Federal prosecutors in New York today announced the arrest and charging of a San Francisco man they say ran the online drug bazaar and black market known as Silk Road 2.0. In conjunction with the arrest, U.S. and European authorities have jointly seized control over the servers that hosted Silk Road 2.0 marketplace.

The home page of the Silk Road 2.0 market has been replaced with this message indicating the community’s Web servers were seized by authorities.
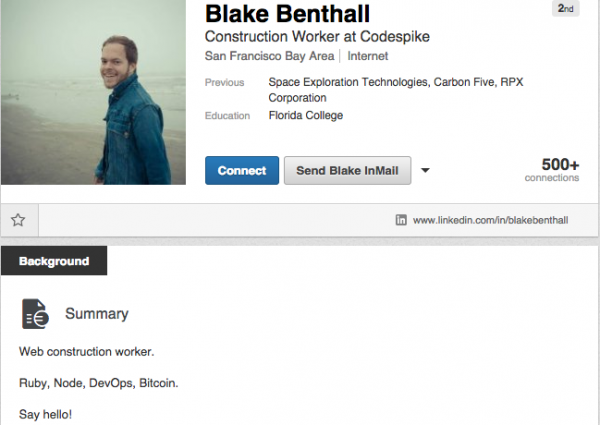
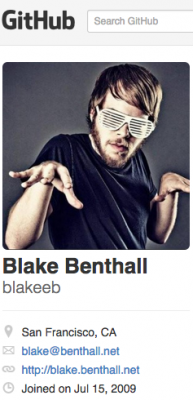
On Wednesday, agents with the FBI and the Department of Homeland Security arrested 26-year-old Blake Benthall, a.k.a. “Defcon,” in San Francisco, charging him with drug trafficking, conspiracy to commit computer hacking, and money laundering, among other alleged crimes.
Benthall’s LinkedIn profile says he is a native of Houston, Texas and was a programmer and “construction worker” at Codespike, a company he apparently founded using another company, Benthall Group, Inc. Benthall’s LinkedIn and Facebook profiles both state that he was a software engineer at Space Exploration Technologies Corp. (SpaceX), although this could not be immediately confirmed. Benthall describes himself on Twitter as a “rocket scientist” and a “bitcoin dreamer.”
Benthall’s arrest comes approximately a year after the launch of Silk Road 2.0, which came online less than a month after federal agents shut down the original Silk Road community and arrested its alleged proprietor — Ross William Ulbricht, a/k/a “Dread Pirate Roberts.” Ulbricht is currently fighting similar charges, and made a final pre-trial appearance in a New York court earlier this week.
According to federal prosecutors, since about December 2013, Benthall has secretly owned and operated Silk Road 2.0, which the government describes as “one of the most extensive, sophisticated, and widely used criminal marketplaces on the Internet today.” Like its predecessor, Silk Road 2.0 operated on the “Tor” network, a special network of computers on the Internet, distributed around the world, designed to conceal the true IP addresses of the computers on the network and thereby the identities of the network’s users.
“Since its launch in November 2013, Silk Road 2.0 has been used by thousands of drug dealers and other unlawful vendors to distribute hundreds of kilograms of illegal drugs and other illicit goods and services to buyers throughout the world, as well as to launder millions of dollars generated by these unlawful transactions,”reads a statement released today by Preet Bharara, the United States Attorney for the Southern District of New York. “As of September 2014, Silk Road 2.0 was generating sales of at least approximately $8 million per month and had approximately 150,000 active users.”
The complaint against Benthall claims that by October 17, 2014, Silk Road 2.0 had over 13,000 listings for controlled substances, including, among others, 1,783 listings for “Psychedelics,” 1,697 listings for “Ecstasy,” 1,707 listings for “Cannabis,” and 379 listings for “Opioids.” Apart from the drugs, Silk Road 2.0 also openly advertised fraudulent identification documents and computer-hacking tools and services. The government alleges that in October 2014, the Silk Road 2.0 was generating at least approximately $8 million in monthly sales and at least $400,000 in monthly commissions.
