A powerful, easy-to-use password stealing program known as Agent Tesla has been infecting computers since 2014, but recently this malware strain has seen a surge in popularity — attracting more than 6,300 customers who pay subscription fees to license the software. Although Agent Tesla includes a multitude of features designed to help it remain undetected on host computers, the malware’s apparent creator seems to have done little to hide his real-life identity.
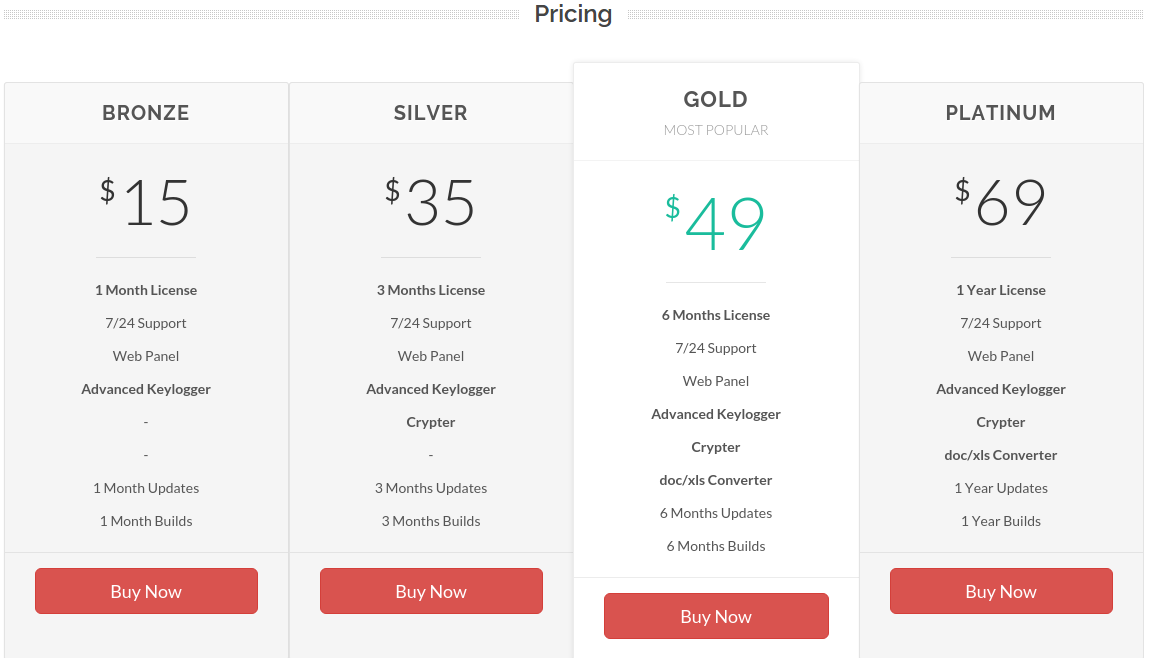
The proprietors of Agent Tesla market their product at agenttesla-dot-com, selling access to the software in licenses paid for via bitcoin, for prices ranging from $15 to $69 depending on the desired features.
The Agent Tesla Web site emphasizes that the software is strictly “for monitoring your personel [sic] computer.” The site’s “about” page states that Agent Tesla “is not a malware. Please, don’t use for computers which is not access permission.” To backstop this disclaimer, the site warns that any users caught doing otherwise will have their software licenses revoked and subscriptions canceled.
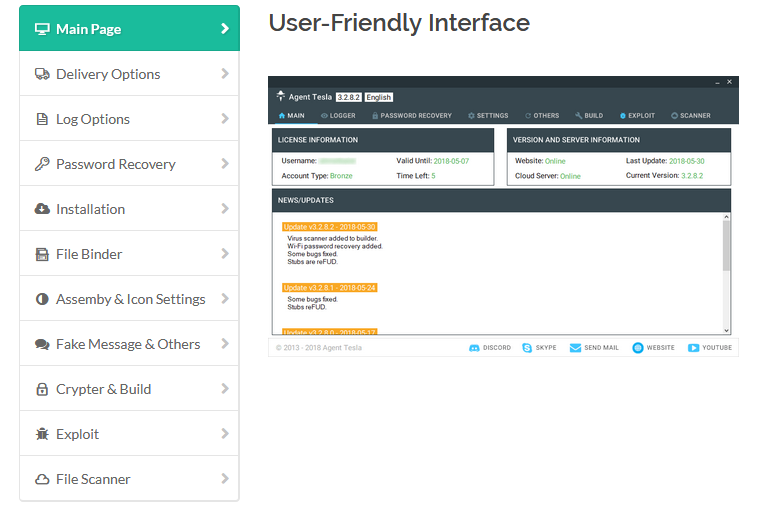
At the same time, the Agent Tesla Web site and its 24/7 technical support channel (offered via Discord) is replete with instances of support personnel instructing users on ways to evade antivirus software detection, use software vulnerabilities to deploy the product, and secretly bundle the program inside of other file types, such as images, text, audio and even Microsoft Office files.
