If you have ever walked up to an ATM to withdraw cash only to decide against it after noticing a telephone or ethernet cord snaking from behind the machine to a jack in the wall, your paranoia may not have been misplaced: ATM maker NCR is warning about skimming attacks that involve keypad overlays, hidden cameras and skimming devices plugged into the ATM network cables to intercept customer card data.

Two network cable card skimming devices, as found attached to this ATM.
In an alert sent to customers Feb. 8, NCR said it received reliable reports of NCR and Diebold ATMs being attacked through the use of external skimming devices that hijack the cash machine’s phone or Internet jack.
“These devices are plugged into the ATM network cables and intercept customer card data. Additional devices are attached to the ATM to capture the PIN,” NCR warned. “A keyboard overlay was used to attack an NCR ATM, a concealed camera was used on the Diebold ATM. PIN data is then likely transmitted wirelessly to the skimming device.”
The ATM maker believes these attacks represent a continuation of the trend where criminals are finding alternative methods to skim magnetic strip cards. Such alternative methods avoid placing the skimmer on the ATM card entry bezel, which is where most anti-skimming technology is located.
NCR said cash machine operators must consider all points where card data may be accessible — in addition to the traditional point of vulnerability at the card entry bezel — and that having ATM network communications cables and connections exposed in publicly accessible locations only invites trouble.
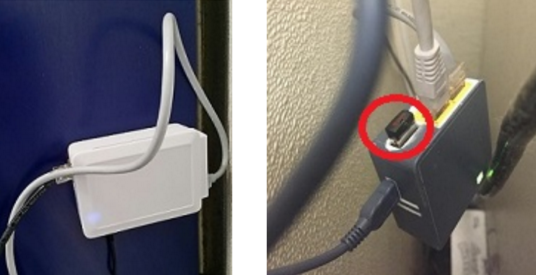
A closer look at the two network cable card skimming devices that were attached to the stand-alone ATM pictured at the top of this story.
If something doesn’t look right about an ATM, don’t use it and move on to the next one. It’s not worth the hassle and risk associated with having your checking account emptied of cash. Also, it’s best to favor ATMs that are installed inside of a building or wall as opposed to free-standing machines, which may be more vulnerable to tampering.




This could be caught if the ATM was monitoring voltage across the line and picked up a voltage drop due to an additional attached line. The ATM could just lock up requiring a technician to open and reset it.
Might work for some but other devices, as pictured, just use a nearby outlet for power.
Something like this would be most likely be implemented inside the ATM itself, not in an external wall-wart.
Are you serious? The voltage drop would have to be substantial for it to be detected, otherwise the required sensitivity would produce constant alarms.
I dare you to list a voltage supply, that connected to any of the common grid, is stable enough to use that as forensic evidence to plan a warning system off of it. There are none in America. If you were lucky enough to have some of the old lightbulbs, in operation, and this is annoying to those older folks, who know what is happening, you can see, rises and falls, in intensity, complete missed cycles, spikes and other problems with the grid. The led light falls off slower then the old lamp, but because of grid problems still don’t operate to their best efficiency.
Im just surprised, of the old fallback, Bluetooth? THat means connected to the board thru usb. Or have they gone more expensive and gotten the mini modem from china? I believe they were a dollar a dozen, a few years ago.
The question I have is how is this attack even possible? There are supposed to be DES keys that encrypt communications between the ATM and its network host. Sniffing network traffic should be futile unless the skimmers are cracking AES256 encryption.
I cant speak for telephone communications, but I would hope to see a similar level of encryption.
Brian do you have any further technical details of how this could be achieved?
DES keys only encrypt the pin and maybe the expiration date. Have looked at these signals before and have been able to see the entire card number.
Asked the vendor about it and got a non-response.
You could put a data protocol analyzer across the tel line and see everything. If you can intercept the data burst between the 1st and second ring for call waiting on the POTS line, you could get this stuff.
Tim,
This is possible because many ATM owners and operators don’t encrypt the data that they send to and from the network. You might ask how this is possible in 2016, but then again I ask that about all kinds of things.
Like, how come we still mostly swipe the card, which also transmits the card data in plain text (stored in plain text on the mag stripe).
