A Web site set up by PC maker Dell Inc. to help customers recover from malicious software and other computer maladies may have been hijacked for a few weeks this summer by people who specialize in deploying said malware, KrebsOnSecurity has learned.
There is a program installed on virtually all Dell computers called “Dell Backup and Recovery Application.” It’s designed to help customers restore their data and computers to their pristine, factory default state should a problem occur with the device. That backup and recovery program periodically checks a rather catchy domain name — DellBackupandRecoveryCloudStorage.com — which until recently was central to PC maker Dell’s customer data backup, recovery and cloud storage solutions.
Sometime this summer, DellBackupandRecoveryCloudStorage.com was suddenly snatched away from a longtime Dell contractor for a month and exposed to some questionable content. More worryingly, there are signs the domain may have been pushing malware before Dell’s contractor regained control over it.

Image: Wikipedia
The purpose of DellBackupandRecoveryCloudStorage.com is inscribed in the hearts of countless PCs that Dell shipped customers over the past few years. The domain periodically gets checked by the “Dell Backup and Recovery application,” which “enables the user to backup and restore their data with just a few clicks.”
This program comes in two versions: Basic and Premium, explains “Jesse L,” a Dell customer liaison and a blogger on the company’s site.
“The Basic version comes pre-installed on all systems and allows the user to create the system recovery media and take a backup of the factory installed applications and drivers,”Jesse L writes. “It also helps the user to restore the computer to the factory image in case of an OS issue.”
Dell customer liaison Jesse L. talks about how the program in question is by default installed on all Dell PCs.
In other words: If DellBackupandRecoveryCloudStorage.com were to fall into the wrong hands it could be used to foist malicious software on Dell users seeking solace and refuge from just such nonsense!
It’s not yet clear how or why DellBackupandRecoveryCloudStorage.com got away from SoftThinks.com — an Austin, Tex.-based software backup and imaging solutions provider that originally registered the domain back in mid-2013 and has controlled it for most of the time since. But someone at SoftThinks apparently forgot to renew the domain in mid-June 2017.
SoftThinks lists Dell among some of its “great partners” (see screenshot below). It hasn’t responded to requests for comment. Some of its other partners include Best Buy and Radio Shack.
Some of SoftThinks’ partners. Source: SoftThinks.com
From early June to early July 2017, DellBackupandRecoveryCloudStorage.com was the property of Dmitrii Vassilev of “TeamInternet.com,” a company listed in Germany that specializes in selling what appears to be typosquatting traffic. Team Internet also appears to be tied to a domain monetization business called ParkingCrew.
If you’re not sure what typosquatting is, think of what sometimes happens when you’re typing out a URL in the browser’s address field and you fat-finger a single character and suddenly get redirected to the kind of content that makes you look around quickly to see if anyone saw you looking at it. For more on Team Internet, see this enlightening Aug. 2017 post from Chris Baker at internet infrastructure firm Dyn.
It could be that Team Internet did nothing untoward with the domain name, and that it just resold it or leased it to someone who did. But approximately two weeks after Dell’s contractor lost control over the domain, the server it was hosted on started showing up in malware alerts.
That’s according to Celedonio Albarran, assistant vice president of IT infrastructure and security at Equity Residential, a real estate investment trust that invests in apartments.
Albarran said Equity is responsible for thousands of computers, and that several of those machines in late June tried to reach out to DellBackupandRecoveryCloudStorage.com but were prevented from doing so because the Internet address tied to the domain was new and because that address had been flagged by two security firms as pushing malicious software.
On that particular day, anyone visiting DellBackupandRecoveryCloudStorage.com simultaneously would have been heading to the Internet address 54-72-9-51 (I’ve replaced the dots with dashes for safety reasons). Albarran said the first alert came on June 28 from a security tool from Rapid7 that flagged a malware detection on that Internet address.
Another anti-malware product Equity Residential uses is Carbon Black, which on June 28 detected a reason why a Dell computer within the company shouldn’t be able to visit dellbackupandrecoverycloudstorage.com. According to Albarran, that second alert was generated by Abuse.ch, a Swiss infrastructure security company and active anti-abuse advocate.
