An identity theft service that sold Social Security and drivers license numbers — as well as bank account and credit card data on millions of Americans — purchased much of its data from Experian, one of the three major credit bureaus, according to a lengthy investigation by KrebsOnSecurity.
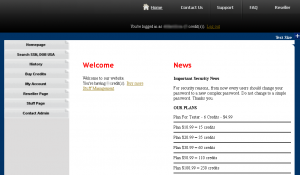
In November 2011, this publication ran a story about an underground service called Superget.info, a fraudster-friendly site that marketed the ability to look up full Social Security numbers, birthdays, drivers license records and financial information on millions of Americans. Registration was free, and accounts were funded via WebMoney and other virtual currencies that are popular in the cybercriminal underground.
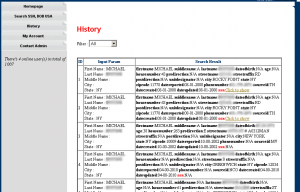
Each SSN search on Superget.info returned consumer records that were marked with a set of varying and mysterious two- and three-letter “sourceid:” identifiers, including “TH,” “MV,” and “NCO,” among others. I asked readers who may have a clue about the meaning or source of those abbreviations to contact me. In the weeks following that post, I heard from many readers who had guesses and ideas, but none who seemed to have conclusive information.
That changed in the past week. An individual who read a story about the operators of a similar ID theft service online having broken into the networks of LexisNexis and other major data brokers wrote to say that he’d gone back and reviewed my previous stories on this topic, and that he’d identified the source of the data being resold by Superget.info. The reader said the abbreviations matched data sets produced by Columbus, Ohio-based USInfoSearch.com.
Contacted about the reader’s claim, U.S. Info Search CEO Marc Martin said the data sold by the ID theft service was not obtained directly through his company, but rather via Court Ventures, a third-party company with which US Info Search had previously struck an information sharing agreement. Martin said that several years ago US Info Search and CourtVentures each agreed to grant the other company complete access to its stores of information on US consumers.
Founded in 2001, Court Ventures described itself as a firm that “aggregates, repackages and distributes public record data, obtained from over 1,400 state and county sources.” Cached, historic copies of courtventures.com are available through archive.org.
THE ROLE OF EXPERIAN
In March 2012, Court Ventures was purchased by Costa Mesa, Calif.-based Experian, one of the three major consumer credit bureaus. According to Martin, the proprietors of Superget.info had gained access to Experian’s databases by posing as a U.S.-based private investigator. In reality, Martin said, the individuals apparently responsible for running Superget.info were based in Vietnam.
Martin said he first learned of the ID theft service after hearing from a U.S. Secret Service agent who called and said the law enforcement agency was investigating Experian and had obtained a grand jury subpoena against the company.
While the private investigator ruse may have gotten the fraudsters past Experian and/or CourtVentures’ screening process, according to Martin there were other signs that should have alerted Experian to potential fraud associated with the account. For example, Martin said the Secret Service told him that the alleged proprietor of Superget.info had paid Experian for his monthly data access charges using wire transfers sent from Singapore.
“The issue in my mind was the fact that this went on for almost a year after Experian did their due diligence and purchased” Court Ventures, Martin said. “Why didn’t they question cash wires coming in every month? Experian portrays themselves as the databreach experts, and they sell identity theft protection services. How this could go on without them detecting it I don’t know. Our agreement with them was that our information was to be used for fraud prevention and ID verification, and was only to be sold to licensed and credentialed U.S. businesses, not to someone overseas.”
Experian declined multiple requests for an interview. But in a written statement provided to KrebsOnSecurity, Experian acknowledged the broad outlines of Martin’s story and said it had worked with the Secret Service to bring a Vietnamese national to justice in connection with the online ID theft service. Their statement is as follows:
“Experian acquired Court Ventures in March, 2012 because of its national public records database. After the acquisition, the US Secret Service notified Experian that Court Ventures had been and was continuing to resell data from US Info Search to a third party possibly engaged in illegal activity. Following notice by the US Secret Service, Experian discontinued reselling US Info Search data and worked closely and in full cooperation with law enforcement to bring Vietnamese national Hieu Minh Ngo, the alleged perpetrator, to justice. Experian’s credit files were not accessed. Because of the ongoing federal investigation, we are not free to say anything further at this time.”
WHO IS HIEU?