Like how come we still authenticate people by asking them to supply info that is widely for sale very cheaply, like SSNs, and DoBs?
Stay away from the stand-alone ATMs and you should not have to deal with this nonsense.
How is the data not encrypted in transit?!
So, customer card data isn’t encrypted by the ATM before it is transmitted? That’s surprising.
To put this in perspective, right around the time of windows XP’s EOL, most ATM vendors had JUST certified Windows 7. Encryption of data in transit isn’t something that is even in these companies vocabularies.
Sadly, it doesn’t surprise me.
For some reason, people think, because an ATM might have a bank logo on it that it’s as “secure as a bank vault”.
It isn’t. It’s really a glorified network attached cash register.
It was designed/optimized for “ease-of-use”. At best, minimal hardening was done to prevent someone from just opening the drawer themselves. — I say minimal, because there are some pretty neat chemistry/physics attacks against banks these days… — I’m not endorsing them, but to think that these were top of the line security from bottom to top is unfortunately naive.
Mostly what you’re seeing w/ ATMs is security theater.
There’s a great line about “how do you outrun a bear?”, the answer is “be faster than the other guy” — Not fast enough to outrun the bear.
The ATM vendors, and the credit card vendors all are putting in minimal effort to be one step ahead of their competitors, so that the bear will attack them instead. It’s not about outrunning the bear, just not being the slowest guy. Getting it actually right would involve way too much effort, money, and probably public discussions (and a lot of ridicule).
The fact that encryption over the wire isn’t being used shows just how behind the curve ATM technology is.
To go back even prior to the curve, Remember when banks had guards? Remember when banks had their own version of the ATM, to dispense money to their preferred customers? That’s all been taken over by outside companies. Remember banks used to be the place to work because of the security? Now, you have to the ceiling avoid the customer approaches. And none of this can stop hackers from trying.
I don’t remember the trial happening, but, one of the mob kingpins sons should be in jail now. He was working for one of the ATM service companies. His crime, was taking some of the cash. He had access to the atms. What else did he do? Take a keyprint of his keys? Take photo of the insides? What else? That’s got to be a fast in/out job, but I am surprised, outside where you can see the connectors? How unprofessional. So this was a two time job. One once in the system, another a driveby. To arm the system.
Makes sense, they have the keys, they know the alarms from mexico, they know the boards, and the system. The implementation seems shoddy. So I don’t suspect American godfathers, but, drugstore, trying to get their cash back? Maybe.
Wait, because data is transmitted in clear text over the network ?
PCI-DSS anyone ?
PCI DSS Requirement 4.1 is that card data be encrypted in transmission over public networks. ATM and EMV networks are closed and not public.
I don’t know, the cables in Krebs’s photo look pretty darn public to me…
If that cable transfers unencrypted cardholder data, it’s part of what PCI DSS defines as the Cardholder Data Environment (CDE). Access to the CDE needs to be physically protected (PCI DSS 9.1). In particular, access to network jacks and network devices in the CDE must be secured (PCI DSS 9.1.2 and 9.1.3).
It’s actually not a violation of requirement 9.9 (as suggested elsewhere in the comments) as that requirement deals detection of tampering, not preventing tampering from happening.
Requirement 9.9 requires that such devices be periodically inspected for tampering.
PCI DSS should be looked as the baseline for controls, and not the maximum that an entity should do to protect card data. Requirement 9.9 for instance doesn’t specify how frequently the inspections should be but just says periodically. I think for true diligence it should be daily. And the convenience stores where most of these ATMs are located should be made responsible, not just the vendor for them. Too many only do what is minimally required.
PCI-DSS doesn’t apply here. PCI is a regulation applied by the banks, to merchants accepting credit cards. No obligation for the banks to apply the standard to themselves.
Actually Banks are required to comply with the DSS. This is from the latest version of PCI’s document, Requirements and Security Assessment Procedures. “PCI DSS applies to all entities involved in payment card processing—including merchants, processors, acquirers, issuers, and service providers”. Acquirers are the banks that provide to entities the merchant accounts so they can accept cards at the point of sale or online.
