KrebsOnSecurity received many a missive over the past 24 hours from readers who wanted to know why I’d not written about widespread media reports that Mirai — a malware strain made from hacked “Internet of Things” (IoT) devices such as poorly secured routers and IP cameras — was used to knock the entire country of Liberia offline. The trouble is, as far as I can tell no such nationwide outage actually occurred.
First, a quick recap on Mirai: This blog was taken offline in September following a record 620 Gpbs attack launched by a Mirai botnet. The source code for Mirai was leaked online at the end of September. Since then, the code has been forked several times, resulting in the emergence of several large Mirai-based botnets. In late October, many of the Internet’s top destinations went offline for the better part of a day when Mirai was used to attack Internet infrastructure firm Dyn.
Enter Kevin Beaumont, a security architect from Liverpool, England who on Thursday published a piece on Medium.com about an attack by Mirai against Liberia. Beaumont had been researching the output of an automated Twitter account set up by security researchers to monitor attacks from these various Mirai botnets. That Twitter account, @MiraiAttacks, burps out a tweet with each new Mirai attack, listing the targeted Internet address, the attack type, and the observed duration of the attack.
Beamont’s story noted that a botnet based on Mirai was seen attacking the telecommunications infrastructure in the West African nation of Liberia. Citing anonymous sources, Beaumont said transit providers confirmed an attack of more than 500 Gpbs targeting Liberia’s lone underseas large-transit Internet cable, which Beaumont said “provides a single point of failure for internet access.”
“From monitoring we can see websites hosted in country going offline during the attacks,” Beaumont wrote. “Additionally, a source in country at a Telco has confirmed to a journalist they are seeing intermittent internet connectivity, at times which directly match the attack. The attacks are extremely worrying because they suggest a Mirai operator who has enough capacity to seriously impact systems in a nation state.”
Not long after Beamont’s story went live, a piece at The Hacker News breathlessly announced that hackers using Mirai had succeeded in knocking Liberia off the Internet. The Hacker News piece includes nifty graphics and images of Liberia’s underseas Internet cables. Soon after, ZDNet picked up the outage angle, as did the BBC and The Guardian and a host of other news outlets.
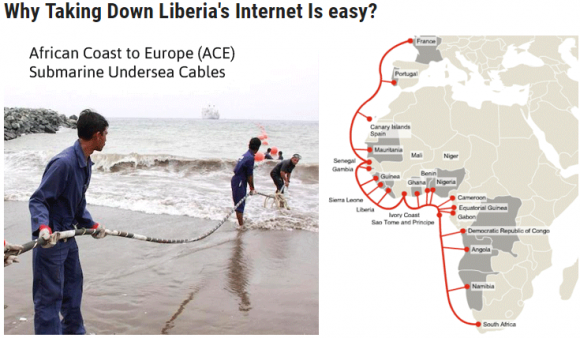
A graphic The Hacker News used to explain Liberia’s susceptibility to a DDoS attack.
The only problem that I can see with these stories is that there does not appear to have been anything close to a country-wide outage as a result of this Mirai attack.
Daniel Brewer, general manager for the Cable Consortium of Liberia, confirmed that his organization has fielded inquiries from news outlets and other interest groups following multiple media reports of a nationwide outage. But he could not point to the reason.
“Both our ACE submarine cable monitoring systems and servers hosted (locally) in LIXP (Liberia Internet Exchange Point) show no downtime in the last 3 weeks,” Brewer said. “While it is likely that a local operator might have experienced a brief outage, we have no knowledge of a national Internet outage and there are no data to [substantiate] that.”
Yes, multiple sources confirm that Mirai was used to launch an attack exceeding 500 Gbps against a mobile telecom provider in Liberia, but those sources also say the provider in question had a denial-of-service attack mitigation plan in place that kicked into action shortly after the attack began.
This was confirmed in a tweet on Thursday by Dyn. The company said in a separate tweet that routing in Liberia has been stable for days.
