Security experts are warning that a newly discovered vulnerability in Internet Explorer 8 is being actively exploited to break into Microsoft Windows systems. Complicating matters further, computer code that can be used to reliably exploit the flaw is now publicly available online.
 In an advisory released May 3, Microsoft said it was investigating reports of a vulnerability in IE8, and that it was aware of attacks that attempt to exploit this bug. The company stresses that other versions of IE — including IE6, 7, 9 and 10 are not affected by the vulnerability. However, all versions of IE8 are vulnerable, including copies running on Windows XP, Vista and Windows 7.
In an advisory released May 3, Microsoft said it was investigating reports of a vulnerability in IE8, and that it was aware of attacks that attempt to exploit this bug. The company stresses that other versions of IE — including IE6, 7, 9 and 10 are not affected by the vulnerability. However, all versions of IE8 are vulnerable, including copies running on Windows XP, Vista and Windows 7.
Meanwhile, a new module that exploits this IE8 bug is now available for the Metasploit Framework, a free penetration testing tool. I would expect this exploit or some version of it will soon be rolled into commercial exploit kits that are sold in the cybercrime underground (assuming this has not already happened).
Update, May 9, 9:00 a.m. ET: Microsoft has released a fix-it tool to blunt attacks on this bug. See this story for more information.
Original post:
The security hole has already been leveraged in at least one high-profile attack. Over the weekend, several security vendors reported that the U.S. Department of Labor Web site had been hacked and seeded with code designed to exploit the flaw and download malicious software.
The attack on the Labor Department site is seen as a watering hole attack, which involves the targeted compromise of legitimate websites thought to be of interest to or frequented by end users who belong to organizations that attackers wish to infiltrate. Previous watering hole attacks have targeted the Web site for the Council on Foreign Relations, the Association of Southeast Asian Nations, and the National Democratic Institute.
According to CrowdStrike, the server used to control this latest attack on the Labor Department site was microsoftupdate.ns1.name. The company said analysis of the logs from the attacker’s infrastructure revealed that visitors from 37 different countries browsed the site during the time it was compromised with the malicious code. AlienVault, Invincea and Cisco Systems have published additional details on this attack. AlienVault also said it has since spotted the same exploit used on at least nine other hacked Web sites, including several non-profit groups and a large European company.
Microsoft is working on an official patch for this bug. What can you do in the meantime to mitigate the threat from this flaw? For now, browsing the Web with another browser is one answer, of course, and it may be more or less advisable depending on which version of Windows you run. For example, Windows XP users can use another browser, and the only other option is rolling and using Internet Explorer 7 until Microsoft fixes this issue (not a great alternative). Windows Vista and Windows 7 users can run Internet Explorer 9, and Windows 7 users can upgrade to IE 10, but should verify compatibility with their applications, as some custom settings may be necessary.
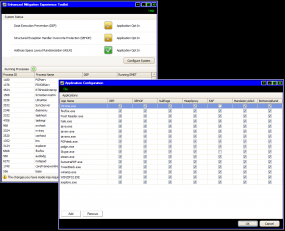
Also, if you use Windows and haven’t taken advantage of Microsoft’s Enhanced Mitigation Experience Toolkit (EMET), now would be an excellent time to check that out. EMET is a free tool from Microsoft that can help Windows users beef up the security of commonly used applications, whether they are made by a third-party vendor or by Microsoft. EMET allows users to force applications to use one or both of two key security defenses built into Windows Vista and Windows 7 — Address Space Layout Randomization (ASLR) and Data Execution Prevention (DEP). Read more about this program at my Tools for a Safer PC primer.




From Microsoft’s advisory (linked in the article):
“Mitigating Factors:
“By default, Internet Explorer on Windows Server 2003, Windows Server 2008, and Windows Server 2008 R2 runs in a restricted mode that is known as Enhanced Security Configuration. This mode mitigates this vulnerability.
Yet again, Microsoft’s ESC mitigates an IE vulnerability. Too bad ESC is only available for Windows server OSs. And while not as convenient and powerful as the NoScript add-on for Firefox, ESC does provide a relatively easy way for users to maintain a whitelist of frequently-visited, legitimate web sites in IEs Trusted Zone.
I wish Microsoft would make ESC optional for IE on its Windows client OSs. If it were to make ESC available, I might actually use IE on my Windows systems.
ESC is a pretty silly hammer. You can emulate its effect by sliding the Internet Zone’s security slider (Tools > Internet Options > Security) to High. Of course, this breaks everything, which is why ESC isn’t used on client systems.
