“Please note that [COMPANY NAME] takes the security of your personal data very seriously.” If you’ve been on the Internet for any length of time, chances are very good that you’ve received at least one breach notification email or letter that includes some version of this obligatory line. But as far as lines go, this one is about as convincing as the classic break-up line, “It’s not you, it’s me.”
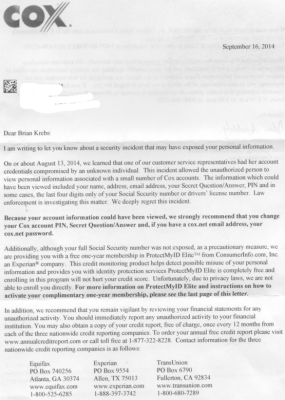
I was reminded of the sheer emptiness of this corporate breach-speak approximately two weeks ago, after receiving a snail mail letter from my Internet service provider — Cox Communications. In its letter, the company explained:
“On or about Aug. 13, 2014, “we learned that one of our customer service representatives had her account credentials compromised by an unknown individual. This incident allowed the unauthorized person to view personal information associated with a small number of Cox accounts. The information which could have been viewed included your name, address, email address, your Secret Question/Answer, PIN and in some cases, the last four digits only of your Social Security number or drivers’ license number.”
The letter ended with the textbook offer of free credit monitoring services (through Experian, no less), and the obligatory “Please note that Cox takes the security of your personal data very seriously.” But I wondered how seriously they really take it. So, I called the number on the back of the letter, and was directed to Stephen Boggs, director of public affairs at Cox.
Boggs said that the trouble started after a female customer account representative was “socially engineered” or tricked into giving away her account credentials to a caller posing as a Cox tech support staffer. Boggs informed me that I was one of just 52 customers whose information the attacker(s) looked up after hijacking the customer service rep’s account.
The nature of the attack described by Boggs suggested two things: 1) That the login page that Cox employees use to access customer information is available on the larger Internet (i.e., it is not an internal-only application); and that 2) the customer support representative was able to access that public portal with nothing more than a username and a password.
Boggs either did not want to answer or did not know the answer to my main question: Were Cox customer support employees required to use multi-factor or two-factor authentication to access their accounts? Boggs promised to call back with an definitive response. To Cox’s credit, he did call back a few hours later, and confirmed my suspicions.
“We do use multifactor authentication in various cases,” Boggs said. “However, in this situation there was not two-factor authentication. We are taking steps based on our investigation to close this gap, as well as to conduct re-training of our customer service representatives to close that loop as well.”
This sad state of affairs is likely the same across multiple companies that claim to be protecting your personal and financial data. In my opinion, any company — particularly one in the ISP business — that isn’t using more than a username and a password to protect their customers’ personal information should be publicly shamed.
Unfortunately, most companies will not proactively take steps to safeguard this information until they are forced to do so — usually in response to a data breach. Barring any pressure from Congress to find proactive ways to avoid breaches like this one, companies will continue to guarantee the security and privacy of their customers’ records, one breach at a time.




Haha, love it. They *always* say this after the fact. The biggest joke around.
oh lookie. Cox’s employee login page
https://insite.extranet.coxenterprises.com/dana-na/auth/url_0/welcome.cgi
Why wouldn’t you at least use IP whitelisting for an application like this?
Astonishing.
Probably not – they may farm this job out to people who work at home, AKA Jet Blue. Logistically it requires more cost/pain to set up a VPN or issue tokens for two factor. Not to mention all the folks who have problems with using a VPN/tokens.
At least a cert on the home PC. It’s better than nothing and restricts log on.
If your core competency is to facilitate ‘Internet connectivity’, then providing VPN support for your own employees should be a no brainer. There is no excuse for this ISP’s security posture.
+1
Yup,
Minimal measure is to authenticate the source network. Otherwise, non-socially engineered employee may simply have fun perusing client data from home.
Autorized access, but inapropriate use. They go hand in hand, in my book
cgi you say… wonder if they’ve patched the bash bug?
