I cannot recall a previous data breach in which the breached company’s public outreach and response has been so haphazard and ill-conceived as the one coming right now from big-three credit bureau Equifax, which rather clumsily announced Thursday that an intrusion jeopardized Social security numbers and other information on 143 million Americans.
WEB SITE WOES
As noted in yesterday’s breaking story on this breach, the Web site that Equifax advertised as the place where concerned Americans could go to find out whether they were impacted by this breach — equifaxsecurity2017.com —
is completely broken at best, and little more than a stalling tactic or sham at worst.
In the early hours after the breach announcement, the site was being flagged by various browsers as a phishing threat. In some cases, people visiting the site were told they were not affected, only to find they received a different answer when they checked the site with the same information on their mobile phones.
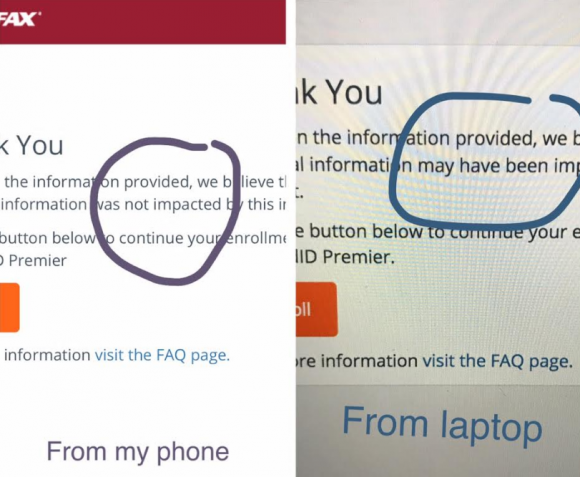
Others (myself included) received not a yes or no answer to the question of whether we were impacted, but instead a message that credit monitoring services we were eligible for were not available and to check back later in the month. The site asked users to enter their last name and last six digits of their SSN, but at the prompting of a reader’s comment I confirmed that just entering gibberish names and numbers produced the same result as the one I saw when I entered my real information: Come back on Sept. 13.
Who’s responsible for this debacle? Well, Equifax of course. But most large companies that can afford to do so hire outside public relations or disaster response firms to walk them through the safest ways to notify affected consumers. In this case, Equifax appears to have hired global PR firm Edelman PR.
What gives me this idea? Until just a couple of hours ago, the copy of WordPress installed at equifaxsecurity2017.com included a publicly accessible user database entry showing a user named “Edelman” was the first (and only?) user registered on the site.
Code that was publicly available on equifaxsecurity2017.com until very recently showed account information for an outside PR firm.
I reached out to Edelman for more information and will update this story when I hear from them.
EARLY WARNING?
In its breach disclosure Thursday, Equifax said it hired an outside computer security forensic firm to investigate as soon as it discovered unauthorized access to its Web site. ZDNet published a story Thursday saying that the outside firm was Alexandria, Va.-based Mandiant — a security firm bought by FireEye in 2014.
Interestingly, anyone who happened to have been monitoring look-alike domains for Equifax.com prior to yesterday’s breach announcement may have had an early clue about the upcoming announcement. One interesting domain that was registered on Sept. 5, 2017 is “equihax.com,” which according to domain registration records was purchased by an Alexandria, Va. resident named Brandan Schondorfer.
A quick Google search shows that Schondorfer works for Mandiant. Ray Watson, a cybersecurity researcher who messaged me this morning on Twitter about this curiosity, said it is likely that Mandiant has been registering domains that might be attractive to phishers hoping to take advantage of public attention to the breach and spoof Equifax’s domain.
Watson said it’s equally likely the equihax.com domain was registered to keep it out of the hands of people who may be looking for domain names they can use to lampoon Equifax for its breach. Schondorfer has not yet returned calls seeking comment.
EQUIFAX EXECS PULL GOLDEN PARACHUTES?
Bloomberg moved a story yesterday indicating that three top executives at Equifax sold millions of dollars worth of stock during the time between when the company says it discovered the breach and when it notified the public and investors.
Shares of Equifax’s stock on the New York Stock Exchange [NSYE:EFX] were down more than 13 percent at time of publication versus yesterday’s price.
The executives reportedly told Bloomberg they didn’t know about the breach when they sold their shares. A law firm in New York has already announced it is investigating potential insider trading claims against Equifax.
CLASS ACTION WAIVER?
Yesterday’s story here pointed out the gross conflict of interest in Equifax’s consumer remedy for this breach: Offering a year’s worth of free credit monitoring services to all Americans via its own in-house credit monitoring service.