In August 2018, computer security firm LastLine said it witnessed a 100 percent increase in Agent Tesla instances detected in the wild over just a three month period.
“Acting as a fully-functional information stealer, it is capable of extracting credentials from different browsers, mail, and FTP clients,” LastLine wrote. “It logs keys and clipboards data, captures screen and video, and performs form-grabbing (Instagram, Twitter, Gmail, Facebook, etc.) attacks.”
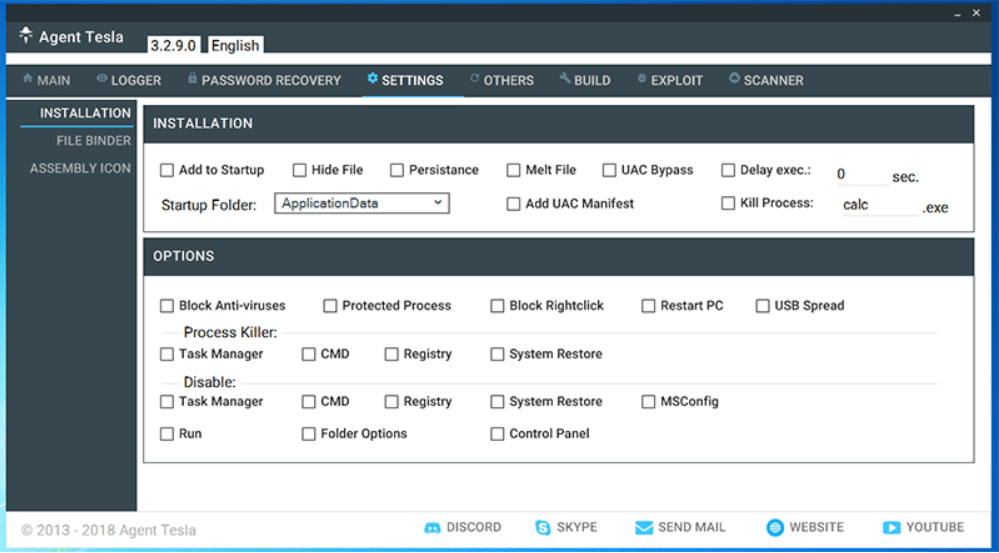
Most of the options included in Agent Tesla revolve around stealth, persistence, evading security tools, spreading to other computers, or tampering with system settings.
I CAN HAZ TESLA
The earliest versions of Agent Tesla were made available for free via a Turkish-language WordPress site that oddly enough remains online (agenttesla.wordpress-dot-com), although its home page now instructs users to visit the current AgentTesla-dot-com domain. Not long after that WordPress site was erected, its author(s) began charging for the software, accepting payments via a variety of means, including PayPal, Bitcoin and even wire transfer to several bank accounts in Turkey.
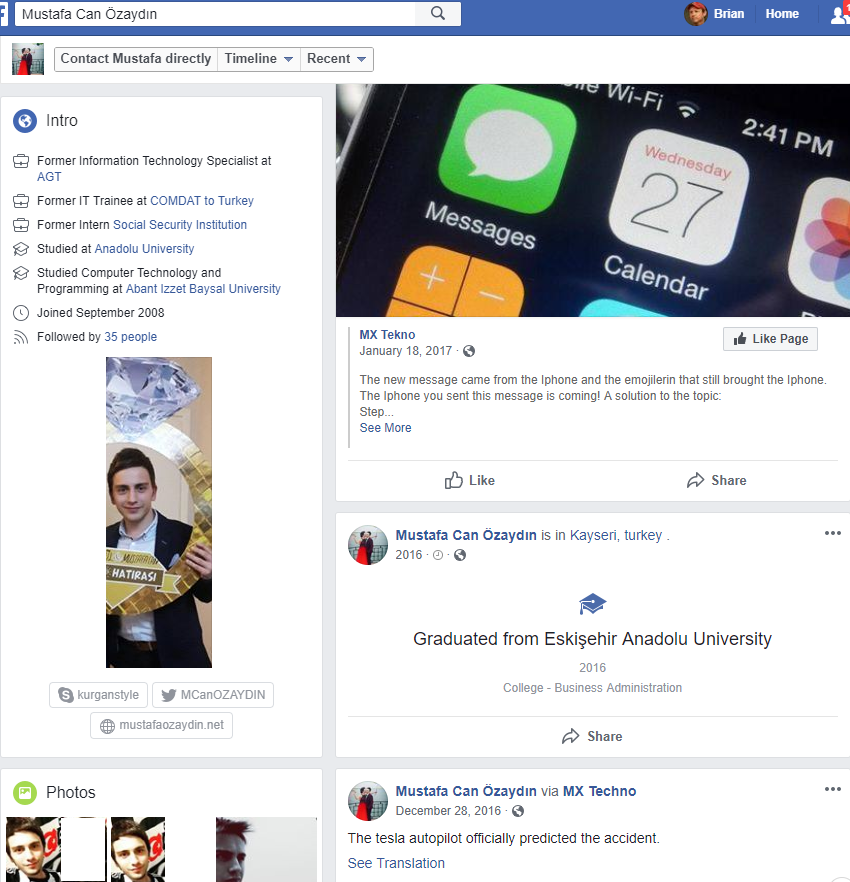 Historic WHOIS Web site registration records maintained by Domaintools.com show that the current domain for the software — agenttesla-dot-com — was registered in 2014 to a young man from Antalya, Turkey named Mustafa can Ozaydin, and to the email address mcanozaydin@gmail.com. Sometime in mid-2016 the site’s registration records were hidden behind WHOIS privacy services [full disclosure: Domaintools is a previous advertiser on KrebsOnSecurity].