As I noted in my 2011 story, I’d found a scammer-friendly forum called talkgold.com where a user named “hieupc” was promoting superget.info as his site. Further searching showed that there was a fairly active Vietnamese hacker who used the nickname “hieupc;” That user appears to have gotten started defacing Web sites, even attacking the Web site of his former university in New Zealand after the school kicked him out for alleged credit card fraud. As it happens, the Web server address history for superget.info shows that it was hosted last year in Vietnam.
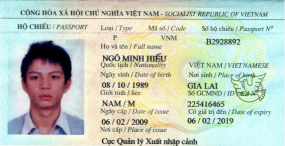 According an indictment unsealed last week by the U.S. District Court for the District of New Hampshire, Hieupc was none other than Hieu Minh Ngo, the 24-year-old Vietnamese individual named in Experian’s statement. According to court documents, Ngo resided in New Zealand and Vietnam, and operated superget.info and a similar ID theft service called findget.me, along with an unnamed co-conspirator, identified in the complaint only as John Doe One.
According an indictment unsealed last week by the U.S. District Court for the District of New Hampshire, Hieupc was none other than Hieu Minh Ngo, the 24-year-old Vietnamese individual named in Experian’s statement. According to court documents, Ngo resided in New Zealand and Vietnam, and operated superget.info and a similar ID theft service called findget.me, along with an unnamed co-conspirator, identified in the complaint only as John Doe One.
These services specialized in selling “fullz” or “fulls,” a slang term that cybercrooks use to describe a package of personally identifiable information that typically includes the following information: an individual’s name, address, Social Security number, date of birth, place of work, duration of work, state driver’s license number, mother’s maiden name, bank account number(s), bank routing number(s), email account(s) and other account passwords. Fulls are most commonly used to take over the identity of a person in order to engage in other fraud, such as taking out loans in the victim’s name or filing fraudulent tax refund requests with the IRS.
All told, findget.me and superget.info acquired or sold fullz information on more than a half million people, the government alleges.
The U.S. Secret Service declined to discuss the case, but a source familiar with the matter said undercover federal agents set up a phony business deal to lure Ngo out of Vietnam and into Guam, an unincorporated territory of the United States in the western Pacific Ocean. The source said that Ngo was arrested upon his arrival in Guam and transferred to New Hampshire. There he is currently facing 15 separate criminal charges, including conspiracy to commit identification fraud, aggravated identity theft, and wire fraud, among others.
If convicted on all counts, Ngo could be facing a very lengthy prison sentence. According to a statement on the Ngo case released Oct. 19 by the Justice Department and New Hampshire U.S. Attorney John P. Kacavas, the statutory maximum penalties are five years on the identity fraud and identity fraud conspiracy counts; two years each on the aggravated identity theft counts; 20 years on the wire fraud count and wire fraud conspiracy counts; 10 years on the substantive access device fraud count; and five years on the conspiracy to commit access device fraud count.
The unsealed complaint against Ngo is available here (PDF).
DATA BROKER BREAKDOWN
Meanwhile, it’s not clear what — if any — trouble Experian may face as a result of its involvement in the identity theft scheme. This incident bears some resemblance to a series of breaches at ChoicePoint, a data aggregator that acted as a private intelligence service to government and industry. Beginning in 2004, ChoicePoint suffered several breaches in which personal data on American citizens was accessed by crooks who’d used previously stolen identities to create apparently legitimate businesses seeking ChoicePoint accounts. ChoicePoint was later sued by the U.S. Federal Trade Commission, an action that produced a $10 million settlement — the largest in the agency’s history for a violation of federal privacy law.
In 2008, ChoicePoint was acquired by Reed Elsevier, the parent company of data aggregator LexisNexis. Last month, KrebsOnSecurity published an exclusive story showing how the proprietors of an identity theft service that competed with superget.info had hacked into the networks of LexisNexis, as well as data brokers Kroll and Dun & Bradstreet.
Avivah Litan, a financial fraud analyst with Gartner Inc., said this latest exposure raises serious questions about U.S. regulators’ capacity to monitor the due care of extremely sensitive consumer data, in accordance with the Fair Credit Reporting Act. Litan said that under 15 U.S.C. 1681b (PDF) credit reporting agencies have strict guidelines regarding to whom they may distribute consumer reports.
“It’s clear that criminal identity theft organizations are excluded from the list of users with ‘permissible purposes’,” Litan said. ” While the government shutdown certainly affected regulator business in October 2013, where have the regulators been for the last seven years when it comes to protecting sensitive consumer data? Have those efforts been shut down as well?”
