I cannot recall a previous data breach in which the breached company’s public outreach and response has been so haphazard and ill-conceived as the one coming right now from big-three credit bureau Equifax, which rather clumsily announced Thursday that an intrusion jeopardized Social security numbers and other information on 143 million Americans.
WEB SITE WOES
As noted in yesterday’s breaking story on this breach, the Web site that Equifax advertised as the place where concerned Americans could go to find out whether they were impacted by this breach — equifaxsecurity2017.com —
is completely broken at best, and little more than a stalling tactic or sham at worst.
In the early hours after the breach announcement, the site was being flagged by various browsers as a phishing threat. In some cases, people visiting the site were told they were not affected, only to find they received a different answer when they checked the site with the same information on their mobile phones.
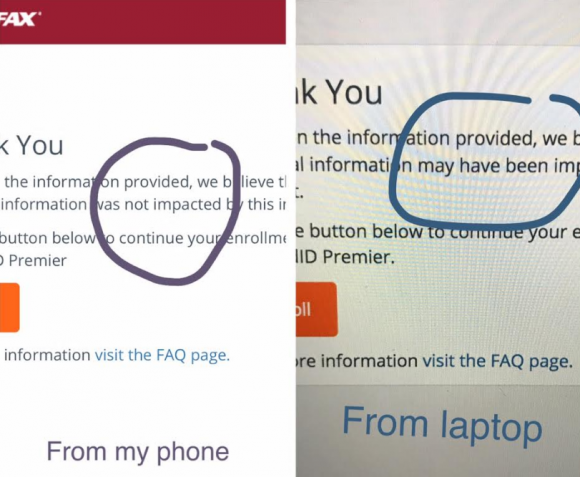
Others (myself included) received not a yes or no answer to the question of whether we were impacted, but instead a message that credit monitoring services we were eligible for were not available and to check back later in the month. The site asked users to enter their last name and last six digits of their SSN, but at the prompting of a reader’s comment I confirmed that just entering gibberish names and numbers produced the same result as the one I saw when I entered my real information: Come back on Sept. 13.
Who’s responsible for this debacle? Well, Equifax of course. But most large companies that can afford to do so hire outside public relations or disaster response firms to walk them through the safest ways to notify affected consumers. In this case, Equifax appears to have hired global PR firm Edelman PR.
What gives me this idea? Until just a couple of hours ago, the copy of WordPress installed at equifaxsecurity2017.com included a publicly accessible user database entry showing a user named “Edelman” was the first (and only?) user registered on the site.
Code that was publicly available on equifaxsecurity2017.com until very recently showed account information for an outside PR firm.
I reached out to Edelman for more information and will update this story when I hear from them.
EARLY WARNING?
In its breach disclosure Thursday, Equifax said it hired an outside computer security forensic firm to investigate as soon as it discovered unauthorized access to its Web site. ZDNet published a story Thursday saying that the outside firm was Alexandria, Va.-based Mandiant — a security firm bought by FireEye in 2014.
Interestingly, anyone who happened to have been monitoring look-alike domains for Equifax.com prior to yesterday’s breach announcement may have had an early clue about the upcoming announcement. One interesting domain that was registered on Sept. 5, 2017 is “equihax.com,” which according to domain registration records was purchased by an Alexandria, Va. resident named Brandan Schondorfer.
A quick Google search shows that Schondorfer works for Mandiant. Ray Watson, a cybersecurity researcher who messaged me this morning on Twitter about this curiosity, said it is likely that Mandiant has been registering domains that might be attractive to phishers hoping to take advantage of public attention to the breach and spoof Equifax’s domain.
Watson said it’s equally likely the equihax.com domain was registered to keep it out of the hands of people who may be looking for domain names they can use to lampoon Equifax for its breach. Schondorfer has not yet returned calls seeking comment.
EQUIFAX EXECS PULL GOLDEN PARACHUTES?
Bloomberg moved a story yesterday indicating that three top executives at Equifax sold millions of dollars worth of stock during the time between when the company says it discovered the breach and when it notified the public and investors.
