I cannot recall a previous data breach in which the breached company’s public outreach and response has been so haphazard and ill-conceived as the one coming right now from big-three credit bureau Equifax, which rather clumsily announced Thursday that an intrusion jeopardized Social security numbers and other information on 143 million Americans.
WEB SITE WOES
As noted in yesterday’s breaking story on this breach, the Web site that Equifax advertised as the place where concerned Americans could go to find out whether they were impacted by this breach — equifaxsecurity2017.com —
is completely broken at best, and little more than a stalling tactic or sham at worst.
In the early hours after the breach announcement, the site was being flagged by various browsers as a phishing threat. In some cases, people visiting the site were told they were not affected, only to find they received a different answer when they checked the site with the same information on their mobile phones.
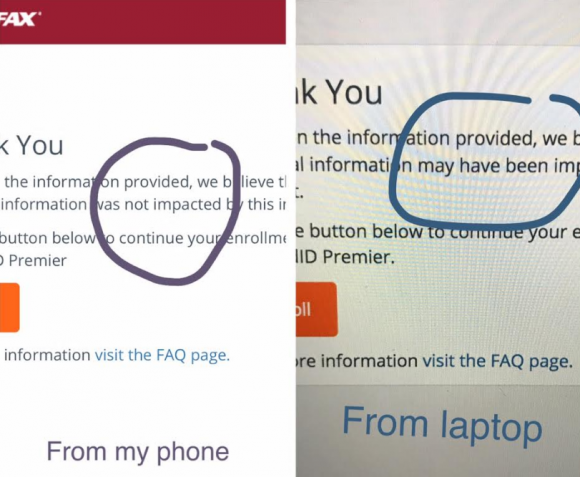
Others (myself included) received not a yes or no answer to the question of whether we were impacted, but instead a message that credit monitoring services we were eligible for were not available and to check back later in the month. The site asked users to enter their last name and last six digits of their SSN, but at the prompting of a reader’s comment I confirmed that just entering gibberish names and numbers produced the same result as the one I saw when I entered my real information: Come back on Sept. 13.
Who’s responsible for this debacle? Well, Equifax of course. But most large companies that can afford to do so hire outside public relations or disaster response firms to walk them through the safest ways to notify affected consumers. In this case, Equifax appears to have hired global PR firm Edelman PR.
What gives me this idea? Until just a couple of hours ago, the copy of WordPress installed at equifaxsecurity2017.com included a publicly accessible user database entry showing a user named “Edelman” was the first (and only?) user registered on the site.
Code that was publicly available on equifaxsecurity2017.com until very recently showed account information for an outside PR firm.
I reached out to Edelman for more information and will update this story when I hear from them.
EARLY WARNING?
In its breach disclosure Thursday, Equifax said it hired an outside computer security forensic firm to investigate as soon as it discovered unauthorized access to its Web site. ZDNet published a story Thursday saying that the outside firm was Alexandria, Va.-based Mandiant — a security firm bought by FireEye in 2014.
Interestingly, anyone who happened to have been monitoring look-alike domains for Equifax.com prior to yesterday’s breach announcement may have had an early clue about the upcoming announcement. One interesting domain that was registered on Sept. 5, 2017 is “equihax.com,” which according to domain registration records was purchased by an Alexandria, Va. resident named Brandan Schondorfer.
A quick Google search shows that Schondorfer works for Mandiant. Ray Watson, a cybersecurity researcher who messaged me this morning on Twitter about this curiosity, said it is likely that Mandiant has been registering domains that might be attractive to phishers hoping to take advantage of public attention to the breach and spoof Equifax’s domain.
Watson said it’s equally likely the equihax.com domain was registered to keep it out of the hands of people who may be looking for domain names they can use to lampoon Equifax for its breach. Schondorfer has not yet returned calls seeking comment.
EQUIFAX EXECS PULL GOLDEN PARACHUTES?
Bloomberg moved a story yesterday indicating that three top executives at Equifax sold millions of dollars worth of stock during the time between when the company says it discovered the breach and when it notified the public and investors.
Shares of Equifax’s stock on the New York Stock Exchange [NSYE:EFX] were down more than 13 percent at time of publication versus yesterday’s price.
The executives reportedly told Bloomberg they didn’t know about the breach when they sold their shares. A law firm in New York has already announced it is investigating potential insider trading claims against Equifax.
CLASS ACTION WAIVER?
Yesterday’s story here pointed out the gross conflict of interest in Equifax’s consumer remedy for this breach: Offering a year’s worth of free credit monitoring services to all Americans via its own in-house credit monitoring service.