This is particularly rich because a) why should anyone trust Equifax to do anything right security-wise after this debacle and b) these credit monitoring services typically hard-sell consumers to sign up for paid credit protection plans when the free coverage expires.
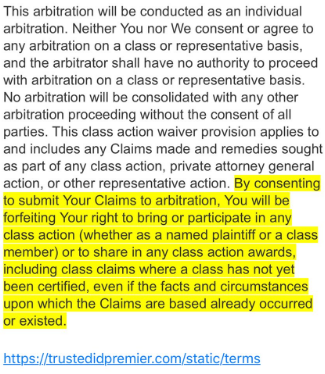
Verbiage from the terms of service from Equifax’s credit monitoring service TrustID Premier.
I have repeatedly urged readers to consider putting a security freeze on their accounts in lieu of or in addition to accepting these free credit monitoring offers, noting that credit monitoring services don’t protect you against identity theft (the most you can hope for is they alert you when ID thieves do steal your identity), while security freezes can prevent thieves from taking out new lines of credit in your name.
Several readers have written in to point out some legalese in the terms of service the Equifax requires all users to acknowledge before signing up for the service seems to include legal verbiage suggesting that those who do sign up for the free service will waive their rights to participate in future class action lawsuits against the company.
KrebsOnSecurity is still awaiting word from an actual lawyer who’s looking at this contract, but let me offer my own two cents on this.
Update, 9:45 p.m. ET: Equifax has updated their breach alert page to include the following response in regard to the unclear legalese:
“In response to consumer inquiries, we have made it clear that the arbitration clause and class action waiver included in the Equifax and TrustedID Premier terms of use does not apply to this cybersecurity incident.”
Original story:
Equifax will almost certainly see itself the target of multiple class action lawsuits as a result of this breach, but there is no guarantee those lawsuits will go the distance and result in a monetary windfall for affected consumers.
Even when these cases do result in a win for the plaintiff class, it can take years. After KrebsOnSecurity broke the story in 2013 that Experian had given access to 200 million consumer records to Vietnamese man running an identity theft service, two different law firms filed class action suits against Experian.
That case was ultimately tossed out of federal court and remanded to state court, where it is ongoing. That case was filed in 2015.
To close out the subject of civil lawsuits as a way to hold companies accountable for sloppy security, class actions — even when successful — rarely result in much of a financial benefit for affected consumers (very often the “reward” is a gift card or two-digit dollar amount per victim), while greatly enriching law firms that file the suits.
It’s my view that these class action lawsuits serve principally to take the pressure off of lawmakers and regulators to do something that might actually prevent more sloppy security practices in the future for the victim culpable companies. And as I noted in yesterday’s story, the credit bureaus have shown themselves time and again to be terribly unreliable stewards of sensitive consumer data: This time, the intruders were able to get in because Equifax apparently fell behind in patching its Internet-facing Web applications.
In May, KrebsOnSecurity reported that fraudsters exploited lax security at Equifax’s TALX payroll division, which provides online payroll, HR and tax services. In 2015, a breach at Experian jeopardized the personal data on at least 15 million consumers.
CAPITALIZING ON FEAR
Speaking of Experian, the company is now taking advantage of public fear over the breach — via hashtag #equifaxbreach, for example — to sign people up for their cleverly-named “CreditLock” subscription service (again, hat tip to @rayjwatson).
“When you have Experian Identity Theft Protection, you can instantly lock or unlock your Experian Credit File with the simple click of a button,” the ad enthuses. “Experian gives you instant access to your credit report.”
First off, all consumers have the legal right to instant access to their credit report via the Web site, annualcreditreport.com. This site, mandated by Congress, gives consumers the right to one free credit report from each of the three major bureaus (Equifax, Trans Union and Experian) every year.
Second, all consumers have a right to request that the bureaus “freeze” their credit files, which bars potential creditors or anyone else from viewing your credit history or credit file unless you thaw the freeze (temporarily or permanently).
I have made no secret of my disdain for the practice of companies offering credit monitoring in the wake of a data breach — especially in cases where the breach only involves credit card accounts, since credit monitoring services typically only look for new account fraud and do little or nothing to prevent fraud on existing consumer credit accounts.
Credit monitoring services rarely prevent identity thieves from stealing your identity. The most you can hope for from these services is that they will alert you as soon as someone does steal your identity. Also, the services can be useful in helping victims recover from ID theft.
My advice: Sign up for credit monitoring if you can (and you’re not holding out for a puny class action windfall) and then freeze your credit files at the major credit bureaus (it is generally not possible to sign up for credit monitoring services after a freeze is in place). Again, advice for how to file a freeze is available here.
