How do fraudsters “cash out” stolen credit card data? Increasingly, they are selling in-demand but underpriced products on eBay that they don’t yet own. Once the auction is over, the auction fraudster uses stolen credit card data to buy the merchandise from an e-commerce store and have it shipped to the auction winner. Because the auction winners actually get what they bid on and unwittingly pay the fraudster, very often the only party left to dispute the charge is the legitimate cardholder.
So-called “triangulation fraud” — scammers using stolen cards to buy merchandise won at auction by other eBay members — is not a new scam. But it’s a crime that’s getting more sophisticated and automated, at least according to a victim retailer who reached out to KrebsOnSecurity recently after he was walloped in one such fraud scheme.
The victim company — which spoke on condition of anonymity — has a fairly strong e-commerce presence, and is growing rapidly. For the past two years, it was among the Top 500 online retailers as ranked by InternetRetailer.com.
The company was hit with over 40 orders across three weeks for products that later traced back to stolen credit card data. The victimized retailer said it was able to stop a few of the fraudulent transactions before the items shipped, but most of the sales were losses that the victim firm had to absorb.
The scheme works like this: An auction fraudster sets up one (or multiple) eBay accounts and sells legitimate products. A customer buys the item from the seller (fraudster) on eBay and the money gets deposited in the fraudster’s PayPal account.
The fraudster then takes the eBay order information to another online retailer which sells the same item, buys the item using stolen credit card data, and has the item shipped to the address of the eBay customer that is expecting the item. The fraudster then walks away with the money.
One reason this scheme is so sneaky is that the eBay customers are happy because they got their product, so they never complain or question the company that sent them the product. For the retailer, the order looks normal: The customer contact info in the order form is partially accurate: It has the customer’s correct shipping address and name, but may list a phone number that goes somewhere else — perhaps to a voicemail owned and controlled by the fraudster.
“For the retailer who ships thousands of orders every day, this fraudulent activity really doesn’t raise any red flags,” my source — we’ll call him “Bill,” — told me. “The only way they eventually find out is with a sophisticated fraud screening program, or when the ‘chargeback’ from Visa or MasterCard finally comes to them from the owner of the stolen card.”
In an emailed statement, eBay said the use of stolen or fraudulent credit card numbers to purchase goods on eBay is by no means unique to eBay.
“We believe collaboration and cooperation is the best way to combat fraud and organized retail crime of this nature, working in partnership with retailers and law enforcement,” wrote Ryan Moore, eBay’s senior manager of global corporate affairs. Detecting this type of fraud, Moore said, “relies heavily on the tools that merchants use themselves, which includes understanding their customers and implementing the correct credit card authorization protocols.”
Moore declined to discuss the technology and approaches the eBay uses to fight triangulation fraud — saying eBay doesn’t want tip its hand to cybercriminals. But he said the company uses internal tools and risk models to identify suspicious activity on its platform, and that it trains hundreds of retailers and law enforcement on various types of fraud, including triangulation fraud.
QUAD FRAUD?
Moore pointed to one education campaign on eBay’s site, which adds another wrinkle to this fraud scheme: Very often the people listing the item for sale on eBay are existing, long-time eBay members with good standing who get recruited to sell items via work-at-home job scams. These schemes typically advertise that the seller gets to keep a significant cut of the sale price — typically 30 percent.
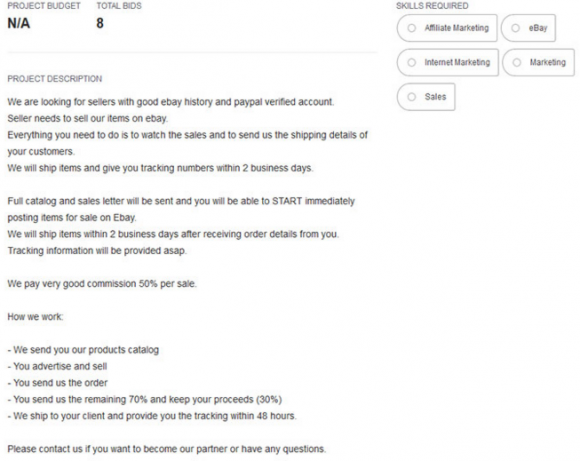
A recruitment email from a work-at-home job scam that involves respondents in triangulation fraud. Source: eBay
Interesting, the guy selling carded goods stolen from Bill’s company has been on eBay for more than a decade and has a near-perfect customer feedback score. That seller is not being referenced in this story because his feedback page directly links to transactions from Bill’s company.
Bill said he believes fraudsters targeted his company because it is relatively small, and is less likely to rely on sophisticated fraud tools that can sort out fraudulent orders. In his company’s case, it wasn’t spending any money on such fraud prevention tools until all this eBay fraud started.
