If you use Gmail and have ever wondered how much your account might be worth to cyber thieves, have a look at Cloudsweeper, a new service launching this week that tries to price the value of your Gmail address based on the number of retail accounts you have tied to it and the current resale value of those accounts in the underground.
The brainchild of researchers at the University of Illinois at Chicago, Cloudsweeper’s account theft audit tool scans your inbox and presents a breakdown of how many accounts connected to that address an attacker could seize if he gained access to your Gmail. Cloudsweeper then tries to put an aggregate price tag on your inbox, a figure that’s computed by totaling the resale value of other account credentials that crooks can steal if they hijack your email.
In a blog post earlier this month titled The Value of a Hacked Email Account, I noted that many people do not realize how much they have invested in their email account until that account is in the hands of cyber crooks. That post quoted prices from one seller in the cybercrime underground who buys compromised accounts, such as hacked iTunes accounts for $8, or credentials to Groupon.com for $5, for example.
Chris Kanich, assistant professor at UIC’s computer science department and principal organizer of the project, said Cloudsweeper’s pricing model is built on prices collected from multiple sellers across multiple underground forums and services. I ran one of my Gmail accounts through Cloudsweeper, and it determined my account would be worth approximately $28.90 to bad guys. While this is not a Gmail account I use every day, I was surprised at how many third party services I had signed up for using it over the years. According to Cloudsweeper, bad guys with access to my account could also hijack my accounts at Amazon, Apple, Groupon, Hulu, Newegg, Paypal, Skype, UPlay and Yahoo, to name a few.
Cloudsweeper uses the Open Authentication (OAuth2) protocol to connect to your Gmail account and search through messages. OAuth is an open standard for online authorization, and using it with Cloudsweeper does not require you to type in your password as long as you are already logged into the Gmail account that you’d like scanned. Cloudsweeper doesn’t keep your credentials, and it forgets about your visit and inbox after you log out of the service, or within 60 minutes of inactivity.
PLAIN TEXT OFFENDERS
Prior to performing a scan, the service asks users if they wish to participate in a study, which Kanich said gathers and securely stores non-personally identifiable information about Cloudsweeper users who opt-in. That data includes how many types of accounts each user has tied to their Gmail. The study also draws on data from the second core feature of Cloudsweeper: The ability to discover and then redact or encrypt passwords that various services may send to users in plain text.
UIC’s Kanich said the project would like to maintain anonymized statistical information — such as how many accounts and what type — about visitors’ use of the tool.
“So with the user’s expressed permission only, we’ll store stuff like, ‘there was a password that was duplicated in seven different emails and the user chose to redact them all,'” Kanich said. “It’s a little bit funny because you don’t have to give us your password for Cloudsweeper to work, but a big reason you’re coming to us is so we can find your other account credentials.”
Click the blue “Cleartext Password Audit” button from the Cloudsweeper homepage and the service will scour your inbox for passwords that various third-party services may have sent to you in plain text. Cloudsweeper then lists the plaintext passwords alongside the names of the sites that sent them to you, and offers the options to encrypt or redact some or all of the passwords (or to do nothing, of course).
This process works by loading your messages via the Internet Message Access Protocol (IMAP), which lets users edit messages in their inboxes. Using IMAP, Cloudsweeper can redact or encrypt just the plaintext password in any email, leaving the rest of the message intact and untouched. Depending on how many messages you have in your inbox, this process may take quite some time.
Upon encrypting the password(s), the service presents a QR code that you can take a picture of with your mobile phone. You can also copy a longish decryption key and keep it somewhere safe. If you ever wish to un-encrypt the now obfuscated passwords, simply revisit Cloudsweeper and click the orange “Decrypt Messages” button from the homepage. Type or paste in your decryption key, or hold the QR code up to your computer’s Webcam and Cloudsweeper’s site will unscramble your encrypted passwords.
The password redaction/encryption feature is nifty, but it might be more trouble than it’s worth. After all, crooks who gain access to your Gmail account can simply request a new password from the site that sent it in the first place.