Shares of Equifax’s stock on the New York Stock Exchange [NSYE:EFX] were down more than 13 percent at time of publication versus yesterday’s price.
The executives reportedly told Bloomberg they didn’t know about the breach when they sold their shares. A law firm in New York has already announced it is investigating potential insider trading claims against Equifax.
CLASS ACTION WAIVER?
Yesterday’s story here pointed out the gross conflict of interest in Equifax’s consumer remedy for this breach: Offering a year’s worth of free credit monitoring services to all Americans via its own in-house credit monitoring service.
This is particularly rich because a) why should anyone trust Equifax to do anything right security-wise after this debacle and b) these credit monitoring services typically hard-sell consumers to sign up for paid credit protection plans when the free coverage expires.
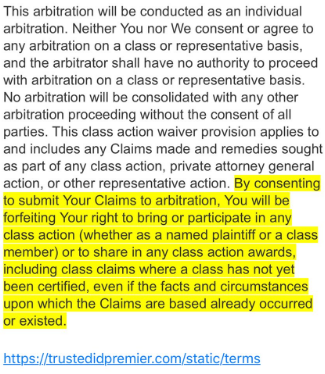
Verbiage from the terms of service from Equifax’s credit monitoring service TrustID Premier.
I have repeatedly urged readers to consider putting a security freeze on their accounts in lieu of or in addition to accepting these free credit monitoring offers, noting that credit monitoring services don’t protect you against identity theft (the most you can hope for is they alert you when ID thieves do steal your identity), while security freezes can prevent thieves from taking out new lines of credit in your name.
Several readers have written in to point out some legalese in the terms of service the Equifax requires all users to acknowledge before signing up for the service seems to include legal verbiage suggesting that those who do sign up for the free service will waive their rights to participate in future class action lawsuits against the company.
KrebsOnSecurity is still awaiting word from an actual lawyer who’s looking at this contract, but let me offer my own two cents on this.
Update, 9:45 p.m. ET: Equifax has updated their breach alert page to include the following response in regard to the unclear legalese:
“In response to consumer inquiries, we have made it clear that the arbitration clause and class action waiver included in the Equifax and TrustedID Premier terms of use does not apply to this cybersecurity incident.”
Original story:
Equifax will almost certainly see itself the target of multiple class action lawsuits as a result of this breach, but there is no guarantee those lawsuits will go the distance and result in a monetary windfall for affected consumers.
Even when these cases do result in a win for the plaintiff class, it can take years. After KrebsOnSecurity broke the story in 2013 that Experian had given access to 200 million consumer records to Vietnamese man running an identity theft service, two different law firms filed class action suits against Experian.
That case was ultimately tossed out of federal court and remanded to state court, where it is ongoing. That case was filed in 2015.
To close out the subject of civil lawsuits as a way to hold companies accountable for sloppy security, class actions — even when successful — rarely result in much of a financial benefit for affected consumers (very often the “reward” is a gift card or two-digit dollar amount per victim), while greatly enriching law firms that file the suits.
It’s my view that these class action lawsuits serve principally to take the pressure off of lawmakers and regulators to do something that might actually prevent more sloppy security practices in the future for the victim culpable companies. And as I noted in yesterday’s story, the credit bureaus have shown themselves time and again to be terribly unreliable stewards of sensitive consumer data: This time, the intruders were able to get in because Equifax apparently fell behind in patching its Internet-facing Web applications.
In May, KrebsOnSecurity reported that fraudsters exploited lax security at Equifax’s TALX payroll division, which provides online payroll, HR and tax services. In 2015, a breach at Experian jeopardized the personal data on at least 15 million consumers.
CAPITALIZING ON FEAR
Speaking of Experian, the company is now taking advantage of public fear over the breach — via hashtag #equifaxbreach, for example — to sign people up for their cleverly-named “CreditLock” subscription service (again, hat tip to @rayjwatson).
