In a notable sign of the times, cybercrime has now surpassed all other forms of crime in the United Kingdom, the nation’s National Crime Agency (NCA) warned in a new report. It remains unclear how closely the rest of the world tracks the U.K.’s experience, but the report reminds readers that the problem is likely far worse than the numbers suggest, noting that cybercrime is vastly under-reported by victims.
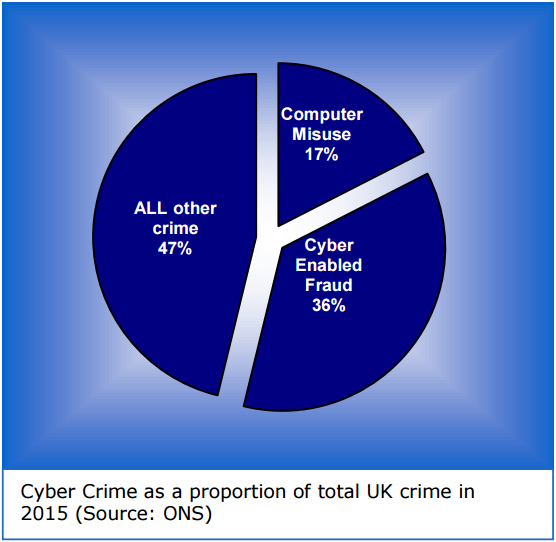 The NCA’s Cyber Crime Assessment 2016, released July 7, 2016, highlights the need for stronger law enforcement and business partnership to fight cybercrime. According to the NCA, cybercrime emerged as the largest proportion of total crime in the U.K., with “cyber enabled fraud” making up 36 percent of all crime reported, and “computer misuse” accounting for 17 percent.
The NCA’s Cyber Crime Assessment 2016, released July 7, 2016, highlights the need for stronger law enforcement and business partnership to fight cybercrime. According to the NCA, cybercrime emerged as the largest proportion of total crime in the U.K., with “cyber enabled fraud” making up 36 percent of all crime reported, and “computer misuse” accounting for 17 percent.
One explanation for the growth of cybercrime reports in the U.K. may be that the Brits are getting better at tracking it. The report notes that the U.K. Office of National Statistics only began including cybercrime for the first time last year in its annual Crime Survey for England and Wales.
“The ONS estimated that there were 2.46 million cyber incidents and 2.11 million victims of cyber crime in the U.K. in 2015,” the report’s authors wrote. “These figures highlight the clear shortfall in established reporting, with only 16,349 cyber dependent and approximately 700,000 cyber-enabled incidents reported to Action Fraud over the same period.”
The report also focuses on the increasing sophistication of organized cybercrime gangs that develop and deploy targeted, complex malicious software — such as Dridex and Dyre, which are aimed at emptying consumer and business bank accounts in the U.K. and elsewhere.
Avivah Litan, a fraud analyst with Gartner Inc., said cyber fraudsters in the U.K. bring their best game when targeting U.K. banks, which generally require far more stringent customer-facing security measures than U.S. banks — including smart cards and one-time tokens.
“I’m definitely hearing more about advanced attacks on U.K. banks than in the U.S.,” Litan said, adding that the anti-fraud measures put in place by U.K. banks have forced cybercriminals to focus more on social engineering U.K. retail and commercial banking customers.
Litan said if organized cybercrime gangs prefer to pick on U.K. banks, businesses and consumers, it may have more to do with convenience for the fraudsters than anything else. After all, she said, London is just two time zones behind Moscow, whereas the closest time zone in the U.S. is 7 hours behind.
“In most cases, the U.K. banks are pretty close to the fraudster’s own time zone, it’s a language the criminals can speak, and they’ve studied the banks’ systems up close and know how to get around security controls,” Litan said. “Just because you have more fraud controls doesn’t mean the fraudsters can’t beat them, it just forces the [crooks] to stay on top of their game. Why would you want to stay up all night doing online fraud against banks in the U.S. when you’d rather be out drinking with your buddies?”
The report observes that “despite the growth in scale and complexity of cyber crime and intensifying attacks, visible damage and losses have not (yet) been large enough to impact long term on shareholder value. The UK has yet to experience a cyber attack on business as damaging and publicly visible as the attack on the Target US retail chain.”
