Millions of Web sites were shuttered Monday morning after Microsoft executed a legal sneak attack against a malware network thought to be responsible for more than 7.4 million infections of Windows PCs worldwide.
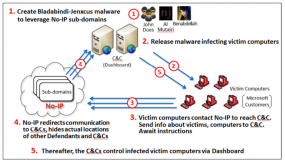
A diagram showing how crooks abused no-ip.com’s services to control malware networks. Source: Microsoft.
In its latest bid to harness the power of the U.S. legal system to combat malicious software and cybercrooks, Microsoft convinced a Nevada court to grant the software giant authority over nearly two dozen domains belonging to no-ip.com, a company that provides dynamic domain name services.
Dynamic DNS services are used to map domain names to numeric Internet address that may change frequently. Typically, the biggest users of dynamic DNS services are home Internet users who wish to have a domain name that will always point back to their home computer, no matter how many times their ISP changes the numeric Internet address assigned to that computer.
In this case, however, the attackers responsible for leveraging two malware families — remote-access Trojans known as “njrat” and “njw0rm” — were using no-ip.com’s services to guarantee that PCs they infected would always be able to reach the Internet servers.
Microsoft told the court that miscreants who were using these two malware strains were leveraging more than 18,400 hostnames that belonged to no-ip.com. On June 26, the court granted Microsoft the authority to temporarily seize control over 23 domains owned by no-ip.com — essentially all of the domains that power no-ip.com’s free dynamic DNS services.
Microsoft was supposed to filter out the traffic flowing to and from those 18,400+ hostnames, and allow the remaining, harmless traffic to flow through to its rightful destination. But according to no-ip.com marketing manager Natalie Goguen, that’s not at all what happened.
“They made comments that they’d only taken down bad hostnames and were supposedly redirecting all good traffic through to users, but it’s not happening, and they’re not able to handle our traffic volumes,” Goguen said. “Many legitimate users that use our services have been down all day.”
Goguen said while Microsoft claimed that there were more than 18,000 malicious hostnames involved, no-ip.com could only find a little more than 2,000 from that list that were still active as of Monday morning. Meanwhile, some four million hostnames remain offline, with customer support requests piling up.
“So, to go after 2,000 or so bad sites, [Microsoft] has taken down four million,” Goguen said.
Microsoft told the Nevada court that despite numerous reports released by Internet security firms over the past year about large volumes of malicious activity emanating from no-ip.com’s service, the company “consistently failed to take sufficient steps to correct, remedy, or prevent the abuse and to keep its domains free from malicious activity.”
But according to Goguen, the first time Microsoft brought its concerns to no-ip.com was at 7 a.m. on June 30, when the company’s CEO received a knock on the door of his family home and was served with a copy of the court order granting Microsoft authority over the 23 no-ip.com domains.
“We work with law enforcement all the time, and our abuse department responds to abuse requests within 24 hours,” Goguen said. “It’s pretty sad that Microsoft had to take such extreme measures to go about this.”
Goguen isn’t the only one who believes Microsoft swatted a fly with the equivalent of an atom bomb. Some of Microsoft’s previous legal sneak attacks targeted “bulletproof” hosting providers — those that promise to keep sketchy (and high-paying) customers online despite pressure from security firms and law enforcement. But according to Dmitri Alperovitch, co-founder of security firm CrowdStrike, treating no-ip.com like one of these shady providers is a mistake.
“They have always been very responsive to security researchers and law enforcement,” Alperovitch said of no-ip.com. “I do not consider them a bullet-proof or abuse-proof host.”
Meanwhile, Goguen said no-ip.com is considering its legal options for responding to the outage and to Microsoft’s allegations that the company somehow turns a blind eye to abuse complaints.
“We’re speaking with our lawyers about this, but right now we’re doing everything we can to fix this, and we need our users to understand that.”
In tandem with the action against no-ip.com, Microsoft also named and accused two men — software developers thought to reside in Kuwait and Algeria — of authoring and selling the njrat and njw0rm.
The complaint against no-ip, the accused malware authors, and the rest of Microsoft’s various legal filings in this case are available at this link.




As a PAYING customer of no-ip, I think MS should have inquired about paying accounts with them, and filtered that data accordingly, followed by the obvious filtering to weed out the suspect subdomains as listed in the court order.
Now I have no access to the service I PAID for, and no resolution for any of my 30 no-ip subdomains.
I’m not a criminal. I remote into computers to provide tech support.
Rather, I’m a victim of theft.