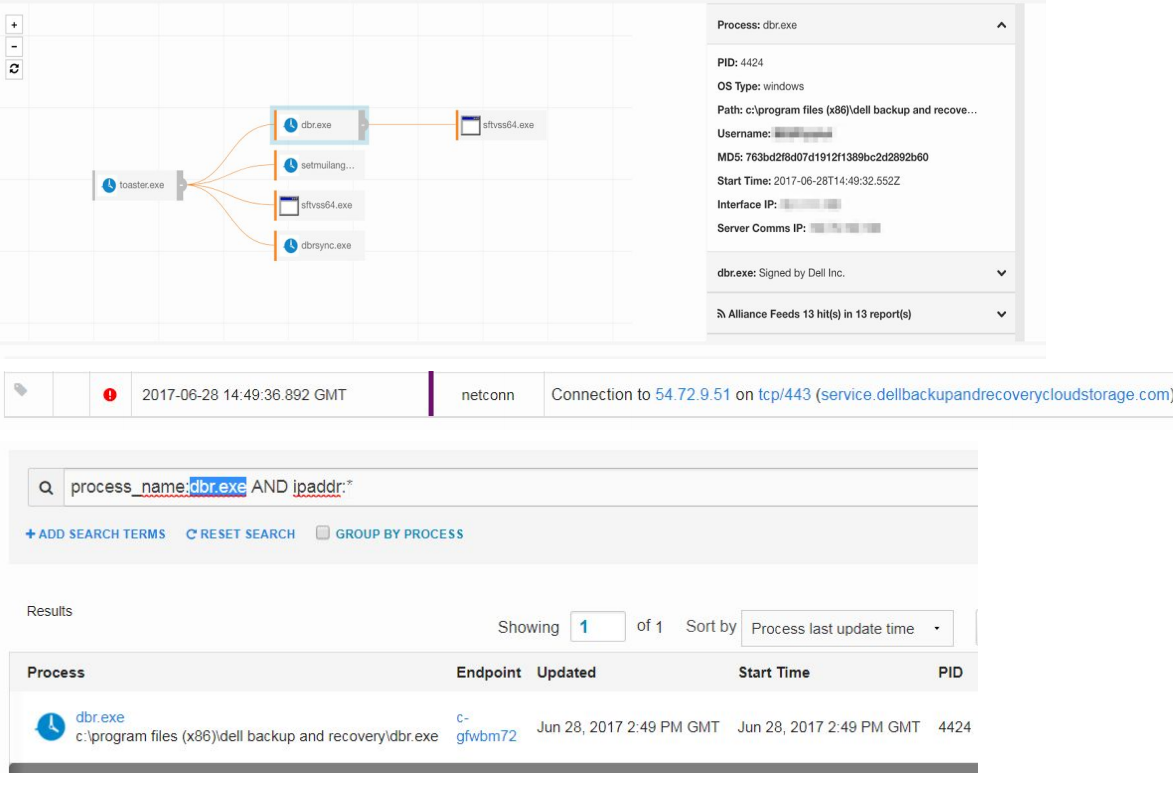
This Carbon Black log shows dellbackupandrecoverycloudstorage.com reaching out to a nasty Internet address on June 28, 2017.
The domain’s host appears to have been flagged by Abuse.ch’s Ransomware Tracker, which is a running list of Internet addresses and domains that have a history of foisting ransomware — a threat that encrypts your files with tough-to-crack encryption, and then makes you pay for a key to unlock the files.
Albarran told KrebsOnSecurity that his company was never able to find any evidence that computers on its networks that were beaconing home to DellBackupandRecoveryCloudStorage.com had any malware installed as a result of the traffic. But he said his systems were blocked from visiting the domains on June 28, 2017, and that his employer immediately notified Dell of the problem.
“A few weeks after that they confirmed they fixed the issue,” Albarran said. “They just acknowledged the issue and said it was fixed, but they didn’t offer any comment besides that.”
AlienVault‘s Open Threat Exchange says the Internet address that was assigned to DellBackupandRecoveryCloudStorage.com in late June is an Amazon server which is “actively malicious” (even today), categorizing it as an address known for spamming.
Reached for comment about the domain snafu, Dell spokesperson Ellen Murphy shared the following statement:
“A domain as part of the cloud backup feature for the Dell Backup and Recovery (DBAR) application, www.dellbackupandrecoverycloudstorage.com, expired on June 1, 2017 and was subsequently purchased by a third party. The domain reference in the DBAR application was not updated, so DBAR continued to reach out to the domain after it expired. Dell was alerted of this error and it was addressed. Dell discontinued the Dell Backup and Recovery application in 2016.”
I have asked Dell for more information about this incident, such as whether the company knows if any customers were harmed as a result of this rather serious oversight. I’ll update this story in the event that I hear back from Dell.
This is not the first time the failure to register a domain name caused a security concern for a company that should be very concerned about security. Earlier this month, experts noticed that the Web sites for credit bureaus Trans Union and Equifax were both redirecting browsers to popup ads that tried to disguise adware and spyware as an update for Adobe Flash Player.