Whether you are considering a freeze, credit monitoring, or a fraud alert (another, far less restrictive third option), please take a moment to read this story in its entirety. It includes a great deal of information that cannot be shared in a short column here.




Some crook applied for SS benefits using my name and SSN in May. SS caught it as the benefits were to go to a temporary debit card. They called me asking about the claim and this is how I learned of the breach. I couldn’t figure out how anyone got my SS etc but now I know. I feel helpless to do anything I still need go to the agencies for a freeze but little good that will do as my SSN is out there.
Try filling a complaint with the Consumer Financial Protection Agency. You can do it on line and it is pretty easy, although you will need to gather all information before filling it out. They way I see it, we will never know how well the CFPB will perform, if they have no complaint data to work with. They will sometimes call you on the phone after filing so be ready to answer the phone ( no it isn’t telemarketers)
credit reporting agencies have become a strong negative upon We the People — affecting job applications, and insurance rates as well as interest rates and loan approvals.
and now clearly they are also putting vast amounts of sensitive data at risk, online.
it is time to ABOLISH these onerous entities. Call Hillary: let’s clean up their servers.
I knew something was going on at Equifax when a credit monitoring service was unable to register my details at Equifax. I was told that I must have a mixed file and that I needed to contact Equifax.
During the phone call at Equifax, I verified several pieces of information and the correct name on the report, that there was no mixed file. Oh, and during the phone call I was being pressed to purchase their credit monitoring service, asked several times, and solicited for a follow-up call.
Sure enough, EquifaxSecurity2017 reports that information was obtained by an outside party. Equifax knew, but wanted to sell me their monitoring service before they would tell me why my Equifax report is blocked to outsiders.
One thing I haven’t seen explained is why Equifax needs the last SIX digits of your SSN for their “you’ve got hack” check? Plenty of people are asking but few are answering.
For every other credit-related thing I’ve done lately, including putting a temporary fraud alert on my credit report, only the last FOUR digits have been needed.
And then there’s this, sort of telling us that it’s all just a way to lure people into helping them mitigate the suit: https://twitter.com/webster/status/906638411930497029
Well if they think time stamps and no action are going to save them, I’d say they are mistaken. God I hope so anyway!
Hi, Brian.. *waving!* Thank you for the work you do! I just had something hit my inbox from Apache. I saw a link passed moderation scrutiny above so I’m including a pertinent one here:
The Apache Software Foundation Blog: Apache Struts Statement on Equifax Security Breach; 2017.09.09
https://blogs.apache.org/foundation/entry/apache-struts-statement-on-equifax
Being the type of software they are, I’m going to jump out on a thin limb and publish an important chunk rather than paraphrase. Since it’s in support of them, I hope they’ll forgive because this is important information that needs aired:
“We are sorry to hear news that Equifax suffered from a security breach and information disclosure incident that was potentially carried out by exploiting a vulnerability in the Apache Struts Web Framework. At this point in time it is not clear which Struts vulnerability would have been utilized, if any. In an online article published on Quartz.com [1], the assumption was made that the breach could be related to CVE-2017-9805, which was publicly announced on 2017-09-04 [2] along with new Struts Framework software releases to patch this and other vulnerabilities [3][4]. However, the security breach was already detected in July [5], which means that the attackers either used an earlier announced vulnerability on an unpatched Equifax server or exploited a vulnerability not known at this point in time –a so-called Zero-Day-Exploit. If the breach was caused by exploiting CVE-2017-9805, it would have been a Zero-Day-Exploit by that time. The article also states that the CVE-2017-9805 vulnerability exists for nine years now.”
Further down they say:
“If the latter was the case, the team would have had a hard time to provide a good answer why they did not fix this earlier. But this was actually not the case here –we were notified just recently on how a certain piece of code can be misused, and we fixed this ASAP.”
Likewise *waving* at Apache. Am a long time fan.
At the end of each and every day, self-protection and self-preservation related to software choices lies in the hands of the end user. Do your due diligence and make subscriptions to related security announcement listservs Job #1……
Are they supposed to send us a notification of if we were breached? Is there a requirement for them to do this?
Equifax security has been terrible for years! Back in 2011 an email address that I used *exclusively* to register at their site for the annual free credit report started receiving a bunch of spam. I contacted their customer service since this was alarming to me because of who they are, and all they had to say in their reply was that I should contact my email provider to check my spam settings. I still have their reply message. I would not be surprised in the least if they were breached way back then, 6+ years ago.
