A recent, massive spike in sophisticated and successful phishing attacks is prompting many universities to speed up timetables for deploying mandatory two-factor authentication (2FA) — requiring a one-time code in addition to a password — for access to student and faculty services online. This is the story of one university that accelerated plans to require 2FA after witnessing nearly twice as many phishing victims in the first two-and-half months of this year than it saw in all of 2015.
 Bowling Green State University in Ohio has more than 20,000 students and faculty, and like virtually any other mid-sized state school its Internet users are constantly under attack from scammers trying to phish login credentials for email and online services.
Bowling Green State University in Ohio has more than 20,000 students and faculty, and like virtually any other mid-sized state school its Internet users are constantly under attack from scammers trying to phish login credentials for email and online services.
BGSU had planned later this summer to make 2FA mandatory for access to the school’s portal — the primary place where students register for classes, pay bills, and otherwise manage their financial relationship to the university.
That is, until a surge in successful phishing attacks resulted in several students having bank accounts and W-2 tax forms siphoned.
On March 1, 2017 all BGSU account holders were required to change their passwords, and on March 15, 2017 two-factor authentication (Duo) protection was placed in front of the MyBGSU portal [full disclosure: Duo is a longtime advertiser on KrebsOnSecurity].
Matt Haschak, director of IT security and infrastructure at BGSU, said the number of compromised accounts detected at BGSU has risen from 250 in calendar year 2015 to 1000 in 2016, and to approximately 400 in the first 75 days of 2017.
Left unchecked, phishers are on track to steal credentials from nearly 10 percent of the BGSU student body by the end of this year. The university has offered 2FA options for its portal access since June 2016, but until this month few students or faculty were using it, Haschak said.
“We saw very low adoption when it was voluntary,” he said. “And typically the people who adopted it were not my big security risks.”
Haschak said it’s clear that the scale and size of the phishing problem is hardly unique to BGSU.
“As I keep preaching to our campus community, this is not unique to BGSU,” Haschak said. “I’ve been talking a lot lately to my counterparts at universities in Ohio and elsewhere, and we’re all getting hit with these attacks very heavily right now. Some of the phishing scams are pretty good, but unfortunately some are god-awful, and I think people are just not thinking or they’re too busy in their day, they receive something on their phone and they just click it.”
Last month, an especially tricky phishing scam fooled several students who are also employed at the university into giving away their BGSU portal passwords, after which the thieves changed the victims’ direct deposit information so that their money went to accounts controlled by the phishers.
In other scams, the phishers would change the routing number for a bank account tied to a portal user, and then cancel that student’s classes near the beginning of a semester — thus kicking off a fraudulent refund.
One of the victims even had a fraudulent tax refund request filed in her name with the IRS as a result, Haschak said.
“They went in and looked at her W-2 information, which is also available via the portal,” he said.
While BGSU sends an email each time account information is changed, the thieves also have been phishing faculty and staff email accounts — which allows the crooks to delete the notification emails.
“The bad guys also went in and deleted the emails we sent, and then deleted the messages from the victim’s trash folder,” Haschak said.
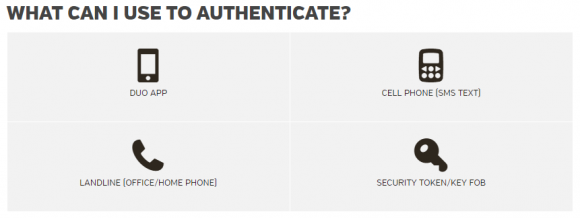
Part of BGSU’s messaging to students and faculty about the new 2FA requirements for university portal access.
Ultimately, BGSU opted to roll out 2FA in a second stage for university email, mainly because of the logistics and support issues involved, but also because they wanted to focus on protecting the personally identifiable information in the BGSU portal as quickly as possible.
For now, BGSU is working on automating the opt-in for 2FA on university email. The 2FA system in front of its portal provides several 2FA options for students, including the Duo app, security tokens, or one-time codes sent via phone or SMS.