“That’s the biggest argument against this: That if you have access to the email account, you can just reset the password anyway,” Kanich said. “Right now, redacting the password is the closest thing to simply deleting the messages [containing plaintext passwords]. A lot of people do want to keep all of their email and don’t want to delete a lot of messages, even those that may have their passwords in them.”
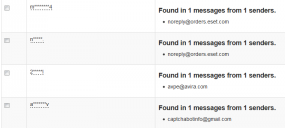
Interestingly, as evidenced by the screenshot above, many of the passwords this tool detected as having been sent to my Gmail inbox in plain text came from antivirus vendors. Storing passwords in plaintext is a security no-no, and these firms should know better. I’ve encouraged readers to name-and-shame companies that perpetuate this practice by forwarding such emails to plaintextoffenders.com, which redacts and publishes these missives each day. Passwordfail.com maintains another list of plaintext offenders, and even has a browser extension to warn users before they register at a site that stores passwords in the clear.
As I noted in several recent posts, Gmail and other Webmail providers — Yahoo! and Hotmail/Live.com — all offer multi-step authentication; if you haven’t already protected your accounts with these features, please take a moment to click the relevant links in this sentence to learn more about how to do that (UIC’s Kanich said his group is looking at adding Yahoo to Cloudsweeper, but that Live.com doesn’t work with IMAP). See this post for a primer on picking and managing strong passwords.
Did you use Cloudsweeper to price your Gmail account? If so, leave a comment below and tell us about your experience.





And… this is why all my email is encrypted.
Bill – question – how do you encrypt auto-sent email from a vendor?
I only understand enrypted email to work between parties that have engaged in some key scheme ahead of time.
[thinking PGP type thing]
23.00 – very enlightening exercise to say the least
My g-mail is worth $0.00! Probably because I have my g-mail setup to automatically forward to my domain owned email address.
Also I try to be very security aware creating completely random passwords for all 50 websites in my LastPass account using 2-step auth wherever possible.
I think programs like LastPass are the way to go for personal account management. The identities feature is fantastic and the two-factor makes for a pretty secure setup.
I always catch a lot of flak from other security professionals for using it though because it’s cloud based. It’s a good example of our selective paranoia in security.
+1 for lastpass
My Gmail is worthless because of the SPAM. Surprise, surprise, surprise.
Why don’t ANY of the major email services have integrated tools to allow us to help disrupt the business models of the spammers? The suckers are relatively scarce, but LOTS of us hate the spam–and then the spam drives all of the rest of it. (Okay, that’s a bit of an exaggeration, because much of the criminal hacking does not depend on spam, but at least the spam is a visible target that could be greatly reduced.)
Or if you think your Gmail does have a positive value, think how much higher that value would be with less spam. If you want to use email to support your business, think how much more valuable your business would be with less spam.
Yes, I hate spam more than the average bear. So give me the tools to hurt the spammers. (And no, I’m not arguing for vigilante lynch mobs against the spammers, though that would be nice. I think the actual triggers of the weapons should remain under professional control–but I desperately want to help with the targeting.)
Gmail is actually pretty well respected for its ability to filter spam. If you’re getting an unusual amount, there could be an explanation. It’s worth learning more about how spammers operate so you can see why you’re getting so much.
There are also things you can do to disrupt spammers if you do want to take action. (See the forum linked by clicking on my username for this post; it is a newb-friendly anti-spam forum.) You probably won’t get any less spam yourself, though, because they’ll just move your address from the list they use to send spam for their sponsors to the list they use for joe-jobs.
Whoo hoo $5.30! Now who do I talk to about cashing in this account?
Send me your password. I can take care of the rest.
(j/k{sort of})
My gmail accounts are worth nothing since they are never given out to anyone or posted online. All of the accounts are behind role email accounts and spam filters that do both white-listing and or black-listing.
Finding my important gmail accounts would be difficult since many are used for POP/IMAP purposes only. Once the email is moved out of Gmail , they are encrypted and in some cases password protected.