This is particularly rich because a) why should anyone trust Equifax to do anything right security-wise after this debacle and b) these credit monitoring services typically hard-sell consumers to sign up for paid credit protection plans when the free coverage expires.
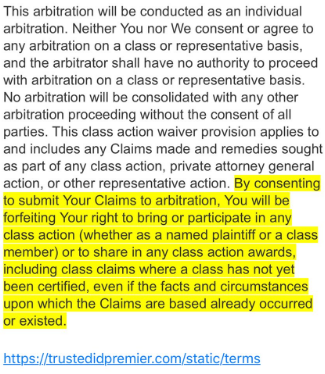
Verbiage from the terms of service from Equifax’s credit monitoring service TrustID Premier.
I have repeatedly urged readers to consider putting a security freeze on their accounts in lieu of or in addition to accepting these free credit monitoring offers, noting that credit monitoring services don’t protect you against identity theft (the most you can hope for is they alert you when ID thieves do steal your identity), while security freezes can prevent thieves from taking out new lines of credit in your name.
Several readers have written in to point out some legalese in the terms of service the Equifax requires all users to acknowledge before signing up for the service seems to include legal verbiage suggesting that those who do sign up for the free service will waive their rights to participate in future class action lawsuits against the company.
KrebsOnSecurity is still awaiting word from an actual lawyer who’s looking at this contract, but let me offer my own two cents on this.
Update, 9:45 p.m. ET: Equifax has updated their breach alert page to include the following response in regard to the unclear legalese:
“In response to consumer inquiries, we have made it clear that the arbitration clause and class action waiver included in the Equifax and TrustedID Premier terms of use does not apply to this cybersecurity incident.”
Original story:
Equifax will almost certainly see itself the target of multiple class action lawsuits as a result of this breach, but there is no guarantee those lawsuits will go the distance and result in a monetary windfall for affected consumers.
Even when these cases do result in a win for the plaintiff class, it can take years. After KrebsOnSecurity broke the story in 2013 that Experian had given access to 200 million consumer records to Vietnamese man running an identity theft service, two different law firms filed class action suits against Experian.
That case was ultimately tossed out of federal court and remanded to state court, where it is ongoing. That case was filed in 2015.
To close out the subject of civil lawsuits as a way to hold companies accountable for sloppy security, class actions — even when successful — rarely result in much of a financial benefit for affected consumers (very often the “reward” is a gift card or two-digit dollar amount per victim), while greatly enriching law firms that file the suits.
It’s my view that these class action lawsuits serve principally to take the pressure off of lawmakers and regulators to do something that might actually prevent more sloppy security practices in the future for the victim culpable companies. And as I noted in yesterday’s story, the credit bureaus have shown themselves time and again to be terribly unreliable stewards of sensitive consumer data: This time, the intruders were able to get in because Equifax apparently fell behind in patching its Internet-facing Web applications.
In May, KrebsOnSecurity reported that fraudsters exploited lax security at Equifax’s TALX payroll division, which provides online payroll, HR and tax services. In 2015, a breach at Experian jeopardized the personal data on at least 15 million consumers.
CAPITALIZING ON FEAR
Speaking of Experian, the company is now taking advantage of public fear over the breach — via hashtag #equifaxbreach, for example — to sign people up for their cleverly-named “CreditLock” subscription service (again, hat tip to @rayjwatson).
“When you have Experian Identity Theft Protection, you can instantly lock or unlock your Experian Credit File with the simple click of a button,” the ad enthuses. “Experian gives you instant access to your credit report.”
First off, all consumers have the legal right to instant access to their credit report via the Web site, annualcreditreport.com. This site, mandated by Congress, gives consumers the right to one free credit report from each of the three major bureaus (Equifax, Trans Union and Experian) every year.
Second, all consumers have a right to request that the bureaus “freeze” their credit files, which bars potential creditors or anyone else from viewing your credit history or credit file unless you thaw the freeze (temporarily or permanently).
I have made no secret of my disdain for the practice of companies offering credit monitoring in the wake of a data breach — especially in cases where the breach only involves credit card accounts, since credit monitoring services typically only look for new account fraud and do little or nothing to prevent fraud on existing consumer credit accounts.
Credit monitoring services rarely prevent identity thieves from stealing your identity. The most you can hope for from these services is that they will alert you as soon as someone does steal your identity. Also, the services can be useful in helping victims recover from ID theft.
My advice: Sign up for credit monitoring if you can (and you’re not holding out for a puny class action windfall) and then freeze your credit files at the major credit bureaus (it is generally not possible to sign up for credit monitoring services after a freeze is in place). Again, advice for how to file a freeze is available here.