“It wasn’t a huge order size, just random products we sell,” Bill said. “They’re going after us as a medium-sized retailer because we’re not yet to the size where we have all the fraud software built-in.”
TRI-FRAUD BOTS?
According to Bill, the company thought it had figured out a fraud pattern to help block future phony charges, which it found all came from different Internet addresses at Amazon’s Elastic Compute Cloud (EC2) service. But he said the fraud didn’t stop until the company started blocking purchases made from servers hosted at Amazon’s EC2 service. After that block was put in place, visitors coming from EC2 servers could still browse the site, but they would be blocked from placing orders.
Bill said he believes the orders may have been placed by automated “bot” programs running on instances of Amazon’s EC2 platform (instances that were also likely paid for with stolen card data).
“The fraud kept going until we put in some things that blocked his bots at Amazon EC2 from transacting with our site,” Bill said.
Bill allowed that he can’t prove it wasn’t just a human manually transacting from all those EC2 systems. However, another security measure that Bill’s company established to fight triangulation fraud lends credence to the theory that some sort of automated EC2-based bots may indeed be involved in placing the unauthorized product orders. Bill’s firm put new data fields in the part of the checkout process where customers type in their name and address. This trick uses data fields that are hidden from regular Web site visitors but that are still visible on the site to computers and Web crawlers.
The idea is to separate orders made by humans from those entered by automated bots. Although the latter may dutifully supply some phony requested data in the new data fields, legitimate, human customers would never input data into those extra fields because they can’t see the information being requested in the first place.
‘Blocking EC2 purchases and the data fields have worked really well blocking this fraudster’s bots from spamming our email forms,” Bill said.
Bill’s company also just signed up with MaxMind, a company that gives retailers multiple clues about potentially fraudulent orders based on the geography of the order. For example, was the order placed from an Internet address that is located near the shipping address?
For its part, eBay says merchants can fight triangulation fraud by focusing on the products being sold by suspect eBay accounts. “Collaborate with auction and marketplaces that are known to have fraudulent sellers,” the company said in its tri-fraud primer. “Together, you may be able to uncover additional orders that may be part of the scam to help identify fraudulent sellers and/or employers.”
Has your company or credit card been victimized by triangulation fraud? Sound off in the comments below about your experience.





Brian,
Have you heard about this event?
http://www.law.ufl.edu/news/2015/10/07/nov-9-2015-poucher-lecture-to-explore-cybersecurity-policy-issues-with-leading-experts/
takes 5 mins to cancel stolen credit cards even if its copied bank refunds the full amount and internet crime unit picks up from there.
No one is arguing that point, and this story isn’t aimed at any “losses” a customer incurs. However, the retailers frequently DO incur losses, when the credit card companies / banks issue a charge back, essentially meaning that the retailer has shipped the goods, and now they are not going to be paid for those goods.
“Internet crime unit”?? Even for police departments that might have such a unit, they are not going to be looking into the vast majority of such crimes, because usually the loss to a single card is too small to bother with. Not to mention, most departments don’t have the skills to track down any type of complex computer crimes, and when they do, they will likely lead to someone that is in another country, that they will never be able to prosecute.
+1. Well put, CJD.
Thanks for putting a smile on my face, that Krebs agreed with one of my points! 😉
Got a call last night that someone in our LA office was hit with ransomware and hit part of the file server as well, and the first thing that came to mind was becoming one of those “…a long time reader of this blog spoke to me regarding a ransomware infection…” – I cringed. I don’t ever want to be one of your “it happened to me” sources, especially on the retail breach side!
Related side note, I am hating Kaspersky more and more every day.
“Bill allowed that he can’t prove it wasn’t just a human manually transacting from all those EC2 systems.”
Maybe not but blocking all EC2 systems seems valid to me unless somebody can sell me on a plausible scenario whereby your average everyday run of the mill human would be shopping for consumer items on eBay from some server in the cloud. I mean, don’t you need a computer to connect to EC2 in the first place? And if so then why bother shopping by proxy just use the first machine to shop.
Kindle accelerated browsing uses EC2 to compress and cache pages on the fly. As a bonus it would obscure the location of the fraudster.
I came up with this over 10 years ago brainstorming how I’d fence stuff if I got into carding. I figured others were doing it everywhere and didn’t bother doing a writeup. Surprised to see it’s a relatively recent thing.
This is not a new scam / its been going on for years. Think of other online market places like Craig’s List / Stub Hub or forums where things are listed for sale. Some of these jokers even build their own sites, and list products they know that they can source via a stolen payment. Someone can make a handsome living by doing this, and as other posters mentioned, its not a high probability that they will get caught so long as they fly under the radar with low volume and spread the fraud around. Tracking this type of crime is often challenging as it requires technical expertise to build the case, it crosses state lines and rarely does it exceed the threshold where law enforcement will do anything other than file a report.
