A greater number of ATM skimming incidents now involve so-called “insert skimmers,” wafer-thin fraud devices made to fit snugly and invisibly inside a cash machine’s card acceptance slot. New evidence suggests that at least some of these insert skimmers — which record card data and store it on a tiny embedded flash drive — are equipped with technology allowing them to transmit stolen card data wirelessly via infrared, the same communications technology that powers a TV remote control.
Last month the Oklahoma City metropolitan area experienced rash of ATM attacks involving insert skimmers. The local KFOR news channel on June 28, 2017 ran a story stating that at least four banks in the area were hit with insert skimmers.
The story quoted a local police detective saying “the skimmer contains an antenna which transmits your card information to a tiny camera hidden somewhere outside the ATM.”
Financial industry sources tell KrebsOnSecurity that preliminary analysis of the insert skimmers used in the attacks suggests they were configured to transmit stolen card data wirelessly to the hidden camera using infrared, a short-range communications technology most commonly found in television remote controls.
Here’s a look at one of the insert skimmers that Oklahoma authorities recently seized from a compromised ATM:
An insert skimmer retrieved from a compromised cash machine in Oklahoma City. Image: KrebsOnSecurity.com.
In such an attack, the hidden camera has a dual function: To record time-stamped videos of ATM users entering their PINs; and to receive card data recorded and transmitted by the insert skimmer. In this scenario, the fraudster could leave the insert skimmer embedded in the ATM’s card acceptance slot, and merely swap out the hidden camera whenever its internal battery is expected to be depleted.
Of course, the insert skimmer also operates on an embedded battery, but according to my sources the skimmer in question was designed to turn on only when someone uses the cash machine, thereby preserving the battery.
Thieves involved in skimming attacks have hidden spy cameras in some pretty ingenious places, such as a brochure rack to the side of the cash machine or a safety mirror affixed above the cash machine (some ATMs legitimately place these mirrors so that customers will be alerted if someone is standing behind them at the machine).
More often than not, however, hidden cameras are placed behind tiny pinholes cut into false fascias that thieves install directly above or beside the PIN pad. Unfortunately, I don’t have a picture of a hidden camera used in the recent Oklahoma City insert skimming attacks.
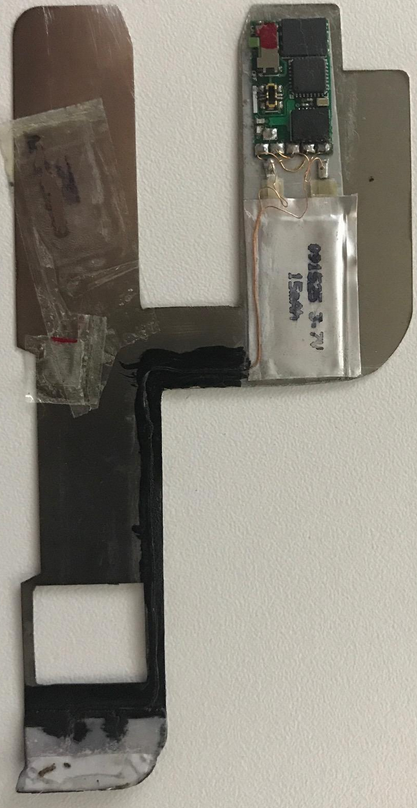
Here’s a closer look at the insert skimmer found in Oklahoma:

Image: KrebsOnSecurity.com.
A source at a financial institution in Oklahoma shared the following images of the individuals who are suspected of installing these insert skimming devices.

Individuals suspected of installing insert skimmers in a rash of skimming attacks last month in Oklahoma City. Image: KrebsOnSecurity.com.
As this skimming attack illustrates, most skimmers rely on a hidden camera to record the victim’s PIN, so it’s a good idea to cover the pin pad with your hand, purse or wallet while you enter it.
Yes, there are skimming devices that rely on non-video methods to obtain the PIN (such as PIN pad overlays), but these devices are comparatively rare and quite a bit more expensive for fraudsters to build and/or buy.
So cover the PIN pad. It also protects you against some ne’er-do-well behind you at the ATM “shoulder surfing” you to learn your PIN (which would likely be followed by a whack on the head).
It’s an elegant and simple solution to a growing problem. But you’d be amazed at how many people fail to take this basic, hassle-free precaution.
If you’re as fascinated as I am with all these skimming devices, check out my series All About Skimmers.




Good Article
First!
Slick! No wifi signal to sniff to give it away!
Does mean you have to show up in person, to collect the hidden camera, though.
Security through obscurity doesn’t work for the bad guys, either!
Thanks, Brian!
That is what I was thinking too – it would also be jam proof (until someone comes up with an IR jammer).
Has any skimming attackers every been caught and convicted? I have to guess that the penalty, if caught, would be minimal. They are stealing “data”, not money.