ESC was designed because users shouldn’t be browsing from server systems and by shipping the feature, the count and severity of exploits against server OS would improve. (This was a key competitive metric in the early to mid-2000s)
“You can emulate its effect by sliding the Internet Zone’s security slider (Tools > Internet Options > Security) to High.”
This is what I recommend to anyone who asks me about personal computer security (amoung other things) and to use Firefox or Chrome instead.
Eric Lawrence wrote:
“You can emulate its effect by sliding the Internet Zone’s security slider (Tools > Internet Options > Security) to High.
Well, you can emulate ESC’s IE Internet Zone permissions with this recommendation, but managing a whitelist of frequently-visited, legitimate web sites in IE’s Trusted Zone (where Javascript and plug-ins are allowed to run) is excruciating with IE on Windows client OSs. With ESC, its relatively easy to add a web site to IE’s Trusted Zone.
Internet Explorer, especially on Windows client OSs, is poorly equipped to deal with watering hole attacks where users are redirected to sites under the control of the miscreants where malware is served. The ability to easily maintain a whitelist of frequently-visited, legitimate web sites for which Javascript and plug-ins are allowed to run reduces one’s attack surface considerably. IMO, Microsoft needs to address this deficiency with IE on Windows client OSs.
Agreed, ESC for client versions of Windows would be a useful addition.
Thanks.
Enhanced Mitigation Experience Toolkit v3.5 has been in Tech Preview a very long time… EMET v4.0 Beta is now out. http://www.microsoft.com/en-us/download/details.aspx?id=38761
I guess the official (stable) version is still 3.0, although the blog you linked to talks about 2.0.
MS should promote this tool. I run 3.5 on several machines in a production environment, seems very stable to me. I guess I will try 4 out soon.
Thanks for pointing that out, Matt. Tells me I need to update that and probably do another post about EMET.
Martin Brinkmann published a useful article about EMET v4.0 Beta on 21 April at Ghacks.net — http://www.ghacks.net/2013/04/21/microsoft-releases-enhanced-mitigation-experience-toolkit-emet-4-0-beta/?_m=3n.0038.858.xg0ao03j3r.vu5 .
Hi AJ North,
Thanks for the link to the article on Ghacks.net.
WOW! Version 4.0 huh? It will be a while before I get to navigate to that! I’m still learning the last stable version. I need to try that one on my XP machines, as the malware has learned how to subvert my mitigations on those machines. I can tell XP’s days are numbered with such an obsolete NT5 system, but until it gets canned next year – I’m still with it!
Hi Matt.
According to the following blog post, the final version of EMET 4.0 will be released next week (if all goes according to plan):
http://blogs.technet.com/b/srd/archive/2013/04/18/introducing-emet-v4-beta.aspx
EMET 4.0 resolves all of the known issues with EMET 3.5 Tech Preview.
In my opinion, Microsoft are promoting the tool, e.g. see the following links:
http://www.crn.com/news/security/240153415/microsoft-security-tool-helps-slam-the-door-on-attacks-says-researcher.htm
http://blog.dangerous.net/2013/04/microsofts-emet-40-free-enterprise.html
I have certainly seen a large increase in questions on the EMET support forum in recent weeks (even before the new beta). As a regular contributor on the forum, next week promises to be busy 🙂
Thank you.
According to the following blog post, the final version of EMET 4.0 has been delayed until the 28th of May 2013:
http://blogs.technet.com/b/srd/archive/2013/05/08/emet-4-0-s-certificate-trust-feature.aspx
I hope this helps. Thank you.
Well – I’ll be counting the days till the end of May! 🙂
Well – I will wait with baited breath till the end of May! I use EMET, but will probably never know when it has stopped the bad guys!
I’ve had to disable about half of its protections on IE9 trying to solve an issue with LastPass – I will probably re-enable it entirely soon, as I don’t think that was the problem.
Sorry for the double post – but I was interrupted by a physical security concern! Dang the neighborhood is getting noisy! HA!
Hi JCitizen,
The issue you are experiencing with LastPass is most likely related to the SEHOP mitigation of EMET (specifically the per-process mitigation of EMET, not the system wide mitigation).
There is a known issue with Google Chrome and LastPass that is resolved by disabling the per-process SEHOP mitigation of EMET. In fact, the beta of EMET 4.0 includes this workaround in its default protection profiles so that you don’t have to make this change yourself.
I also describe how to work around this issue with Google Chrome (for an older version of EMET) as well as other related information in the following EMET Support thread:
http://social.technet.microsoft.com/Forums/en-US/emet/thread/d6a8a945-ea55-4970-8b83-f31f4225085b
If you continue to encounter this issue with IE 9 and LastPass, please consider posting a new question/thread on the EMET forum and one of the forum members or myself would be happy to assist you.