There are signs that at least some federal regulators may be taking a harder look at the practices of the data broker industry. In an August 2013 keynote speech (PDF) at the Technology Policy Institute’s Aspen Forum, FTC Chairwoman Edith Ramirez said “the time has come for businesses to move their data collection and use practices out of the shadows and into the sunlight. In other words, with big data comes big responsibility. Firms that acquire and maintain large sets of consumer data must be responsible stewards of that information.”
Ramirez noted that the FTC can already bring actions under Section 5 of the FTC Act, and that it will continue to be active in punishing data brokers that fail to secure the information they collect. But she said stronger incentives to push firms to safeguard big data must be in place, and that the FTC has urged Congress to give the agency civil penalty authority against companies that fail to maintain reasonable security.
“Firms of all sorts are using consumer data in ways that may not just be contrary to consumers’ expectation, but could also be harmful to their interests,” Ramirez said. “This problem is perhaps seen most acutely with data brokers — companies that collect and aggregate consumer information from a wide array of sources to create detailed profiles of individuals. Their success depends on having more and better data than their rivals. The concern is that their mega-databases may contain highly sensitive information. The risk of improper disclosure of sensitive information is heightened because consumers know nothing about these companies and their practices are invisible to consumers.”
Last year, the FTC called on data brokers to give consumers access to their information through an easy-to-find, easy-to-use common portal. The agency also supported legislation to give consumers access to, and a right to dispute or suppress, data held by brokers. As it stands, Congress can’t even bring itself to pass a national data breach disclosure law, a relatively nonpartisan legislative effort that has enjoyed broad support from industry leaders for nearly a decade.
FTC Chairwoman Ramirez said the agency also issued subpoenas to nine data brokers, seeking information about the nature and sources of the consumer information the data brokers collect; how they use, maintain, and disseminate the information; and the extent to which they allow consumers to access and correct their information or opt out of having their personal information sold. The FTC said it expects to issue a report later this year with its findings.




Here is a question, and I think I just might start a legal movement to do this, why don’t we get a cut of the sales profits that these companies are making off OUR DATA???
IF the information I found out is correct, we would have to Trademark our P.I.I. And I have no idea if my source was reliable. It costs a lot of money to do an International Trademark too. If you find out something different though, please post it.
I will def have to look into that, and thanks or that fast reply..
Good read: http://defendourfreedoms.net/2013/10/23/reclaim-your-name-privacy-in-the-age-of-big-data-.aspx
Reclaim Your Name: Privacy in the Age of Big Data
Sloan Cyber Security Lecture by Commissioner Julie Brill
It’s not YOUR DATA. It’s data ABOUT YOU.
Nice semantics. But our data is like our fingerprint. It is used to distinguish or trace our identity. Therefor it is our data.
They are selling the service of gathering and cataloging the data and not the data itself. Additionally, somewhere along the way, we all agreed to this when we filled out an application for credit or lic. (that long contract we didnt read)
The Consumer Financial Protection Bureau and Federal Trade Commission refer to Experian, as well as the other credit bureaus, as selling data. The laws governing their practice, such as the FCRA and GLBA refer to the data as belonging to the person and governs the sales practice of said data.
Experian, and the other credit bureaus gather the data whether we, the data creator, authorize its collection or not. Those little opt outs you refer to on the credit cards is authorizing sales to the credit card affiliates. Has nothing to do with the credit bureaus gathering it.
However, the credit bureaus cannot release that data without the person’s consent.
Question to Krebs: Is it known how much money Experian made from sales to ID theft services? Is there a minimum/maximum possible amount?
Obviously not an english speaking person – “Thanks you” 🙂
Great post, I would definitely be interested in how much he made from this.
Experian and the other credit reporting corporations could care less about your personal information or if your identity is stolen. They are in the business of selling your personal information.
this is precisely the reason why I use privacymate.com for removal of my info from the cyberworld
Will the CEO or other managers of Experian be criminally punished for multiple counts of identity theft? Or will the shareholders of the company be punished by some kind of fine instead? It’s time for the bosses of companies to face criminal prosecution when the “company” commits a crime. They get all the credit and bonus money when the company does well – they should also take responsibility when the company engages in criminal behavior. I’m certain if CEOs went to jail when the company committed crimes, that CEOs would stop crime from happening in their company.
My God, Mr. Krebs…I actually have Experian’s Protect my ID service. Should I cancel it and move to Lifelock? Whatever would we do without you — reporting on key problems and issues that we would not otherwise know about. ellen
“paid Experian for his monthly data access charges using wire transfers sent from Singapore.”
The always xenophic American. You mean he used a bank other than one of the big five crooks? RED FLAG!
