites.
“OFAC has offered a general license authorizing the export of certain services for the exchange of personal communications over the Internet, such as instant messaging, chat and email, so that these sanctions don’t have the inadvertent effect of cutting the Syrian people off from the rest of the world,” said John Sullivan, spokesman for the Treasury Department’s Terrorism and Financial Intelligence division. “But the [general license] that allows for that does not authorize the exportation of Web hosting or registration services, so those could be subject to enforcement actions under our Syrian sanctions program.”
The domain seizures came to my attention after reading a report produced last month by HP‘s security and research team, which noted that individuals associated with a pro-Assad hacker group known as Syrian Electronic Army were complaining that NetworkSolutions had seized their domains, including syrian-es.com, syrian-es.net and syrian-es.org.
A reverse WHOIS report ordered from domaintools.com produced this list (PDF) of some 708 Syrian domains recently shuttered and assigned an “OFAC” designation by Web.com. According to historic Web hosting records also maintained by domaintools.com, the vast majority of the 700+ domains were hosted at Internet addresses assigned to the Syrian Computer Society (SCS). Interestingly, prior to assuming the presidency, Syria’s Assad was president of the SCS, a group now widely believed to have been a precursor to the Syrian Electronic Army.
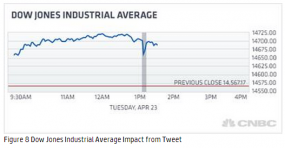
Probably best known for hijacking the Associated Press’s Twitter account and sending the stock markets swooning after posting a fake tweet about a bomb going off at the White House last month, the Syrian Electronic Army uses distributed denial-of-service attacks, phishing scams and other tricks to target dissidents within Syria as well as sympathizers outside the country.
The hacking of the AP’s Twitter account may have been the first widespread exposure for the Syrian Electronic Army, but it has been targeting and successfully compromising other high-profile media outfits for the past two years. As the HP report notes, the SEA took credit for hacking Reuters’ Twitter account in Aug. 2012, and for hijacking various social media accounts belonging to NPR, BBC, CBS, and even organizations that might be more sympathetic to the pro-Assad activists, such as Al-Jazeera, Sky News Arabia and the Qatar Foundation.
WHAC-A-MOLE MARTYRDOM?
According to HP, the SEA is somewhat unique because of the combination of the tactics used in support of their pro-Assad agenda. Past actions by the SEA have involved setting up fake Facebook and Youtube sites in a bid to collect login credentials and spread malware. “When an account has been compromised, it is used to collect information on the user and to distribute pro-Assad messages,” the HP researchers wrote. “For Syrians participating in anti-Assad protest movements this can be dangerous, as it has been alleged that the SEA turns information on these individuals over to the government.”
The HP report details how the SEA’s other social media and propaganda arms on Twitter and Facebook are constantly being shuttered, often for unspecified violations of those sites’ terms of service. Undeterred, the group simply registers another Facebook account with the same name, adding tacking on successive digits to the end of their Facebook account names (its latest account name ends in 207).
Ted Ross, executive technologist at HP’s Office of Advanced Technology, said he worries that all of this Whac-a-Mole activity targeting the Syrian Electronic Army’s various social media properties is creating a digital martyrdom effect.
“We feel like there is this unfortunate side effect of this whac-a-mole game played by Facebook and Twitter,” Ross said. “It impacts SEA’ ability to propagate their propaganda, but you can’t help but wonder what the impact is to the people who are following them and who agree with their motives. This whac-a-mole game almost gives people who are doing this the type of [activity] the legitimacy they seek. When their Facebook page gets disabled, the community rallies behind that.”
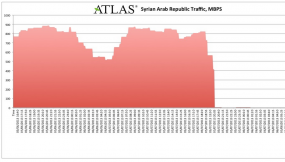
It’s not clear how much hacking the Syrian Electronic Army is going to be doing for the time being. In an abrupt move, Internet access in Syria was taken completely offline by the Syrian government last night. At roughly 18:45 UTC on May 7, nearly all of the Internet paths from Syria were withdrawn from the global routing table, according to Renesys. OpenDNS and Arbor Networks also have more information on this outage.
In the meantime, U.S. hosting providers and domain name registrars should be aware that supporting Syrian businesses and other entities associated with the Syrian government or regime could result in civil enforcement actions from the Treasury Department and potentially hefty fines.