Although it would likely be difficult for a large, multinational European company to hide a breach similar in scope to that of the 2013 breach at Target, European nations generally have not had to adhere to the same data breach disclosure laws that are currently on the books in nearly every U.S. state — laws which prompt multiple U.S. companies each week to publicly acknowledge when they’ve suffered data breaches.
However, under the new European Union General Data Protection Regulation, companies that do business in Europe or with European customers will need to disclose “a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to, personal data transmitted, stored or otherwise processed.”
It may be some time yet before U.K. and European businesses start coming forward about data breaches: For better or worse, the GDPR requirements don’t go into full effect for two more years.
Hat tip to Trend Micro’s blog as the inspiration for this post.




at last criminals got savvy !!
This story is clearly wrong. As always, speeding is the massively dominant crime in the UK, with many billions of crimes committed per year, of which only a minuscule fraction are ever reported. After that is driving without due care and attention. And after that are other minor motoring offences. Crimes that anyone really cares about, including cybercrime, are a statistically insignificant proportion of total crime.
I’m not sure that speeding would qualify as a “crime.” On top of that we certainly can’t expect to include unreported incidents of speeding in ANY crime stats as the numbers would be wildly inaccurate.
I’m not from the UK but I know here in the US there are distinctions made between minor traffic infractions like speeding and crimes such as theft.
In the UK, there are no distinctions. Something is a crime or it isn’t, and speeding is a crime. Parking offence were decrimimalised many years ago to allow local councils to keep the revenue from parking fines, but no moving-vehicle offences have been decriminalised.
Also, you say we shouldn’t count unreported crimes, but one of the points of the report being discussed is that cybercrime is under-reported. If we’re not counting unreported crimes, we can’t talk about that.
There is a HUGE difference between under-reported and unreported.
If you’re going to make that distinction, then speeding is also an under-reported crime, not an unreported crime. Some speeding offences are reported. Billions are not.
It depends upon what State you are talking about. In Texas speeding is a Class C Misdemeanor.
First!
Banks are backed up with insurance money stolen money is same as credit it will negative. Other side. Without dept we cant print the money . So more debt more consumers more more but uk is too big too fall so debt will be payed from other dept dept keep us up and run. Money is not most important if someone zteal money it will create illusion basecly crime can help to keep value of money more crime meaning less inflation. People steal money couse they think ots something what is so important that in order to get that they have to steal… but its not crimininals are deluded crimes like this gives huge value so thays why pounds have sucche high valuation and inflation will not come anytime soon as longes money circlelation is going on and everybody chasing money .
I’m sure you had a coherent thought in there somewhere, buddy. Good for you for making words.
Brian, good article as usual. Run by CNN, foreign, tiwan, just announcing the latest attacks on secure ATM’s, of German manufacture. Seems to be a tap and withdraw. Not much yet, but with your reputation, you may get more then what’s admitted.
People of the UK ask yourselves.. would I rather be stabbed for a few ‘quids’ or would I rather lend a thief some Paypal funds which will be returned within 72 hours… ?
Would you rather have your family heirlooms stolen from you or would you rather lose £500 for a minute?
I guess neither would be better, but the world don’t work like that. If you can’t accept & understand that your answer is irrelevant. Let people fraud you and stop being so sour faced, it’s nature.
Stabbed or frauded. People are hungry! They take your money eather way . Uk is fulll of poor africans and eastern europeans every money they can make they make. Nsa was absaloutely right !!!
From the report:-
“This assessment has been jointly produced by the N
ational Crime Agency (NCA) and the Strategic Cyber Industry Group (SCIG). It outlines the real and immediate threat to UK businesses from cyber crime.”
*to UK businesses*…
In other words – as is implicit from the explicit terms of reference that link this to business impact only – this report cares not for the impact to private individuals.
As if the people of the UK needed another reminder that their sole purpose in life is to generate more profit for “big business”…
Sigh
RE: Mike Scott
“cybercrime… a statistically insignificant proportion of total crime.”
‘Think so? Billions of $$$ lost to cybercrime -every- year (see Symantec’s annual reports) are “insignificant”?
And if you’d bother to check here:
> https://www.akamai.com/us/en/solutions/intelligent-platform/visualizing-akamai/real-time-web-monitor.jsp
… with at least -some- regularity, you’d see the UK leading the way, every day, in getting whacked.
