The Associated Press today points to a remarkable footnote in a recent State Department inspector general report on the Hillary Clinton email scandal: The mail was managed from the vanity domain “clintonemail.com.” But here’s a potentially more explosive finding: A review of the historic domain registration records for that domain indicates that whoever built the private email server for the Clintons also had the not-so-bright idea of connecting it to an Internet-based printer.
According to historic Internet address maps stored by San Mateo, Calif. based Farsight Security, among the handful of Internet addresses historically assigned to the domain “clintonemail.com” was the numeric address 24.187.234.188. The subdomain attached to that Internet address was….wait for it…. “printer.clintonemail.com“.
Interestingly, that domain was first noticed by Farsight in March 2015, the same month the scandal broke that during her tenure as United States Secretary of State Mrs. Clinton exclusively used her family’s private email server for official communications.
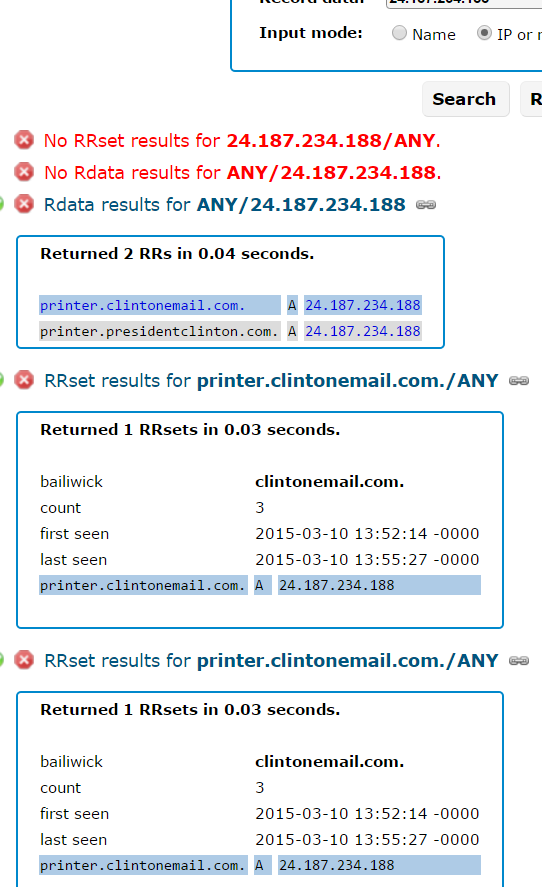
Farsight’s record for 24.187.234.188, the Internet address which once mapped to “printer.clintonemail.com”.
I should emphasize here that it’s unclear whether an Internet-capable printer was ever connected to printer.clintonemail.com. Nevertheless, it appears someone set it up to work that way.
Ronald Guilmette, a private security researcher in California who prompted me to look up this information, said printing things to an Internet-based printer set up this way might have made the printer data vulnerable to eavesdropping.
“Whoever set up their home network like that was a security idiot, and it’s a dumb thing to do,” Guilmette said. “Not just because any idiot on the Internet can just waste all your toner. Some of these printers have simple vulnerabilities that leave them easy to be hacked into.”
More importantly, any emails or other documents that the Clintons decided to print would be sent out over the Internet — however briefly — before going back to the printer. And that data may have been sniffable by other customers of the same ISP, Guilmette said.
“People are getting all upset saying hackers could have broken into her server, but what I’m saying is that people could have gotten confidential documents easily without breaking into anything,” Guilmette said. “So Mrs. Clinton is sitting there, tap-tap-tapping on her computer and decides to print something out. A clever Chinese hacker could have figured out, ‘Hey, I should get my own Internet address on the same block as the Clinton’s server and just sniff the local network traffic for printer files.'”
I should note that it’s possible the Clintons were encrypting all of their private mail communications with a “virtual private network” (VPN). Other historical “passive DNS” records indicate there were additional, possibly interesting and related subdomains once directly adjacent to the aforementioned Internet address 24.187.234.188:
24.187.234.186 rosencrans.dyndns.ws
24.187.234.187 wjcoffice.com
24.187.234.187 mail.clintonemail.com
24.187.234.187 mail.presidentclinton.com
24.187.234.188 printer.clintonemail.com
24.187.234.188 printer.presidentclinton.com
24.187.234.190 sslvpn.clintonemail.com




It has, I think, been shown by Venafi that there was for some time in 2012 and 2013 a VPN running on the clintonemail.com domain. However, that certificate expired. Running a directly Internet connected printer seems more a security threat than simply a chance of sniffing printer queues as modern printers sometimes have their own vulnerabilities.