Drawing a connection between the data theft and unauthorized usage of a cloned ATM card is well beyond the capabilities of most any law enforcement. The buyers of the card data, the card cloners, and the users of the cloned ATM cards are likely all different people. It’s only the users of the cloned ATM cards, who are actually stealing money, that are likely to be prosecuted.
We have caught attackers red handed several times. They will be arrested, but either no charges brought or just fines assessed. It is pretty sad that there seems to be no major consequence for these guys.
That’s a great question. A quick Google search comes up with a few stories, but I’m guessing there’s not a lot of these guys being caught.
Proud to say I know the people who found the fraud first and got the ball rolling to catch this guy.
http://www.readingeagle.com/news/article/police-man-charged-with-stealing-debit-card-info-from-customers-at-convenience-store-in-wyomissing
This story makes my point. All the charges, like theft, are from activities that happened after the data was captured – when the money was stolen. There are no charges for the skimming attack.
“Identity theft” is related to the skimming attack (third paragraph goes into a thought experiment about this), and you could make the case for the conspiracy charge as well. But that’s like asking if someone’s being charged for casing a house before robbing it later that night. Sort of an irrelevant thought experiment as the crimes are inextricably linked.
If someone skims data, and never does anything with it, they’d likely never be caught. Unless the ATM/gas pump maintenance schedule includes a “check for skimmers” step (which they honestly should at this point), there’s not going to be a reported crime/abnormality. Fraudulent card activity is usually the only thing that alerts cardholders and authorities that there’s been a compromise.
As a thought experiment, we could consider what the possible charges would be if, instead of cloning cards, these attackers simply sold the information. Would THEY still be charged with identity theft if they sold the information to a third party, who then cloned the cards? Since more than three people were involved, I’d imagine the conspiracy charge would still persist. I’m not a lawyer or cop, but “theft by unlawful taking or disposition” seems vague enough that they could still be charged with that. “Unjust enrichment” is something I’ve heard of, too. I’d like to see someone do this now, just so we can get an idea for the charges that would be brought up.
Thank you so much for keeping us informed on new and developing threats to our security and privacy. Also for your interest in your subscribers.
Larry
I thought this was going to involve the hidden cameras using infrared to see which buttons you pushed even if you covered the pad.
You are thinking of thermal cameras, which may detect changes in the infrared frequency, but does it passively, and does not have a light or laser diode. The image tube does this passive detecting.
A few weeks ago on TWIT’s “Security Now”, Robert Bellecer said he finally found a skimmer after yanking those card readers for seven years. He took the skimmer. His Twitter is padresj.
I still yank the card readers, though my confidence level that I know what I’m doing is low. Obviously it would help to train on a real skimmer.
Many ATM machines are eliminating such card reader by building it within the machine so you don’t need to yank them. Better yet use your phone using NFC as a mean to withdraw cash or the cardless ATM where you use the bank app to request cash.
now why would Pharrell Williams and Macklemore want to do this kind of stuff don’t their music give them enough money?
Since these circuits are being manufactured, I would think it may be possible (with enough resources and time) to figure out what company made the components and date of mfg, list of companies/people that ordered them in that time frame, and so on. There are only so many chip and PCB fab places. Just a thought. I do know there are lots of small assembly places, but the combination of PCB and chips may be able to be correlated, if the FBI or similar keeps any databases on such… just a thought.
Could I translate your article to Portuguese and insert on my blog?
Why don’t you link to a Google Translate(d) version of this page? No copyright infringement, credit where credit is due, and full access to Portuguese readers, including all comments right up to the time of reading!
Google Translate is horrible off for some languages.
I did try just to see if it is possible, but google translator doesn’t get the subtle and technical stuff.
I am preferring to “tap” at stores. I know ATM’s you can’t do that, but the less I have enter a PIN, the better.
I’m going to have to start pulling out my phone camera and checking for infrared emissions. Thank you for upgrading my overall paranoia.
Brian people are so lazy they just keep on their practice of not learning and protecting themselves as they should. Like any other security issue the problem is the user and bank/financial institution for not informing clients…
With more interconnect devices the issue gets even more scary IE: remote car security systems, cell phones, camera’s that have brains, homes with security systems that can be programmed and the list just goes on…
It’s a little unfair to call people “lazy” for not knowing about all these technical exploits and knowing how to protect themselves from them.
What the general public do suffer from is a trap that’s all too easy to fall into, and indeed they are being led into it all too often.
That trap is to assume that the financial institutions and the authorities are protecting them. It is often the banks and the cops and the politicians that are leading people directly into this trap. While some things are being done to protect consumers and their identities, clearly more could be done.
I suspect that most ATM users have no idea about the existence of skimmers, extra cameras, etc., so they’re only likely to cover the PIN pad if someone is standing behind them.