Thousand of customers… the irony of talking about privacy then advocating an interrogation of everyones businesses practises is delicious.
As is fining companies who are victims of criminals.
“The always xenophic American. You mean he used a bank other than one of the big five crooks? RED FLAG!”
No, the red flag should have been cash wires, which are not used very commonly, especially for a monthly fee.
Or maybe the face that someone posing as a private investigator is purchasing information about people in one country and paying for it in cash from another country?
“As is fining companies who are victims of criminals.”
Experian’s negligence caused material injury to their clients. Surely you’re not saying that businesses shouldn’t be held liable for that?
Nope, the OP is correct; to suggest otherwise is to suggest that PIs, who tend to be some of the most corrupt and untoward people out there, aren’t basically using a lot of the same sorts of arrangements. Or did you think that they all lived in Delaware and Texas, and all did their banking in perfectly legitimate ways?
Why don’t you ask Mr Krebs, here, what makes this case so special, when this data has been out there for everybody and anybody to buy through a thousand other vendors, and when voter registration and drivers license registry data has been available in various states for the past 20-30 years?
Oh yeah, that’d be, like, way too ambiguous. We like our good guys good, and our bad guys non-American. I forgot.
It’s not thousands. South Carolina’s Department of Revenue was hacked and over 6 million citizens were affected. Experian was hired to provide ID Security.
Much as it’s good for these scumbag fraudsters to face justice, I’m somewhat troubled in this instance. As I understand it, the perp in this case lived in Vietnam and had not committed any crimes whilst on US soil, yet the United States lured him to a US territory and there arrested him.
By what reasoning does the US have jurisdiction here? Are they claiming to have jurisdiction over anything that’s done over the Internet? Or anyone that does business, from overseas, with a US company like Experian?
It’s disturbing that the US seems to believe that it has the right to rendition anyone from any country in the world who does something on the Internet that the US doesn’t like. Besides the fact that the US isn’t perfect, other countries are much worse and could use the US’s behavior to justify doing similar things.
Imagine what would happen if Saudi Arabia or another very restrictive regime did likewise? Advocates for women’s rights, say, could just be snatched away to the Middle East to face charges for violating their “Sharia law” (and the penalty would likely be death).
There needs to be a clear ruling made in the United Nations or similarly, to the effect that:
a) If someone located in country X transmits internet packets from a computer in country X hooked up to a country X network provider, then only country X has legal jurisdiction over his or her actions vis-a-vis these particular internet packets, regardless of what other countries the packets travel through or arrive at, or what countries’ citizens read or are otherwise affected by the transmissions.
In simpler language, you’re subject only to the civil and criminal law of the country within whose borders you’re presently located, and using a computer or phone doesn’t magically change that and subject you to everyone else’s (or just the US’s) jurisdiction as well.
b) It is a violation of human rights for agents of a state to either enter a foreign country and abduct one of its citizens (extradition procedures through proper legal channels notwithstanding) or to lure one of its citizens abroad to “arrest” them there.
If someone has committed a crime on your soil and then fled, you can declare them wanted. If the destination country’s law enforcement catches them they can be subjected to extradition proceedings, with due process. You cannot take egregious shortcuts with this process by means of entrapment, infiltration, or invasion (and the latter two should additionally be considered acts of war).
And if you have no jurisdiction because they didn’t come into your country and perpetrate a crime there, but merely did something on the Internet that you didn’t like, then too f*cking bad. You can’t touch them. If they violated local law, you can report that violation to their own area’s law enforcement for them to prosecute. If the other country’s laws allow things on the Internet that you disapprove of, your recourses include learning to live with it or being a dick and blocking (some of) the other country’s network packets at your borders like Iran and China do. They do not include luring, arresting, and charging the person with a violation of one of your laws, when they never were subject to your laws.
You make some very valid and excellent points. Since many places in the US have laws against entrapment, I find it appalling that this was a tactic that was used. It mentions ‘federal agents’ but not which agency it was that lured this person.
I agree with you though, this is offensive behavior and no one country should act like this. I sure wouldn’t want other countries doing the same to US citizens for the very reasons you mentioned.
You may want to look up entrapment – it doesn’t mean what you think it does. It is perfectly legitimate to set a trap to catch a criminal. Entrapment on the other hand, is the attempt to coerce someone to commit a crime for the purposes of subsequent arrest and prosecution.
What you’re falling to realize, is that he wasn’t arrested for his internet behavior, he was arrested for conducting illegal business in the US over the internet. Regardless of where he was when the business took place the transaction itself originated in the US, and that is illegal. While I agree it’s questionable to lure him under false pretenses, I think the actions were justified considering the scope of his actions.