I was wondering the same thing.
It appears to be a Juniper SSL VPN. Juniper states they are using Bash, but “scenarios required for known remote exploitation vectors do not exist on these products”. Heh
http://kb.juniper.net/InfoCenter/index?page=content&id=JSA10648&actp=RSS
SHOTS FIRED!
I know what we continually pound into our users heads is that IT will never ever ask for login credentials over the phone or by email. If anyone does, they are supposed to report it to IT security. Unfortunately, when your userbase consists of thousands of college students and hundreds of staff, the message doesn’t always get through to them. That’s why (particularly for student accounts) systems are monitored closely for logins that are outside of normal locations, or too close together timewise from different geographic locations.
Cox probably has contracted support staff worldwide that need access to their system. However, I would think a VPN tunnel would be preferable to opening up their private customer system to the whole world.
But that would require extra work!
One of the bigger questions is why does Cox need your Social Security number!
So they can put something nasty on your credit report if they don’t get their cable box or modem back.
Brian, how worried are you that the your information was specifically searched for? Possible that the person(s) behind this knew who your ISP was?
That was the most interesting part of the whole article. Out of Cox’s entire customer base only 52 names were specifically searched for, and Brian’s was one of them. So who, I wonder, were the other 51?
@Peter,
The SSN was originally collected, and I believe still is, to get a credit check for service activation and then also adopted as a means to verify identity–which is why the associate could see it. Old habits die hard –especially bad ones.
“The nature of the attack described by Boggs suggested two things:”… I would like to add a third. Based on the reply you received from COX my bet would be that they outsource this particular service and their “Risk Assessment” was based on very bad information and or recommendations.
Doesn’t really matter that the representative was a female, does it?
Of course it doesn’t 😛
I shared the information about the rep’s gender because the spokesperson did. Take it up with Cox.
That was the first thing that caught my attention too. Why on earth would the gender matter? Thanks, Brian, for giving us that little tid-bit too. Poor unwitting girl tricked by a big bad wolf…
You guys would be whining if he left the details out too…
The fact the spokesperson mentioned the gender, is one thing. If you were reporting on the company’s gender attitudes and made the point that the spokesman offered up that information for no apparent reason, including it in the story would be relevant. As it wasn’t part of a direct quote, it seems extraneous at best.
So often, “female employee” is used because of the standard that we credit women separately from “workers,” that it has carried over to where it gets used no matter what. In this case, she was a perp and not to be credited. If something positive is said about a “female employee” who was particularly helpful in a good way, no one would balk at the use of the word “female.” BK just passed along the quote.
Yeh, the attacker had the keys to the vault and only took data for 52 individuals is strange. Seems like Brian might have been the target.
Makes me wonder who the other 51 were. Were they chosen at random to disguise that Brian was the target? Were the others also high value targets given where Brian lives and the concentration of possible high value targets in the area? Perhaps Brian was a decoy target and the others were the real targets.
My guess we will find that a 15-year-old was responsible, and that most of the other 51 were this kid’s friends and enemies.
Another person trying to get your address to send you a gift?
Just think of it this way Brian: Some 15 year old kiddie so hates you he’s willing to risk 10 years of PMITA federal prison to get your information.
You get such great friends.
52 (credit) card pickup anyone?
The number is probably close to what the rep had pulled out of the customer database and worked on for that day.
More than likely the rep didn’t have the main database up, if thats even possible. Cox Communication typically asks for an account name/ company name and the PIN associated with the account to access the info. So if the did jack her, they potentially could see the records she accessed since last reboot or browser flushing.
Hey, it happens. All a crook has to do is dupe the caller ID to say the same business name and people let their guard down. The password bit, yeah, I guess she didn’t read the good ole’ Snowden tactic, eh ? You should never reveal a password to anyone. IT doesn’t need a password UNLESS you call them and are having login issues, and then, immediately reset the passsword on next login.
