Multiple stories published here over the past few weeks have examined the disruptive power of hacked “Internet of Things” (IoT) devices such as routers, IP cameras and digital video recorders. This post looks at how crooks are using hacked IoT devices as proxies to hide their true location online as they engage in a variety of other types of cybercriminal activity — from frequenting underground forums to credit card and tax refund fraud.
 Recently, I heard from a cybersecurity researcher who’d created a virtual “honeypot” environment designed to simulate hackable IoT devices. The source, who asked to remain anonymous, said his honeypot soon began seeing traffic destined for Asus and Linksys routers running default credentials. When he examined what that traffic was designed to do, he found his honeypot systems were being told to download a piece of malware from a destination on the Web.
Recently, I heard from a cybersecurity researcher who’d created a virtual “honeypot” environment designed to simulate hackable IoT devices. The source, who asked to remain anonymous, said his honeypot soon began seeing traffic destined for Asus and Linksys routers running default credentials. When he examined what that traffic was designed to do, he found his honeypot systems were being told to download a piece of malware from a destination on the Web.
My source grabbed a copy of the malware, analyzed it, and discovered it had two basic functions: To announce to a set of Internet addresses hard-coded in the malware a registration “I’m here” beacon; and to listen for incoming commands, such as scanning for new vulnerable hosts or running additional malware. He then wrote a script to simulate the hourly “I’m here” beacons, interpret any “download” commands, and then execute the download and “run” commands.
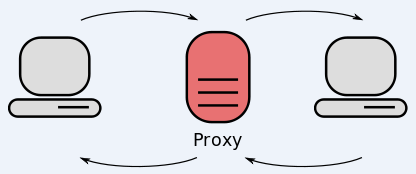
The researcher found that the malware being pushed to his honeypot system was designed to turn his faux infected router into a “SOCKS proxy server,” essentially a host designed to route traffic between a client and a server. Most often, SOCKS proxies are used to anonymize communications because they can help obfuscate the true origin of the client that is using the SOCKS server.
When he realized how his system was being used, my source fired up several more virtual honeypots, and repeated the process. Employing a custom tool that allows the user to intercept (a.k.a. “man-in-the-middle”) encrypted SSL traffic, the researcher was able to collect the underlying encrypted data passing through his SOCKS servers and decrypt it.
What he observed was that all of the systems were being used for a variety of badness, from proxying Web traffic destined for cybercrime forums to testing stolen credit cards at merchant Web sites. Further study of the malware files and the traffic beacons emanating from the honeypot systems indicated his honeypots were being marketed on a Web-based criminal service that sells access to SOCKS proxies in exchange for Bitcoin.
Unfortunately, this type of criminal proxying is hardly new. Crooks have been using hacked PCs to proxy their traffic for eons. KrebsOnSecurity has featured numerous stories about cybercrime services that sell access to hacked computers as a means of helping thieves anonymize their nefarious activities online.
And while the activity that my source witnessed with his honeypot project targeted ill-secured Internet routers, there is no reason the same type of proxying could not be done via other default-insecure IoT devices, such as Internet-based security cameras and digital video recorders.
Indeed, my guess is that this is exactly how these other types of hacked IoT devices are being used right now (in addition to being forced to participate in launching huge denial-of-service attacks against targets that criminals wish to knock offline).
“In a way, this feels like 1995-2000 with computers,” my source told me. “Devices were getting online, antivirus wasn’t as prevalent, and people didn’t know an average person’s computer could be enslaved to do something else. The difference now is, the number of vendors and devices has proliferated, and there is an underground ecosystem with the expertise to fuzz, exploit, write the custom software. Plus, what one person does can be easily shared to a small group or to the whole world.”
ROUTER SECURITY 101
As I wrote last week on the lingering and coming IoT security mess, a great many IoT devices are equipped with little or no security protections. On a large number of Internet-connected DVRs and IP cameras, changing the default passwords on the device’s Web-based administration panel does little to actually change the credentials hard-coded into the devices.
Routers, on the other hand, generally have a bit more security built in, but users still need to take several steps to harden these devices out-of-the-box.
For starters, make sure to change the default credentials on the router. This is the username and password pair that was factory installed by the router maker. The administrative page of most commercial routers can be accessed by typing 192.168.1.1, or 192.168.0.1 into a Web browser address bar. If neither of those work, try looking up the documentation at the router maker’s site, or checking to see if the address is listed here. If you still can’t find it, open the command prompt (Start > Run/or Search for “cmd”) and then enter ipconfig. The address you need should be next to Default Gateway under your Local Area Connection.