The complaint describes how federal agents infiltrated Silk Road 2.0 from the very start, after an undercover agent working for Homeland Security investigators managed to infiltrate the support staff involved in the administration of the Silk Road 2.0 website.
“On or about October 7, 2013, the HSI-UC [the Homeland Security Investigations undercover agent] was invited to join a newly created discussion forum on the Tor network, concerning the potential creation of a replacement for the Silk Road 1.0 website,” the complaint recounts. “The next day, on or about October 8, 2013, the persons operating the forum gave the HSI‐UC moderator privileges, enabling the HSI‐UC to access areas of the forum available only to forum staff. The forum would later become the discussion forum associated with the Silk Road 2.0 website.”
The complaint also explains how the feds located and copied data from the Silk Road 2.0 servers. “In May 2014, the FBI identified a server located in a foreign country that was believed to be hosting the Silk Road 2.0 website at the time. On or about May 30, 2014, law enforcement personnel from that country imaged the Silk Road 2.0 Server and conducted a forensic analysis of it. Based on posts made to the SR2 Forum, complaining of service outages at the time the imaging was conducted, I know that once the Silk Road 2.0 server was taken offline for imaging, the Silk Road 2.0 website went offline as well, thus confirming that the server was used to host the Silk Road 2.0 website.”
The government’s documents detail how Benthall allegedly hatched a selfless plan to help the Silk Road 2.0 community recover from an incident in February 2014, wherein thieves stole millions of dollars worth of Bitcoins from community users.
“On or about September 11, 2014, Defcon had an online conversation with the HSI-UC, in which he discussed, in sum and substance, his intention to reopen the Silk Road 2.0 marketplace, and his plan to recoup the deficit of Bitcoins that had been stolen from Silk Road 2.0. Specifically, Defcon confirmed that the site needed to recoup approximately 2,900 Bitcoins to cover the loss, and stated that he intended to donate approximately 1,000 of his own Bitcoins to return liquidity to Silk Road 2.0 (“I’m planning to throw my 1000 BTC to kickstart the thing.”).”
“Defcon further acknowledged that the site had approximately 150,000 monthly active users (“We have 150,000 monthly active users. That’s why we have to save this thing.”). The HSI‐UC asked how long it would take to recover from the theft, and Defcon replied that it would take approximately three months’ worth of commission payments, if sales on Silk Road 2.0 continued at a steady rate (“Three months if sales continue at current pace and we don’t bottom out”). Thus, Defcon appears to have expected Silk Road 2.0 to generate approximately $6 million in monthly sales over the next three months, which would have resulted in commissions over that three‐month period totaling approximately $900,000 ‐ equal to approximately 1,900 Bitcoins at the then prevailing exchange rate.“
Benthall’s biggest mistake may have been using his own personal email to register the servers used for the Silk Road 2.0 marketplace. In the complaint against Benthall, an undercover agent who worked the case said that “based on a review of records provided by the service provider for the Silk Road 2.0 Server, I have discovered that the server was controlled and maintained during the relevant time by an individual using the email account blake@benthall.net.”
“To me, it appears that both the human element, an undercover agent, plus technical attacks in discovering the hidden service, both played a key part in this arrest,” said Nicholas Weaver, a researcher at the International Computer Science Institute (ICSI) and at the University of California, Berkeley.
Federal agents also say they tracked Benthall administering the Silk Road 2.0 from his own computer, and using Bitcoin exchanges to make large cash withdrawals. In one instance, he allegedly cashed out $270,000, and used $70,000 for a down payment on a Tesla Model S, a luxury electric car worth approximately USD $127,000.
Benthall faces a raft of serious charges that could send him to federal prison for life. He is facing one count of conspiring to commit narcotics trafficking, which carries a maximum sentence of life in prison and a mandatory minimum sentence of 10 years in prison; one count of conspiring to commit computer hacking, which carries a maximum sentence of five years in prison; one count of conspiring to traffic in fraudulent identification documents, which carries a maximum sentence of 15 years in prison; and one count of money laundering conspiracy, which carries a maximum sentence of 20 years in prison.