Forget the cyber-criminals, Don’t let the N.S.A. read your emails!
Funny – my gmail address is the one I give out to everyone – since google has such a good spam sniffer.
Verizon is useless – allows all sorts of junk in – but if I try to pass any of it along, VZ accuses me of sending spam…………………
I guess VZ doesn’t wonder how the spam got into my VZ account in the first place…………………
Verizon webmail and at&t yahoo don’t even encrypt their pages anymore.(they only encrypt the password page) and yes verizon doesn’t even filter junk mail, but if you called they would tell you not to use their site for mail lol, and at least they have a pop up warning for no encryption, unlike at&t.
Although regular yahoo encrypts everything.
I would recommend using outlook, which is compatible with many 3rd party spam filters. and if necessary, there is a checkbox to keep the email on the servers so you can still open them up on other computers if need be.
I just set my grandpops up with outlook express and Norton antispam and a/v.
$0.00 – No free rent to the creeps!
I also might add , who would give up your email address and password to Cloudsweeper to verify that it’s worth anything. Should a person trust Cloudsweeper with their log-in information?
I wonder what Mr. Krebs gmail account is worth? With all of his cybercrime information, it’s has to be worth a ton of money LOL
Lol I was hesitant to use the site too, but I figured if Brian Krebs used it (and it’s from uic.edu), it’s probably safe.
Yea, so was I! The paranoid security side of me said don’t do it. But the domain, the SSL, and the fact that Brian did it makes me assume it’s okay.
Unless of course this is a massive conspiracy between Cloudsweeper and Brian, and they’re poised to make a few bucks hawking Gmail accounts on the dark side of the net. lol
It is very clearly spelled out, in both Brian’s article and the Cloudsweeper site, that your password is not needed or used.
Try actually *reading* the article before commenting.
Why so sensitive? It was merely meant as a joke. I am aware of what it said.
Just because it’s written that Cloudsweeper “uses the Open Authentication (OAuth2) protocol to connect to your Gmail account and search through messages” doesn’t mean that they have people who work for them that will circumvent their security practices. Who would have thought a person by the last name of Snowden who had a top secret government clearance , would throw the N.S.A. under the bus. Just because it states that Cloudweeper protects users doesn’t mean that what they do is 100 percent secure at at all times. Who’s to say a year down the road , that their servers get breached and then we have yet another security article from Mr Krebs stating ” should internet users have put some much trust in such a service?”
I mean come on people the N.S.A has all your gmail email content at Site M or their new Utah Data center so who’s fooling who here.
Nice write up!
I have 4 account so hackers can get more than 100$.
$15.
$28.30
Two-factor authentication just sets my mind at ease about things like this.
Additionally, I have a mostly-unique password for every site so that the plaintext passwords (which have definitely been emailed to me at some point, but this audit didn’t pick up) aren’t a problem.
However, I also don’t have a single-site point of weakness like a password manager, and here’s how: I just have a stock, super-secure password I use for everything, but I add some characters depending on the site name. Only I know how I determine the modification, but it’s really easy to remember and I don’t ever have any trouble remembering passwords. I think this is the way to go, and I’ve convinced a few of my friends to adopt the same technique. Can you see any problems with the idea?
Seems pretty solid. The harder you make it, the less attractive of a target you become – unless you’re high profile. Most hackers would just move on. There are plenty of people out there with passwords like ‘password’ I would imagine.
That might be an exaggeration, but I’ve seen people use some passwords that are just saying “Over here! Pick me!” and are surprised when their accounts are compromised. *smh*
Old age.
I get around the “old age” thing by having my password generation scheme appended to my last will and testament, sealed and placed in a safe deposit box. That way, if I really have to, I can open that up myself and just get everything re-notarized. And when I die, whoever’s cleaning up my mess will have easy access to all my accounts.
I think we should start a campaign to get Amazon to enable two-factor authentication. They already use it for AWS, and it’d be realllly nice to not give someone free reign if they get access to my account lol.
$5.00
$0.00. Absolutely worthless. Yes!