The spyware episodes at Equifax’s and Trans Union’s Web sites were made possible because both companies outsourced e-commerce and digital marketing to Fireclick, a now-defunct digital marketing product run by Digital River. Fireclick in turn invoked a domain called Netflame.cc. But according to an Oct. 13 story in The Wall Street Journal, Netflame’s registration “was released in October 2016, three months after Digital River ended support for Fireclick as part of an ‘ongoing domain cleanup.'”
The problem with the Dell customer support domain name comes as Dell customers continue to complain of being called by scammers pretending to be Dell tech support specialists. In many cases, the callers will try to make their scams sound more convincing by reading off the unique Dell “service tag” code printed on each Dell customer’s PC or laptop.
How can scammers have all this data if Dell’s service and support system isn’t compromised, many Dell customers have asked? And still ask: I’ve had three readers quiz me about these Dell service tag scams in the past week alone. Dell continues to be silent on what may be going on with the service tag scams, and has urged Dell customers targeted by such scams to report them to the company.




Today, there’s malicious communication inbound to 54.72.9.51 –simplyinstaller.com–not only outbound:
xhttps://www.virustotal.com/en/file/ddac96e18627fe11b6ea6ddf8f28a874805c566139cd6a765af8db62acf4595b/analysis/#behavioural-info
Sality malware too:
xhttps://www.virustotal.com/en/file/fd1b9c3db6ec566cb731d5bcd720952a382c817b16f154845395241de358146f/analysis/#behavioural-info
The virustotal consolidated information on the IP doesn’t go back to early June-July.
There are heavy amounts of malicious inbound communications to the IP as far back as the virustotal record shows, every day since October 9th (and likely before that date):
“Latest detected files that communicate with this IP address” >
http://www.virustotal.com/en/ip-address/54.72.9.51/information
xhttps://hosts-file.net/?s=54.72.9.51&view=matches&page=14 back to early June-July, dated in dd/mm/yyyy: Categorized as Exploits, Phishing, Fraudulent software and websites
Well, is it a given in this day and age to assume that pretty much every popular website was compromised and that representatives of that company will be refusing it if pressed? Especially dinosaur companies like Dell.
PS. When I purchase a Dell computer, the first thing I do is I wipe it clean and install my own (clean) version of Windows/Linux. This has a benefit of also wiping out all their (buggy) crapware.
Good research. It appears the domain was let go last year, after DBAR was discontinued last year. It shows, people and companies need to hold domains in higher regard than their $10.00 renewal allows, because of identity theft-related fraud.
Why don’t companies simply use subdomains? This is something that could have been avoided entirely by using BackupandRecoveryCloudStorage.Dell.com instead of DellBackupandRecoveryCloudStorage.com
They should be penalized financially for such stupidity.
I’ve wondered this also, but using this example, the argument may have been that customers who don’t understand domain names would be victimized by a typo-squatter who purchased BackupandRecoveryCloudStorageDell.com , attempting to snare traffic to BackupandRecoveryCloudStorage.Dell.com .
But for pre-installed domain names that customers never need to type, the subdomain is a much better solution.
It would be wise for companies to spend an extra $10 a year and additionally register all their sub domains without the period.
BackupandRecoveryCloudStorage.Dell.com
and
BackupandRecoveryCloudStorageDell.com
Much cheaper than fighting a lawsuit.
Some Apple accounts were compromised, I imagine, by phishers using just such a technique: register SupportApple.com and copy Apple’s graphics for the phishing email! Apple would do well to use UDRP to confiscate those impersonating domains:
supportapple.com
appleidapple.com
checkcoverageapple.com
securityapple.com
getsupportapple.com
iforgotapple.com
The above are based on subdomains of apple.com, such as:
support.apple.com
appleid.apple.com
etc., and owned by people other than Apple, and are likely used in phishing attempts to get into Apple owners’ accounts!
I don’t own anything, nor will I purchase anything Apple.
BackupandRecoveryCloudStorage.Dell.com
and
BackupandRecoveryCloudStorageDell.com
are both just wrong domain names anyway either as subdomain or primary domain names.
It’s about time that we [all of ‘us’] stopped using stupidlylongdomainnames which are likely to result in typo fraud.
Enterprises should be user friendly and stop using them and users/customers should stop using them in pursuit of self-preservation and sanity.
For instance my personal bank provides online banking services at onlinebankingmybanksname.com
brief sensible subdomains may be acceptable such shop.dell.com perhaps or support.dell.com but the silly stuff should be resisted by users and eventually the kids with the marketing MBA’s will come to recognise the insanity of their product.
Thanks.
JB
Joe Blogs said:
Right! And don’t be a tightwad, and register:
ShopDell.com
SupportDell.com
to protect those subdomains!