In a just world, Microsoft would pay reparations to every paying customer of no-ip as well as to no-ip itself. And, more importantly, the judge that signed this order would be put on trial for theft.
That the last could never happen tells me how far from a just world I truly live in.
JUST? It sounds more like “your world”.
Plenty of other countries with different mind sets out there. If this one happens to not meet your expectations, help yourself and see if there is anything better.
Are you trying to say that we should stop fighting injustice? America is good because people fought to preserve their rights. If you just turn around and bend over, it wouldn’t be long before America becomes like Saudi Arabia. People at the top would like to get as much power as they can amass, but it is the duty of the citizens to make sure they do not tread on our freedoms.
I’m one of those affected and I have a PAID no-ip account. I host a couple of closed minecraft servers running on Linux and I’m totally inaccessible to everyone now.
Microsoft is responsible for this mess and it’d be nice if they’d reimburse us for the lost access. I just don’t want them giving me Windoze freebies. I fled Micro$oft for a reason. Now I have another reason, heavy-handed incompetence.
My MC server is down too thanks to this!
I’m another paying legitimate user too. I’m all for stopping malware but I can’t believe this was the only way. Seems like Microsoft just flexing its money and taking the easy way out.
All affected customers of no-ip should individually sue microsoft. You may not win your lawsuit, but it will cost microsoft quite a bit in lawyer fees if there are at least a few thousand cases, and next time they will think twice.
The problem is not no-ip. They are a symptom. The problem is the MS desktop operating system. It appears to me MS wishes to deflect their OS problem responsibility and solve their problems on the backs of others. Using any type of normalized measurement: For example: MacOS and Android and Linux (server) do not seem to have a persistent issue of miscreant hijacking via defects in their code. All OSs have defects that enable miscreant access and have suffered miscreant hijacking. Yet, WinOS desktop is the only one that seems to have persistent miscreant hijacking by any normalized measurement. The WinOS persistent hijacking has been ongoing for way over a decade. Is it time to accept and make non-backward-compatible changes? (I am not encouraging a flame-war here. Please don’t. I want to encourage everyone to think in terms of problem solving and creative ideas.) Let’s start having incremental individual changes that becomes a tsunami of change.
Well when you look to target an OS where are you going to go? To the smallest market share or get the most bang for your buck and hit the most used OS’s in the world? Add that to a largely uninformed and click happy user base and you have the perfect platform to exploit. If Linux and any of its variants were the leading OS, it would be primary OS to be targetted.
Add to this the difficulty of actually getting the user base to adopt those incremental changes. Too much of the discourse ends up being about securing operating systems one day but whinging about life-cycle-expiring old stuff like Win XP the next. Too many people participating in the debate end up choosing contradictory stances. And that doesn’t help.
Evolution of platforms and gradual retirement of the old is indeed a good principle to operate under, but part of the friction is contributed by human nature. And that’s not as easy to overcome.
My opinion from a long-term and leadership perspective, again, my opinion: A quantity argument here is a smoke screen, a red herring, for problem solving. And yes, people not keeping things up-to-date is also an issue. I believe I read in one of these other comments MS law firm that brought this action uses an outdated version of MS server. Taking action from new perspectives seems desperately needed. I think MS taking this action is a signal that new perspectives and new solutions are necessary. They risked and then made many people angry. (I will stop here. These are incomplete thoughts. Again, no flames please.)
Did you read the article? Sounds like you didn’t.
Yes, I did read the article.
+1 Reed!
– https://isc.sans.edu/diary.html?storyid=18329
2014-07-01 – “… a similar justification may be used to filter services like Amazon’s (or Microsoft’s?) cloud services which are often used to serve malware [4][5]. It should make users relying on these services think twice about the business continuity implications of legal actions against other customers of the same cloud service. There is also no clear established SLA for abuse handling, or what level of criminal activity constitutes abuse…”
4] http://blog.malwarebytes.org/fraud-scam/2014/04/cyber-criminals-interested-in-microsoft-azure-too/
5] http://www.washingtonpost.com/blogs/the-switch/wp/2014/01/16/amazon-is-a-hornets-nest-of-malware/
.
You use a service that also runs, hosts miscreants and botnet injectors.
You are surprised it came to this?
Excuse: I have ## computers to remote serve
Solutions: use TeamViewer, LogMeIn or other service or buy static IPs. You could bill for this, duh!
Excuse2: I paid for this service (but didn’t care to mention I also pirate-bittorrent movies…)
Solution2: you don’t say.