“If the numbers of compromised accounts keep increasing at the rate they are, we may get to that next level a lot sooner than our current roadmap for email access,” Haschak said.
2FA, also called multi-factor authentication or two-step verification, is a great way to dramatically improve the security of on online account — whether it’s at your bank, a file-sharing service, or your email. The idea is that even if thieves manage to snag your username and password — through phishing or via password-stealing malware — they still need access to that second factor to successfully impersonate you to the system.
Are you taking full advantage of 2FA options available to your various online accounts? Check out twofactorauth.org to find out where you might be able to harden your online account security.




My oldest is at Cal State Fullerton and they use 2FA. For his generation 2FA is not an inconvenience and appears to be widely adopted when made available. Good to know his school has been proactive in this area.
The issue is the older people who are involved in decisions that lack the know-how to be more security-oriented or protected
47 year old IT Tech.
“The issue is the older people who are involved in decisions that lack the know-how to be more security-oriented or protected”
Citation needed.
Age has nothing to do with it. I am pretty old myself and I know far more than most of the younger IT people employed at my college (and I am not in IT).
We had a spear phishing attack recently and it took 6 hours from the time that I reported it until something was done by our young tech support people. Then our youngish IT guy sends out a notification about a “fishing attack” (sic). What’s worse is that he posted the phishing link in his email with instructions not to click on it.
Honestly, colleges don’t get the best IT people, since they have to compete for talent with better paying organizations. And once people are in place, there is not much meaningful job performance evaluation. Personally, I think colleges should outsource their security or at least deploy third party tools like BGSU with duo.
It would be real nice if all major banks would utilize 2FA
I would have expected by now California to have passed a law requiring all CA financial institutions to use 2FA. My CA-based credit union sure doesn’t. CA seems to lead the way in areas of consumer information privacy/protection.
When it comes to your bank, may I ask why wait? if your bank or credit union is using weak pins, or no 2FA and you are security minded why are you banking with them? Yes Banks and CUs have ‘good’ anomaly detection systems, but that is just one layer of defense, I am glad I am with a bank that treats all layers with importance.
Wells Fargo and CitiBank have it
I have a VISA Citibank account.
I looked Online to find a way to add 2FA and was sent to an 800 number by ‘Online chat’ to talk to the “team” about setting up ‘multi factor authentication. I talked to 3 different people before I found someone who even knew what 2FA or multi factor authentication meant.
Seems there is no such thing as 2FA or multifactor authentication for Online banking at that section Citibank.
So much for that added protection for my account.
I found neither VISA nor Chase, another too-big-to-fall, is not willing fix security holes, even after a publication. Only thing I can do is to stop my business with both.
I found neither VISA nor Chase, another too-big-to-fall, is willing to fix security holes, even after a publication. Only thing I can do is to stop my business with both.
It’s interesting. I think it’s who you get on the phone when you call the bank support line. I received a new Visa from Citibank. Then I noticed it had the near field access icon (or some call it the RFI symbol) and I d0n’t want this feature. When I called I got the usual scripted feedback of turn it on with your phone blah blah blah, which has nothing to do with the card. I was finally elevated to a supervisor who wanted to know what I was talking about. She went back and did research and It turns out that the bank can turn this feature OFF in the bank system. I did this, and voila, the card no longer works as a magic wand at near field terminal. 🙂 Some people love this stuff, especially the retailers who can get people through a transaction faster. For me, it’s something else I need to worry about, so I turned it off.
Now back to the issue at hand, 2FA. Again, this can get lost in the scripting with the agents, so if you are not satisfied with the answer, escalate it!
I’ve been with Wells Fargo (unfortunately) for many years, and I find no knowledge that they use 2FA. Earlier today I even stressed to them in feedback regarding their revised website that they need 2 factor authorization. If you have a link, please supply.