I hope this helps. Thank you.
Hi JCitizen,
In relation to knowing if EMET is working and blocking exploits, as you can see from the screenshot in the following blog post, a blocked exploit will show as an error in the Windows Event log:
http://blogs.technet.com/b/srd/archive/2013/05/08/microsoft-quot-fix-it-quot-available-to-mitigate-internet-explorer-8-vulnerability.aspx
I also mention how best make use of the Windows Event log to see EMETs activities in the following thread:
http://social.technet.microsoft.com/Forums/en-US/emet/thread/562e2284-e3ff-4621-a1a6-bc02b5388c12
EMET 4.0 Beta still provides this reporting capabilitie and allows you turn it on/off easily too. This feature is described in detail on pages 14 and 26 of the EMET v4.0 Beta Users Guide PDF.
I hope this helps. Thanks.
Thanks JimboC! I’m beginning to believe it is malware manipulation related – only one restricted account is affected, all other accounts work fine with full settings.
I’m pretty sure it isn’t EMET now, I just need to let LastPass know they are under attack – which will not surprise them at all! 😀
You forgot to mention that Windows 8 users can browse using IE10, as the flaw does not affect Windows 8.
Why would Windows 8 users have IE8 installed? Windows 8 comes with IE10. And the story mentions which Windows versions are affected.
Like, I suspect, a lot of other folks, our enterprise Win7 install includes IE8 to maintain compatibility with certain corporate Web apps. Even though one can now migrate up to IE10 on Win7, as I have at home. Same reason enterprise Web apps still use Java, I suppose.
“If you do what you’ve always done, you’ll get what you’ve always gotten.”
—Tony Robbins
Hey sweetie, it also says IE 6 is not affected, so go with that ;). Are you a link clicker?
emet 3.0 .. ms link: http://www.microsoft.com/en-us/download/details.aspx?id=29851
‘other versions of ie not affected’ — try again ms.
It’s time for more internet users to get their act together and ditch Internet Explorer for good. When more computers start using Firefox and Google Chrome, the the sleeping giant that is Microsoft might actual release better products instead of giving us Windows 8 with those god awful tiles. I’ve never been a huge fan of Internet Explorer because of the Active-X controls
I think we can drop the ‘gi’ here:
Microsoft – the sleeping (support/security/usability/PR/…) ant. 😉
In our dreams John, they will count the hits they get from peeps like me looking for malware lol.
I just downloaded EMET. Glad I checked this post out.
Does anyone know if EMET (v4.0) prevents successful exploitation of this bug?
Hi Some Guy,
As mentioned in both of the links provided below, EMET 3.0 or EMET 4.0 Beta makes exploiting this flaw harder but not impossible.
I would suggest using one or more of the recommendations in the comments of this blog post and/or the suggested actions mentioned in Microsoft’s security advisory until this flaw is patched:
http://technet.microsoft.com/en-us/security/advisory/2847140
http://www.computerworld.com/s/article/9238922/Microsoft_admits_zero_day_bug_in_IE8_pledges_patch
I hope this helps. Thank you.
Hi Some Guy,
I wanted to provide an update to my previous comment. EMET is a very effective protection against this flaw but Microsoft’s new FixIt solution offers better protection than EMET for this flaw:
Here are some more sources that describe this in more detail:
http://blogs.technet.com/b/srd/archive/2013/05/08/microsoft-quot-fix-it-quot-available-to-mitigate-internet-explorer-8-vulnerability.aspx
http://www.cert.org/blogs/certcc/2013/05/keep_calm_and_deploy_emet.html
I would recommend continuing to use EMET with Internet Explorer even when this flaw is patched since EMET can protect against future attacks too. I.e. it’s a great layered defence.
Brian has posted a new article on this FixIt workaround:
http://krebsonsecurity.com/2013/05/a-stopgap-fix-for-the-ie8-zero-day-flaw/
I hope this helps. Thank you.
Prolly doesn’t help IE 9 – just kidding! 🙂
Just installed 4.0 and thought for a minute they removed the “import” feature for xml configurations. Quick search turned up this: http://social.technet.microsoft.com/Forums/en-US/emet/thread/acd338d2-c06c-42f7-97a6-b8ee422f7dde
Luckily they only moved it. A bunch of blog posts about how to setup EMET will have to be updated, as this is a simple but critical step. I personally used a modified all.XML on my systems for 3.5.
Hope this helps someone!
Hi Matt,
Thanks for pointing out my thread that I created when I faced the same issue.
I am also glad that it has assisted you. Many thanks for spreading awareness of this change.
Spam.