“Apple takes the security of your personal information very seriously.”
– https://www.apple.com/legal/privacy/en-ww
Biggest lie ever told.
Squeeze out a few greand, and reserve the dot com of your subdomains, if you care about your customers, Apple!
I don’t think you’re very familiar with the internal workings or economics of software companies if you’re asking this question… Considering it was a third party providing the service it being hosted on a dell.com subdomain is not an option.
Letting third party companies you contract host services on your subdomains would be far more risky and potentially damaging to the company than having them lose control of their own domain. Like orders of magnitude worse.
Oh so true Evan….oh so true. Allowing a backup service provider on your subdomain directly, eeeeeeesh.
Someone already gave the answer, but…
access to web servers via domains in web browsers historically have been secured via cookies. Roughly, a browser and a website can agree to allow sharing cookies between related domains.
(clientbackup.dell.com and http://www.dell.com would be related domains)
The first problem is that this web site isn’t actually run by dell, but by an affiliate. In general, you really don’t want an affiliate to be able to get access to your own domain’s cookies.
There are some ways around this, but it isn’t particularly simple.
In the end, most companies just add additional domains.
As someone said, secure cookies are a reason not to allow a third-party contractor access to your domain. But, a simple CNAME could be been used.
BackupandRecoveryCloudStorage.Dell.com could simply be pointed as a CNAME to BackupandRecoveryCloudStorageDell.com.
Then, when the contract was up, Dell could remove the CNAME and point the domain at their own page on Dell.com notifying customers that DBAR had ended and instructions on how to remove the software.
Great article as always, Brian. I have a Dell computer but I do not use clouds. I’ve seen too many problems over the years. I use an external hard drive for backup and I use Kaspersky for security which, despite some ridiculous articles recently, is not in league with the Russian government.
I have the option of using Microsoft’s cloud but I don’t have a whole lot of faith in them either. I work for a government entity and they sub contracted personnel data to a company in India. The next thing we knew there was a problem so we all got protection for a year. Sound familiar? I’ve got it with Equifax too.
So Dmitrii Vassilev also owns crypto-mine.com, maybe another clue as to what hes up to……
https://www.whois.com/whois/crypto-mine.com
Great informative article.
Dell’s ‘Jesse L’ greatest day = gets appointed official Dell blogger.
Dell’s ‘Jesse L’ worst day = gets called out by KrebsonSecurity.
Dell’s ‘Jesse L’ biggest regret = forgot fav t-shirt on profile pic day.
Dell should be more concerned about their service tag data being compromised. Short of a hack on Dell infrastructure, their bloatware is beaconing out the service tag everytime Dells bloatware phones home.
In my shop, I’ve seen evidence that hackers are hijacking automatic updaters to ride back into the machine using (I believe) some sort of man-in-the-middle attack that allows them to hijack a TCP/IP session. “HP Update”, “GarminExpress” are two the should be looked into. Too bad I can’t get anyone to look into these.
Think about it…what have these miscreants learned from the exploitation of Flash/Java updates? Yep, we don’t need you to click on anything. Your computer manufacturer has done it for us. All we have to do is hijack what’s already in place.
Sound advice from earlier post – wipe and reload!!!
First, why did Dell stupidly not register the domain itself? And register it for, say, five or ten years? IIRC, I have my own domain registration paid for the next five years.
Second… not *all* Dell servers. They sell a lot with either no o/s installed, or with Linux. And that b/u system doesn’t work with Linux.
Datum: I work for a federal contractor, civil sector, and of our fed Office’s around 150 servers that we sysadmins deal with, we have three (count them) Windows servers. .. and I assure you that this backup isn’t running, esp. behind the agency’s firewall.
Nothing like subcontracting out essential services to incompetents for maximizing shareholder value!
Have used free Macrium Reflect for many years and recoveries, from UK Paragon software. Have never experienced a vendor restore, or Microsoft one that worked.
Used Macrium on WXP, 7 and – once on 10 used Macrium when HP restore was needed, on a new system, and it cajled and froze after 1 1 /2 hours. As a habit one of the first things I do is backup new system with Macrium. You can create a bootable disc or USB to boot and restore OS, – on another computer if necessary. Restore with Macrium Reflect is simple, and works in a half hour or so.
I second that. Macrium Reflect is superb!
Recently I cloned my system (Windows 7) to a new larger internal SSD drive. It worked perfectly – the only slight inconvenience I experience is that every now and then I get a message that my Windows is not genuine. Microsoft told me I can reinstall Windows, but if I don’t, nothing happens (except these messages). I can live with these messages – and prefer that to a time consuming reinstall.