It should be encrypted even though PCI doesnt require it. The card brands are more worried about users losing confidence in the security of their data and not using plastic. This of course would mean the loss of fees to the brands and banks. I think they also believe that users would balk at the slight increase in processing time that encryption would result in and decide that cash is easier.
Should be, but is not, and won’t be for years. First you have to look at how credit evolved – security was NEVER baked in to the process for credit, and only marginally for ATMs. Almost all security applied to credit and ATM transactions has been shoehorned in after the fact.
Bank owned ATMs would be the easiest to encrypt, but past that it gets expensive, and no one wants to absorb that cost. The biggest reason credit transactions arent encrypted on the wire (which is the case for most retailers) is because the banks and service providers all charge you an extra fee every time you process a transaction, on top of the existing fees. That equates to millions of dollars per year for most retailers, and that comes straight off the bottom line. Its a hard sell to get a Board to approve taking a few (or more) million out of the profits of the company, just to mitigate a potential threat. And that doesnt include the costs to implement the encryption. Unfortunately registers / POS systems aren’t easy to just “turn on” encryption – you have to spend a fair amount of money in development to have it baked into your POS, or your card readers (which then still requires POS development).
Thanks for this post, Brian.
And 2 questions:
Q1) Isn’t it the total responsibility
of the Bank Branch “security personnel”
to be in the constant lookout
for the ATMs being modified
in detriment of the Bank’s customers?
(certainly Bank profits are HUGE,
they can afford
to be one step ahead of crooks and provide a safe banking experience to their fee-laden clients …).
Q2) As an Bank ATM user,
what can you actually DO to protect yourself
against these new devices?.
I already look for cameras, fake kbd overlays, etc,
but…. to _detect_ these external boxes and cables on the side or behind the ATM,
is virtually impossible for the lay person!
Hope you (or other readers) can chime in
these 2 questions…
I’ll leave question 2 to those more knowledgeable than I, but to answer question 1, many “Free-standing” ATMs aren’t in banks. They’re in restaurants, nightclubs, grocery stores, etc, etc.
Brian is (wisely, IMHO) recommending that we not use such ATMs and stick to those built into buildings, ideally those built into bank buildings and secured by banks as you describe. (Which I guess kinda answers your second question?)
Thanks, Jon!
It does partially answer my question.
In principle, I NEVER use ATMs in supermarkets, etc.
only inside a Bank,
(where ATMs are supposed to be more secure?)
@SFer – I never use those standalone machines like in the laundromat where I was my oversize bedding and rugs, but I do use the ATMs that are part of the branch inside the grocery store. My bank is a fairly large one and has a branch near my home, but the chances of getting mugged there since the machines are on the exterior of the building and shielded from view by shrubbery. Since I am in the grocery store, say Safeway, Trader Joes or Whole Foods at least once a week, I usually get cash back from a purchase rather than stand in line again, with my back to the door in most cases, to withdraw cash at the bank. I recently had to replace a card and stood in line behind at least a dozen people with ID issues, language issues or just plain ignorance about cashing a grimy illegible 3rd party check (arouses suspicion, duh!) and there was only one teller who was bilingual at the time, so I concluded that the banks want us to use their machines and not stand at the window to get cash. We take advantage of direct deposit and use bank apps to deposit any stray paper checks like rebates, gifts, refunds etc., so generally avoid banking institutions in general. I’m not sure I want to drive 15 miles to find a safer ATM, and so I get my cash from the grocery store ATM as I said above. So I’m curious – I was unclear by your post if you restrict your withdrawals to bank ATMs or do you go the teller route?
They are most definitely required, at least under PCI DSS Requirement 9.9 – “Are devices that capture payment card data via direct physical interaction with the card protected against tampering?”
Requirement 9.9 principally had POS terminals in mind when it was written but ATM’s are also such devices.
I don’t know if these ATMs are using encryption or not but they should be. However encryption is not a panacea.
For example if all the same brand of ATMs use the same key (no idea if they do or not but it has happened in other hardware) the attacker simply copies the encrypted data and then decrypts with a key they got from a machine they bought off eBay. or maybe there isn’t enough randomness allowing for a trivial brute force attack to succeed, or they used some other attack, who knows, my point is
Just because encryption doesn’t always mean security.