“When you have Experian Identity Theft Protection, you can instantly lock or unlock your Experian Credit File with the simple click of a button,” the ad enthuses. “Experian gives you instant access to your credit report.”
First off, all consumers have the legal right to instant access to their credit report via the Web site, annualcreditreport.com. This site, mandated by Congress, gives consumers the right to one free credit report from each of the three major bureaus (Equifax, Trans Union and Experian) every year.
Second, all consumers have a right to request that the bureaus “freeze” their credit files, which bars potential creditors or anyone else from viewing your credit history or credit file unless you thaw the freeze (temporarily or permanently).
I have made no secret of my disdain for the practice of companies offering credit monitoring in the wake of a data breach — especially in cases where the breach only involves credit card accounts, since credit monitoring services typically only look for new account fraud and do little or nothing to prevent fraud on existing consumer credit accounts.
Credit monitoring services rarely prevent identity thieves from stealing your identity. The most you can hope for from these services is that they will alert you as soon as someone does steal your identity. Also, the services can be useful in helping victims recover from ID theft.
My advice: Sign up for credit monitoring if you can (and you’re not holding out for a puny class action windfall) and then freeze your credit files at the major credit bureaus (it is generally not possible to sign up for credit monitoring services after a freeze is in place). Again, advice for how to file a freeze is available here.
Whether you are considering a freeze, credit monitoring, or a fraud alert (another, far less restrictive third option), please take a moment to read this story in its entirety. It includes a great deal of information that cannot be shared in a short column here.




If you want a free credit security freeze after a case of identity theft you usually have to send in a copy of your drivers license along with the police report, why do I have a bad feeling those are the 200,000 or so drivers license numbers they are talking about not just disputes?
So, my immediate response to the breach was to setup fraud alerts on the four bureaus. Then I began looking at a more permanent solution – like a credit freeze and/or credit monitoring.
Experian offers credit monitoring for a fee with reasonable features. One feature really stands out: you can do arbitrary freezes.
Trans Union offers a similar monitoring service, including arbitrary freezes. The best feature is: it’s free.
I looked for reviews on these services. Experian looked “OK”. BUT Trans Union: OMG! Reviewing the feedback on Trans Union on consumeraffairs.com made me want to take a long shower afterwards. Look for yourself:
https://www.consumeraffairs.com/privacy/transunion.html
Based on the feedback on Trans Union, I saw at least a few core problems. 1) They outsource their call centers and it’s clear those centers are consumer nightmares. 2) The centers seem (to me) to be a security risk themselves 3) too many consumers end up being signed-up & billed for their for-fee credit service without their consent.
Ug.
For me, Experian looks interesting because I can also freeze/unfreeze my credit report at will via their credit monitoring service. For that, the cost doesn’t seem that bad. If this turns out to be even mostly true (I need to review the service further) then it would mitigate the downside of doing a bureau-wide freeze as it would make unfreezing my report at Experian easier. Some potential creditors will work with you and use the bureau you request them to use. So, in that scenario, I’d just have to unfreeze Experian & leave the others frozen.
I give up. I ain’t gonna sign up for nothing not even a freeze. I’m tired of this crap. I tried the Equifax site to check myself and they said I may have been impacted. Screw it. Let it be. What happens happens. I’m tired of living the paranoid life. All of this is out of my control and I’m sure the freezes ain’t gonna help anything its just a hope in a fart. Maybe my info will get lost in all that 146 million people data and I am dead before they try to use it. I hate that my info was collected involuntarily by Equifax and I hope they rot in hell. But the bottom line is ultimately I have zero control over any of this crap. To think we do is an illusion.
Even if you freeze your credit, your unfreeze secret code is at the credit agency and may be hacked along with everything else.
Exactly! I’m not even gonna waste my time anymore with these people. Freezes don’t stop breaches…
I changed my mind and placed security freezes on all of them…lol. Equifax was free and the other 2 were only 3.00 each. I put a freeze on innovis long ago and never took it off.
Worse….
A Freeze IS a freeze. Wife and I are now Identity Guard members. Not perfect – but better than nothing.