Whether you are considering a freeze, credit monitoring, or a fraud alert (another, far less restrictive third option), please take a moment to read this story in its entirety. It includes a great deal of information that cannot be shared in a short column here.




Equifax and Experian are still charging for a credit freeze via their website as of 20 minutes ago (4:10 p.m. ET). While, Transunion and Innovis are not.
TransUnion just charged me $10 for a credit freeze.
Equifax should not be charging for freezing or unfreezing after this debacle, and they should be *paying for* freezes on the other two sites.
NY AG Schneiderman’s Twitter account https://twitter.com/AGSchneiderman is saying that the arbitration clause is/was unenforceable and Equifax seems to have changed their site to reflect that change
Signed up for freezes with three of the four.
All went smooth, simple, and free (NY state).
I was able to design my PIN with Experian.
Innovis will will mail the PIN in a letter.
Equifax gave the PIN as described by others (pretty unsecure way it is generated).
Have not done it with TU because it wants me to register with them first and, so far, I balked at that.
Should have added that all three sig-ups were done online.
You’re lucky that your state is free. Not here.
It costs $10 per bureau. Doing it for a family, $10 x # bureaus x family adds up.
Costs the same again to unfreeze, even temporarily.
Out of all of this, the Fair Credit Reporting Act should be amended to make freezing and unfreezing credit bureau reports free for everyone forever. No questions asked.
They claim they didn’t have prior knowledge, yet the WHOIS record for equifaxsecurity2017.com shows it was registered August 22nd. I’m gonna call BS.
Appears that Equifax uses sequential numbers for its generated PINs when you freeze your credit.
The whole ‘free credit monitoring for a year’ when some careless corporation loses all your data has always been a laughable slap in the face and a complete scam – the guys who dropped the ball don’t even have to pay for it. If they lost 50M peoples’ data, then Exquifax gets 50M one year free trials for their useless subscription service. Everyone wins except the victims, who get further victimized.
Turning around and doing it for yourself is a new level of chutzpah, though.
The whole thing is probably the result of a viral marketing study: “how can we convince the maximum number of people to sign up for our credit monitoring service”?
Hmm. A year from now articles on this topic will probably say “big-two credit bureaus.”
If Arthur Andersen didn’t survive the Enron cluster-***k, then Equifax may not survive this one.
(On the other hand, Moodys and Standard&Poors rating agencies survived the mortgage CDO meltdown even though they sold, for money, good ratings for those toxic assets.)
Llloyds of London, the insurance brokerage, has a system whereby their members — their “names” — assume unlimited liability. Their insurers may not be “Limited Liability Corporations.” If names want to limit their liability they need to write their contracts appropriately.
HIPAA and ARRA-2009 “pierce the corporate veil” for liability for breaches of health care data. Persons, not corporations (sorry, Mitt Romney), can be held civilly liable for harm done, and can be held criminally liable, if peoples’ health records leak due to their actions. One result of this is that errors&omissions insurance for outfits like that is very expensive.
Why shouldn’t the executives of companies handling sensitive Personally Identifiable Information (PII) have similar liability? Why shouldn’t the shareholders of those companies have that liability?
I completely agree!!! Well put!
Because we aren’t the customers; we’re the product. Unless the government regulates it, their only reason for keeping our information secret is to make their actual customers pay to get it. (Like that criminal in Viet Nam …)
Thanks for info. In addition to freezing our credit with all three bureaus, do you also suggest notifying the IRS/SSN offices? Do they offer any type of monitoring or protection services?
So Equifax is now being sued for $70b class action lawsuit but no one is giving information on how to join it. Any information on that weather one should join and if yes, how?
Some people see phantoms in the shadows. What sort of ‘sinister’ thing could EFX be up to? I’ve been on their announced website several times, accessed my account with no difficulty and no peculiar ‘happenings’. Experian went through a similar situation in 2015 and just about every U.S. government computer has been hacked. It’s not good news but a lot of finger pointing isn’t too productive.
Also it seems that a good number of people have no clue as how the economy steams ahead. Credit! Take down the three major reporting agencies and the economy folds. EFX does need to be public about the causes of the breach and up front on a faster basis than it has been so far. Then again, who is to say the FBI didn’t instruct EFX to remain silent during the early part of the investigation. Krebs negative wanderings are really unprofessional.
“Also it seems that a good number of people have no clue as how the economy steams ahead. Credit! Take down the three major reporting agencies and the economy folds.”