Seriously, M$ did a big unplug but like any tactic, you wait, and the No-IPs play a game that allows the charade to continue.
If a home user, there are programs that can mail your your IP if Dynamic. And if you are hosting a server, how about being serious and get a cheap hosting service…(but you will pay for No-IP…sounds fishy to me).
Hucklenead,
The services you use are likely to be used by miscreants so you should expect you service to be disrupted as well in the future.
By the way no-ip.com only provides hostname to dynamic ip mapping. It does not provide hosting services. The actual hosts are run by other providers or the miscreants themselves.
TeamViewer and LogMeIn are also abused by miscreants. One called me just last week from a spoofed phone number supposedly from Microsoft tech support asking me to download logmein so they could help me disinfect my Windows computer. TeamViewer and LogMeIn should also be shut down by that logic.
Microsoft Azure cloud and Amazon AWS services actually host miscreants, they should also be shutdown.
I do not believe it is possible to provide a service to millions of customers and have no miscreants among those customers.
I agree with all of the above from Scott. I have a long time small BB that is essentially a honey pot for a lot of miscreants (the bot spamming kind). I block addresses from hosts that spam me. There are some AWS and Cloud addresses but not that many, relatively. I looked up noip.com primary IP address and I have no blocks associated with it.
If you think about it’s purpose, and that it doesn’t host, then you can see that it is just a means to for the miscreants to switch malware host IP addresses while it’s bots just look at a noip address. We frequently read that they do this (you can shut down a host but the bots find another one) but a commercial service is pretty duh as far as stopping it.
MSFT could have just started scanning noip’s routing destinations and checked for malware (as search and AV software does with Safe Site checks) and shut down the connections to malware hosts. But that would have taken all of an hour for one of MSFT’s .NT programmers to write a loop. Way too much trouble.
I like being able to have a easy to remember name to log in to my VPN to securely access my computers or safely use public wifi. Its frustrating that M$ can do this and stupid that a judge allowed this. I don’t need to pay for a host when my own machines work just fine.
Knucklehead,
Excuse: Yeah this all sounds good to you I’m sure but static IPs can be quite expensive. As far as TeamViewer and the like, this puts a Man-in-the-middle who one has no control over, I doubt your customers would like that.
Excuse 2: That’s a mighty accusation from you. You’re as bad as MS. Even if the real number were 18,400, that’s still only 0.0043% of the user base. Hardly enough to accuse someone here of serving pirated warez.
Bla bla bla, I do not need to wade through a bunch of emails to find a cuurent IP address.
The charade has been that MS has been allowed to flood the world with OSs that are quite easy to exploit.
MS is only half of the problem here. We also have a judge somewhere in Nevada who thought this was a good idea.
Repercussions for interrupting so many legitimate users should be severe and should include the court personnel who create these problems by ruling on stuff they do not comprehend the consequences of… Obviously due diligence was not done in this case…
Like in any court case, it’s stupid (in my own sense) that all it requires is a court order from a single judge who most of the time knows nothing about IT…
I’m not surprised such steps were taken by Microsoft. Its just confirmation that maleware is getting out of hand and companies are getting desperate. Its the responsibility of domains to actively prevent it from being used by malicious software and cybercrooks. They might not think so, but the courts are now allowing these strong measures to curtail it. I suspect we will see more of what Microsoft has done.
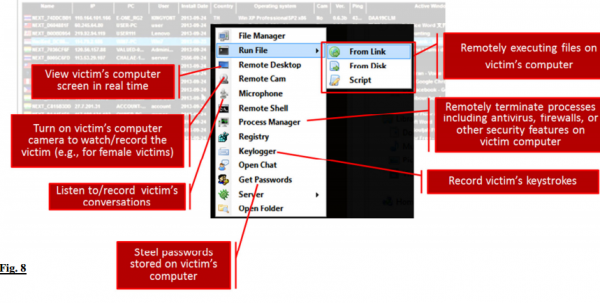
Better be careful…they’re out to “Steel” your passwords! Look at figure 8.
From http://www.zdnet.com/microsoft-sues-to-take-down-another-malware-gang-7000031093/, the 7.4 million infections attributed to these no-ip.com hostnames were over a year period. That is 20.3 thousand infections per day. If there were 2000 malware serving hosts on the day of takedown, that means each host is responsible for about 10.13 infections each. The 18,400 number that Microsoft gives seems to be about a week of observation. That is 1/2 percent of the 4 million hosts taken down.
