Apple on Friday released a software update to fix a serious security weakness in its iOS mobile operating system that allows attackers to read and modify encrypted communications on iPhones, iPads and other iOS devices. The company says it is working to produce a patch for the same flaw in desktop and laptop computers powered by its OS X operating system.
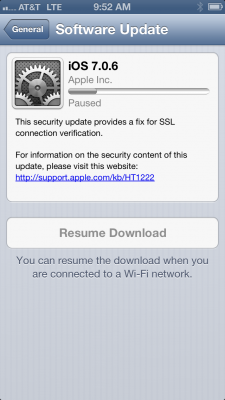 The update — iOS 7.0.6 — addresses a glaring vulnerability in the way Apple devices handle encrypted communications. The flaw allows an attacker to intercept, read or modify encrypted email, Web browsing, Tweets and other transmitted data, provided the attacker has control over the WiFi or cellular network used by the vulnerable device.
The update — iOS 7.0.6 — addresses a glaring vulnerability in the way Apple devices handle encrypted communications. The flaw allows an attacker to intercept, read or modify encrypted email, Web browsing, Tweets and other transmitted data, provided the attacker has control over the WiFi or cellular network used by the vulnerable device.
There has been a great deal of speculation and hand-waving about whether this flaw was truly a mistake or if it was somehow introduced intentionally as a backdoor. And it’s not yet clear how long this bug has been included in Apple’s software. In any case, if you have an iPhone or iPad or other iOS device, please take a moment to apply this fix.
Generally, I advise users to avoid downloading and installing security updates when they are using public WiFi or other untrusted networks. On the surface at least, it would seem that the irony of this situation for most users is that iOS devices will download updates automatically as long as users are connected to a WiFi network. But as several folks have already pointed out on Twitter, Apple uses code-signing on iOS and app updates to ensure that rogue code can’t be pushed to devices.
I will update this post when Apple ships the patch for OS X systems. For now, it may be wise to avoid using Safari on OS X systems. As Dan Goodin at Ars Technica writes, “because the Google Chrome and Mozilla Firefox browsers appear to be unaffected by the flaw, people should also consider using those browsers when possible, although they shouldn’t be considered a panacea.”
For a deeper dive on this vulnerability and its implications, check out this piece by Larry Seltzer at ZDNet, and this analysis by Google’s Adam Langley.
Update: Apple has fixed this and a number of other important issues with OS X, in this release.




Thank you. I subscribed two weeks ago and did hear this news yesterday but as always after reading your email today you have different information and added information. Enjoy reading your updates.
Are we sure it isn’t the NSA or other government entity? Weren’t they upset that they couldn’t break the encryption of the Apple operating system just a year or so ago, threatening at one time to have a judge force them to do so?
I actually updated yesterday, so I am good to go, but the rest of you, beware…
Just joking….
Thank you, Brian for keeping everyone on top of things.
It’s not outside the realm of possibility that the government wanted something Apple refused to give. Charging them with price fixing seems odd, given the miniscule share of the book market they have. Sometimes there are dots to connect.
Anybody know of plans for I-Pad 1? Mine runs IOS 5 and will not update.
The original iPad reached end-of-life a couple of years ago, and there are no planned updates for the device, as far as anyone knows, though certainly Apple took it seriously enough to release a new version of iOS6 – which, to my knowledge, has never happened before.
On the other hand, it is also not currently clear whether versions of iOS lower than 6 are currently affected – it may have been a bug introduced with iOS 6. If you’d like to check whether your device is vulnerable, visit http://gotofail.com and see whether the image loads. If it does, your device is vulnerable to the bug.
However, as Brian notes, a significant mitigating factor is that at least one point between your device and the site you are visiting needs to have been compromised in order to execute this attack. As for what you can do: exercise caution in connecting to untrusted Wifi and cellular networks, and consider moving to a different device.
Any iOS device that runs iOS 5.x or earlier should be fine – the bug was introduced in iOS 6.0.
On the Mac side, the bug was introduced with OS X 10.9 Mavericks. I was pleasantly surprised to find my 10.8 Mountain Lion system isn’t affected.
I can confirm that an iPod Touch 3G running iOS 5.1.1 is NOT vulnerable, according to results from gotofail.com.
Urgent iPhone and iPad security update, Mac OS X pending
http://wxx.welivesecurity.com/2014/02/22/urgent-iphone-and-ipad-security-update-mac-os-x-pending/
another reason you should ALWAYS use a VPN. And yes I know they can mitm once you egress the VPN but that defeats the rogue AP’s or coffee shops. better to wrap it up when inserting your data into anything foreign.