Akamai, a company with a global Internet presence and visibility, said it saw a dip in traffic levels from Liberia. Akamai tweeted a graphic Thursday evening that indicated traffic to Liberia was lower than normal as compared to traffic patterns from previous days this week. But there was nothing to indicate a nationwide outage, and the dip in traffic may just as well have to do with the fact that the first Thursday of November in Liberia is Thanksgiving, a public holiday there.
“Neither @dynresearch nor @akamai_soti have data supporting the assertion that Liberia suffered a national outage,” tweeted Dyn’s Doug Madory.
To recap: Did a Mirai botnet attack an infrastructure provider in Liberia? No question. Is the IoT problem bad enough that we have to worry about entire countries being knocked offline? Quite possibly. Was there an outage that knocked the country of Liberia offline this week? I have yet to see the evidence to support that claim.




Why go after Liberia ?, they are a very poor country , not a very good target for this type of cyber-attack.
Proof of concept, perhaps?
Their are a lot of smaller countries around Liberia with a lot less internet conductivity to run a “proof of concept” Liberia was chosen for a reason
Many countries on the ACE fiber submarine cable could have been hit at any time , maybe Liberia had the least amount of DDos security protection in place to deal with such a attack.
Did you not read the article you’re commenting on? The Beaumont report was incorrect in claiming the DDoS was targeting Liberia. The DDoS was pointed at a telco in Liberia which happened to have really good mitigation in place. I do like your username btw, and you don’t mean conductivity.
If you look at most of Brians articles, the user with name “IRS ITUNE cards” is almost always the 1st commenter. I suspect some weirdo has some bot setup to notify them of a new post and then they come and blab in the comment sections at the 1st person (lol). Sorta weird IMO
If anything it could have potentially been a test attack just to figure out how powerful it really is. Maybe finding a direct target as easy and ripe for the picking like liberia is the best option for such a test. Not many users at the level in which it would cause mass panic, but would still effectively wipe out service showing what its capable of.
Thankfully not a big problem. Meanwhile, we can procrastinate and do nothing about IoT. Nothing good ever came from an ounce of prevention….
Pre-cisely.
Thanks for the research and the professionalism to stick to facts.
The excuse I’ve heard is that Liberia was a good place to test a wider attack.
BTW, is Gpbs supposed to be Gbps?
No, it actually means Gigapits Ber Second.
Those are bigger,..so that was a big attack,…
What? Brian the manufacturer of these IOT devices already recalled all of them. They said they already fixed all this! Are you kidding me? Is there even a list of what devices are vulnerable? Sort of like dd-wrt has a list of models you can install it on. I don’t think you have shamed the maker enough. Their threats of lawsuits from attorneys that aren’t even licensed to practice law in the states is hilarious. I’m in favor of a story about the people in charge of their turd company. They should be publicly shamed. Time to send out a press release letting the media know their devices still haven’t been fixed even 1% of them.
“Is there even a list of what devices are vulnerable?”
-> https://www.scribd.com/book/328743810/Mirai-Devices
Robert,
That list posted at Scribd was lifted from my story here:
https://krebsonsecurity.com/2016/10/who-makes-the-iot-things-under-attack/
Bk
The News websites you have mentioned, including zdnet and HackerNews, have clearly said that someone is “trying” to take down the Internet and partially succeeded as well. Why do you always think that every story should move around you name? Yes you had been hit by ddos, now move on.
HackerNews did not clearly state “trying.” The headline reads
“Someone is Using Mirai Botnet to Shut Down Internet for an Entire Country”
Sing, it is helpful to recap past events for many reasons.
Also, you might want to “move on” from making harsh judgments about the author when you haven’t been there yourself.
While “The Hacker News” article did say “Someone is trying to take down the whole Internet of a country…”, the headline in the graphic stated, “DDOS Attack Knocks Entire Country Off the Internet” along with an exclamation point within a red triangle. Thus, they used sensationalism and should be called on it.
http://thehackernews.com/2016/11/ddos-attack-mirai-botnet.html
Yeah. The graphic The Hacker News used was hardly subtle:
https://krebsonsecurity.com/miraiknocks/
They have seriously put their names out there on this story. Talk about a swing, and a miss,…
What about you move on? Away from this site back to Etsy where people might be interested in your comments. Which I actually doubt, but who knows, have a try.