You also have a fair point regarding the business originating in the US. There is such a fine line here with the way things were handled.
My problem here is definitely with the entrapment.
Entrapment is occurs when law enforcement provokes someone into committing a crime that they wouldn’t have otherwise committed. This person had already committed the crimes, allegedly, he was not lured into committing them by law enforcement. So calling what the Secret Service did entrapment is incorrect.
From Merriam Webster:
the illegal act of tricking someone into committing a crime so that the person you have tricked can be arrested.
He wasn’t tricked into committing the crime ergo he was not entrapment. Luring someone into this country on false pretenses is not a crime, unless you are trying to commit immigration fraud, or engaging in human trafficking, and that was not the case here.
Fair enough, I was using the wrong word. He was lured here. I do believe people have a valid point. I very much want the guy to receive justice for his crimes, because I know a number of people who have had their identities stolen and credit cards duped by people overseas, etc.. I’m just not sure how I feel about the *luring* of him.
And before anyone goes off calling me dumb or calling my patriotism into question, again, I feel like he should get what is coming to him so if that is the ONLY way we could have managed this, fine. But what happens when the shoe is on the other foot and it’s an American committing this offense? Are people going to cry foul? Cause that’s what I see happen all the time and it’s really quite irritating.
Personally, no – i would not cry foul if an American is extradited to another country to face trial for crimes he/she committed there.
But this Vietnamese person didn’t commit any crimes in America. He committed crimes in Vietnam. Why should that open him up to being extradited to America? Do we really want any country, even America, actually being the de facto “world police”?
Cassandra:
He committed crimes against us citizens thru computers that were in the United States. His physical location doesn’t matter and he wasn’t extradited. He was arrested in the United States. Btw, your argument suggests that countries are powerless to protect themselves against anyone outside its borders. You might want to rethink that theory
How do you believe he came to be subject to US jurisdiction? Having sent internet packets that affected US companies and US citizens can’t suffice, or everyone who posts something publicly on the internet would be subject to every jurisdiction in the world.
As for how countries defend themselves against people outside their borders, THEY HAVE BORDERS. Here are ways that this could be handled by the US that don’t involve the US acting as “world police”:
1. Have an MLAT treaty with Vietnam. Alert the Vietnamese authorities. If the miscreant is violating Vietnamese law, he can be arrested and tried under the laws and with the protections of his own country.
2. If the miscreant is *not* violating Vietnamese law, or Vietnam refuses to prosecute if there aren’t Vietnamese victims, the US can refuse to do business (banking, etc.) with Vietnam, both pressuring Vietnam to conform *and* protecting US citizens from Vietnamese scamsters.
3. If this doesn’t suffice (say, the miscreant is launching bombs into US territory and not just sending information into it that they’d be unwise to treat as authorized transactions), and the government is complicit in allowing this to continue, then military action could be indicated. (This is actually a bit stricter than what triggered the “intervention” in Afghanistan. The attackers in that case actually traveled to the United States and then committed crimes on US soil. It applies to their conspirators that stayed home, though.)
The perp lived in Vietnam, but he didn’t sell personal information about Vietnamese, but about Americans. He committed crime where U.S. citizens were victims. An probably sell it to U.S.-based crooks.
The problem with that logic is that a country like Saudi Arabia could decide that posting information online that encourages women to seek equal rights is a “crime” against men in Saudi Arabia that would rather keep women subservient, or even a form of “theft” since they regard women as their property there. Other countries may also regard commonplace Internet activities as somehow “crimes” against their citizens.
In the case of fraud, the actual crime — the event that causes there to be a victim — is the fraudulent transfer of funds. The fraudster eventually needs to access the funds, either as money or converted into goods. If their conduct is illegal in the country where they reside, then they can be prosecuted under its laws.
If US citizens need to be protected against bad actors in a country that *legalizes* fraudulently withdrawing money from overseas accounts, the solution seems to be for US banks to deny outbound transfers of money (and, likely, shipments of mail-order goods) to such jurisdictions as have legalized such behavior, to protect their own customers. Countries that behave that way are then pushed towards international norms on what’s considered illegal fraud by business pressure — the more they deviate from such norms, the fewer banks in other countries will do business with banks in their country, hurting their bottom line. The US legislature could also outlaw banks from doing business with counterparts in “risky” countries, however-defined.
(Indirect transfers to route around geo-blocks, such as causing a fraudulent transfer to country A (not blocked in the US) and thence to country B where this is legal, would need addressing, but really country A should be blocking transfers to country B in this situation.)