Hey, it only took 100 comments for someone to say this is not news! Funny, I acknowledge that in the second paragraph:
“So-called “triangulation fraud” — scammers using stolen cards to buy merchandise won at auction by other eBay members — is not a new scam. But it’s a crime that’s getting more sophisticated and automated, at least according to a victim retailer who reached out to KrebsOnSecurity recently after he was walloped in one such fraud scheme.”
This is our most common type of fraud on our ecommerce site. It has been going on for quite some time (as was mentioned) but it has picked up in the last couple years.
Ebay needs to make it easier for retailers to report this, but most retailers probably don’t bother to track down the root cause. We do. We’ve shut down many credit cards by contacting the billing side and shut down many Ebay accounts once we contacted the receiver and found out where they purchased it from. We do have internal contacts now at Ebay to report this kind of thing but they really didn’t make it easy. We want to make the bad guys’ lives as difficult as possible. I want to look like a porcupine to them 🙂
Frankly it doesn’t sound like they have very good anti fraud measures in place. Our order volume is lower but we have much better systems and processes in place. We certainly have plenty of attempts but very few per year are successful.
Why cybersecurity-policy don’t follow the fraudster’s PayPal account? Sooner or later the fraudster will want to take his money in his hand. Why don’t follow the money?
I should hope that these ecommerce sites become more aware of whom they are selling to. Perhaps they only ship to the card address (zip) and if the buyer wants a different ship to address they charge a fee based on total sale.
Keep in mind, working in the credit union industry, we pay a fee to file an ecommerce dispute of $20-$50 per transaction. We are out money too. Three $50 transactions and we are out $150, not the ecommerce site.
Thanks Brian, for reminding us of trends. I am sure this one will take off as chip cards change the fraud landscape, if only for a while.
Hello Krebs,
I had and i still have a question regarding Antivirus. We have recently seen pretty much things going on and when it comes to protecting ourself from all virus, malwares, rootkits etc has become very hard. My question to you is… Which antivirus do you use ? or personally recommend (if there is any 😀 ) ?
Thanks waiting for your reply.
I thought your shipping address had to match the billing address on the credit card when making online purchases.
I remember being prevented from purchasing things with a pre paid visa because it did not have a billing address associated with it.
Chip and PIN is not the perfect solution, but it is effective.
I am not sure why no one is suggesting doing what they do in other countries. A couple years ago when I was living in Germany, my bank issued me a little calculator-looking thing. It was a cheap item and had a keypad on it (numbers) and a place to dip your chipped card in. Every transaction required you to put your card in and confirm the PIN (using, presumably, the new algorithm that wouldn’t allow a “FUN” chip on the card to work successfully).
On the order page of the website is a little box that is flashing in some pattern. Holding the calculator thingy up to this flashing box would cause it to show it “filling up” – in that, in a few moments it would be complete. Then, the calculator thingy presents you with a 6 digit number that you enter into the site’s field and the your order is confirmed as a “CARD PRESENT” transaction backed by both the chip and the PIN (yes, CCs require PINs in other countries).
Though, not perfect, I would much rather use non-proprietary technology rather than some credit card company technology like password verifications, etc. which are different for each issuer. CnP is where we are going, why not do it right like they are doing in other countries?
It seems to me that it’s not worth the risk of fraud to allow the billing address (tied to the credit card, and approval of the transaction) to differ from the shipping address (tied to nothing, and unverified). Is it so essential to online retailers to allow this?
If credit card companies could tie approval to an optional shipping address (registered with them), then this type of triangulation fraud ought to be easily stopped.
You’d be surprised by how many totally legit orders have a mismatch when it comes to the shipping/billing address. It varies by vertical and company, of course, but in general it’s far more common than you’d think – students using family cards to ship to dorms, expats, traveling businessmen or artists, items being sent to a friend or family member as gifts, or because they’ve offered to act as mailman, even soldiers and diplomats (and their families)… There are a lot of genuine use cases.
So although you’re right that insisting on a match would help, you’d end up rejecting a lot of good customers into the bargain. It’s a fine line to tread.
Initially, I thought it wasn’t worth the risk of billing shipping. OK, wrong, for the reasons you mentioned.
Triangulation fraud could be stopped just by validating part of the shipping address via the approval/denial decision. A zip code would do nicely, if (big if) cardholders would willingly provide that information (via online banking) OR have it collected to prime the system before it becomes mandatory for transaction approval.
It comes down to economics.
Won’t the company ship an invoice with the order?
Also, the customers will see that the package comes from a different company which is something fishy.