I pointed that out in a prior comment, but not just via taking down the reporting agencies. The same could be done against the credit card companies themselves using the millions of dark web credit card numbers whose sites could be compromised by nation-state actors and all of the CC numbers stolen. All could be held in reserve for a massive, simultaneous, -automated- attack on the US credit system. Guess what happens when millions suddenly have online fraudulent use of their CCs occurring along with other misuse of their personal data.
I’ve noticed what I’ll bet was a previous attack which was never reported in the news. Several years ago on -Veterans Day- I called my credit card numbers to make sure there had been no fraud on either prior to a trip. I’d experienced fraud, so I was being careful. NEITHER Visa nor Mastercard’s systems were working as far as the ability to check balance. I talked to a person at one of the two and they confirmed that they had no access to anyone’s account for that data. Veterans Day.
Admittedly, security and IT are difficult to get right and it’s expensive to write secure code. But, this is a bad, bad situation we are in. We don’t have any control over our data. What can we do to make a change?
Has anyone read “The Complete Privacy and Security Desk Reference, Vol 1”?
What Estonia has done, to use cryptography to “do” identity is really interesting.
https://www.economist.com/news/international/21605923-national-identity-scheme-goes-global-estonia-takes-plunge
@Franco
If Estonia had done it correctly it would be more interesting:
https://www.schneier.com/blog/archives/2017/09/security_flaw_i.html
– Sofa
Estonian SSN-s are public data. All business practices take this into count. Nobody can get a loan / credit by presenting your SSN / home address. Identity theft does not exist there. Not because of good privacy, but because consumer protection and sensible business rules.
Their crypto solution for identity is okay. Europe has strict rules for identity / digital signature solutions; look up eIDAS and QSCD (cryptographically strong signature creation device) for a reference.
What they have got is a weakness in the crypto implementation on the devices. This is only theoretical attack; no abuse is possible yet; the average citizen is not affected in any way; and they will fix it soon.
Meanwhile, they are still miles ahead of whatever US consumers have. Most of the Europe is. Estonia is ahead in the sense that they have most citizens covered with decent identity devices, but the eIDAS scheme and consumer privacy protection laws are the same across all Europe.
Some very smart people I know suggest that keeping your personal information secret is as obsolete as forts in modern warfare. They suggest having a better totally open way to VERIFY that you are you, and that your actual data that is accurate be stored somewhere where it cannot be overwritten would be a smarter way to make a system that works. I sometimes wonder if this is what we should be striving for. Congress tried something similar but failed in the Real ID Act.
As a note, checking your information at the https://www.equifaxsecurity2017.com/ site twice on a desktop will cause it to show ‘may have’. So that may just be a side effect of having viewed entered data on a desktop and then on a phone.
Some states waive the charge for a credit freeze if you are the victim of security breach. Anyone know in which states this breach will allow them to get a security freeze at no charge?
I went into the Equifax site and three times and entered my information for my three different last names and each time received the exact same response. I received two ‘no’s’ and one ‘may have’.
I went into the Equifax website three times and entered my information for my three last names. Each time I received the exact same response. I was told two ‘nos’ and one ‘may have’.
can you provide a link in the relevant section of the article to whichever past article you use to recommend that consumers put a “security lock” on their accounts? i’m not sure what that means in this context, and i’m sure others are in the same boat.
try google they know about these things, google for:
site:krebsonsecurity.com freeze
The “barbarians” overwhelming the roman “system?” Geeze.
You’re doing great work here Brian, and we all appreciate it. You convinced me to freeze my credit reports a couple years ago and I’ve been preaching it to my friends and family every since.
Hopefully those of us who have taken this small precaution will be spared any negative fallout from this fiasco.
Since the data breached may have included the means to reset the PINs for our freezes, our only remaining protection comes from an unlikely source: the fact that, at least here in CA, it seems as well as having the PIN you need to pay for the un-freeze. Hopefully that will deter the crims somewhat.
FWIW, Equifax has updated their security2017 page to include:
“In response to consumer inquiries, we have made it clear that the arbitration clause and class action waiver included in the Equifax and TrustedID Premier terms of use does not apply to this cybersecurity incident.”
“please take a moment to read this story in its entirety”
Which story?
The one linked in the previous sentence: https://krebsonsecurity.com/2015/06/how-i-learned-to-stop-worrying-and-embrace-the-security-freeze/
Wouldn’t it be great fun if what was stolen was actually the first six numbers of your social security number, and by entering the last six digits to check if your data was compromised, you actually provided the right information to become compromised?
I’m kidding, of course, but during sign-up for the various credit monitoring sites, one realizes that there is some truth in this line of thinking. You are sharing information over the wire to gain protection. The irony.
I agree that freezing one’s credit report issuance with the bureaus and setting very low-threshold alerts all accounts is the smartest course of action.