Looking at Adam Langley’s analysis reminds me “Goto considered harmful”.
Indeed! And, how ironic that the offending line is “goto fail.”
Bug of the year.
I would prefer to not update from iOS6 to any version of iOS7. Battery life, ‘flat’ display, etc.
What options do I have?
Is there any discussion of Apple updating iOS6? I have an iPhone5.
Yes, an update for iOS6 has been released.
I spoke too quickly. The update for iOS6 has been released, but will only be offered to “the iPhone 3GS and 4th generation iPods.”
See Larry Seltzer’s ZDNet article for more info.
Jailbreak it and install the patch.
Brian I hope you do an article on this CEH ECCouncil hack. This is devastating to us in the security industry to have all of our passports leaked to attackers. Truly sucks that myself personally had his passport leaked because a certification company that issued a CEH cannot keep their clients stuff secure.
Qualys has a test up that checks to see if you’re affected, here:
https://community.qualys.com/blogs/securitylabs/2014/02/24/ssl-labs-testing-for-apples-tls-authentication-bug
MacOSX 10.8.5 is NOT vulnerable
Right, its only OS X v10.9 and higher. On iOS its only on iOS 6 & 7. Earlier versions of the OS’s do not have the issue.
Can you spot pot the goto fail; failure that is the source of this bug?
Forgot the link: https://gist.github.com/alexyakoubian/9151610/revisions
Wow, even 30 years ago at Georgia Tech we had it pounded into our heads to not use “gotos”. Why are ‘developers’ still using this crummy code structure?
I don’t think that goto is the real culprit here. The same bug could have happened in other languages which offer either “break” or early return.
The main problem is the lack of brackets for the if statement and, worse, the lack of any static code check which looks for dead code (the java compiler would reject similar code outright). Or a decent test suite (although Adam Langley waved that away with “too complicated to build”) for that matter.
https://gotofail.com/
test site
“hand-waiving” — probably you wanted “hand-waving”?
Just updated my MBP (10.9.2). The issue is now fixed. I verified by visiting the link in the imperialviolet.org write-up. Before the OS X update Safari was vulnerable. Now it is not.
Interesting that the OS X update addresses a number of items, but the Safari security fix is not one of the items listed.
j
Two questions if I may…
1. What does “a privileged network position” actually mean (as documented in the Apple release info)
2. Why is cellular connectivity not included in the discussion (at least not consistently)? Some articles say lan/wi-fi and cellular, some say cable and wi-fi only and some say wi-fi only. Isn’t an IP based exposure an IP based exposure regardless of who is providing the IP?
> 1. What does “a privileged network position” actually mean
Privileged means having control.
Network position means between you and something that you are contacting.
Consider your average visit to a friend’s house.
Your device (P0) connects to their Wi-Fi Access Point (P1). That AP might be connected to a Router or directly to a cable modem (P2). The cable modem is on a shared loop with a bunch of other cable modems (P3). They are collectively connected to the cable head end (P4). There are some routers in the cable network (P5). From their your packet typically travels to an upstream provider (P6), e.g. Level3.
That is just the average base path for any random packet you send to anywhere on the Internet.
Let’s say you are actually taking to http://www.washingtonpost.com. To do that, your packet will travel to the upstream provider for WP (P7), to the WP’s ISP (P8), to a router for the WP (P9), and potentially on some shared loop (P10 – but hopefully not) before reaching your intended destination.
All of the Ps are privileged network positions – anyone sitting at any of these positions is in a fairly good position to send out fake replies.
Also note that before you send a packet to WP, you need to find its IP address – the path for that lookup will probably be slightly different, but again, people along the path to it are in a privileged position and can sometimes forge a day response.
Also, while you may think that you are visiting WP, the page you get will probably load resources from 5-10 other content providers (typically including at least one advertising network). Each of those servers will have their own path (between you and the server).
> 2. Why is cellular connectivity not included in the discussion (at least not consistently)?
Usually the easiest attacks are on your poorly secured Wi-Fi AP (P1..P2). Or if not an attack there, then on the shared cable loop (P3). And while some cellular carriers may have bad infrastructure (or “amusing infrastructure”), the chances of this aren’t that great.
There’s of course a chance of an attack based on the remote side (P9..P10), but there’s an assumption that someone would notice.
Brian: You promised an update when Apple released the fix for OS X. As John noted, it’s out (I upgraded yesterday).
Gotta update my Mac before I get slimed.
Paying for traffic requires a great deal of keyword research and testing different types of ads, which does take time. I