With all the stones that Brian has turned over and created a story about, I am sure there are a few that may go out of their way to either get an legitimate private email address or address and phone numbers. Even though some of the crooks may have that data, it doesn’t need to be smeared all over the internet, unless Brian wants to have a book signing in his front yard.
In 2002, California introduced the S.B. 1386, “The California Database Security Act” (http://www.leginfo.ca.gov/pub/01-02/bill/sen/sb_1351-1400/sb_1386_bill_20020926_chaptered.pdf)
The first state in the US to enact such legislation.
My understanding is some of the reps work from home via SSL VPN. I know for a fact that the dish network does that as I had several classmates last year working for them doing tech support/customer package upgrades.
Onstar does same thing.
and to add to that a bit, I used to live next to a person working for onstar who used an unencrypted wireless headset for their land line phone. I could hear everything said for the onstar calls. CC info, names dates, etc. I didn’t intentionally listen, it would just pick it up from time to time
the police scanner would pick it up
For me, free monitoring services are like a promise to call after a one-night stand … it doesn’t materialize, just like my free monitoring promised by Target never materialized. And this was after I clicked on their email offer twice.
i got mine from target. It had to be same email used with redcard, But you are right.
I called my bank after the home depot hack because I use my debit card there all the time. I said I wanted a new one because it was used at target and home depot and both had been breached. They wanted to charge me $12 for one, I said that was ridiculous and argued about who was responsible for charges if it was used fraudulently and they said they were, and I said then why not spend the 50 cents and inactivate my old card and save yourself, and me the headaches and they refused
OTOH, my bank had a real person call me to say they are sending me a new debit card because of the Home Depot breach. Kudos to them!
Nice that they called you and didnt just send a new card.other than that all this means is that their fraud department found the transaction so it never appeared on your statement. They dont just send you a new card because youve shopped there.
I work for a community bank and we absolutely did personally call each customer whose card had been used at Home Depot to alert them to the breach and to the fact that their current card would be restricted. We then ordered a new debit card for each customer and did not charge them for it. This was done to prevent fraudulent charges in the first place, not that we found fraudulent charges.
The community bank where I work did the same thing as Kelly…called the affected clients, limited account and reissued the card. It is a nice touch that big banks don’t do given their size.
more like someone handing you a condom after giving you an STD…
Great! Another reason for me to hate on Cox.
Like you should need a reason to hate a cable company?
My cable company likes to disconnect internet service in the middle of the night, when they think nobody will be using it. I sent a nastygram to the office of their president, asking for them to start notifying customers of outages, after one unscheduled outage went on for a couple days.
Even Comcast notifies customers when they’ve got scheduled outages, FFS… of course they don’t notify about unscheduled outages, but there’s no way my ISPs outages are unscheduled. They always start between the hours of 1am and 3am on a Tuesday or Wednesday, and always clear up before 7am. Maintenance window, anyone?
The cliché offer of free credit monitoring is like promising to close the barn door after the horse gets out. It does nothing to repair the damages done by a breach. Between the HD and Target breaches, is there anyone left who doesn’t have free monitoring? The question I would have liked to put to Mr. Boggs is, “How does free credit monitoring protect me from anything?” The answer is that it doesn’t, and at best is a lukewarm placebo to calm the ignorant.
The beat goes on. Received an email from Bank of America on 9/27 advising that they were issuing a new credit card to me. In bold type they explain “This does not mean fraud has or will occur on your account…..”
Have no idea what the problem was or if there even was a problem.
I am comforted in the knowledge that they take the security of my personal information very seriously.
“Have no idea what the problem was or if there even was a problem.” That’s getting more common these days. Without the sense part, it’s a problem.
Dress-Coded for Your Convenience
“There’s a reason armies wear uniforms even though they make them easy to spot. Sometimes that’s what you want. Uniforms suggest organization, power and numbers. These in turn inspire fear. And as any good operative knows there is no more effective weapon than fear.”
— Michael Westen, Burn Notice, “Hotspot”
Because you made purchases at Home Depot. I got the same letter and new card. I wasn’t one bit offended or put off.