Beyond that, some of these credit monitors appear to have rather laggard technology, themselves. As Krebs says, “the intruders were able to get in because Equifax apparently fell behind in patching its Internet-facing Web applications.” I have to believe that so have many of these so-called credit monitors.
It’s worse than that. The first three digits of your SSN are coded to where you were living when you applied. Since the 1980s, parents have had to get SSNs on newborns to deduct them on their taxes. So almost all people born after that will have SSNs whose first three digits are predictable from their place of birth, which is public information.
I tried freezes at all four this morning. Three went smooth using the online forms. Only Equifax refused to freeze my account. The message displayed tells me to put all of my details _and_ my credit card info into an envelope and mail it to them. The instructions aren’t particularly clear, I don’t really want to wait for snail mail, and I can only imagine how enticing an envelope addressed to Equifax might be. I don’t particularly trust the US mail these days (My mail woman drives a dented 90s area Grand Cherokee and usually wears shorts and a t-shirt, doesn’t instil much confidence)
If you sign up for the Equifax service, however, you can turn your last class with them on and off at will.
Any advice from you kind folk? Do I snail mail, sign up with Equifraud, or keep trying their site hoping it changes it’s mind?
If you don’t trust your local mail carrier, DO NOT BE LAZY and “live only on the interwebs”. Get in your own vehicle and drive to the nearest post office yourself and drop the envelope in the slot yourself.
As for not wanting to wait for “snail mail”, I hate to inform you but you are not making the rules in this relationship with Equifax.
As for your mail carrier, how far out “in the sticks” to you live to have a mail carrier that is driving what sounds like a personal vehicle, and that suggests “rural mail carrier” to me.
Quick one:
Google’s reCaptcha in the form (as in collected data) + last names + last numbers of SSNs => love all the way…. and some more profiling. Nicey…
Gr8 point. Does Google gain man in the middle status, collecting SSN’s by virtue of its captcha being on the page?
This whole setup, with a third party site represented as Equifax, but with no authenticated SSL ownership or domain name of Equifax on it, shows an ongoing ferocious lack of security protocol.
Just having Google on the page alone should ward off anyone self-breaching on this site.
Gr8 point. Does Google gain man in the middle status, collecting SSN’s by virtue of its captcha being on the page?
This whole setup, with a third party site represented as Equifax, but with no authenticated SSL ownership or domain name of Equifax on it, shows an ongoing ferocious lack of security protocol.
Just having Google on the page alone should ward off anyone self-breaching on this site.
I just wonder why don’t they close those (rogue) bureaus altogether once and for all?
The only things they do is giving headaches to the 5-to-5 folks…
See if your personal information is potentially impacted
clicking the link now gives:
This site can’t be reached
trustedidpremier.com
Went to annualcreditreport.com for a copy of my credit reports. TransUnion and Experian worked fine.
When it came time to get the Equifax report — you guessed it — I got an error. No dice.
I just tried to sign up for a freeze at all four companies.
Experian worked, charged me $10, which I will sue Equifax for. Plus expenses.
Innovis asked me if I was an identity theft victim. I said I was. So is everyone, due to Equifax. They froze me for free.
TransUnion made me go through the entire process, including entering my credit card number, then told me that they couldn’t do it.
Equifax at least let me freeze my account (for whatever that promise is worth) without trying to charge me for it.
But TransUnion more than likely charged you anyway, there’s probably a pending charge on your card. Same thing happened to me and TransUnion charged me 4 times within 20 minutes even though I tried to Security Freeze only once.
As of now, it appears TransUnion’s Security Freeze website is down or only partially working. I went to Freeze last night, got up to the pay $5 … the TransUnion Site errored and said it couldn’t process the Freeze. I check my credit card, and even though TransUnion never did the Security Freeze … TransUnion charge my card twice within a minute. You can’t get through to TU about the issue, so I had my credit card company nix the TU charges. Then 2 more TU $5 charges appeared. Had my Credit Card company nix those too, close my old credit card number and reissue me a new card number. I’d stay away from TU Security Freeze until they get their site back in order.
“We pride ourselves on being a leader in managing and protecting data, and we are conducting a thorough review of our overall security operations.”
Pffft… What happened here amounts to (at-least) criminal negligence. The fat-wallets at Equifax should serve hard time for their crimes. Instead, watch how they float away free and clear on their golden parachutes, while some clueless IT person from India on an H1-B visa gets hung out to dry.
I don’t even care if I don’t see a penny from a class action suit I just want to see Equifax ground into dust.
Also, freezing and unfreezing credit should be free. Congress should really fix that.