> Back in 2011 an email address that I used *exclusively* to register at their site
Unless the email address was extremely unique such as yourname-equifax@example.com , I would not count this as a breach. Spammers routinely query all usernames at every ISP to see if they can guess un-publicized email addresses: to illustrate – if they have firstname.lastname_1993@example.com from some other database, they will try sending email to firstname.lastname_1993@gmail.com, firstname.lastname_1993@hotmail.com , etc.
Plus fraudsters are creating thousands of new domain names every day, and it would be so easy to link to the wrong site to fill out forms! That would be like giving the crooks everything they need without even having to breach any legitimate agency!! I shudder the thought!
I’m no lawyer, but I am under the impression Sarbanes-Oxley Section 404 holds corporate officers criminally liable for the scope and adequacy of the internal control structure and procedures for financial reporting.
That suggests the Equifax officers who dumped Equifax stock may be criminally liable for not knowing of the breach.
Only Officers related to the financial reporting, usually the CFO and CEO. They usually pass the buck down to the controller and accounting departments as well. But not to Marketing or HR or Sales. I have heard of IT but never been somewhere that had them certify.
So no, I don’t this will apply.
Although, I think that this coincidence will be hard to defend. Some email somewhere is going to prove they knew about it or someone remembers hearing a conversation they were involved where they knew.
Don’t you worry, the SEC will slap their wrist if it actually finds anything anyway.
That only pertains to the security controls for FINANCIAL REPORTING.
The security breach of their services to customers is unrelated to an organization’s financial reporting and financial reporting controls. Although as a result of the security breach occurring their financial reports will likely be affected in the future due to the new losses that occur as a result of consumers avoiding them and potential future lawsuits.
So if the site equifaxsecurity2017.com can’t be relied upon to give an accurate answer of whether you were affected or not, is there another way to find out?
At this point safely assume you are one of those affected and if not it’s bound to happen to you again with the way things are going. As they say it’s “better to be safe than sorry”.
I believe this breach happened during the summer so you should be able to go to http://www.annualcreditreport.com and pull one of the three credit bureau reports for free (I usually pay and order all three) and see if there is credit on the report that you didn’t obtain and if there is no fraud on your credit report you can freeze your credit. My question is, do I have to go to all three sites and freeze my credit?
in attempting to put out my personal dumpster fire via the sites for Transunion, Experian and Equifax–only Transunion and Equifax actually let me complete my fraud alert and credit freeze attempts. Experian only succeeded in duping me into getting multiple credit card charges of 10 bucks a pop by trying to get my freeze setup. each time their site stated they ran into internal errors and i am left with the option to mail them $10 with multiple documents proving my identity and residence. so, not only are they charging people’s cards up front for their state’s freezing charge, they also expect us to mail them whatever resident state charges are for credit freeze placement way to add to the screwing us from behind level, Experian!! you GO, girl.
Please don’t forget to freeze Innovis! (See Brian’s article)
This is BS.
In their annual report (10K), they state that they know they are a regular target of cyber attacks. And they identify security breaches as a risk factor for the company.
In other words, they acknowledge in their FINANCIAL statement that cyber attacks are a FINANCIAL risk. Yet, we are to believe that their Chief FINANCIAL officer was not informed about a breach that has FINANCIAL consequences for at least three days?
Some explanations that come to mind:
– Their incident response plan did not include notification of the CFO
– They didn’t follow their incident response plan
– They have no incident response plan
– They are lying
Their annual report clearly states that their board of directors has oversight of cybersecurity activities. So on paper, they appear to be doing what they should. But in practice, something else..
Didn’t this breach occur during the summer? If so the CFO and the Board were well aware of this breach before the CFO sold his/her stock. I think they’re lying.
Business criminals lie? SAY IT AIN’T SO…!
If you are going to commit a crime, do it wearing a suit with a C-level title
I obtained my credit report for Equifax. I also placed a security freeze on my credit report. Equifax did not charge me for this. Maybe they are feeling guilty.
Are you going to put a freeze on your credit information at Transunion and Experian too? Whatever information Equifax has, the other two have also.
I was just told by a friend that she was denied a credit freeze from Experian, citing insufficient cause for her to demand one. They told her she would need to show legal paperwork such as an instance of fraud before they would enact a security freeze for her. Isnt this illegal? It’s her account and data. She disclosed to me that Equifax and Trans Union did not give her a hard time. Trans Union charged her $10, Equifax was free. Anyone else have this experience with Experian?
If you want a freeze for no charge, you have to have a police report. Otherwise you have to pay the fee amount your state allows.