If you don’t know your router’s default username and password, you can look it up here. Leaving these as-is out-of-the-box is a very bad idea. Most modern routers will let you change both the default user name and password, so do both if you can. But it’s most important to pick a strong password.
When you’ve changed the default password, you’ll want to encrypt your connection if you’re using a wireless router (one that broadcasts your modem’s Internet connection so that it can be accessed via wireless devices, like tablets and smart phones). Onguardonline.gov has published some video how-tos on enabling wireless encryption on your router. WPA2 is the strongest encryption technology available in most modern routers, followed by WPA and WEP (the latter is fairly trivial to crack with open source tools, so don’t use it unless it’s your only option).
But even users who have a strong router password and have protected their wireless Internet connection with a strong WPA2 passphrase may have the security of their routers undermined by security flaws built into these routers. At issue is a technology called “Wi-Fi Protected Setup” (WPS) that ships with many routers marketed to consumers and small businesses. According to the Wi-Fi Alliance, an industry group, WPS is “designed to ease the task of setting up and configuring security on wireless local area networks. WPS enables typical users who possess little understanding of traditional Wi-Fi configuration and security settings to automatically configure new wireless networks, add new devices and enable security.”
However, WPS also may expose routers to easy compromise. Read more about this vulnerability here. If your router is among those listed as vulnerable, see if you can disable WPS from the router’s administration page. If you’re not sure whether it can be, or if you’d like to see whether your router maker has shipped an update to fix the WPS problem on their hardware, check this spreadsheet.
Finally, the hardware inside consumer routers is controlled by software known as “firmware,” and occasionally the companies that make these products ship updates for their firmware to correct security and stability issues. When you’re logged in to the administrative panel, if your router prompts you to update the firmware, it’s a good idea to take care of that at some point. If and when you decide to take this step, please be sure to follow the manufacturer’s instructions to the letter: Failing to do so could leave you with an oversized and expensive paperweight.
Personally, I never run the stock firmware that ships with these devices. Over the years, I’ve replaced the firmware in various routers I purchased with an open source alternative, such as DD-WRT (my favorite) or Tomato. These flavors generally are more secure and offer a much broader array of options and configurations. Again, though, before you embark on swapping out your router’s stock firmware with an open source alternative, take the time to research whether your router model is compatible, and that you understand and carefully observe all of the instructions involved in updating the firmware.
Since October is officially National Cybersecurity Awareness Month, it probably makes sense to note that the above tips on router security come directly from a piece I wrote a while back called Tools for a Safer PC, which includes a number of other suggestions to help beef up your personal and network security.




The company Synology just came out with a new router that has outstanding firmware installed, which is very similar to their N.A.S. drives.
Great article !
AWESOME article, GRC.com TWITS computer security podcast also covers many of the security flaws in consumer routers and how to protect yourself against them in several podcasts for further research for anyone interested.
Like the good ole 2000s in computing…. Never thought of it that way, but it works well for comparison. Nice article.
Just wait for IOT 2.0 when the dishwasher can ‘like’ the blender and the old microwave from your college dorm can keep all the appliances up to date on the lastest chemtrails outrage.
There’s a lot of talk this year about the possibility that wireless router designers will make it impossible to install DD-WRT or Tomato on their products for sale in the USA.
https://www.wired.com/2016/03/way-go-fcc-now-manufacturers-locking-routers/
The motivation is preventing end-users from generating interference, especially in the 5GHz band, by fiddling with the software radios in the routers. That’s a tolerably good goal.
But if the cheapest way to prevent this is to build routers than can’t have their firmware changed, the integrity of the internet becomes critically dependent on the WiFi makers. Can they repel people trying to hack their source code? If vulnerabilities appear, will they be able to update their devices in the field?
Things are getting brittle on the net.
People should just bite the bullet and buy a $60 router ( ER-X or hEX ) and do away with these crappy multifunction devices that are bad at both. Then they can use their AP’s as bridge devices and not have to deal with the FCC regs interfering with OpenWRT.
The IoT standards setting process could take 5-10 years to complete, advises one product manager. Many new standards are being proposed for communications protocols, software, and services. Some key issues include the range of IoT applications as well establishing coordinating among different standards-setting groups.
“Where are the IoT industry standards?”
http://semiengineering.com/where-are-the-iot-industry-standards/
I have a DVR that is connected via cable. Is there anything I can do to keep it from being exploited?