The problem I see is far too much collateral damage for the scope of the issue. No-IP does not allow miscreants to abuse it’s service nor ignore them either.
Microsoft has higher numbers and percentages of shady sources running through it’s services. So Microsoft themselves could be accused of being friendly to the miscreants. Should the same solution of takedown be applied to those Microsoft services? I hope not.
Should your ISP be shutdown for 1/2 percent of it’s customers being miscreants? Should your email provider? Should your town or city be walled off from the world due to 1/2 percent of it’s population being criminal? I hope not.
I am all for shutting down criminal operations. I cannot justify harming 99% of a large population for the criminal acts of less than 1% of that large population. There are better ways.
Small edit, word occurs twice:
“In tandem with the action against no-ip.com, Microsoft also named and accused accused two men”
Wow talk about over reach, I’m with Dmitri try that on AWS, they never respond to abuse reports, EVER.
I read the lawsuite and MS seems to have a pretty compelling case. Symantec, Cisco and others and have also called out no-ip for failing to take action against abuse.
One of the interesting points made is that these dynamic ip services -which are free no less – are set up to avoid the normal regulations and accountability that the DNS system was set up to enforce. So now you have these companies like no-ip that are enabling all kinds of sleazebags (admittedly a majority of their clients) to disguise their activities by constantly changing ip address.
Please explain to me why all these legitimate businesses can’t afford the $10/month that a static IP requires?
I’m glad MS took these guys down. Regrettably as Spamhaus has shown collateral damage is one of the only things these “biznessmen” understand.
It’s more than $10/month. That’s advertised, but then there are other requirements. Also, it depends on your ISP. Ours charges much more than that! Instead of giving a 1-to-1 connection, we get a block, no option. Another of our providers (different location, different ISP, namely Frontier) horribly wastes addresses in blocks of 4 (network/broadcast/their side/our side). It could be set up as a /32 network, like Qwest would do (don’t remember if CentLink does it the same now). That system wasted no addresses.
Pookie:
The cost for a static is typically the difference between the cost of a home connection vs. a “business-class” connection, typically much more than $10/mo (closer to $40-50/mo).
I use no-ip (previously used dyndns until they dropped the free service) to connect to my home network using OpenVPN when necessary to help my wife & kids with problems, or grab files I may have at home.
My brother uses no-ip to host a minecraft server that his kid and my kids play together on.
Are you calling us criminals? Is no-ip evil for providing this service “for free no less”? Are you out of your mind?
And if you’re so damned insistent on this, why are you hiding behind an anonymous name, “Pookie”?
Having worked in DNS for a long time the only oversight it gives is someone had a credit card number, not necessarily theirs. When you’ve done the charge back and cancel cycle a few times, and blacklisted most of west Africa, and Romanian cafes as places that can buy your domains, you’ll realize it is a make money scheme not some sort of accreditation scheme.
People use no-ip for lots of services, and I’ve seen lots of legitimate website domains aliased to the no-ip address. Often non-profits, or fun projects. The Internet is also bigger than the web.
The question of if they were responsive to abuse requests can be asked legally without taking down the service first. Looks like Microsoft messed up big time.
The court order gives them permission, I assume it doesn’t protect them from liability. Folks affected who feel aggrieved can speak to a lawyer, lawyers like nothing more than targets with large piles of cash and well documented actions.
In no way are the abusers “admittedly the majority of customers”.
Dynamic DNS does not permit an end user to “change addresses to disguise their activities”.
You may have read the lawsuit, but you fail to comprehend the operation of dynamic IP address assignment methods, DNS resolution.
I applaud your tenacious grasp of generalization, and acceptance of ends justifies the means measures. They certainly complement the ethos that Postel and others embraced to gift us with the Internet.
You clearly don’t understand how that service works, do you? Those DNS services are used to redirect a DNS to a new IP assigned to a client BY THE ISP. The ISP keeps track of the IPs and the transactions that have been through, so whether the activity was illegal or not, the ISP can link the IP to the client.
Killing 4million sites to take out 2k bad actors seems to me to be the Internet age equivalent of use of a general warrant. Who is this judge, why is MS acting as an LEO, and not the FBI doing this, what is the standing that allows for this massive seizure of private property by another private company. In my mind this is the equivalent of Bestbuy getting a warrant to remove a single cell of terrorists in a city by getting a warrant to search the entire city, and then keeping the property after. No-ip should have zero problem finding a judge to stay this warrant in part or whole, at least until a hearing on this has happened.
Why Nevada? Is No-IP headquartered in Nevada?