I think you need to be a little more respectful Suresh, Brian is simply reporting on something he has been asked to by his readership. He is not bemoaning the fact that he was subject to a DDOS attack – please try and be a little more aware of what you are reading. We are all here to help keep our data and our networks secure and while this article may not directly effect you or me for that matter, these articles help many people and having someone who reports factually and does his home work before posting sensationalist stories is extremely helpful, we could all do witgh taking a leaf out of Brian’s book.
Someone needs to tell us what is really going on in the computer security field. I appreciate Brian Krebs for doing so.
Regards,
Actually, it appears as a concept attack. A can I get the backer I need to do this. Krebs is a news service that verify his information, making it more valuable, it’s verify able. Durn Google. Rather then newsworthy. It’s usable.
Now, I believe, the researchers need to do immediate back looking skillsets. Where did this attack emminate from. The iot’s or a host. Nation state or a player? Did they overload the channel? The cable? Can this be used to overload and break a backbone network? Anyone checked if this can translate to Sat internet systems?
Was there any motivation by the political climate in America where some people like scare-mongering? I wonder.
IoT edge devices in LoRa modems used in 30km range of LoRaWAN don’t use IPv4 & IPv6 stacks.
IoT only can send between 1-255 bytes every 100 seconds on ISM.
This story is polluting the IoT area of interest with silly IT issues with DDOS & DNS issues.
IoT does not need IP actually. As long as it can talk to it’s gateway or peer.
Please stop polluting education for humans.
We only want REAL facts not just media FACTS.
Hyper-Normalization is affecting you now.
“IoT does not need IP actually. As long as it can talk to it’s gateway or peer.”
Without an IP, it CANNOT ‘talk to it’s gateway or peer’. IoT is just like everything else on a network. An IP address is required. Otherwise, there is no connectivity and thus no function.
Real IoT uses hardware cryptography in the shape of a 508a
from Atmel. This provides hardware cryptography with public key. We have solved the issues with security.
We just need the will now to implement it.
We can protect from 99% of all of this with 508a hardware, grow up stop this stupid FEAR campaign and start educating people & companies.
If you’re not part of the solution you’re part of the FEAR WAR problem.
This goes to Anonymous ISIS hackers, your TRAITORS to mankind.
You will be hunted and tagged like all enemies of the people you are.
Anonymous will not let you go unpunished FAKE Anonymous ISIS fighters, working for the man. SHEEP., SILLY KIDS are all SHEEP.
WAKE UP STUPID SHEEP!
I don’t see “FEAR WAR problem” in acknowledging that there is a problem.
I see THE problem as the problem. You fix THE problem and there will not be a problem for anyone to spread fear about. However, the problem is not going to get fixed through cryptography. Cryptography in reality is security through obscurity. This is what feeds the blackhats. It is also what feeds everyone else’s false sense of security that is represented in a never ending cycle of updating for the sake of updating.
THE problem has so much more to do with the kind of thinking most people put to this. Most people tend to think that something is worth buying when it comes with a higher price tag, or when it falls under a brand name that everyone in the world knows, or when it has been given enough positive reviews. It’s all about keeping up with the Jones’s in a world where no one cares to understand anything about what they are buying. From the loley home user to the CEO with the golden parachute.
Some things are just not worth buying or using. THE problem is a serious lack of understanding on the part of the masses that most IoT devices are (at the core) built out of crap and are insecure by design. It is this lack of understand that creates the ‘fear’ you speak of. Ignorance breeds fear. it always has and always will. This cannot be fixed with an update or by a cryptographic algorithm that has already been cracked by the bad guys two years ago.
As for ISIS:
I completely agree.
Cryptography is based on mathematics, not security through obscurity. If something has been encrypted, you can’t just decrypt it based on the fact that the file is now no longer “obscure” and blending in with the crowd. I think you might be thinking of steganography, where you hide a file inside another file, but once it has been found it’s very simple to extract the hidden file.