– SR
Brian,
Since these network skimmers are actually packet-sniffing the card data off the wire, why do they need a separate PIN pad overlay or hidden camera? Wouldn’t the PIN be included in the data sent over the wire? Or are the ATM communication protocols doing something (relatively) smart to prevent that?
I say “relatively” smart because the fact that you can packet-sniff the card data at all means they’re not using an encrypted transmission protocol, which is absolutely ridiculous. Not surprising given how systems like this typically are locked into antique protocols, but utterly inexcusable for an ATM manufacturer trying to sell its devices as secure. SSL has been around for decades; it’s not that hard to use (with plenty of libraries available for the programmer), and it would solve this problem in a flash! (Of course there’s still always the potential for man-in-the-middle attacks if SSL isn’t implemented carefully, but it would at least be an improvement.)
EJ
I think the PAN (Primary Account Number) is sent in the clear on the phone line as a way of identifying which bank it should talk to and to which account the transaction is dealing with. The phone line is thought of as inaccessible and therefore secure.
The PAN should be encrypted under SSL for internet based transactions and should therefore be somewhat secure.
The PIN and the PAN are XORed together as a “pin block” in the ATM, then they are encrypted with 3DES but the key is rotated every transaction under DUKPT (Derived Unique Key Per Transansaction) rules.
I’m guessing that you are using SSL in a generic sense to describe PKI encryption because SSL is now insecure and PCI now requires at least v 1.2 of TLS.
They don’t even need to use SSL/TLS. It is very common for legacy protocols to be simply wrapped in a VPN or VPN-like system. Then you don’t need to change your ancient (but trusted) legacy systems, but do get modern security.
The ATM sets up the VPN, and then all the rest communicates over that.
David, in their infinite wisdom, the Council backed off on the TLS 1.2 requirement (for 2+ years) – https://www.pcisecuritystandards.org/pdfs/15_12_18_SSL_Webinar_Press_Release_FINAL_%28002%29.pdf
I’ve heard various reasons for this but the most credible one I’ve heard is that something like 10% of mobile devices do not support TLS 1.2 and that many of the carriers/phone providers are slow to provide updates to phones or don’t do so for older phones.
The PIN is encrypted, as I remember, through out the process. I think there are separate standards for this. Why is a great question.
Brian – great information ! The photo’s are helpful as to help quickly identify if someone messed with the ethernet/telco line.
There are about 3 Million ATM’s worldwide giving thieves many choices where to perform their breach. It can be a challenge to insert a skimmer / modify the bezel without raising eyebrows. The bad guys are innovative….thanks for great reporting.
Scott
http://www.scottschober.com
This is, almost, incredible!
So, if they wire it hidden enough we have no way of detecting it.
I’m not _that_ worried since, my bank (BBVA), here in Spain, has well done security measures (of the likes that it will ask me to approve with my mobile anything that’s, at least, suspicious…
But, that said, is terrifying (and. I have to admit it, amazing) the way these crooks operate…
AES256 encryption? That is no where to be found on ATM networks. The DES keys are used for authentication on initial connection between the ATM and the processor. There are other parties involved in processing your ATM transactions and not just your bank or CU. The ATM manufactures and processors just can’t get it together on strong encryption. If you have ever done authorized packet capture of ATM traffic you were shocked what you saw. I had unhappy coworkers for insisting that exposed network cables be in rigid conduit. Avoid ATMs where the back of the ATM is exposed or you can see network cables.
Wow! This wouldn’t even be possible if they bothered with encryption!
I saw an ATM in Kroger with this exact same issue. yesterday I posted about it warning my Facebook friends to stay away from ATMs that look like this. Nice to see an article back me up on that!
https://www.facebook.com/JBSibley/posts/10102540576506337
OMG … If only there was a technology to allow a client to safely communicate with a server, preventing men-in-the-middle to read or modify the transmitted data! … But wait! Isn’t there something called TLS (formerly SSL) which provides exactly that? (I believe I use it every time when doing a Google search.) OK, it has only been around for about 20 years, so maybe it’s just to “avant-garde” to be known to the manufacturers of ATMs.
Not included in this write up, but was included in communication from NCR:
This vulnerability can easily be prevented. NCR strongly recommends the implementation of secure encrypted network communications. NCR provides TLS protection to enable this type of data security. In addition, ATM network communications cables and connections should not be located in publicly accessible locations
This.