Love the headline.
You suggest multi-factor auth and VPN as solutions, but since this was a phishing attack, I don’t think they would have helped.
Why do CSRs have access to such sensitive information as your drivers license number and social security number? They should at most have the ability to authenticate you *using* those pieces of information.
Cox’s suggestion to change your “secret questions/answer” drives home the insecurity of secret questions.
Did you read the whole post? The events were:
Miscreant contacts COX support claiming to be support staff
Miscreant talks agent into giving them her username and password
Miscreant uses these details to access the customer records using a portal that can be logged into via normal internet channels.
If a VPN was used the VPN could be locked down and require 2 factor authentication. For example I have 2 ways of getting onto my works VPN. I can use my username, password along with my ID card and pin (ID card slots into the laptop). Alternatively I can login via a website however I need a username, password and a one time password generated from a fob.
Having such a setup would have helped stop this miscreant gaining access instead of leaving the door wide open.
Because a CSR who gives his username and PW can’t be talked into giving up two factor auth info?
“OK great, so now to verify that I am talking to the right person we will need to use that RSA key fob thingie. Please read the numbers for me when they’ve changed the next time.”
People dont get security. Heck developers dont get security so what do you expect from some student CSR?
Sure they can, but it’s another hurdle. Also, as I mentioned in the story, having this stuff accessible via a portal on the Web that you don’t even need to VPN into is just dumb.
Oh I absolutely agree that it would add a layer of security and it may help with certain people. I’m also saying that for certain kinds of people it’s practically of no use at all. You’re trying to solve a people problem with technology. The fallacy is that you let people who don’t “get” security log in from the outside at all. I don’t believe that I’ve seen a technology so far that has prevented stupid users from making stupid mistakes.
As I said, what I’ve heard and seen from senior software developers in regards to these things makes my head hurt. I have had access on a big international bank’s internal network for two weeks while doing a small contract with someone else’s credentials because “it’s no use applying for a user and password for such a small timeframe. IT takes months to get that done”.
If you do have someone that understands security then two factor auth can successfully help prevent problems should credentials be stolen for example. If someone can be tricked into giving a password up then they will easily give up other authentication information as well. We’ve seen that in Europe where TANs were introduced for online banking. So crooks got people to enter a TAN and we were back to square one. Then indexed TANs were introduced so that crooks can’t just use a random TAN but have to have one that the bank chooses randomly for each transaction. And now banks are switching to SMS TANs even. All that will do is for crooks to create SMS reading phone malware.
Although I know this isn’t the point, and I agree with the premise that corporations do not care to take adequate precautions, the “personal” information listed, including the last 4 digits of SS#, and driver’s lic #, are very easily obtained on line. In Florida your driver’s lic info, including your address, is readily available & public information.
A few decades ago some states used a person’s Social Security number as the state’s identification number on the driver’s license. Texas was one that did not.
When I started college in 1974 the student ID had my Social Security number. Professors would post a sheet of test grades on their door with the student ID – the Social Security numbers. I did some volunteer work with the school newspaper for a few semesters and they had a computer printout of all the registered students and their Social Security numbers and addresses. The police station on campus also had the same type of computer printout.
In those days it was very difficult to get credit.
Who really does take security seriously anymore? Even the simplest of checks seem to be overlooked at all levels. This is somewhat dated but when someone on the FBI’s most wanted list can stand next to the president of the U.S. for a photo ops along with multiple senators, we might have some issues with messaging the need for improved security
http://abcnews.go.com/Blotter/bobby-thompson-fbi-fugitive-posed-president/story?id=17386614
Security is a 24×7, exhaustive and relentless effort with no room for complacently. Ever watchful, every questioning and never comfortable. When is your security good enough? Never is the answer, but unfortunately short sighted economics just enough funding philosophies override long-term strategic vision and vigilance. If the companies leadership or customers/constituents don’t care, why should you.
How many fortune 500 lead with their ability and investments to secure their customers information. Almost zero. Its that last thing on the list until they are hit with a compromise. Then they take it very seriously. At least in print.