I had someone send me an email asking for my email address. Granted it’s at a publicly hosted, free service. I reasonably said that I had a friend who works as a valuation expert for internet assets valuated (this friend is a lie) the worth at $25kUSD, and he offered $500USD. Very funny exchange.
Albert, interesting idea but I think it could in some ways be a disimprovement from having totally different passwords for each system you use. For example if two sites were to send your password to you in the clear, and your email was compromised for whatever reason, a perceptive attacker would notice the repeated strings in the two passwords. He could then have a go at all your passwords using the super secret fixed string as prefix and brute-forcing the rest. Unless the unique suffix of additional characters is quite secure in and of itself (complex and 16 characters+) they would be cracked in relatively short order.
Maybe far-fetched but you can see that your fixed password is the weak point, if it is ever compromised, all your accounts will be, this wouldn’t happen with varied secure passwords for all systems.
Brian I use Cableone for my email, they use gmail as their backend mail program. Would this be the same or does it need to be @gmail.com?
A paltry 8.00 for all my stuff using gmail, on an account that is used everyday for personal email.
For those of you scoffing at the perceived low value of your inboxes ($8, $13, $20, e.g.), consider that the type of individuals most likely to have access to your inbox are criminal hackers who control huge botnets of hundreds or thousands of computers. Now do the math.
$20
After the exercise I put in two factor authorization on GMail.
$13.00 Not completely worthless…
Cloudsweeper is useful, but not as useful as it appears. I get that having ANY emails from Amazon.com could expose *some* credentials from my Amazon account to anyone who gained access to the Gmail account my Amazon email is forwarded to…but Cloudsweeper missed a lot of plain text passwords (I found them simply by searching for the string “New password” in Gmail.
It also falsely claimed that cpanel.net sends passwords in plain text. Not only does it NOT, but end-users almost never get email from cPanel. The end-user would get email from their hosting company, which Cloudsweeper totally missed.
It’s on the right track, but needs some tweaking before it’s ready for prime time.
And for those concerned about the OAuth being “live” for 60 minutes, after you run the test, go to your Gmail account settings (top right corner, “Account”), then under “Password” chose “manage security”, which takes you to this page:
https://security.google.com/settings/security
Under “Connected applications and sites”, chose “review permissions.” You’ll need to re-enter your password.
From there you can see a list of all the applications, including Cloudsweeper, that you’ve authorized to connect with Gmail through OAuth. You can revoke access there.
Is it telling that it takes some effort to search through the GMail settings to find the security page?
Not sure and not going to give a 3rd party access to my account to find out. Who’s to say they aren’t saving all this information and cashing in on that money? =)
I couldn’t resist and tried it out even though the internet security side of my brain said “don’t do it , you will be sorry in the end ” $20
I wasted my time over this nonsense.
My emails are secure because any, or all of them could be tagged by a forensic seeding process. Making them worthless to the buyer of stolen emails.
KeePass is what I use. I store my key on a thumb drive that looks like a key. It’s great! Gmail is one of the only sites that i have found that will allow a password to 60 characters.
You’re all remarkably trusting.
I was about to try this service a time ago, but I was not sure about how secure Cloudsweeper site is. Since Mr. Krebs uses this service I must say it is ok. Finally I got an answer – $12.00 almost worthless Gmail.
Wow, $15,034! Maybe this will help expand my social life?
28.30. Woo Hoo I’m rich! I use Gmail’s 2 factor authentication and the single use password feature for my random devices. I’ve stopped password reuse on sites that could cause me loss but I’m careless on random news sites that irritate me with sign up requests.
I also use a password safe, one of them named on this comment thread. I do have the password stored in the safe deposit box since if anything happens to me, life will be easier for my family if they have all my financial passwords. I really recommend this – even in 1999 when my father died it was difficult to get some things switched over to my mother since they did auto login to AOL and we lost the password. I think this was before Cain :-).
I’m reluctant to log in to my gmail account with an unknown App watching. I’ll just have to guess what my account is worth and for me it’s priceless.
My account is worth a wopping $5!