I bank with WF as well. Even though their website states they support the RSA SecureID for 2FA, I’ve yet to figure out how to get one.
https://twofactorauth.org/#banking
https://www.wellsfargo.com/privacy-security/advanced-access
And then I went to their FAQ and noticed this answer. Maybe I’ll just call the number instead of their standard customer support.
If you lose your RSA SecurID device, you can request a new device for a one-time charge of $25, which includes shipping and handling. Call 1-866-609-3037 to place your order.
Incredibly, most brokerage, finance and investments websites such as Ameritrade do NOT have multi-factor authentication. Shame on them !!!
Even scarier is many financial groups limit the password size between 6 and 10 characters or won’t allow special characters…. Oh my…
Toronto Dominion (TD Bank).
2Fa? no.
Website works with Chrome? no.
Made me whole when a skimmer drained my account? yes,
Considering switching? yes.
Glad to see my alma mater making the right move.
It a good change, but the criminals will catch up. Let’s start a timer till when the Duo app is first hacked on Andriod devices…
– hack the Andriod phone
– get the address of the email account used by the phone
– hack the Duo app or Andriod comm port to send the 2FA code somewhere else
– send a phishing message to the email address
– proceed as before.
And, I’d think the same people most likely to get their Android compromised would be the same people most likely phished–same destination, different path.
Security is a cat-and-mouse game. There’s no “perfect” security, only “better.” All you can do is make it harder and more expensive for attackers. Zero-day exploits for android are very rare and expensive to acquire.
However, out of date android devices (like ones where the carrier doesn’t push out the updates in a timely fashion) are a real problem. But Duo does have options to only allow patched and up-to-date versions of iOS, android, etc.
Using push-based 2FA instead of phone calls, SMS, or timer-based one-time codes makes things a lot harder for attackers. What you really want now is one of those Yubikey U2F tokens.
Great article. Recently there is also few discussions on difference between two-factor authentification and two or multi step authentification, that realy make sense(2FA vs 2SA), so in my opinion this article could at least introduce readers in different opinions on subject of 2FA and 2SA from writter point of view.
In the internet Security news today, Instagram has enabled 2FA on their website.
Fascinating insight from the IT head: “We saw very low adoption when [2FA] was voluntary,” he said. “And typically the people who adopted it were not my big security risks.” So true with so much technology risk!
Are all these phishing attacks the Bowling Green Massacre we’ve been hearing so much about?
“In other scams, the phishers would change the routing number for a bank account tied to a portal user, and then cancel that student’s classes near the beginning of a semester — thus kicking off a fraudulent refund.”
I never cease to be amazed at the creativity of crooks when it comes to getting their hands on someone else’s money. Kudos to BGSU for doing something about it.
If I know student university job’s pay the crooks probably got away with about $50 dollars total
You may think that.
If a student has full load classes and the bill totals $2,000 which the student paid it in full. The thieves cancel the classes and the university refunds the billed paid. When you add up the number of students in that group, it is a big pay off. The bad part is that the student finds out that his/her classes were cancelled and has to re register for the classes again and pay again.
What os the number one now? And where is it Usa ?
Bank trfanfers? Paypal jobs? Romance jobs?
Dumps jobs?
“We saw very low adoption when it was voluntary.”
This just shows how the younger generation (most people) have no concept of online security.
But his is a university. Are the providing any awareness training? We talk about it for our employees. Heck they might event do it for their employees. But what of the students?
I find it interesting that this story doesn’t knock the fact that the two factor authentication can use texts when you just wrote the eBay story very unhappy their system will rely on texts?
Text messages are better than what the school had before, so it’s a step up. The Ebay story is about a step down in security.
Although it’s better than nothing, 2FA using text/phone verification is still a problem. I had someone social engineer their way into my banking acct and change the 2FA verification # to theirs. Thankfully, my bank sent an email notice of change on the acct and I was able to lock it down before any further damage was done. My bank now uses the one time code (via Authenticator app) model and I’ve recommended to all my friends that they use that whenever possible.