I verified something with Identity Guard today – under a FREEZE, they can’t monitor the big three. Under a rolling 90 day Fraud Alert? They CAN. We’re going the FRAUD ALERT route…. Calendar app and a little work.
Dean – I addressed this in the story. You can get monitoring before you freeze. IF you have frozen, you need to temporarily thaw the file (24h should do) to sign up for the credit monitoring.
And what, you’re supposed to freeze your credit forever, which is as long as your SSN etc will be on the black net?
Yep. Why wouldn’t you? If you want to take out a loan, unfreeze temporarily.
yep, you’re totally correct, we’re fucked, the idea that anything is free is an oxymoron, google has your number, dude.
My recommendation is: DO NOT SELF-DEFRAUD AT THIS SHAM SITE. It mirrors the social engineering identity scams… Once you are frightened, you go to the luring site and enter your data voluntarily.
After seeing it accept my phoney info as if real, having a Google Captcha on it, and no legitimate Equifax SSL identity, why in the hell would anyone trust this site in any way?
Security 101: Don’t trust a site that sounds like all those fraud antivirus programs that were infecting systems circa: 2005-2015. And don’t trust entering your private data, to give to what now appears to be a P.R. firm!!!
Exactly what I said when I saw this site. What a joke.
Give us your SSN on a hastily-stood-up website so we can tell you that you ‘might’ have been impacted by our negligence. Wow… just… wow.
Interesting that Mandiant was brought in to investigate this. According to FireEye marketing material, Equifax was a customer.
“Zero-day and targeted attacks that evade simpler defenses are where you’re going to need a next-generation product like FireEye. We looked at other vendors, but FireEye stood apart in its ability to detect these advanced threats and keep us secure.” —Tony Spinelli, SVP and CSO, Equifax
snack oil and meaningless key words is 95% of what comes out of “the valley”
Thank you for the details, very interesting. What does this state about Fireye?
It doesn’t necessarily say anything about the security vendor. I’ve seen many organization purchase all sorts of tools, and poorly implement them (or not at all). Or they implement, then fail to staff accordingly or keep up.
Let’s not forget that the breach vector was software they hadn’t kept up to date with from at least a security perspective.
-ASB
I’m going full anon for this one, but a few years ago, my org was popped by APT. Our new CIO brought them in because he had prior experience with them. They had very good tools and a ridiculously nice threat intel to reach back to, but the TTP of the attackers were all very cutting edge and their threat intel returned nada. Their analysts were slower than ours, and, in the end, they never produced anything of much worth.
Maybe these stupid agencies think doing after disaster action is the way to go? All they had to do was PATCH their Apache servers!! How lazy can you get?!! There would have been no need to call in the cavalry too late if they had just been doing their baseline jobs.
they should never have been allowed to have that data to begin with. the hack was inevitable.
Adding insult to injury, the PIN generation for the Equifax credit freeze is terribly insecure. They auto-generate a 10-digit PIN, which seems superficially secure. Except…the first 6 digits are the date e.g. 090917 and the next 4 are simply generated in sequence. When I set up a freezes for myself and my wife, our PINs were just a few numbers apart. So effectively this becomes a 4 digit PIN.
Any guesses as to how resilient the online unfreeze system is against brute force attacks for just 10,000 numbers? The attackers already have everything else they need…
A dumpster fire indeed.
You can set your own PIN for the security freeze, don’t use the pre-generated ones.
Just FYI – the pins were just a few numbers apart because the last four are the time.
I have had all 4 files (Equifax, Experian, Transunion & Innovis) frozen for more than a decade and so far it appears to be a solid defense against hackers/ID theft. And I get to hold the Credit Reporting Agency liable when they blow it, again, as I expect they will.
A word of advice: When signing up for a Credit Freeze DO NOT use their website to do so because they require you to agree to arbitration in their online form.
However the paper version I filled out and mailed (using trackable mail of course because these companies hate Freezes and will “lose” mail when they can) does not have the arbitration requirement in it; even if they changed their practice of now adding arbitration (I don’t believe so) to the paper form, delete that text and send it in anyway.