A copy of the complaint against Benthall is available here.
Update, Nov 7, 9:01 a.m. ET: The National Crime Agency in the United Kingdom is reporting that the demise of Silk Road 2.0 was part of a much larger operation targeting more than 400 “dark web” sites. From their press release:
“The six people arrested on suspicion of being concerned in the supply of controlled drugs were a 20-year-old man from Liverpool city centre, a 19-year-old man from New Waltham, Lincolnshire; a 30-year-old man from Cleethorpes; a 29-year-old man from Aberdovey, Wales; a 58-year-old man from Aberdovey, Wales; and a 58-year-old woman from Aberdovey, Wales. All six were interviewed and have been bailed pending further enquiries.” Read more here.




It’s frankly mind boggling that he would use a real-world identity email address for this.
Typical…dumb criminal!!
But, by his own admission he was a rocket scientist.
I have to agree, it seems almost too stupid for a guy like that to do. With all the spoof and disposable email services out there that he would use his personal information like that. I have 0% faith in our government and it would not be above LEO in my opinion to lie about something like this. It’s one of those if it’s too good to be true kinda scenarios.
Bring on SilkRoad 3.0:D
Ha! I don’t think that anyone is stupid enough to try it again under that same branding. The Silk Road as well as it’s predecessor were too public, a quick Google search could find the URL and the name alone brought a lot of attention. From what I’ve been reading it seems the next gen of dark Web markets may very well be P2P, thus eliminating the central server of current dark markets. Similar to how after Napster was taken down torrents were born. Open Bazaar may be the next big thing in anonymous P2P dark Web markets.
“law enforcement personnel from that country imaged the Silk Road 2.0 Server…”
“the UC admin mentioned the logs indicated Brett logged onto the site without Tor and on chrome…”
Why would he turn the server’s logging on?
You’re assuming he did it. The UC admin could have enabled logging. It’s not like a huge red banner pops up when logging is enabled. Or he may have had logging enabled for his own purposes. When someone’s credentials get hijacked logging is quite useful.
What a maroon.
You are literally too stupid to insult.
Now you’ve gone and hurt my feelings.
Hahaha
You’ve never watched bugs bunny?
I’m not sure how much of the government’s complaint I’m buying. Just like the first Silk Road seizure – their explanation seems suspect.
Yeah I agree, I tend to believe the part about how a undercover LEO was able to infiltrate the site, after the SR 1 was taken down anyone trying to resurrect the site should have done their due diligence. But I think they may have hit a dead end in the investigation and simply falsified evidence to get an arrest and take the new site down too… looks for the agency.
Sill no information on HOW they located the hidden service though. Did the UC entered random characters on the login box?
Since an undercover agent was given administrative access to the forum, more than likely at some point he was provided with login credentials to the server, which was then used to locate the server. Or he could have simply placed a web bug into the forum that breached Tor for anyone silly enough to have javascript, etc. enabled.
It doesn’t help to keep your front door locked if you also give a copy of your keys to law enforcement.
Since the alleged owner registered the server in his own name, he probably didn’t do a number of other things “correctly.” Everyone likes to think they’re a mastermind, but more often than not you end up making a number of stupid mistakes that trip up your elaborate schemes.
Blake didn’t even use Tor and used chrome so its doubtful he had JS disabled.
Looks like the TOR network has some serious security flaws what are not revealed to the public.
Time to use GnuNet, i2p or something else.
>Time to use GnuNet, i2p or something else.
Those are probably even less secure, they lack the extensive amount of research and attention Tor had over the years.
In the complaint the UC admin mentioned the logs indicated Brett logged onto the site without Tor and on chrome. Considering the site was hacked at least once its not hard to imagine he had other vulnerabilities like XSS.