It seems a dereliction on the part of manufacturers and/or banks, not to place a simple visual aid, designed to remind users to cover the key pad when entering their pin. It seems such a simple step to maybe, help protect the user and the financial institution from loss.
Most ATMs I’ve used have a little animation showing a hand covering the PIN pad. I doubt most people pay attention.
There is something like that on the gas pumps at Costco.
Is this the end of the ATM card?
This helps me understand the rationale behind banks such as Wells Fargo’s new app feature – cardless ATM transactions which require one-time codes.
But I wonder how long it will take before those are compromised as well?
Thank you so much for the updates & tricks to get rid of scammers.
It’s really annoying when some lost their ATM cards or their Money from their ATMs.
Another reason not to use an ATM card. Remember, the ATM card has access to all of you available cash. You are stuck with the loss. A thing to remember, it can take up to six months to transfer account numbers for retirement accounts. That’s up to that many times your parents could live without monies.
I’m surprised. That the nefarious ones have not associated the keypad reader with the open tones associated with with the reader, thru EMF yet. The keypad creates a signal, just as a card reader does. Has anyone checked the chips for antenna yet?
Good article, well worth the read.
“It’s an elegant and simple solution to a growing problem. But you’d be amazed at how many people fail to take this basic, hassle-free precaution.” At a drive-up ATM, I can’t reach the PIN pad with my right hand. Maybe I’ll put a paddle on a stick that I can hold over my hand to mask it. Alternatively, I could put a peg on a glove and poke the buttons with the peg, obscuring which buttons I actually poked.
I have a strategy for this. I place my index, middle, and ring fingers on 3 different numbers, and only press the one I want, but make it look like I press all 3 (for the cameras) if that makes sense. Then, shift my fingers and do the same thing for the next number in my pin. I also do this in conjunction with putting my other hand over the hand doing the pressing whenever possible. Sometimes I’ll even add false key presses into the mix. This also helps to obscure any device that uses thermal imaging to see what buttons were pressed, since you touch many more buttons than needed.
Great ideas. I’ll try these.
You could try getting out of the car every now and then.
Pretty sloppy soldering. What chips were used? Espressif,Atmel, or something else?
Was it based on a commercial package or custom printed circuit board? If it’s custom, you might track down the people behind it.
It would be interesting to dump out the code and see what it was actually doing.
Good questions! Maybe it’s the quality of the picture, but it looks like they might have rubbed off the printing on the chips to make identification and reverse-engineering more difficult.
All that effort, and they still get their picture taken by the ATM camera…
So… these geniuses were captured on a non-hidden camera as they were installing this state-of-the-art skimmer and hidden camera?!
Bwhahahahaha!
Like I tell my kids – if most criminals had the skills to pull off their heists and scams without getting caught, they’d have the skills to earn the money legitimately.
Done with ATMs, not worth the risk or hassle if compromised. I keep some cash on hand as needed, otherwise just use a CC. Doing an occasional trip to a teller to replenish cash stash or deposit the odd check isn’t a big deal.
Just still can’t figure out how the infrared was used in the method described.
How you imagine a device hidden on the inside of the machine to pass IR light to device outside of it. Try with your remote control. Place your hand over the ir-diod and try to change channel on tv.
The camera is usually sensitive for IR, so if the card data is transmitted slowly, the camera could record all the data needed.
BTW, even just a minute of fiddling with a photo editing program would have made the faces on the “camera 04” photo much more identifiable.
I often wonder when I see these kinds of crappy security camera images on the TV news whether they’ve bothered to clean them up or not.
More importantly, does anyone know who that blonde chick is in the picture? I want to do some more “research” on this awful crime. Thank you fellow researchers.
My bank has a “Cardless Cash” option where I can use the bank app on my phone without a card to get cash. It seems like a good way to foil skimmers to me.
First, infrared remotes require line-of-sight. This means the infrared signal won’t transmit through walls or around corners — you need a straight line to the device you’re trying to control. Also, infrared light is so ubiquitous that interference can be a problem. 20 years and I have never seen this (not saying impossible, but). I have seen many other ways to transmit the information but never this. I have dozens of devices, three devices like the one pictured and I know how it was made, chip set from China sold for $400.00 two years ago. The makers of the device were RN’s (not nurses), on Visa overstays or brought in by human traffickers also RN’s, who have been traced to California, New Jersey, Maryland, Florida and Texas to name just a few States. I don’t use ATM cards never have (that’s my money), remember a credit card is the banks/CC companies money, they use antiquated technology and loose money every day. When they do its their loss. If I pay off the balance every month it costs me nothing. Even Mexico used chip only cards 20 plus years ago (had an account with Banco Bital in 95′ when I lived in Mexico City)… wake up America.
ive seen this PCB before in a different model device, same battery and everything.. I also suspect he sharpied large areas?