People who don’t know anything about the banking industry will too easily mistake that the manufacturer is often not the actual developer of the whole ATM software.
They will provide the OS and the base layers; then it’s up to the integrator to be careless as hell and not use a VPN, or try to do something more sensible.
(In my country all ATM actually use a VPN. Then we also use EMV for about 20 years… US payment industry is quite a different bunch.).
PS: regarding another comment, BSD also works very well without using a VPN. The OS is totally irrelevant there.
It’s only a matter of time till it goes another step backwards. There is a wiring closet somewhere that the data has to go over and then they just have to skim the pin using more covert tactics.
I’m guessing this only lasts for a little while.
I was thinking the same thing. Was also thinking that this might give better cover and delay discovery by ATM techs.
More than 30 years ago, in high school, we made our own lineman a phone out of a princess phone and a couple alligator clips. Would connect up to the junction box on the alley wall behind the supermarket, drug store, or convenience shop. We didn’t know anybody to call long distance, and were afraid of getting busted, so we called a few 800 numbers to Disneyland and the like before quitting after having proved the concept.
I’d bet that such external junction boxes are still there, still insecure, and still shielded by dumpsters and empty alleyways. Perfect pickens for the skimmer crews.
You are safer if you used a real bank ATM instead of the stand alone ones pictured.
True, and I agree. That said, enough people do use those instead of actual in-wall bank ATMs to where it’s lucrative for scammers to target them.
Security is all too often a case where people who know the least have the most insecure practices simply because they know no better. And because the practice wasn’t designed against these sorts of attacks to begin with (I often see more physical damage and physical theft measures in place on these standalones than I do communications and skimming defenses).
Oh, remember: It’s far from impossible to hijack bank in-wall ATMs. They may not be able to do it in the way highlighted here, but it’s unfortunately all too possible. From one of Brian’s older posts:
http://krebsonsecurity.com/2011/02/having-a-ball-with-atm-skimmers/
Keep in mind that a credit card transaction and debit card transaction are not created equal, even if they both can be performed by the same card. I’d like to hear what the differences are in the data sent back to the bank is with each type, and if the PCI-DSS really covers data from a debit card transaction. There is also the element that most of these machines transmit over a ‘private’ network, so again, how does this impact compliance or not. But then again, compliance does not equal security.
From a technology standpoint, encryption, especially in transit, has been in wide use for more than a decade and a half. Even at the time of Y2K, IT professionals and applications were having to manage SSL certificates. So, from a technology standpoint, one simply cannot make the argument that encryption is too new or cumbersome to be implemented, even in many of the older ATMs that are still in use. There is simply no excuse from a technology standpoint as to why all transactions are not encrypted in transit.
But, there is still the issue of updates. Someone with more knowledge of ATM technology would need to chime in here, but how are patches applied to ATMs, and how often? OpenSSL, which is the base of much of the encryption in use, has regular releases, including a number of security fixes. Even if you encrypt traffic, the encryption may have some flaws that could allow an attacker to still gain access to the data. If you cannot patch known flaws, the encryption may not be effective. After all, if an ATM model did encrypt all traffic, but nothing has been patched since 2009, how comfortable would you be that your data is protected over the wire?
Encryption alone isn’t enough. The ability to maintain the systems and their software in an efficient, effective, and secure manner is also critical to maintaining security of the data. (The discussion for how to protect and sign software updates to be applied in order to protect against compromised updates is part of the solution, but I’ve typed enough for now.)
I get the impression that most companies are behind the curve when it comes to having to pay for newer, more secure technology and aren’t committed to the investment even in the face of great financial loss.
Credit cards can also be used at an ATM, specifically to get a cash advance. Of course the interest they charge for those would astound a loan shark.
In what country was this? Is this from the Europol investigation of the Romanian gang (arrestedin early January) that targeted only NCR ATMs?
Nevermind. I remembered. Those guys used something else.
10 years ago, maybe longer… Thailand had a problem with theft of card data being transmitted in the clear through their phone lines/POS network, but they cleaned themselves up. I’m gobsmacked that this is still possible on ATM data given PCI DSS requirements, but not gobsmacked that the place that this is happening is the US – your payment data security is f**ked up. Seriously.