In some states if you are 65 or older, there is no fee for a credit freeze: See here for a ‘how to’:
http://consumersunion.org/pdf/security/securityNM.pdf
She is willing to pay whatever fee to enact a freeze. They are not denying her because she is unwilling to pay. They won’t give her a freeze because they told her they see no fraud and want proof of fraud before they give her a freeze. They won’t even SELL her a freeze!
I had my identity stolen years ago, and I have had my credit frozen since then. I have dealt with the big 3 for years, and they are all equally horrible. The only thing that surprised me about this breach is that it didn’t happen years ago. There needs to be much more stronger federal oversight of these reporting “bureaus.” They have a great deal of power over people’s financial lives. I’m not one for big government, but I think a case could be made that, at the very least, these credit reporting companies should have embedded federal auditors. If you think I am off-base, feel free to challenge me. I’m open to other opinions.
On the one hand I agree, but on the other I’m not sure. Beyond not being for big government, I don’t trust government! It’s the old who watches the watchers?
To play devil’s advocate on the Mandiant angle, “Brandan” also registered another domain at the same time, equivalenthax.com. Could be a false positive. Not the point of this, I know.
Maine residents can have their credit frozen and unfrozen for free. http://www.maine.gov/pfr/consumercredit/file_freeze_info.htm
I wasn’t aware of that, thanks! – fellow Mainer
Top corporate officers typically have to schedule large stock or options transactions far in advance. And they typically do so at regular intervals to avoid making changes in behavior that could affect the stock price. I can’t say if that is the case here, don’t have all the details.
I told my wife the same thing (Rule 10b5-1). However, I read an article right after that stating these sales were NOT part of those scheduled sales. I’m sure we will hear more shortly though.
According to Bloomberg “None of the filings lists the transactions as being part of 10b5-1 scheduled trading plans.” so I stand corrected
Now’s a good time to say thanks for the multiple articles over the years on security freezes. I’m hoping all those I sent the articles to did the same.
I would think that any company that gave your financial information to Equifax is also liable because they failed to properly vet a third party with your data.
I just attempted to place security freezes with the major credit bureaus. Only TransUnion required me to set up an account, and — unbelievably — would not accept a new password that contained any “special” characters; only alphanumeric characters were permitted (I kept getting error messages until I removed the special characters from my proposed password).
Having gone through the account setup, I requested a freeze and was greeted with an error message referring to “technical difficulties” that prevented the freeze request from being processed.
Many more than the top three agencies are collecting information on you.
https://www.consumerfinance.gov/about-us/blog/so-how-many-consumer-reporting-companies-are-there/
Transunion’s website for placing fraud alerts or credit freezes is not working now – wonder if they’re being overwhelmed or if there’s concern they may be using web software that’s vulnarable….
Out of curiosity, what happens if the corporate officers are found guilty of insider trading? Does the government seize the unlawfully obtained cash? Or do they just send the officers to a prison resort?
Brian,
Here’s a question that I have not even seen asked: for those of us who have a freeze on (I got one after the OPM breach)…have the PINs been stolen?
I was wondering the same thing as I also set up my freezes years ago. I did check, however, and the only way to change your PIN is to submit the request to them in writing with copies of your ID’s.. passport, license, etc…. Not sure how that actually verifies anything. I don’t remember giving them that info when I set up the freeze…
Brian, you forgot to mention that they continue their abysmal “security” practices. The pin for credit freeze … drumroll … MMDDYYHHMM timestamp. No joke.
https://twitter.com/webster/status/906638411930497029
It’s time to immediately change the definition of identity theft. It’s no longer sufficient or meaningful to define identity theft as the answer to: “What did the thief use your information for?”
Personal information (and data that is associated with my identity) that is exposed in a data breach should be legally defined as identity theft — whether or not someone actually uses your stolen personal information to open accounts, file taxes, take out a new loan, etc.
Credit freezes are controlled by a pin given to the requester. Bureaus have procedures to allow users to request replacements for lost pins. How secure is this replacement process? Wouldn’t a skilled identity thief already have access to the required information to obtain the replacement pin?
The dumpster fire grows. They have now announced they have a customer “response” team to answer questions about the issues you’ve raised here. So I called them. What did they say? “You need to look at the answers on the frequently asked questions page.” Huh? There are no answers to these questions, and the folks on the “response line” cannot answer the questions.
The proposed “solution” is more more monitoring, which is the original product I had with them (that is at risk in this mess). Of course, there’s no answer to that on FAQs, either.
The “response” person I spoke with also said she had no supervisor — so I suppose there is still no answer from Equifax about anything, and no attempt other than to stall for time while sending customers in circles.