Or is this just court-shopping, to find a judge willing to sign off on Microsoft’s preferred tactic? They usually opt for a Texas court for those…
From the complaint: “Defendant Vitalwerks is a limited liability company registered in and operating under the laws of Nevada.”
Vitalwerks is the corporation running no-ip.com.
ANONYMOUS
TAKE DOWN MICROSOFT BIG TIME !
perhaps you should get a real job instead of trolling security blogs. now go play out side in the sun, you seem to have a vitamin e and d deficiency. besides you never were anonymous, we never knew you.
I think the No-IP people should have done a better job of reviewing their network. This is not this first, second, or third time they were notified their network was hosting malware. They obviously have a pattern of only fixing the problems when they are notified instead of being responsible stewards of the Internet and monitoring how their system are being used.
Since they willfully ignored how their network was being used, somebody took it away from them. It sucks there are people caught in the crossfire, but you should direct your anger to No-IP for running a shotty network with loose regulation. Microsoft only got fed up with their ignorance and fixed a problem that needed to be fixed.
Steve,
they aren’t hosting malware, they are providing DNS.
The traffic to them would be DNS lookup and responses. Whilst it is probably possible to figure out some bad behaviour from patterns in traffic, and the traffic is likely cached, so most of the queries come from valid DNS servers. Almost by definition DNS providers are never the problem.
Spent a lot of time thinking about this previously, and my main concern with taking out DNS services was that the structure of the Internet provides no indication what the effect of taking out a domain name is. It is very hard to gauge the impact of a change. Most domain names have little impact if removed, but unless you know the services under a domain name (which can be other name servers), it is very hard to predict to impact of any change.
In some ways this is a protocol design flaw with DNS, on the other hand it should be a big hint to Law Enforcement and Courts, that DNS is generally not your problem, leave it alone. Unless people are distribution dodgy content in the DNS itself, there is little to gain by taking it down. The main exception would be like recently registered domain names obvious designed to be used fraudulently (bank phishing). But where a domain is established, has, or likely has other significant uses, it is folly to take it down without co-operation of the owners.
Yeah! Digital terrorism on the highest level… Iam a legal user of no-ip and have webcams using no-ip to monitor my 81 old mom and to see if everything is ok with her if iam on travel.
This means for me now as private and busines user, do never.. never use any service hosted in the US. The way how Microsoft acts is unbelievable and if it happens one time than it will happen a second time.. Which service will be the next? Azure taken over by Amazon or Google taken over by Samsung? Malware websites can be found thru Google, illigal content on some Servers hosted by Azure? Great job, really a great job and there is no excuse for acting in this way.
It figures it was a judge in Las Vegas, where corruption reigns… They have a large footprint in Reno (their whole licensing division is headquartered there), so why not file it there?
Maybe Microsoft blundered here. No-one minds if a few thousand miscreant websites get taken off air, it’s the collateral damage in this case that raises eyebrows.
Heh, this would explain why my SIP server is inaccessible from devices outside my home network…
I like the analogy of swatting a fly with an atom bomb. I wonder what is next from MS. Actually dropping an atom bomb on the city the data center a bad actor has their tools in? I’m sure they have someone working on it deep underground in Redmond, after all, it requires no permission from anyone that way. Hopefully said bad actor will be using Azure and they’ll bomb themselves out of existence.
I missed the technical bulletin explaining that the Nevada courts are now in charge of the Internet.
If companies that want to wildly swing a big stick can venue-shop for a court that is computer-illiterate, this is going to get ugly fast.
Microsoft’s lawyers, Shook, Hardy & Bacon are running their noticeoflawsuit site using IIS 6.0, which is unsupported and heavily exploited.
They’re obviously creating a hazard to the rest of the Internet, and should be shutdown until they clean up their act.
If MS spent half the money they spend on legal developing quality secure software this kind of thing would not happen. MS makes it to easy for usres of its roducts to be stupid users.
G
I am a paid user of noip.com. Have been for several years. When we first started with them, static ips wer not $5 more a month. It cost $250 a month for business class, and most of my small clients could not afford it.
This blunder by Microsoft has taken down over 5,000 devices that our software connects to for gps logging to determine the location of vehicles for the safety of the drivers. Today our customers were forced to pull their fleets in and re-program their devices so that they continue their business.
Grant it, static ips are cheaper now, in some markets, but there was no warning about this “denial of service” by MS. It shows the over reach of our court system. We had no preparation, no way to warn our customers, and handle the problem in an organized fashion. Go MS. This is why MS is losing in the device war. They are beginning to lose their grip and want to remind us all of who they are.