Benthall has been widely criticized for apparently having accessed at least some of the market’s administrative interfaces using normal connections apart from Tor, which obviously would reveal his source IP in that server’s logs. This criticism is valid however realistically, some out-of-band access is required for any environment, especially here as the Tor network will be up-and-down and its client software may need to be re-initialized. If those server logs were visible to the other administrators or teased out by any means, Benthall could have been identified (if the origin IP was traceable to him) even before the server was located, and the server location subsequently determined through, for example, a review of Benthall’s financial, telephone or other interactions with the colocation provider.
The following is very speculative, and admittedly very tin-foil-hat. I have NO evidence:
Beginning on January 30th, and ending on July 4th, an unknown group was conducting what appears to be a large scale deanonymization attack on Tor. This was probably the attack by Alexander Volynkin and Michael McCord of CERT, which was the subject of their cancelled-by-CERT lawyers blackhat talk.
The timeline matches: It would take a while for the group of relays they introduced to be utilized as a guard node for the SR2 hidden service. And running 200 EC2 instances 24x7x4 months = $50K, which is more than one would spend on a simple hobby project.
No tin hat needed, this how you would do it.
Own enough nodes and you can control it, so simple.
There is no issue with resources here, “they” have more than enough tools to exploit the design and protocols.
But, in order to stand up in court one would need to provide evidence that can’t be excused away, thus the manipulation of the documents and the need for a undercover mole to substantiate the “facts”.
More likely we would find that the network itself has been compromised and can be used for purposes not intended by it’s users.
Amazing. Aren’t they the ones that sent you a present via mail? LOL Twits!!
He got that package via the old SR, before DPR was apprehended.
No, you silly girl
Thanks Brian for the highly readable analysis of what transpired leading to the downfall of yet another criminal enterprise that exploits technology to make millions. A deftly written piece of journalism, succinct and to the point. You’re a top notch tech journalist keeping the public informed on the latest threats and scams. Keep up the excellent work.
Yeah, because every single person that utilizes the silk road is a criminal /s. Please.
I would love to hear a bit more about legitimate business being conducted on Silk Road 2, if there is any. All I ever read about are nefarious enterprises, be they dealing in illegal substances/services, fake merchandise, money laundering or other underground trade. Perhaps in my ignorance I just assumed the main reason one deals on a web clouded from visibility via onion routers and whatnot, was to hide from laws, taxes, etc.
So since you seem suggest this isn’t the case, tell us a bit about what totally legal commerce occurs on Silk Road and if you can, explain why legitimate vendors would choose to operate on a site like this.
I have an open mind.
If you purchase, sell, or facilitate the sale of illegal goods or services, you are, by definition, a criminal.
And that’s the key point: only by definition.
Legally, yes. Morally, no
I don’t think the definition of ‘criminal’ includes anything about morals.
I posted a reply to E Nigma here. I know it posted as I checked it right after it was submitted. It is now missing. There was nothing insulting in the post, whatsoever. I can’t figure out why it was moderated off the comments. Anyone?
Never mind. After missing for several minutes it is now back. Odd
And my comment is missing once again. Last I saw it it was back and said “awaiting moderation”. Apparently since my comments made since that are still here, it was moderated out. I’d love to get an explanation as to why it was deleted.
More likely he was a “bitcoin scientist and rocket dreamer” rather than the other way around….
Clearly a coordinated action, and probably at least part of the reason they waited so long before effecting an arrest.
Not only was Silk Road 2 seized, but also Hydra, and Cloud9 (smaller Darknet Markets) and the forum for Cannabis Road (the market was defunct but the forum stuck around).
TOR and all the little onions should be hauled off to prison.
Brian, what area are you working on now? How soon we can expect another amazing story ?