Target remains the number one merchant for fraudsters to purchase gift cards with stolen credit cards. How secure do you feel knowing monies from these thefts is going to fund numerous illegal actives ranging from human trafficking to terrorist threats. Sure they take security seriously as long as it doesn’t’ decreases sales on high margin products.
Brian , wouldn’t you be compromising your security even more but telling people publicly who your internet provider is?
I can see the cyber-criminals in Eastern Europe now port scanning all of the Cox Communication net blocks trying to find your end point.
I may be mistaken but there are large sections of the US that have monopolies operating providing internet access.
It wouldn’t be that hard to ascertain where Brian lives and see who provides the area.
People seem to have easily found his specific address in the past as has been highlighted in previous posts (the drugs delivery, being swatted etc)
I would hazard a guess that as Brian was targeted with such a small pool of people that the perpetrators had a very god idea he is a cox customer.
Many DC/NoVA residents would know that there are two cable companies and one phone company that provide residential last mile service in Fairfax County (where Brian has acknowledged living in prior posts). Even without his address, that’s a 1 in 3 chance of him being a Cox customer (possibly more like 1 in 2 assuming he doesn’t have DSL).
It’d be a lot more of a stretch if they weren’t familiar with the DC Metro Area, unless Cox was specifically targeted for Brian.
And remember that the only reason we don’t know that they didn’t try the same thing on the other two ISPs is because Brian does have Cox. For all we know they were unlucky and tried the others first 🙂
The sad truth of the matter is that it is cheaper for companies to take the risk and accept the fines when breached than it is to pay for the security gaps to be plugged.
Look at the Sony breach for example in the UK they were fined £250,00.
The only other thing that companies need to be concerned about is their reputation but this tends to come back over time regardless. Companies probably lose more money from the loss of support from customers.
The annoying thing is it now seems to be the norm that small companies who have data breaches get heavy fines whereas large companies get a slap on the wrist.
Security is hard – and not just in the technical sense. It is difficult to define the right balance between secure and usable. Too usable and you risk breaches and public shaming. Too secure and you risk losing business because you’ve made yourself an unusable service.
You make the point that is is less costly for businesses to accept the risk and pay the consequences. I think more accurately, businesses have transferred the risk, and there is not substantial incentive to change the practice.
Ten years ago, a credit card number was stolen and it was “Oh !@#$” Now it’s “ho hum, I get another credit card.” Several responses to this post mentioned their banks proactively calling them and sending replacement credit cards after the Home Depot breach. I did too. Yeah, it’s a nuisance having to update my auto-pay accounts, but that’s the end of it. It didn’t hurt me. So maybe business models are evolving.
Of course, we are diverging from Brian’s original point … credit card breaches are very different from customer service portals that leak PII. Credit card numbers may be becoming throwaway, but PII isn’t.
Brian, wow, new look w/o the signature red baseball cap. We are doing payment security roundtable in N.Cal. Want to join us in November? You’ll be in good company. Messsage me @PaySecurityNews
I am lost here. Most security systems I know allow sensitive info to go in but never come out. Why does the cox system allow any customer service person look up pins, security answers, or license info. THe normal procedure is that they can take the infor from a user, save it, overwrite it, but thr way you verify the customer is them reading off the number, the CSR entering into the system and having the computer report a match. That way if the CSR account is compromised the invader can try to guess information for a user but they can’t just copy it down. Cox just has a pathetic system
So true! Answers are often simple if you are looking for them. I use cash and phone calls for for as many payments as possible. ;^)
“chF” Devin Bharath and “Criminal” Antonio Rodriguez posted screenshots of your account… lol
Wah geese! Don’t get me started on COX@#%r Communications!
>:(
Comcast is no better & possibly worse. I went to cancel my hybrid business account – waited over an hour to speak to a rep at the desk & was told I had a special account that they couldn’t handle there, call this number. I called & “Sorry can’t help, don’t really know how your do it, but I’ll check & get back to you.” (NOT!).