I can’t tell you the number of times I have had to fix something because of a MS OS issue. They are pathetic.
Noip.com got notification of one day or less? I hope that they can get this stopped. My staff will be working for days to get this corrected. And on a holiday weekend?
Thank you again, MS for your great consideration to your customers.
Not defending MS here, but have you considered that this has also exposed a flaw in your implementation?
If this is critical to your business, you should have multiple DDNS providers, so in the event one goes offline you have backup means of communication. You should consider this a (very, very rude) wakeup call to have a more robust implementation.
Businesses like noip go out of business with little warning all the time; get bought by a competitor who shutters their service, get bought by a larger corporation who plunders their IP and shutters the company, etc.
Even if Microsoft didn’t pull this poorly thought out & implemented maneuver you would have been bitten eventually. Best of luck on the cleanup though, personally I hate rude surprises like this.
You are running critical enterprise level services for your company over IP’s you don’t control and it’s M$ fault your system went down?
I couldn’t access my home cctv now because of this 🙂
Ooopps.. wrong emoticon.. 🙁
I’m hearing that thousands of families using no-ip domains to keep an eye on aged and frail relatives are now unable to do so.
Their web cams or other monitoring systems that allowed them to check in on Nana to make sure she’s up and about daily are now shut down thanks to Microsoft. Nana’s independence is now potentially compromised. She can’t stay in her own home by herself without someone looking in on her. She either has to go into a home or the family might need to move someone in with her. I know it sounds a bit big brother, but many older people like to stay in their home and this is one means of doing so.
Leave no-ip out of the equation for a moment. What right does Microsoft have to impinge on the rights of honest law abiding citizens.
Law suits will not come from just no-ip, I see a class action of epic proportions from the other 3.980 million users. From those running web cams for family reasons, small businesses struggling to make ends meet and all manner of people will be involved.
This clearly shows that two things need to happen now:
1. DNS must be repaired, so this sort of US-backed domain hijacking can’t happen again.
2. Microsoft and Windows must be eradicated from our Internet, because it’s finally damaging low-level infrastructure at a large scale. TCP/IP is a Unix protocol suite anyway.
If this had happened 20 years ago, Microsoft would have been completely de-peered already.
And we should add in all of the linux and unix hosts.
http://blog.eset.ie/2014/03/18/operation-windigo-malware-used-to-attack-over-500000-computers-daily-after-25000-unix-servers-hijacked-by-backdoor-trojan/
Did any of the whiners here actually read the court documents?
I didn’t think so.
I’m surprised no one has commented on what has to be the most telling example of hubris in the entire lawsuit; One of their ‘experts’, in his declaration to support the TRO, said this.
“.. Microsoft’s goal is to cut off traffic to “illegal_1.no-ip.biz,” while allowing traffic through to any other sub-
domains, if there are any such sub-domains at all.”
If there are any such sub-domains at all?!? Really Microsoft?
I use No-IP to access home and office. I use the same domain for both. Unfortunately I can’t access my home but fortunately I can access the office. I can’t understand why any court would or could grant a private company like Microsoft such vast power over individuals. It seems to be a violation of the US Constitution.
Please READ and EDUCATE yourself as to why the actions were taken.
It’s all here: http://www.noticeoflawsuit.com/index.htm
READ and EDUCATE yourself:
http://www.noticeoflawsuit.com/index.htm
John,
having read it, all it confirms is Microsoft don’t have a clue what they are doing here. They really screwed up.
Put it like this, they took over 4M domains with a system they hadn’t tested, with both servers in the same class C, and not producing correctly formatted answers, reminds me of the incompetence that took Microsoft DNS of the net with a single router fault many years back. These are not competent people to run a large DNS installation. The problem is we have to wait for legal systems to act, as Microsoft hasn’t yet admitted it is not competent to proxy this service, how long does it have to be down before they’ll admit their incompetence I wonder.
I doubt it is really 4M active users, on the other hand we know how spammers and scammers operate, and we know they create lots of accounts. So it is hardly any surprise there are a lot of accounts that use to be used by dodgy people, if they have found any use for the service what so ever.
Funny thing is I’m not a no-ip user, just an ex-DNS consultant, now doing security stuff, but I’ve seen enough no-ip aliases in my previous employers userbase to know you don’t prat around with it.
Criminals use banks to store their money, maybe shutting down all bank accounts will fix the problem.