I have a smart tv also. For downloading applications I have to enter a username and password.
There is nothing stopping law enforcement from using honeypots to intercept the criminal activity passing through imitation SOCKS servers. Except that internet law enforcement is in it’s infancy.
Reminds me of cattle rustling in the US 1880s. Once law enforcement got into gear and a few cattle rustlers were caught, and hanged, that crime was no longer very appealing.
These proxy hiding guys are going to get easily caught as soon as law enforcement decides to lure and catch them.
If only they had worldwide jurisdiction… it’s the dream of every dictator, including democratically elected ones!
Yes indeed!
Interpol manages to function without a dictator overload. But in the field of cybercrime, they certainly have not hit their stride.
Cattle rustling is still a problem in Texas. I don’t have a link, but the San Antonio Express-News had an article about it sometime in the past 6 months. There are still plenty of public roads with cattle guards that run through ranches. No wire cutting required.
Just remember that you should only update the firmware if you’re sure the device hasn’t already been hacked. If it has, the only safe course is to go out and buy a newer, more secure, device.
Doesn’t sound very practical to me. Even the best most secure devices have vulnerabilities and patches and updates. Like cisco is one of the best in network world, and they fix issues all the time. There’s no one to upgrade to at that point lol.
Also, how many people are going to go out and buy a new camera? The entire point of getting that cheap crappy Chinese knockoff camera was the price. And most people getting them aren’t going to pay to replace them.
Now, there ARE some devices out there that are so incredibly vulnerable and crappy, one should get rid of them. If one has the knowledge to know this stuff in the first place.
No, bad advice.
The open source pfSense router also provides a serious commercial-level router with various options that include using an ol’ PC-box to fully supported, pre-built hardware. We chose pfSense over Cisco in 2008 and have never been disappointed.
Put this in angle-brackets and it got wiped/hidden in my posting.
pfSense site: https://www.pfsense.org/
pfSense is good. I’ve been using it for the last few years without any issues.
For those that might not know, pfSense is basicly an OS that will work fine with a wide variety of hardware. It can turn an older desktop into a router. So rather than throwing out that old machine just because it runs so slow, wipe out the existing operating system and go this way.
Router Security 102
http://www.routersecurity.org
For several hours earlier I was blocked from accessing this web site. Even just reading was forbidden. Any attempt to do so resulted in the browser being redirected to some Google site, which itself was not working correctly at the time.
An explanation for this seems warranted, along with an apology and a promise that complaints or evidence of abusive behavior will be investigated more thoroughly in the future so as to avoid punishing the wrong user. I had done nothing abusive; I should not have been banned, even temporarily.
I would further submit that banning a user from even *reading* the articles here is excessive and unnecessary. Spammers and other troublemakers can surely be dealt with adequately by banning them from posting comments while still permitting them to read. That would also reduce, though not eliminate, the harm from punishing the wrong person, since lurkers who mainly just read, likely in the majority, would no longer be impacted if wrongly accused.
@Skrool, calm down. This site was attacked several times today, causing issues for some readers. It wasn’t personal (at least it wasn’t personal toward you). Nobody was banned. Take a deep breath.
https://status.cloud.google.com/incident/compute/16020
More than likely you have a browser exploit or a PUP on your PC that is redirecting your sessions. This has become a serious problem as of late, for my clients.
You might start out with downloading AdwCleaner from majorgeeks and run it to see what if anything it finds. I delete everything it finds myself, and have never had bad side effects. It can usually remove such pests even better than MBAM, but it also wouldn’t hurt downloading at least the free scanner version, of that as well, to see what else may be on board. Hopefully, if your version of Windows is new enough, you can enable the onboard AV and AM utility called Windows Defender to at least get the minimum of real time protection. Make sure to run as a standard user as well.
If you are using OSX or other apple product, it wouldn’t hurt to investigate anything similar to this advice at the Apple store; also quit using Safari and switch to Chrome or other FOSS based browser for Apple. I’d do that on cell phones as well.
Another fabulous article be the esteemed Mr Krebs !!
No wonder your website is the recipient of so many
DDOS.
You are one of my best bookmarks!
For the untech like me hear is an article
explaining the difference between routers
and modems.
http://www.techbout.com/difference-between-modem-router-17059/
We only have a modem in our lower middle class
household. As this above piece mentions, some
modems combine both functions into one.
We have no router (the second piece of equipment),
yet our cell phones enjoys the Internet and the wifey
can use her laptop throughout the house.