This would resolve the danger to US consumers’ finances without trying to enforce US laws in places that lie geographically outside of US territory, and without trying to turn the Internet from “no place in particular” to “subject to US jurisdiction as if it were a US territory”.
The curse of foresight coupled with the inability to get anybody to listen; isn’t this always the case?
And once again, ‘they’ like to go after the people seemingly providing information to criminals (and other people), when it’s really a case of preferential treatment. These sorts of cases seem to intimate that searches that anybody can do by paying a fee are a whole lot worse when an aggregator is involved, even though there are a ton of aggregators out there. As usual, someone with money probably complained that they weren’t getting a big enough piece of the pie.
What, did people think doing lookups on people, in and of itself, was a crime? In case nobody knows, this itself is NOT identity theft, fraud, or anything of the sort.
In your reasoning, is the following correct:
I am standing in Island A, and Island B is a couple of yards away (Both these islands are fully sovereign entities). From Island A, I shoot a person on Island B. Should I not be prosecuted on Island B for my crime committed from Island A against a person on Island B? Jurisdiction is a very complicated affair, and best left to persons well versed and educated in the matter.
If Island A and Island B have a MLAT (mutual law-enforcement assistance treaty), the police on both islands can cooperate to identify the shooter, and the shooter’s own local police and courts can arrest and try him according to the laws he’s subject to, assuming his own local laws forbid shooting people (even across the border).
If the shooter’s country doesn’t cooperate or doesn’t outlaw shooting someone outside its borders from inside its borders, the other country can erect a wall just inside its borders and make that bulletproof, or take other steps. Good fences and good neighbors, etc. … if the shooter crosses the border to shoot someone he then becomes subject to the jurisdiction there.
If the shooter starts launching missiles over the wall, the country being bombed can threaten the other with war. If the other doesn’t stop the missile launches (say, by arresting and trying the perpetrator), or its government is directly responsible for them, then actual war is justified to end the threat. Same if an army of shooters sets forth with government blessing to cross the border and invade.
Should people change bank account numbers with the possibility of this type of breach affecting them? Credit locked or not, the criminals have access to those numbers.
So do used car lots, pretty much every customer service agent you’ve ever paid a bill to, and every apartment complex out there — as well as anybody considering renting a room. Technically this sort of data, btw, is not the same as pulling a credit check; it’s the equivalent of pulling what is known as ‘credit headers’ — and has been going on as far back as the modern credit system has gone on. It doesn’t provide account numbers, limits, or balances, but it does provide name, all past addresses going back as long as the credit report does, often DOB, generally speaking SSN (but not always), etc. Basically think of it like a credit report with all the money stuff stripped out. A used car lot can get the whole shebang. This is far less. And yes, it’s intrusive — but it’s also, unfortunately, illegal in the US — if you do not like it, then do something about it; fight for privacy laws instead of falling for the FUD.
Correction: “but it’s also, unfortunately, illegal in the US” should have read “but it’s also, unfortunately, LEGAL in the US”
My question is, how do you find out if your data was sold? Was it the entire customer data base? I don’t use Experian, but some of the companies I’ve worked for did. So…? Is there a way for me to find out if my personal information has been sold?
There honestly is no way. If you look at the number of breaches that have occured over the past 3-5 years, its simply incredible. Data that is out there will remain out there. Your credit card information may change or expire and then, at least that part of the equation is broken.
What you may want to do is obtain a credit report every once in a while. Then you can validate what is on it, and what is not. Some will monitor it monthly and set alerts.
Like all the other breaches and break ins, laptops, cdroms, dvds thumb drives, data at rest of old workstations and servers and other items stolen, its tough to know when, if ever data will be used.
I try my best to stay proactive, and try to limit my expsure to a few websites. I also try my best to keep passwords different on each website, so they cannot try to use that information to gain further access.
Keep an eye on your bank accounts and any weird charges you do not recognize. Pretty simple stuff, takes a few minutes a day. If you feel you need to start changing passwords on sites, and write them down somewhere safe. I don’t recommend carrying them with you unless they are pretty well disguised.
I suggest to worry about it – – – Mildly. It will keep you vigilant, but not over protective or paranoid. It COULD be out there, somewhere, but then again it could not be out there at all. Some companies will send out Breach notification letters and let people know what is up. Its a mixed up world out there, so do your best to manage what you have control over, and hope for the best.