I have deep experience as a Consumer going around with all 4 credit companies and trust me, the greed, arrogance and depth of their corruption is absolutely breathtaking.
Hans, you get a hug from me for your use of the word “breathtaking” 🙂 Gotta have some fun, right?
So the questions I have after this is are: why were the databases not encrypted? Perhaps additionally, why was the communication to/from the databases not also encrypted? Please inform me if I am over simplifying here.
Right? The lack of encryption is equally as stunning as the breach itself.
Encryption isn’t magic pixie dust.
Let’s start with the basics:
Let’s say someone wants to set a password for use at a website.
The webserver tells their browser to encrypt the connection using keys negotiated by the server and browser. The browser sends the initial password.
Once the webserver receives the password, what should it do with it once it decrypts it?
It could encrypt it, but doing so requires storing a key somewhere, and with that key, anyone can decrypt the password.
Any server that claims to store passwords ended for authentication is doing it wrong. Instead of encryption, passwords for authentication should be hashed. Hashes are designed to be one-way (technically many-to-one). This means that one can’t actually find out what the original was, although with enough computing power and time, one could find many possible keys which happen to hash to that value.
The next time you log in, the server hashes the provided password the same way and compares, a match means it’s probably the same password, and the user can be let in.
Ok, so hashes are more secure than encrypting, because they destroy the original data. Note: using a week hashing algorithm or failing to salt (include a random token with each key to protect against rainbow tables) makes for weak security, nothing is magic pixie dust.
OK, so, why doesn’t everyone just hash all data? Answer: because people sometimes need the data. Great, so encrypt it instead. But they need the data! Ok, so store the key next to the data. Well, gee, then the let and data will be stolen together and what had that gotten you?
Sure you can “encrypt” data, but encryption is fine for at-rest storage or in-transit data, it’s pretty useless for in-use data. And these brokers are data brokers, they make money looking up and selling data. And, as usual, you aren’t the customer, you’re the product, this your data needs to be accessible by lots of other customers. Say they pick your SSN as the encryption/decryption key. Don’t worry! *EVERYONE* has that. This such encryption is useless.
Anyone else notice that Experians security freeze page no longer exists? Even clicking on the link in their site takes you to a page that says it doesn’t exist.
Yeah, that’s what I’m going to do, use an internet link to a company that’s been compromised to this extent:
“Bear in mind this is the THIRD TIME in 16 months that Equifax has been hacked– there was another breach earlier this year, and another in May 2016.
“Even worse– this wasn’t an overnight attack. Hackers spent MONTHS probing the Equifax network, burrowing deeper into the system and gaining access to more and more data with each attempt.
“Yet Equifax’s defenses failed to detect anything.
“Finally on July 29, a whopping TEN WEEKS after the attacks started, Equifax realized that something was wrong.
There is only ONE solution corporations understand – SUE THEM OUT OF EXISTENCE. Send a message to all of the other irresponsible concentrators of our personal data.
Equifax PIN numbers for credit freeze are not random – they are just the time stamp of when the credit was frozen. This is yet another example of how utterly incompetent Equifax is.
If you submit a freeze today, your PIN will be 090917xxxx, which means it will take only 10,000 attempts to guess the PIN.
See this reddit post for details: https://www.reddit.com/r/personalfinance/comments/6yv4gb/official_mega_thread_recent_equifax_security/dmqvoqf/#dmqvoqf
You can set your own PIN.
Can you provide information on how you can change your PIN when doing a credit freeze, please?
As far as I’m seeing, there’s no options to actually do this on the websites-maybe I’m missing it.
This whole business of charging for a security freeze, temporarily lifting it, or permanently lifting it is bogus. There is no way to tell when your ID may be compromised. It could be years. I just checked and 4 of my children are impacted as are my wife and me. Having been a victim of ID theft 10 years back, it is extremely painful. By the way, Equifax site now says the following:
1). YOU CAN DETERMINE YOUR STATUS IMMEDIATELY
Some consumers who visited the website soon after its launch failed to receive confirmation clarifying whether or not they were potentially impacted. That issue is now resolved, and we encourage those consumers to revisit the site to receive a response that clarifies their status.