“…If something has been encrypted, you can’t just decrypt it…”
What? Like HTTPS? What has HTTPS stopped? or have you been paying attention?
I know full well it’s based on math. So is the heart of Javascript, VBScript, and all other programming languages. For that matter, computer technology is all based on math.
“…you can’t just decrypt it…”
Really? Are you sure? What do you think ‘computer hacking’ is all about? If a blackhat can’t fool someone into just giving them the keys, they will take it by force. Depending on how bad they want it. Have you even heard of the idea of ‘reverse engineering’? The entire world has been given all kinds of proof over the years that anything that can be encrypted can also be decrypted.
The issue here is that people develop a false sense of security around things that have no security. If encryption were the answer, we would not be seeing all the mess we see. I’m not saying it’s meaningless. I’m saying that it is dangerous to say something is encrypted and then go about your merry way thinking it’s safe. Too many people are doing that and are getting hurt by it. I am saying that it does not mean what you think it means.
Encryption on it’s own is nto a complete answer. Because there is no one single technology, no matter how well implemented and managed that is “The” answer.
Having said that, the technology of encryption is not typically what fails. It is the breakdown of the people and process behind it that fails.
A well implemented and managed encryption scheme renders pretty much everything you say, as being meaningless nonsense.
“…A well implemented and managed encryption scheme renders pretty much everything you say, as being meaningless nonsense.”
I’ll have to remember that the next time I try to pull up krebsonsecurity.com over https as I watch it fail for a ddos attack.
I do understand that there are multiple things that need to be done. That no one thing will fix everything. Infact, it is usually everyone else that seems to flock toward that one action (that one thing) under the thinking that it will fix everything. I just find it funny that while the world throws everything in one direction, it still falls apart.
You can ignore what I say here if you wish. But these issues are growing in size and scale. It is no longer about individuals. It is huge chunks of the web across the planet.
“It is the breakdown of the people and process behind it that fails.”
That is exactly what I’ve been saying. While “everything you say, as being meaningless nonsense.”
Encryption does not prevent DDOS attacks. What are you talking about?
Tell that to Mark Edgar
Security experts have dismissed last week’s reports that Liberia’s entire internet infrastructure was taken down by a DDoS attack, stating that this story was “simply not true”.
Why is the date for this post Nov 16 when, based on comments left 4 days prior to today, Nov 8, the post was written on or before Nov 4?
John,
The big number is the day. Also, there is a date and time stamp at the end of every story. This one says
This entry was posted on Friday, November 4th, 2016 at 3:20 pm and is filed under Other.
****HACK TODAY AND GET FREE MONEY FOR CHRISTMAS****
We are hackers, We just succeeded with a new invention. We’ve got hacked ATM cards for sale. These hacked ATM cards have been programmed to work on any ATM machine. The cards have been topped up with $100,000 With a daily withdrawal of $3000 per day ( depending on how it is programmed ). The cards have got some special features which includes;
*Deactivating the CCTV cameras when inserted in the ATM machine,
* It comes with a 4 digit pin just like every other ATM card,
* It can be topped up when the money in it has been exhausted,
*It is untraceable and undetected.
The cards were successfully programmed with the hard-work of our hackers in USA. And they are cloned using a writer (MSR 606).
If you need to get the cards, order one today and it will be shipped to your location. Contact us on to get one..
SIMPLEHACKERS2@GMAIL.COM
***********Serious buyers only**********
Hi Brian, I wonder why you never talk about the ransomware Locky and guys who are behind ? Like many other men, I receive every days spam asking me to install a file downloading this malware.
I’ve written quite a bit recently about ransomware
https://krebsonsecurity.com/tag/ransomware/
Are these botnets being used to compromise/brute force online accounts?
My wife’s Microsoft account had a successful sign in yesterday from a Chinese IP address and when I browsed to it, it was an IP camera – username and password were both “admin”.
Scary thing is her password was 12 random upper, lower, numbers, and symbols!?!
Microsoft account + strong password being accessed by an IoT device = me super spooked.