Brian,
Local news radio station WTOP has just reported that it has been hosting malware which targets only IE.
http://wtop.com/41/3313012/WTOP-vicitim-of-malicious-cyber-attack
Not clear if it is related or not but seems likely.
From what I can tell, it is unrelated and had to do with a rogue AV attack. See:
http://www.invincea.com/2013/05/k-i-a-wtop-com-fednewsradio-and-dvorak-blog-site-serving-malware-media-sites-compromised-to-push-fake-av/
Yeah I didn’t see that until after I mentioned it hear. My mistake. Keep up the good work Brian.
Unrelated (but needs to be added to Brian’s Safe Computing Guidelines):
http://www.theonion.com/articles/after-checking-your-bank-account-remember-to-log-o,32260/?ref=auto
FYI – Microsoft Security Advisory (2847140) was updated on May 8, 2013 to include one of those little Mr. Goodwrench “Fix It” widgets for users to click on:
http://technet.microsoft.com/en-us/security/advisory/2847140
https://support.microsoft.com/kb/2847140
What kind of way is this to fix a browser flaw? Why don’t they issue a regular patch like they do on Patch Tuesdays (or other times on an urgent basis)? This just seems goofy to me…
Posted this last night:
http://krebsonsecurity.com/2013/05/a-stopgap-fix-for-the-ie8-zero-day-flaw/
I have a hunch that elevating the IE internet zone to high goes further in protecting a system than simply locking down IE. I found that Trend Micro’s RUBotted broke after setting the internet zone to high. This suggests that simply refraining from using IE is not sufficient. The runtime support system for IE should be tied down so that it is made harder for malware to exploit IE runtime support like RUBotted legitimately does. Does this make sense?
I have used Windows XP since 2002 and have yet to experience a single instance of malware climbing aboard and making itself at home. I am definitely not complacent though.
I do however use Puppy Linux (thanks Brian) for such as online banking.
Your hunch would be correct in my opinion, provided you could put up with all the messages and blocking every time you tried to do something. I used to run a honey pot lab, and still do a lot of testing on my own equipment, and even at lower settings IE8 was blocking around 85% of the threat sites and files that we were running into . This got so difficult and time consuming that we switched to opening attachments in emails so that we could bypass the browser and test our other defenses more directly. Even the previously dangerous “zero-day” threats had expired malware in them, and couldn’t get past the various security features of the IE8 browser.
However – I’ve noticed lately on XP that even doing this and running as a restricted user will not save you from very damaging Trojans. They can take advantage of unknown or unpublished vulnerabilities in the XP NT5 system that just can’t thwart their malcode.
I’m talking about fully updated XP Pro installation with all on-board applications fully updated too. Part if it is probably that the application support teams are drawing down dedicated support for Adobe Flash, and Java on such platforms, and the malware may be accessing these with new exploits. I’m afraid XP is in a downward spiral, and I’m now advising my clients who can’t switch hardware to install a good Linux distro like R4U which is considered a good “Replacement for Windows”.
Many of my clients have avoided these issues by installing Spybot Search & Destroy, which despite not being the best measure of an anti-malware, has very good real time passive protections that it institutes in the built in IE browser cookie and site controls. I’ve even been using it myself, now that Lavasoft has become disreputable.
Thanks JCitizen. I appreciate your interesting comments. I believe that you are in effect saying that MS’s withdrawal of security updates for XP after April 2014 is not such bad news since there are already so many unfixed/unknown vulnerabilities.
Thank you for the recommendation of the R4U Linux distro. I have a machine prepped and see Linux as the way forward.
I also like R4U because it has a version at On-Disk that is coded for legacy hardware, for clients that only have maybe 1 or 2 Gbs of RAM and an old CPU.
Thank you for your participation in this discussion! 🙂
ONLY 2GB of Ram?!?!? I used to program computers with 1K. Even the mere thought of 2GB brings on an attack of agoraphobia.
Thanks for the extra info 🙂
If history is any teacher, someday people will lament, “This computer only has 2TB of RAM in it.” 🙂
Back in 1991, I remember people joking that the biggest lie Microsoft told in 1991 was that you could run Windows 3.0 in Enhanced Mode in 1MB of RAM, and that the second biggest lie was that you could run it in 2MB — you really needed 4MB for it to run well!
For legacy users, Windows 3.0 Modes and Memory Requirements is still on their web site, too:
http://support.microsoft.com/kb/58317
My 1983 HP Touchscreen 150 came with a whopping 5mb hard drive and I naively thought I’d never fill up. *cough*
Meant to add that to the best of my recollection, it had 256k RAM.
Thanks for sharing this valuable post with us about IE8.. After reading this post i am very much aware about the security.
Appin Security