Here’s what is ironic: My credit card info was compromised in the Adobe hacking incident a few weeks ago. Adobe told me to sign up for an Experian account for my security, to keep track of my credit activity. I signed up for it *yesterday* and then this report comes out. Any idea what my next steps might be?
Got the same letter from Adobe, but it was Equifax who used a 3rd party to sell me my credit score, I did not take out monthly service but ordered a credit score, my bank statement shows 3-withdrawal charges. Shows pending but I also got my credit score from the 2-other agencies and they only charged me the one charge. I called Experian, they assured me the other 2-charges will be removed tomorrow. We’ll see.
Petition created at:
https://petitions.whitehouse.gov/petition/demand-experian-contact-and-pay-damage-12-million-consumers-whose-data-was-sold-hacker/WBwKv46z
It’s our rights as potential victims to know if our data has been mishandled.
What about starting a petition on that to pass to Congress? 1/2 million potential victims! Heck that’s a lot.
Shall we all wait till someone uses our info to our detriment to know if we have been impersonated?
What a joke and some nerve from those companies to ask us to pay them to protect our identity that they have mishandled in the first place… Is that a farce?
What are the politicians doing?
The argument that he shouldn’t be charged because he wasn’t on US soil when he committed the crime is ridiculous. He sold Americans PII to fraudsters around the globe using computers based in the USA. By your argument, any hacker/thief can commit any crime against USA provided they aren’t actually in USA and whatever country they are in might not have a law specifically against it. That is patently stupid. That’s saying USA has no right to defend itself against these people because they aren’t on their soil. It reiterate…dumb.
Also, calling a lure entrapment shows your lack of understanding of the word. To entrap someone means to induce them to commit a crime,through extraordinary means, that they otherwise wouldn’t commit. This guy was committing these crimes since 2007 and would have continued unless he was caught. Plus, he wasn’t charged with traveling to USA so being “entrapped” to travel makes no sense at all. He was charged with the crimes he committed and wasn’t induced by anyone to commit those crimes. To my knowledge, Vietnam doesn’t extradite ppl to USA so what other choice did fbi have?
Greed plays into this. He was willing, as expected to look for more opportunities to exploit. IF he was smart, he should have realized, that Guam is a US territory and by touching that soil, he made a big mistake.
Its one less vile individual off the streets for now.
Look, I live in the USA. At least we are proactive in trying to thwart some of the crooks and put them away. I have to admit, sometimes the process is slow and lethargic, and the penalties afterward are probably not enough.
Its like anything else, some one starts something good, and other will follow. You can either accept what they are doing, and potentially become a victim of their ways, or assist in any way you can in a manner which isn’t too stressful or load bearing.
When an incident of someone using your credit line to make a major purchase (over 10,000 USD) happens to you, I bet you’d be the first in line to hang’em from the highest tree. Me, I have been lucky so far.
I simply keep proactive and keep an eye on what is considered mine.
It was Doug!
Solution: Charge Experian $1,000,000,000,000 per identity sold through this. That should put sufficient terror into the remaining companies that trade in identity information.
I find it humerous that I just got a letter form Adobe appologizing that my data may have been exposed and offering me free credit monitoring with EXPERIAN! I guess if the hackers didn’t get it from Adobe, they can buy it from Experian.
Wow! Give a headache, sell an aspirin!
http://www.experian.com/hitwise/press-release-adobe-hitwise-partnership.html
Experian and Adobe expand partnership to include Hitwise and Adobe SiteCatalyst data exchange
They interface.
so brian, how does one go about finding out if their information was included in this breach?
I say this sounds like a class action lawsuit waiting to happen!
Experian provides the Identity Proofing service from the Federal Data Hub for Obamacare.
Do you just string buzzwords together and hope they form a complete sentence?
Experian provides the Identity Proofing service from the Federal Data Hub for Obamacare . Google it.
Brad,
Why is USInfoSearch.com. off the hook? They admitted to being a partner of Court Ventures and to sharing all their info with Court Ventures. Apparently Court Ventures was the company that started selling info to this jerk.
So I’d say the web of greed-driven incompetence starts with Court Ventures and extends to *anyone* who trusted data with them. The word “cavalier” leaps to mind about Court Ventures, USInfoSearch, and Experian. Not to mention congress…
We only have Marc Martin’s side of the story. I wouldn’t expect him to mention anything that would make his own company look bad. And that’s all I’m going to say about that.
The whole business model of companies selling people’s personal data is pretty ethically challenged. Why is it legal for Experian or US InfoSearch to sell our data to anyone who claims to be a private investigator in the first place? How many other little companies are doing the same thing? Why are big companies with big breaches still able to continue in the same business?