“US companies need to be aware of our sanctions program,” Treasury’s Sullivan said. “A very important part of doing business is that they do not enter into financial transactions with sanctioned parties. And OFAC is very active about pursuing enforcement cases where they need to happen.”




Cool, from now, Syrians will learn IPs instead of domain names to access their websites
Not a problem .We have pleanty of room in RU.SU zone .
your welcome
You wonder after reading this article if the CIA, The Pentagon or the DHS where involved with the take down of the domain names
So does ofac support AL-QAEDA in Syria? We must send this information to CIA and FBI: they must prosecute AL-QAEDA supportes in USA
Not entirely accurate. Domain name registration and hosting for “personal communications” is exempted:
http://www.treasury.gov/resource-center/sanctions/Programs/Documents/syria_gl5.pdf
Way to restate what is already in the article (including the link to that treasury pdf)
“Although the general licenses permit services that are designed for personal communications, the provision of Web hosting and domain name registration is specifically called out in Treasury regulations (PDF) as not authorized under general licenses.”
(b) This section does not authorize:
(1) The direct or indirect exportation of services with knowledge or reason to know that such services are intended for the Govemment of Syria or any other person whose property and interests in property are blocked pursuant to the Orders;
(2) The direct or indirect exportation of Intemet connectivity services or
telecommunications transmission facilities (such as satellite links or dedicated lines);
(3) The direct or indirect exportation of web-hosting services that are for purposes other than personal communications (e.g., web-hosting services for commercial endeavors) or of domain name registration services; or
Then did I misunderstand this sentence?
“While there are a number of exceptions — referred to as “general licenses” in OFAC-speak — domain hosting and registration services are not among them.”
That HP report was a excellent synopsis on the S.E.A. I would highly recommend everyone to read the whole thing
“A spokesman for the Treasury Department said OFAC had not contacted either Web.com or Network Solutions regarding these Web sites.”
If the Treasury Department spokesman is fully aware of what goes on in his department and being honest, then it suggests that Web.com settled on the name “OFAC Holding” on their own. If Web.com discovered these Treasury Department rules by themself, or if they received some external information and/or encouragement, is not clear.
I think this should be illegal.
OK to prevent US business from working with Syrian companies, this is your problem.
However seizing and taking ownership like that just because of US laws should be forbidden by ICANN. ICANN needs to be more independant and more international. They should have allowed those customers to move away and keep control of their domains.
By doing this, US is saying to the whole world: look, the internet is ours, ICANN is ours, deal with it.
This is illegal and immoral thing to do. We should ban all American domains .cos they started that illegal WAR in Iraq .
Web.com is USA part of AL-QAEDA, if you don’t want to support AL-QAEDA IN USA and Syria, close your accounts in WeB.Com
Well that is a good start before the end we all know will come, as aptly explained by THE ONION
http://www.theonion.com/articles/syrian-electronic-army-has-a-little-fun-before-ine,32324/
How about your image and the Syrian domain seizures??
FFS – You have got to be kidding, how is this even legal???
– http://krebsonsecurity.com/2013/05/trade-sanctions-cited-in-hundreds-of-syrian-domain-seizures/
In apparent observation of international trade sanctions against Syria, a U.S. firm that ranks as the world’s fourth-largest domain name registrar has seized hundreds of domains belonging to various Syrian entities, including a prominent Syrian hacker group and sites associated with the regime of Syrian President Bashar al-Assad.
I hope another country seizes everything and anything related to Network Solutions in retaliation (I think Brazil implemented something similar over the laptop searches last year)
The United states needs to wake up to itself and realize if you keep screwing with .com,.net and .org domains then countries around the world might just start routing around you.
I mean seriously folks how as techies can we continue to support the Obama administrations efforts after watching videos like this
-FSA Insurgent Cuts out and Eats Heart of Syrian Soldier – http://on.fb.me/10ntB7a
This is what my taxes are being spent on this week, funding munitions and equipment so this guy can walk around cutting out hearts and eating them??? – all I have to say is….sorry but I’d like a tax refund on the taxes I pay in the USA as you aren’t spending it where I’d like it to go.
Cheers,
Dean
I think NS took this action without getting back to OFAC and they assumed that all domains belong to Syrian entities.
One of the domain owners “daleel-com.com” for example is a company registered in Egypt!!!!
On the other hand, NS changed the status of some of the domains to delete prohibited which means that such domains will never expire and the owners will not be able to register the same name ever.
I think that ICANN needs to be more independant and more international and shouldn’t allow such an action.