Hydra, Cloud9 and The Hub also showed the “Seized by FBI” message, but now are all down
Yeah, what a real dirtbag. Such a scumbag criminal, lock him up in cage where he belongs, ForEver!! Guys, First though, Can we please, Make sure you Steal (uh.hemm) I mean, Seize, every single bitcoin, penny, and item he has first. That way the stolen goods, (uh.hemm) I mean Assets Seized, can be sold and diverted to revenues, for our enterprise (uh.hemm) I mean organization. Since we are gonna launder it all (uh.hemm) I mean, Show as a Tax WriteOff so our sister agency and helpful colleagues at the IRS can look the way when it comes to the mountains of all the money and assets kept to ourselves (uh.hemm) I mean spent and utilized properly. Example, We need to use these revenues to hire as many criminals (uh.hemm) I mean law enforcement agents as we can get. so more theives (uh.hemm) Agents, I mean, can be hired to protect the sole totalitarian authoritarian ruler and forever to be the only Drug Dealer on the block with full power (uh.hemm) I mean DEA under the US Govmnt continue mandated supervision of the worlds transactions., and interests thereof. Its people like this dirtbag, that make me realize how much I love my job and hate myself. Good job to all us self rightous douche bags with our heads up our asses (uh.hemm) I mean double standard tax payer teet milking, (Uh.hemm) damnit….Sorry guys, I mean protectors of the freedoms that we control for the American people. Yeah, thats it. Okay lets go play some GTA in real life on the streets of Mexico and kill a ton of people (Uh.hemm) I mean, and protect everyone here in our country substituting more heroin production! We’re gonna shut down a couple huge pharmaceutical manufacturers next week, so we need to really be picky about who we are gonna vote in to be the head heroin production supervisors (uh.hemm) I mean new cartel informants. Oh on last thing, Be sure to lock that criminal in the same cell as that murderer guy, that one guy that rapes dead bodies, the cannibal criminal, the other child rapist, and adult male butthole serial rapist, alongside the decapitating serial killer, oh and don’t forget the mafia hitman too, along with extortion expert, guy that is always assaulting innocent people, BTK, and the rest of the criminal dirtbags that are the same kind of person as this POS.
People do not like reading walls-of-text.
Lock em up for life.
Now, if they can just get the other two dozen bazaars like BlackBank we could all sleep a bit better.
Looking forward to your book in a few weeks.
Carl
Clearly plenty of operational security errors were committed here, starting with rebooting Silk Road with largely the same set of principal players that had all just been involved with / likely doxxed during the Ulbricht-era takedown. Apparently an undercover agent was hired on almost immediately and given at least some level of administrative access.
As with the Ulbricht-era bust, the FBI here still does not spell out exactly how the server was located physically, but there are plausible ways that this could have happened. Keep in mind that a LEO was hired as an administrator. Administrators can typically see network configuration. Even a “front end only” administrator may be able to tease this information out by manipulating the interfaces. More advanced attacks against the Tor network itself are also conceivable.
With regards to Torified HTTP as a blackmarket platform, I’m of the opinion that this is not likely a robust solution against an intelligent and resourceful adversary such as the FBI. For one thing, the FBI undoubtedly has canned exploit payloads for modern web platforms that can be delivered against online systems including through a Tor tunnel to an HTTP endpoint. Even if the target system is correctly isolated to an internal-only network – a level of protection that fallen blackmarket operators have not apparently deployed to date – compromising the HTTP server would leave the adversary at most one hop away from the actual Internet-conected machine. So the one system could be used as a bridgehead to then compromise the adjacent gateway.
One would think that each generation of these sites would learn from the mistakes of the prior ones, but this does not seem to actually happen. What we see commonly is that the people who are actually undertaking these ventures are not actually the most technically qualified people, and the FBI does not necessarily reveal all of its true methods. In all of this I think the FBI is leaving out some bait, essentially allowing observers to believe that the busts which occur happen only because the site operators are sloppy, and so further operators launch with the Torified webserver approach that’s expected by users rather than something more exotic.
The upshot is that an illicit webserver provides a massive attack surface and this favors the FBI since they are extremely capable. I don’t think this calculus changes until somebody actually deploys a more decentralized, peer-to-peer based network, perhaps using some more sophisticated cryptographic underpinnings.