As mentioned in another comment, the problem is that people are given too much access simply by possessing data that is permanently associated with other people. You’d never choose your birthdate or SSN as a password, yet you can use mine to get an instant charge account? Seriously? My data has been stolen so many times from so many sources, it’s hard to imagine any more breaches would make a difference. And Experian has everyone’s data. But even the fact that any crazy dude you’ve ever worked for legally has your social security number ought to make companies stop using it like it was the equivalent to your signature.
The main problem here is that banks etc uses social security numbers, mothers maiden name, and other related information as AUTHENTICATION.
This kind of information should be considered publicly available, as this article shows, and thus should not be used as anything more than IDENTIFICATION of someone.
However the bank will verify the person who claims that the presented identity is valid is a good question, but accepting social security numbers and similar trivial information should be a crime!
“Each SSN search on Superget.info returned consumer records that were marked with a set of varying and mysterious two- and three-letter “sourceid:” identifiers, including “TH,” “MV,” and “NCO,” among others.”
I read somewhere that the “MV” was the Department of Motor Vehicles, and I don’t recall what the other two were called. It was a post, maybe 6-8 months old. if it wasn’t on Krebs, then it could have been on
http://www.databreaches.net/?s=dmv&searchsubmit=
Databreaches show a few people have been busted for abusing the DMV records, and may have contributed to the issue.
No idea what TH is other than Town Hall ? NCO, no idea as well, but I will dig.
NCO may be some sort of Online Courts Information, I think there is a website that will identify information about upcoming and past cases, outcome and info about the related charges.
I dont remember if it was tied to a locality or if it was USA wide. All you had to do was type in a court case number or name as it appeared on the court papers.
http://www.ncogroup.com/
NCO is a collections agency….. wonder how much PII they have….
wonder if there any insiders working in that organization.
= \
The problem is the personally identifying information is not secret, yet still used to authenticate people.
These breaches will always happen because far too many organizations need access to the information for the same reason: to identify people.
Relevant:
It’s Me, and Here’s My Proof: Why Identity and Authentication Must Remain Distinct
http://technet.microsoft.com/en-us/library/cc512578.aspx
P.I.I. is protected information. Not even obtainable without authorization from the owner depending on the source it is being obtained from.
Motor vehicles, protected under DPPA.
Health data, which includes birth certificates, HIPAA.
Financial, protected under FCRA. Organizations cannot run a credit check with the Bureaus without authorization from the person being checked.
Data brokers want to claim everything is public because they make large amounts of monies in selling it. This is why they are so cagey about where the data they have comes from.
P.I.I :
Guide to Protecting the Confidentiality of Personally Identifiable Information (SP 800-122).
The OMB memorandum defines PII as follows:
Information which can be used to distinguish or trace an individual’s identity, such as their name, social security number, biometric records, etc. alone, or when combined with other personal or identifying information which is linked or linkable to a specific individual, such as date and place of birth, mother’s maiden name, etc.
http://csrc.nist.gov/publications/nistpubs/800-122/sp800-122.pdf
It doesn’t matter what is is protected under. if a priviledged user goes rouge and decides to sell your information at all costs, its over. All it takes is one miscreant to grab PII and offer to sell it, and whatever consequences happen after that are done and over.
Guides and procedures and such are only as good as the structure polices, screening processes and monitoring. Agencies are to lax and pay pitifully for the talent they require. many are understaffed or improperly trained and things go amuck.
You make it sound like it is in a vault with limited people having access to it. I assure you it is not that tightly guarded. Go to http://www.databreaches.net and type in DMV and that alone has a half dozen people arrested for selling PII.
The system is broken, no matter what some people don’t wish to see.
Oh, I agree. I was making my post disputing the claims that it is all ‘public’ information. P.I.I. is protected information therefore mass trade in it and flinging it all over the place is not ok.
In banking, we employed field masking of sensitive (PII) data, and controlled access to this data through the use of role profiles. The goal was to make sure that folks only had access to the information they need to do their job. We even monitored account “touch” activity for signs of internal fraud or information abuse by employees.
Tar… feathers…
It’d be interesting to see if Experian is punished in any way for the data breach. Great story, Krebs!
Just think, Experian is working on security related tasks for the ACA (Affordable Care Act) . ACA brings with it, a host of its own security challenges.
Any scoop on arrest of Paunch?
http://rt.com/news/blackhole-paunch-arrest-russia-946/
コーチ 財布 最新 coach アメリカ アウトレット http://www.hanlinbook.com/ショルダーポシェット-z4-4.html/