So now having confused myself, do I still need to
reset the username and password??
Thank you for any replies.
Are you a Verizon customer? Some ISPs will ship devices to their customers that act as both modems and routers.
Mr Krebs, we are on the CenturyLink network.
I did check the list and the Actiontec C1000a
is not mentioned.
The username on this device is admin and the
password is well defined.
I think we are fine.
BTW, you made it to the following:
https://consumerist.com/2016/10/13/millions-of-hijacked-smart-devices-already-aiding-criminals-research-finds/
This campaign by these scumbags, hopefully will lead
to their undoing and downfall.
Thank you for making this deft person a little smarter!
Thanks for your courage and the Krebs’ counterattack.
Yours appears to be a combination modem/router. Which is good. It’s dangerous to have anything directly on the internet without some fort of firewall/router in place! So if yours was indeed only a modem it would be bad.
Yes, your device isn’t on that list, but have you set your own password or is it still the factory default?
If it’s the factory default, yes you need to change the password.
Someguy, thanks for the advise. I found the DNS
again and will follow your command.
Your phones can connect over cellular or of wifi. If your not using wifi then they are using cellular. If your using wifi then your either using your wifi or someone else’s wifi. If your using your wifi then you DO have a router. If your using someone else’s wifi then you are using someone else’s router. If you are using Your router then it is your wifi login credentials that are of concern.
Wifi comes from routers. Wether they are built into one unit with the modem or as a separate unit.
There are devices that also provide cellular ‘hotspots’ provided by cell companies for people that have issues with dead zones or weak cell signal in their homes. These are not routers. These should be looked at as tiny cell towers.
I once had a client that didn’t even know she had a wifi router in her apartment until I saw the list. She insisted the SSID was not hers. Found out later that her son had installed it but she just didn’t understand the “magic” involved. Some simple explanations using plain English and we had her understanding the topology in no time.
If you’re unlucky enough to have AT&T then you have no way to completely bypass their “Residential Gateway.” It has no true bridge mode.
That’s one of the reasons I left AT&T. And if I didn’t want them to spy on my traffic, I would have to pay 50% more.
The IOT is great, but as pointed out it can result in cyber crime. Gartner estimated that at the end of 2016, there will be around 6.4 billion connected objects in use — things like smart refrigerators, smart thermostats, wearable fitness gadget etc. By 2025, there will be 20.8 billion objects making up the IoT therefore being aware of what is pointed out in this blog post is very important. These vulnerabilities can exist anywhere within the IoT — even consumers’ own living rooms. Trend Micro researchers found earlier this year that some Android-based smart televisions are susceptible to attack via third-party apps that people download onto their devices.
I’m honestly surprised, you are still up and readable. But it only took two tries this morning. An article like that would have had “wigi” visiting me with cement shoes.
Ok., could the professor, have dated his powed program? Like how long this has been in the wild? Like several years, say , the old target problem? Where infiltration was found from an iot thermostat? People blamed the vendor, but, this could have been the key thy found into the system?
How close are devices such as this, ready for prime-time and providing adequate protection?
http://www.bitdefender.com/box/
There are no IoT security problems.
There is always a user problem.
2 basic principles for all networked devices:
1) dont expose port 22,23 to internet
2) change web port to something other than 80
Those are basic principles which also applies to PCs, routers etc..
No idea whats all the noise about IoT security.
General security principles apply.
Brian, just got the US-CERT notification about you, it’s here..
It appears I can not change the username
for our Actiontek c1000a!
I am also having a difficult time changing
the password itself! Damm! It was changed
but goes back to the default.
Hear is a website devote entirely to securing
modems and routers.
http://routersecurity.org/bugs.php
I tried for a second time and could not
change either the username nor the password.
I followed the correct procedure and it went
back to the default settings on the underside
of the modem!
CenturyLink must do this so they can turn off
the device for non-payment.
i’ve had no luck with DDWRT or OpenWRT. (Can DDWRT even be updated?) could be something else tho but most low end home routers seem to be junk no matter how well you secure them
here’s another router security checklist:
http://routersecurity.org/checklist.php
Just FYI. Your source is most likely not the first who has implemented such a honeypot. You may want to check our research article on IOTPOT at USENIX WOOT 2015. We had documented lots of details on the DDOS attacks before they got that bad.
Stay away from this guy’s website
and his programs !!
https://www.grc.com/shieldsup
Are you offering a good solid reason why?
Maybe the warning from Hans is reverse psychology?