This is exactly what tor was originally trying but a real p2p network requires many computers connected to host it properly. Its like creaing a cluster where the nodes are distributed… now the same comcept can be applied to seize this parallel p2p network: own as many nodes as possible as the agency is doing for entry and exit points.
Conceptually thr defense against any anon network is the same…
I’m still not sure if the focus should not be on how the heck this illegal substance s are getting into / being produced though…
The website for the above-linked Benthall Group, Inc. mainly contains what is referred to as “placeholder” information. There are numerous web sites with nearly identical content.
Just Googled ” “james masters” “vanessa king” ” – two names from the Our Team or Our Crew web page. Google found 1,410 results with the nearly identical language on the page once the repeat text results are omitted.
Question: Could these various web sites be related to Silk Road 2.0? or are these just web sites from Brian Benthall’s web site development business?
I discovered that site after doing a reverse whois at Domain Tools for the email address that he used, according the complaint. DomainTools says that email was also used to register
Domain Name Create Date Registrar
benthallgroup.com
2014-05-28 1 API GMBH
blake.vc
2014-05-13 1API GmbH (R154-LRCC)
codespike.co
2014-05-28 —
cspike.com
2014-07-23 1 API GMBH
fatbit.co
2013-09-22 —
haaaaay.com
2014-09-27 1 API GMBH
sciview.com
The content of the pages must be some sort of template data, then. The HTML of these particular web pages mentions Squarespace, the web page developer, next to the name Blake Benthall, in comment lines.
I just thought it curious because the photos of the three people, members of the team or crew, are hosted on various flickr pages of photographers. I didn’t think that a service such as Squarespace would link to flickr pages for its template photos due to possible download time problems, permission issues, etc.
The templates used may not even have originally come from Squarespace
I looked up
benthallgroup.com
and
codespike.co
on urlvoid.com and saw they are both on the same IP address, 62.116.130.8
The hostname for that IP address is “redirect.domain-robot.org”
which is not a confidence-inspiring address … except for “confidence artists”
One of the side-effects of the small number of unique IP addresses (less than 4 billion!) under IPv4 is a disreputable business seeking a unique domain name is forced to share the IP address of the domain name with the domain names of other businesses, many of which will also be disreputable.
We are going to have a lot of grief when IPv4 is fully deprecated and all IP addresses are IPv6.
@Brian,
> millions of dollars generated by these unlawful transactions,”reads a statement
You’re missing a space between the closing quotation mark and “reads”.
Hey timeless,
Why don’t you become an English teacher as you like to critique writing so much, and stop critiquing Brian. Your comments are really annoying.
Is SpaceX part of Moon Express Inc.? Did working for SpaceX give Blake Benthall access to the Intelius servers?
Smells like a honeypot, just sayin
Pooh
I think this guy just stumbled across this cash cow. He probably never thought it would get so big.
Hey timeless,
Why don’t you become an English teacher as you like to critique writing so much, and stop critiquing Brian. Your comments are really annoying.
is it possible they are simply looking at all ip addresses (256*256*256*256) and looking for the the website to appear?
No captcha issues this time.
Another criminal that lacked enough infosec awareness. Just like the lagit business world its the human aspect you need to watch out for. Also the underground customer service aspect may also be the undoing of many of these dark web sites. As greed takes over they tend to let their guard down in hopes to keep their customers happy and cash flow coming.
I’ve read the whole criminal complaint, this guy threw his whole life away because of greed. What a waste
So they indicted the idiot with counts of computer hacking and yet the Christofascist pigs which identified him committed the same crimes.
Funny how fascist pigs can break our laws even as they charge others for the same crimes.
Call the cops what you will but they played this guy from what seems to be the very beginning of his would-be venture. HE gave them the keys. As many of my digital forensics instructors who worked within the local PDs always told us: ‘9 times out of 10 the ones we’re catching and putting in front of a judge are not brightest’. So whenever we discussed stenography or encryption or just plain common sense it wasn’t something these guys saw a lot of in the field when making arrests.
Used his personal email address! We don’t catch the smart ones! 😉