Venafi’s posts (first story has information about VPN):
https://www.venafi.com/blog/post/new-data-confirms-venafi-analysis-on-clinton-email-server/
https://www.venafi.com/blog/post/what-venafi-trustnet-tells-us-about-the-clinton-email-server
https://www.venafi.com/webinars/view/on-demand-clinton-email-server-security-lapses
Hillary was so careless with state secrets. She’ll be indicted for sure (or at least she should)!
No she won’t. She and her husband are both solid members of the oligarchy – charges won’t even be filed.
I don’t see why she needs a public routable IP address for a mail server, an email server and a print server. It could all have been NATed behind a router on a single public IP.
I don’t see why she requires a publicly routable IP address for a mail server, print server and VPN server. It can easily be NATed behind a router on a single public IP.
I’m intrigued, to say the least, at reading “bailiwick” in this posting.
Jim, as in Bailey
I’m intrigued, to say the least, by seeing “bailiwick” in this posting.
Jim, as in Bailey
On a show last week, Rachel Maddow did a segment on the Department of State’s official archive policy.
According to Maddow, the DoS requires workers to print out each email sent or received, and file it in a box, which is preserved. In general, these printouts, when done at all, are “filed” in printout order, making them difficult to search (which may be the intent, given the historic hostility to FOIA requests).
This reminded me that the DoS was dismayed at not finding Brian Pagliano’s .pst file, indicating they did not expect to find his emails on any server-side backup. Presumably, no server-side DoS email backup capability exists.
Also, wasn’t mail.presidentclinton.com used for the emails of the Clinton Foundation aides? Doesn’t this mean the FBI likely now has very precise timing of both Hillary’s SoS travel communications and Bill Clinton’s speaking fee arrangement and Clinton Foundation donation emails, due to the emails likely having timestamps from a common clock?
Indeed, that’s their policy because (wait for it) that’s the only method of archiving email on their servers. If she had used their servers and not printed out their emails, as many prior SoSs didn’t do (Colin Powell being the most recent after Clinton), there still would be nothing on their mail servers to find, search, etc. because they don’t archive mail that way. They archive mail via hard copy.
Why in 2014,2015,2016 is it not a Federal mandate that all Fed email use Fed managed email server(s), and all Fed email copied to an archive, and the use of any other email system for conducting Federal business is big line in Fed penal code. No wonder why we are losing this cyber-battle.
Well, there are many printers have more than one port and protocols in use which means many different ways of establishing a connection to that printer and not just layer 2.
Yes, there are so many printers with integrated frame relay ports.
Loved all the arguments, but, show me in the laws where it was illegal, for Hillery, to have a second E-mail address? And that it was illegal to use it on government time. Or to have a printer hooked to that account? But, I will tell you what was illegal. The employees using that address to send classified information too. You shouldn’t worry about Hillery, but the useful idiots.
Outside of the security implications, 44 U.S. Code § 3101 “Records management by agency heads; general duties” is relevant
There are some registrars that setup DNS by way of a template and assign A record subdomains by default to make it easier….such as MX, www, etc. Not excusing it as you need to be way more careful when you are the state department…but this is hardly the worst thing Clinton has done.
So glad to know that there are people on here keeping the hope alive in the Bernie Sanders camp. Clinton shouldn’t be our next president; Sanders should. He knows a ton more about security.
It is time Enterprises take security seriously and start focusing on new age Endpoint security products saner business
I hope they do I just recently rented a car from them.
I’m not surprised since people don’t realize how much of a security risk a printer can be — and how to protect themselves and their network. Great white paper about printer and network security written by a third party here: bit.ly/1sq1kyG
I also just read a story about printers and security on Computerworld.
http://www.computerworld.com/article/3074902/security/printer-security-is-your-companys-data-really-safe.html
–Karen Bannan, commenting for IDG and HP
If Hillary wins in Nov she’ll pardon herself. If she loses she is in for a boat load of nasty. It makes sense why she is trying so hard to win in Nov, its a do or die scenario for her. Bottom line is this, the whole thing stinks, she may not have known about the technical details, and it could have breached classified data in more than one way.