2). NO WAIVER OF RIGHTS FOR THIS CYBER SECURITY INCIDENT
In response to consumer inquiries, we have made it clear that the arbitration clause and class action waiver included in the Equifax and TrustedID Premier terms of use does not apply to this cybersecurity incident.
If you already had an Equifax freeze in place at the time of the breach, are the unfreeze PINs also compromised? Is there some way to change the PIN now using my existing PIN or do I have to go through the replacement PIN process as if I have lost it?
As I write this, I have been on hold at Equifax, awaiting a real live person to talk with, for more than an hour. Like you, I have a freeze.
I tried to change my password and PIN online this morning, but could find no way to do it. Doing a search for “change password,” I got a “page not found” message. Wonderful.
When I called, I had to go through a hugely confusing phone tree. It took me two tries to find a route to an agent. I’m sure the agents are buried. All I’ve heard so far is an elevator music concert.
If you get information on your question, please post it. Maybe Brian can get through and ask if the passwords and PINs have been compromised.
If any industry ever needed to be regulated, it is this one. WHAT A BUNCH OF HACKS!
Finally got through. Talked to an agent named Blake. Very nice, but sounded tired and overwhelmed.
Blake said the freeze PINs and passwords have not been compromised. That’s the information he has gotten from the morons who run Equifax, I’m sure. So, we’re probably OK, but who really knows?
Blake said you can change your PIN and password. He said to call 888-298-0045.
Best of luck to all.
Ed,
May I ask what password you are talking about? I had my credit frozen two years ago with Equifax and was only given a pin.
I misspoke. There is no password for the freeze, so far as I know, just a PIN. I also have a password for Equifax. I’m not sure why. Using it just exposes me to endless advertising.
One of the few benefits of being broke with bad credit, none of this worries me!
Just in case anyone’s looking for a job….
https://equifax.gr8people.com/index.gp?opportunityID=7194&method=cappportal.showJob&sysLayoutID=122
WHERE ARE THE D*MNED HANDCUFFS?
It’s time to start locking people up and destroying businesses with federal criminal indictments
2017-09-08 09:12 by Karl Denninger
https://market-ticker.org/akcs-www?post=232369
Excerpt:
[Congress has] not enforced the law with regard to intentional and willful misconduct when it comes to cyber security in these large data stores nor do they give a damn about the material and incalculable harm these large firms inflict on consumers when your data is either stolen or misused because of their intentionally lax security. Further, the Congress and Executive allow effective extortion of every consumer in the nation by allowing these companies to charge you to freeze your credit, thus denying scammers access, they can charge you again to “unfreeze” it temporarily if you wish to obtain new credit and they deem said data “theirs” instead of “yours” which means you can’t insist that they either not collect and store it or delete it.
See, proper security costs money and can be inconvenient. Having access to such data only when properly-secure machine certificates are used to encrypt same and all communication all the way back to a traceably-secure device would mean that “instant credit” decisions at millions of cash registers (e.g. to sell you a credit card while in the checkout line) could not be made.
Forcing these companies to allow consumers to turn “on” and “off” access to their credit files whenever they want, without cost, would mean that these companies couldn’t sell your data to anyone and everyone who has a few bucks, and they’d have much smaller businesses than they have now. And prosecuting and jailing the executives of firms who put convenience for their customers, which are businesses — not consumers — ahead of security would mean they’d have no business at all. But at the same time it would make defending against someone opening a credit account in your name and stealing your identity very easy since you could disable access to your credit information any time you wish without having to pay to turn it on and off.