I’m still trying to figure out how people fall for phishing emails to begin with. I truly don’t get it. I can maybe understand it if the victim was say over 70 yrs old….maybe.
P. T. Barnum figured it out a century ago.
2fa is for the user. It is about making the end user ‘feel’ better about whatever it is they are doing. There is no real security involved here. If one were to actually follow this site, one would come to realize that the main problems come from the companies, individuals, and staff that are given control over the servers, networks, infrastructure, tools, and equipment. This does NOT change with whatever the method is for login by the user.
There are certain truths that people simply refuse to see. With regard to IT security….. once the bad guys are in, there is absolutely NOTHING the end user can do except walk away and just not use the service. The bad guys are sometimes people from within. The bad guys are so often people allowed in by the people that manage the system. 2fa does NOTHING about that.
If the younger generation is more likely to believe they are safer with 2fa, it is because they are made to believe that they don’t need to understand anything beyond the Facebook like button. Apple, Microsoft, Sony, Facebook, Twitter, and the federal government will take care of everything for them.
vb, you should read a bit more about how duo works. If someone did hack the phone, simply changing the email address would do nothing.
fraud is like multy-million or even multy multy billion business
fellas who run all kind of schemes are addicted coz its a lot money they make. guys in ukraine russia moldova and romania live in mansions and drive with luxury cars.
the locals know them like some local property or construction business persons. But their main income come from frauds.
needless to say that they invest their money for equipments too
sometimes they hire developers.
its just endless appetite for money. Its like addiction
One of the downside of 2FA is that sometimes it takes too long before it shows up in the text even if you did not change the phone # that is on record.
I had it one time with BOA and utilized it only to wait until the next day before I got it. I watch my account zealously and to be on the lookout for any phishing attempts. Many of the phishing attempt that I got comes from the so called wrong bank.
Any organisation using SMS for 2FA is doing it wrong – offline token generators are the way to go: instant, free, always available, not vulnerable to mobile porting. Google Authenticator is free so there’s no excuse.
….until the server gets hacked.
Fraud is the old story.- now days much better ways to earn is like ponzi schemes like amway loynness and etc.
investment scheme creators can earn like millions in few months.
So fraud are mowdays waste of time !!
No point for that
Watch, next we’ll start seeing major attacks on services like that mentioned in the article or Google, etc. And recall too that RSA got it’s seed factor stolen. That wasn’t cute.
Good article. But, this begs the other question? Why? Is the employee information on an open portal? Why? Is the banking information on an open portal? Grades, classes, that kind of stuff, yes. Social security numbers, wages, addresses, are you kidding!!! Phone numbers, as a reminder dear, when convenience overrides security, everyone loses.
Sori 4 off-topic, but, what, if, subjective, scrutiny, intensity, such, that, every, word, carries, it’s, profound, personal, significance? Watch, those, consumer, protection, seals, on, every, food, supply, & Keep Looking Up!!
Can’t make 2FA optional … lazy and unaware people are the norm and not the exception, so you need to protect them from themselves.
Here’s a good list of 2FA and non-2FA sites
https://twofactorauth.org/
Hi Brian – thanks for the good work. I wasn’t sure how to reach you, but thought this might interest you. The other day we had a malware attack on an AS400 server where I work.
Nothing is safe…
While awaiting a scheduled TurboTax callback I received a call that began with a recorded voice saying “Here is your callback, press 1 to continue.” I pressed 1. It connected me to an Indian-sounding fellow who said, “Hi, is this ?” I said “Yes.” He said, “And you have Medicare?” I hung up. Then I got the TurboTax callback. D’oh….
Crazy coincidence? Legitimate callback contractor system error on a busy day, connecting to the wrong support service? Or callback contractor system hacked so phishers can beat TurboTax and get the word “yes” (or more)? Scary.