//
I’m sure cybercrime went up many times the other day in the US when they made all password sharing without permission from the service owner a crime, and all visiting a website without the site owner’s permission a crime…. Just think of all the millions of husbands and wives who share accounts and are now committing federal crimes in cyberspace (i.e. “cybercrimes”) every day…
@Bnk, I was going to attempt to refute what I think was your point that cybercrime doesn’t cost society anything, but after 3 re-reads, I’m still not sure that was your point. In any case, since society is made up of people, if you believe cybercrime has no costs, kindly let me have your online banking Id and password. You may have a different perspective then.
NSA… What sort of comment is yours? Meaningless and pointless (yes I know, like mine is)
His comment is relevant to those who can understand it. It’s kind of correct.
So, the miscreants have a microchip on their shoulders now?
Hello Brian,
This is a completely unrelated question, but why do you not enforce https on your website?
All images are loaded over http so even though I try to use https it’s still not secure.
I do wonder how under-reported cyber crime is in the UK and Europe. I expect the real figure to be much higher.
Simple answer: cybercrime is and will be under-reported in the UK all the while that the average police officer hasn’t a clue what’s at issue. Attempting to get the police to understand what’s at issue, let alone actually do something useful about it, is a monumentally difficult task: after the first time most people don’t bother again.
I received an email from an individual claiming to be an HR recruiter a couple of weeks ago. The individual said he had a job in my professional field and in my local region (he acquired my resume info from LinkedIn or Indeed). The individual’s email domain matched the website that he provided a link to. Doing a little quick search led me to believe that he is a scammer who has contacted others with the goal of getting a hold of victim’s social security number and date of birth.
I did further research and found that the scammer has created more than twenty-five fake staffing companies with all the information on the web sites being identical but for the HR directors’ names.
As a warning to others I created a blogger web site with all the information I gathered. It seems the scammer likes using one particular hosting company in Brea California. I have warned the hosting company and provided all the evidence that I gathered and show that the scammer is violating the hosting company’s Terms of Service but their abuse department would rather leave the scammer up and running as they continue to get paid.
You can see the list here:
http://fakestaffing.blogspot.com/
Nice resource, John, but why not update it more often? Last post is from Feb. 2016
it has been updated with a recent find that i had not added. It would be great if an established journalist got the word out about the corrupt nature of the hosting company in California that has allowed this criminal to continue to victimize new people. That hosting company and its employees are accessories to the crime.
As a UK resident, I found this reort some time ago and read it with interest. The one thing which stood out from it was the claim of the report that there is a huge discrepancy between the amount of cybercrime that the police know about – reported crime – and the amount of estimated cybercrime. Quite how they arrived at their estimates is unclear, but the underlying and unstated message is clear : the police need more resources to deal with the problem. To anyone not familiar with the history of the past few years this may seem obvious but not worth emphasising. However, we here are all too aware that funding for the police has been repeatedly cut, that police numbers have been slashed, and that the response of the police to their situation has been to refuse to take on investigations of whole classes of low-level crime. If your car is stolen or broken into, if your house is burgled, don’t expect the police to be interested. By dissuading people from reporting those incidents they enable “reported crime” figures to be kept lower than they should be. In addition, the ongoing investigations into very large numbers of “celebrities” and others following allegations of historical sexual abuse mean that there are severe strains on the police because so many officers are devoted full-time to pursuing those allegations.
As a result the resources available to the police for investigating cybercrime are limited. They also have a major problem in recruiting or training enough people with the right skills and aptitude, something which is not helped by the detailed and intrusive security vetting that applicants have to go through, and all for a job where the pay is no better (and often much worse) than similar jobs in the private sector.
So in dealing with this report you have to read between the lines, understand the context, and know the history. Those estimated figures and claims of under-reporting were being used as a bargaining measure by the police to attempt to get more money from a tight-fisted central government and to increase the priority of this category of crime as against the terrorist-related and sexual-offences categories. Well, good luck with that. I have a feeling that the only way for their chances to improve would be if Murdoch’s News Corporation were to be crippled by a massive cyberattack. It’s amazing how much politicians can be influenced by the support for a particular policy of a powerful media tycoon …