The solution is to force Equifax to eat the cost of ANY fraud that ensues and all costs of its cleanup including liquidated damages for your time and effort on a permanent basis since they, and not you, decided to use an identifier never intended for that purpose and in addition they, and not you, were grossly negligent in failing to secure said data. In addition forcing all of these firms to allow no-cost lock and unlock options for consumers where locking your file at one bureau does so at all of them and can be done at zero cost at any time for any reason on a permanent basis would actually mitigate said risk. Finally, deeming any credit opened while you have locked your file as conclusively fraudulent and uncollectable with liquidated damages payable to you if someone does it anyway would shift the burden from you for said incidents to them.
I’m a regular reader of KrebsOnSecurity but not much of a poster. That said….
To date I’ve managed to keep readily accessible personal details to a minimum on the Internet. No social media accounts pointing to my real persona, multiple email accounts for various functions, unique & complex passwords and two-factor auth for every financial account. Don’t get me wrong, if you want to dig up info on me it’s still relatively easy with some basic info but that’s the point. You would need to dig up that info.
When a retail chain loses some info (CC# and name) it doesn’t concern me. The CC fraud is protected and the retail chain info is what I elected to share.
However, when a credit reporting service loses my info they have essentially thwarted all my efforts to keep a relatively low profile and destroyed any chance (no matter how slight) of control I had over my identity not to mention the potential negative impact to my credit.
There is no way that Equifax can ‘make this right’. The speech by Rick Smith (CEO of Equifax) is non gradus anus rodentum! Actually made me angry enough to post.
If Equifax truly wanted to make things right they would do the following;
– offer to work through the process of getting a new SSN for each impacted individual. In my world they should be forced, by law, to do this. The cost in dollars and manhours would be staggering and would definitely ensure tighter safeguards on our data at all the bureaus.
– immediately enable free (opt-in) credit monitoring on all impacted accounts for the life of that individual. Agreed…monitoring doesn’t stop identity theft but at least there is a baseline of credit history that allows for action to be taken when unauthorized changes occur.
– allow for (opt-in) an immediate credit freeze/unfreeze at all the credit bureaus at Equifax’s expense for the life of the impacted individuals. This includes ensuring a multi-factor authentication process is in place to preserve the integrity of PINs using something other than the data that was stolen.
– setup a liaison group with ties to federal, state, and local governments to ensure open and timely communications with the various tax agencies for the disclosure of compromised SSNs and assisting the various tax agencies with alternative tax payer identification methods.
Of course none of this will happen and we will be left to fend for ourselves. So I will settle for a class action suit that puts Equifax out of business and the arrest, conviction and jail time (real jail/real time) for all Equifax employees that new of the breach and profited by selling stock prior to disclosure.
Nope…not bitter at all.
You hit that nail right on the head – but I choose to be bitter! Your damn right I’m mad as hell and am not going to take it anymore!
Ok, so your supposed to go to a web site that looks like equifax, enter the last 6 digits of your social, and be told that you are affected and sign up for credit monitoring. I smell rotting phish. Once you give them the last 6 digits, it ain’t that hard for software to figure out the rest. Boy, do I feel “suckered”. Time for the DOJ to get involved.
Right? Why did they have to put out a new domain name? Why not put it off of their real site? My company marks all domains that have not been visited before or are newly-registered as potentially malicious. Our proxy blocks them and requires users to take specific actions if they want to continue. So why stand up a site like that?
I just tried to get an Equifax Annual Credit Report and at the end of the process I got the message: “Online delivery unavailable. We are not able to deliver your free Equfax Annual Credit Report online” I can get a copy mailed to me by filling out a form and providing copies of my Social Security Card (!) and drivers license.
I was able to get mine online this evening.
So is the “Online Delivery Unavailable” a temporary message caused by people pounding their servers? I eventually got a credit report from TransUnion…but still can’t get one from Equifax.
I learned the following from Equifax:
“Based on the information provided, we believe that your personal information may have been impacted by this incident.”
The cretins can’t even man-up and say something like: “Sorry, we messed up and didn’t have the cyber security we claimed and we allowed miscreants the ability to have All Your Credit Card Numbers, Your Bank and Savings Account information, Your Drivers License Number, Your Social Security Number, Your Birth date, Your Full Address, Your Telephone Number, and all the other information we had gathered about you.”