Security? We don’t need no stinking security! We got something waaaay better!
A monopoly!
That is just one of the reasons I called the FCC today to vote NO on the Comcast merger. Consumer’s Union reports that the servers are being bombarded over there, so bad the FCC has only been able to collect around 780,000 comments before crashing several times. I wanted to darn sure get mine in! It is better to do this through the Consumer’s Union action arm, as they are gathering data on this, if you call this number 1-888-598-4221, and you want to throw your weight behind the comment, leave the message to FCC Chairman Wheeler, your email. or phone number, and identify yourself – that way the comment is recorded and counted towards the period for public discourse.
A Google search on “we take the security of your personal data very seriously” returned 61,000 hits.
Scrolling down through these results makes me wonder what companies actually do take their client’s data security seriously.
Even if some of them care, can they be effective through the current wave of cyber crime where the criminals clearly have the upper hand?
Yeah they care as far as when they get in trouble and are looking at huge losses! Before then, they could care less – typical junior gee man executive action(or in-action more likely)!
I they really did take it seriously, they would have been locking their systems down, and probably trying to exceed PCI standards to prevent what happened last year at Christmas time!!
The other type of hollow statement that usually follows “We take your privacy and security seriously” is…
“There is no evidence that any of the records affected by this illegal action have been abused.”
I’ve always believed this is purely a statement their lawyers make them say to calm customers down. But I have no idea what actual legal defense it provides.
On the bright side, if you play your cards right, and can manage to be a victim of a breach every 12 months, you can look forward to a lifetime of free credit monitoring…
It’s a non-committal statement with the intended purpose of inferring there was no breach without actually guaranteeing it.
It’s damage control without making any binding legal promises.
Brian, I think I reported this here before, but months ago, maybe last year, I got a couple of calls right before my Time Warner Cable bill was due. These smooth-tongued devils knew my name, apparently my account number, and said they were calling because my “TWC bill was overdue” and they wanted to “save me” from having my service cut off. Nice guys, friendly and well-spoken. They quoted an amount that was very close to the expected month’s bill. Then, they cheerfully asked me if I wanted them “to charge my card ending in yxxx (so I don’t get cut off!), the “y” being one digit off from real my credit card. I never voluntarily let stores or websites store my cc info, but the cable company?
The point was certainly for me to give them the “correct” cc number. If they gave me the correct full 4 digits, there’d be no point in me “correcting” the number. I could just say “yes, okay,” and then what? The first time I said no, that I would call TWC directly, the guy offered to charge my bank account! They were obviously phishing, but it was creepy. I told the first guy that I was going to call TWC. When it happened again, I said that I was recording and going to report them the cops! It stopped, but these guys were very convincing, and bold.
I did complain to TWC that someone obviously had some kind of access to my bill records. I called them several times, getting kicked up a level of management each time, but ultimately, TWC was neither responsive or helpful. All I got was a couple of lectures about “being careful of this type of call,” like I was the one at fault. Got a new TWC account number. TWC was my phone, tv, and internet ISP. Now I’m Verizon, but just another kettle of the same fish, no? Since starting to read KOS, I am paranoid and super careful with everything. I’ve learned things here at KOS that are out of this world.
Oh, by the way, my TWC bills were NOT overdue, but they were due!
I would be interested to know where the individual was located when accessing the portal. I am sure his connection was proxied but I would still be curious.
You would think that Cox would also (as well as those recommendations above) would block well known IP blocks of hostile nations from accessing this portal.
>>would block well known IP blocks of hostile nations from accessing this portal
That’s the big glaring issue to me, these systems aren’t even being put through the basic safeguards. Services are ported to the public facing internet WAY to often in the interest of convenience. Hackers LOVE convenience.
Brian, out of only 50 accounts, do you think they happened upon yours randomly (and unfortunately) or do you think you were targeted?
Speaking of Experian, has anyone seen their new TV ad campaign with the two towers in an empty warehouse, talking to one another? Ha! What a joke. They should be ashamed.