No great surprise.
When kg of prevention and meters of improvement are needed, the US is dealing with things in ounce and inch increments.
ATM systems have to be TR39 certified to use STAR, Pulse, etc. Per TR39, only the PIN is encrypted. All other ATM card data is in the clear which is why mag tapes are easy to produce from skimming. Having the account number is the easy part. Criminals only need the PIN to make the circle complete which requires camera, shoulder surf, fake keyboard, etc. which makes for additional work.
This is ridiculous. Even my Android smartphone can encrypt a connection.
ATM manufacturer’s invest in a real OS that knows about security. A BSD variant comes to mind.
The OS is almost the least of the concerns: you can implement competent crypto at almost any layer of the stack.
I remember ATM manufacturers talking about crypto as an essential security measure two decades ago. But it takes two to tango, so acquiring banks have to play ball too. Hence, it needs to be mandated, not treated as an optional-extra: least-cost, least-effort always wins out otherwise.
It’s amazing how we don’t learn from history as a race.
The ATM pictured in the top of the story is one of thousands inside 7-11 stores throughout the US; most of which are sponsored by Citibank.
I live in a small town with only a handful of banks. My bank-Wells Fargo-has only drive-up ATMS and not a one inside the building. However, the ATMs look locked tight and I don’t know how a skimmer could be attached without it being very obvious. My workaround is to get cash back when I go to the grocery store, Walmart, or some other place that offers it. It also seems like the armored car companies who service the ATMs would notice anything suspicious. Plus, it also seems to me that it would take time for a thief to set up his electronics. Aren’t there alarms on these things that go off when they’re tampered with?
A couple of commenters mentioned getting cash via cashback when buying groceries.
That is not a solution, either. Once those POS devices in the grocery store get infected you are back to point zero.
http://krebsonsecurity.com/2016/02/safeway-self-checkout-skimmer-close-up/
You can limit the size of the damage if you establish a secondary account in which you keep enough for your cash withdrawal. The secondary amount can be replenished via periodic transfers from the primary account. I do this with two checking accounts at the same bank. The transfers are handled either via the phone or in person at the bank if I am near a branch.
All my in-person or phone activity is password protected.
If you use a credit card to get cash back, then worst case you end up w/o your card for a few days while your card issuer sends you a new card.
This is much better than trying to correct the mess that can result from using a Debit/ATM Card.
timeless,
I think if you use a credit card to get cash you are in effect taking a loan from the bank and have to pay interest.
With an ATM card you withdraw your own money – no interest to be paid.
Why aren’t the number pads displayed on touch screens?
Problem solved NCR & Diebold.
You’re welcome.
Visually impaired /ADA liability lawsuit heading your way, Sam.
NCR & Diebold said you’re welcome.
Clear brail overlay?
You would trust Diebold? The election machine maker. Known issues with black box counting, arithmetic problems, printing problems, and actual vote switching problems. Could that be the problem, someone got po’ed and tried to fix it?
Brian how can I contact you? I want to tell you material that will help in the writing of articles on fraud.
krebsonsecurity at gmail dot com
Hi Brian,
I was wondering if you could post a link or attachment of the NCR alert? I can’t seem to locate it through Google searches. I’m probably just not searching the right way, but I’d appreciate it!
Also, can anyone point me to a reliable site that discusses the encryption or lack thereof of ATM network communications in a little more detail?
Thanks
If they can tap a POTS line at the device and get the mag strip data, they can tap it at the pedestal as well. No need to get anywhere near the ATM for any other reason than the possible need to identify the which line to tap at the pedestal. These types of ATM’s are in gas stations all over the place. It would not be hard to pose as a telephone repairman and root around in the pedestal. Whether or not the pin data is in the clear over a POTS line is the real question. That doesn’t sound like the case on Ethernet connected ATM’s seeing they used pin pad overlays or cameras.
“need to identify the which line to tap at the pedestal”
That is not necessarily an easy task. Depending on the pedestal there may be many lines, none of which are identified. You probably would need the Tel No. as well. It would be much easier to plug in an adapter at the connecting block and hide the device in back.