I understand there are already several class action lawsuits pending. I have trouble grasping the size of a 150 million person class action anything.
The night before Equifax announced the breach, I was reviewing my twitter account and noticed Experian was offering a free search of my information on the Dark Web. That same evening I took them up on their offer to run a search. Today, Sept 9, I received an e-mail reply from Experian stating I could sign up for their identity protection service “free for 30 days.” After that, a fee to continue the service would be required. The question that comes to mind is whether Experian may have known of the pending Equifax announcement and attempted to grab market share ahead Experian’s announcement which steered people to their own credit monitoring product. Collusion? One hopes not. Time will tell.
I just tried to do a credit freeze at all four companies
No problems with Experian, Equifax and Innovis (except one of them charged me $10)
TransUnion is another matter
Filled out the online credit freeze information and it failed
I was given a telephone number which appears to be nothing more than an ad for their services
No email address to send to
It appears to require inputting personal information for their ads to proceed … so I hung up and filed a complaint with the Consumer Financial Protection Bureau (cfpb)
I guess the only option with TransUnion right now is via snail mail
Next I tried to get the free credit report of Equifax through the annualcreditreport.com site and was informed that I couldn’t get it … so filed another complaint with the cfpb
So is this breach for those who were USING Equifax online? What about those who never had a email or log in?
They already had your information. Remember they’re one of the “big three” credit bureaus, so they trade in your personal information any time you apply for any credit with anyone. Plus, signing up for their “free one year credit monitoring” means you get auto-renewed after that year at normal price (even if you never gave them your credit card because they already have that information) UNLESS you cancel it.
Even when you check to see if you have been hacked, the “warning” says you have to come back on September 15 and no other reminder will be sent.
THEY screwed us over and they’re making on us by offering “monitoring” that is useless but even worse, charging us after a year because WE have to remember to cancel it.
The absolute avarice of Equifax and most of the businesses in this field is just astounding.
Best we can do, just deal.
Experian’s password reset functionality is broken.
Check out the username they are presenting to me as mine
@@$reusedusername##
Awesome….
I have the same username when trying to login to my credit report on Experian. Are equifax and experian connect or is this a separate security breach????
They are claiming my username is : @@$reusedusername##
As often happens with these breaches, Equifax may not have told us the full extent of what they lost. (Did they lose the credit freeze pins as well?) I have an employee who had unauthorized charges on both his personal credit card and his business credit card at almost the same time. There is no crossover between the merchants he visits with his personal and business cards. We couldn’t figure out, short of someone accessing his physical wallet, how someone could get both numbers, and it seemed too unlikely to be a coincidence. Now we have another theory. I recall that we had to give the bank the SSNs for each employee who would receive a business card. This may have been reported to Equifax, who could conceivably store the business card data, even though it doesn’t show on his credit report.
I’ve been seeing leaked credit network data being used for crime for years.
When unique identifiers given to credit agencies start appearing in targeted phishing and spam campaign, it’s pretty obvious that this is just the last in a long line of complete irresponsibility.
Just nutted up and paid TransUnion the $7.50/ea. to do a credit freeze on both my wife and I’s account .. better safe than sorry.
The worst thing about this is the rush to give TONS of bad advice by any number of websites. Read the following and see if this person didn’t just cut/paste his article from any other websites who are just quoting the Equifax “FAQ”:
http://www.popularmechanics.com/technology/security/news/a28131/equifax-hack-protect-yourself
Even worse, the same “check if you’ve been affected” site still shows completely useless information. Oh, and since we have to wait until September 15, how is that NOT giving hackers MORE time to steal and open more credit cards and accounts in our names?
So useless is Equifax’s response to this. There’s just no way to close this barn door but they’ll keep stating that everything is fine while rearranging the deck chairs.
Free online resource about credit freezes, CRA links to order credit freezes, valid link to FTC-approved website to order free annual credits reports and link to FTC to report ID theft fraud and receive customized re overly plan. Authored and published by a data breach victim. No advertising.