PS. I should add: Recently I cloned my system … using Macrium Reflect.
I should add: …Recently I cloned my system … using Macrium Reflect.
54.72.9.51 currently has www-paypal.com.updateoinformation.com pointing to it along with many other sites: https://www.virustotal.com/#/ip-address/54.72.9.51 . This DNS name was flagged by Alien Vault in January, looks like they waited 9 months and went right back at it.
This is a “feature” of their retail desktops, but their servers have a remote access device called an iDRAC that runs a web server and the Tomcat java appliance.
But I’m sure that’s all secured, patched, and maintained right, Dell?
Nothing like subcontracting out essential services to incompetents for maximizing shareholder value!
Ah its a amazing informatiable article, thanks for sharing with me. İ loved.
Most domain registrars offer auto-renewal, so it’s pretty silly to allow these domains to expire. Granted, credit cards behind auto-renewal also expire.
Auto-renew is a suggestion that has been cited by bloggers much of late with the high-profile domain expiries that took down Marketo.com, Sorenson Telecom and a bunch of IBM cloud apps (to cite a few.) The thing is “don’t forget to set auto-renew” is like saying “don’t forget to lock the doors to your building when you leave.” The reason there is a process-controlled building security industry is to protect we humans from our habitual forgetfulness. The fact is, SoftThinks having being a mission critical app to Dell (and others) should register all their domains with a corporate registrar that has a system for monitoring domains, including all resource records. Network engineers use monitoring and alarms as a matter of course. Domains and DNS (equally critical) are rarely monitored as closely. Companies that use multiple retail registrars are an accident waiting to happen. Systems with permissioned access, 2FA, secure audits, real-time monitoring (etc.) is the answer. Not “don’t forget to set auto-renew.”
What site/utility is used in last screenshot?
The lesson here is that if a company ever uses a site to serve updates, it has to own it forever (25+ years) instead of just saying “Oh, our software reached end of life, we don’t need the domain anymore.”
If they want to discontinue the service, they need to let people that they no longer use it rather not just letting people know after the fact.
They need to create a main domain that they own for as long they are in business. Then create a subdomain that they can use until the end of life. Should the customer continue to use it and find it it does not work, it would be directed to the main one which would indicate to the customers to contact the company.
One of the biggest problem lies in the fact they don’t do due diligence on domains after the acquisition of said business rather than streamlining it and eliminate the excess DNS they don’t need. It lies with management’s ineptitude in dealing with security of the domain.
I hope in one day that i can own a big company like Dell , But i think their way is not professional as supposed to be .
Big companies like Dell need more respect for their customers.
If you plan on registering a domain name please read the “fine print” (especially if you allow a hosting company to register the domain for you.) You may be surprised to find out that you don’t actually own the domain. You don’t actually own a domain name any more than you “own” your phone number anyway, but instead the hosting company retains all rights to that name and can do anything they want with it, including selling it to someone else. This happens all of the time. We lost a very valuable domain when our hosting company didn’t automatically renew the name, although they had been doing so for years. Our domain expired on a Tuesday, and on Wednesday it had been sold to someone else. No notice, no reclamation period, nothing, just gone. We file complaints with ICANN, hired lawyers, etc. We ended up getting compensation, but never got the domain back.
I have a lot of Seneca PCs which also use PC Angel by Softthinks for pre-win8+ recovery options.
Only recently I’ve been seeing Avast detect their files hidden in the recovery volume. DEVLOG.EXE and DrvInst.exe.
I wonder if this is related?
Thanks for sharing useful information
Application Support
Prior to this article, I brought this to Dell’s attention on Sept. 13th, and it seemed to me that not everyone at Dell was aware of this expired site. We saw traffic on our network and alerts that indicated that this site was compromised. That’s when we reached out to Dell. Supposedly our data and reports that we provided to them, reached their IT Security and Legal team. I was told that they were investigating. Mind you, this dragged on until Oct 16th, they stated that bad domain is now being redirected to a proper site. So based on that info, Dell let this go on longer than they may have admitted. If it was overtaken in Mid June, and I got a direct response from Dell that traffic was finally been redirected, that’s 4ish months.
Domains expiring are a common occurrence. Notifications go to either individuals or sometimes email aliases. If the person who’s listed has left the company or otherwise doesn’t get the email then the domain will not be paid for and get unregistered. The same if an email alias gets turned off or disabled.
Lots of companies are going to corporate Top Level Domains (TLD’s). For example, support.dell or home.dell. Not sure these would help this particular situation since it was a subcontractor. In theory, dell could have given up a name under *.Dell but who knows if that would have helped.