Historic WHOIS Web site registration records maintained by Domaintools.com show that the current domain for the software — agenttesla-dot-com — was registered in 2014 to a young man from Antalya, Turkey named Mustafa can Ozaydin, and to the email address mcanozaydin@gmail.com. Sometime in mid-2016 the site’s registration records were hidden behind WHOIS privacy services [full disclosure: Domaintools is a previous advertiser on KrebsOnSecurity].
That Gmail address is tied to a Youtube.com account for a Turkish individual by the same name who has uploaded exactly three videos over the past four years. In one of them, uploaded in October 2017 and titled “web panel,” Mr. can Ozaydin demonstrates how to configure a Web site. At around 3:45 in the video, we can see the purpose of this demonstration is to show people one way to install an Agent Tesla control panel to keep track of systems infected with the malware.
Incidentally, the administrator of the 24/7 live support channel for Agent Tesla users at one point instructed customers to view this same video if they were having trouble figuring out how to deploy the control panel.
The profile picture shown in that Youtube account is remarkably similar to the one displayed on the Twitter account “MCanOZAYDIN.” This Twitter profile makes no mention of Agent Tesla, but it does state that Mustafa can Ozaydin is an “information technology specialist” in Antalya, Turkey.
That Twitter profile also shows up on a Facebook account for a Mustafa can Ozaydin from Turkey. A LinkedIn profile for a person by the same name from Antalya, Turkey states that Mr. can Ozaydin is currently a “systems support expert” for Memorial Healthcare Group, a hospital in Istanbul.
KrebsOnSecurity first reached out for comment to all of these accounts back in August 2018, but received no reply. Repeated attempts to reach those accounts this past week also elicited no response.
MALWARE OR BENIGN REMOTE ACCESS TOOL?
Many readers here have taken the view that tools like Agent Tesla are functionally no different from more mainstream “remote administration tools” like GoToMyPC, VNC, or LogMeIn, products that are frequently used by tech support personnel to remotely manage one or more systems to which those personnel legitimately have access rights.
U.S. federal prosecutors, meanwhile, have adopted a different position. Namely, when someone selling a remote administration tool begins instructing customers on how to install the product in ways that are arguably deceptive (such as through the use of software exploits, spam or disguising the tool as another program), the proprietor has crossed a legal line and can be criminally prosecuted under computer misuse laws.
In previous such cases, the prosecution’s argument has hinged on the procurement of chat logs showing that the software seller knew full well his product was being used to infect computers without the users’ knowledge or permission.
Last week, a Lexington, Ky. man was sentenced to 30 months in federal prison after pleading guilty to conspiracy to unlawfully access computers in connection with his admitted authorship of a remote access tool called LuminosityLink.
Colton Grubbs, 21, admitted to selling his software for $39.99 apiece to more than 6,000 customers in at least 78 different countries. LuminosityLink allowed his customers to record the keys that victims pressed on their keyboards, spy on victims using their computers’ cameras and microphones, view and download the computers’ files, and steal names and passwords used to access websites.
“Directly and indirectly, Grubbs offered assistance to his customers on how to use LuminosityLink for unauthorized computer intrusions through posts and group chats on websites such as HackForums,” the Justice Department wrote in a press release about the sentencing. Grubbs must also forfeit the proceeds of his crimes, including 114 bitcoin, presently valued at more than $725,000.
Around the time that Grubbs stopped responding to support requests on Hackforums, federal prosecutors were securing a guilty plea against Taylor Huddleston, a then 27-year-old programmer from Arkansas who sold the “NanoCore RAT.” Like Grubbs, Huddleston initially pleaded not guilty to computer intrusion charges, arguing that he wasn’t responsible for how customers used his products.
That is, until prosecutors presented Skype logs showing that Huddleston routinely helped buyers work out how to use the tools to secretly compromise remote computers. Huddleston is currently serving a 33-month sentence after pleading guilty to selling the NanoCore RAT.
Update, Oct. 30, 9:42 a.m. ET: On Oct. 25, three days after this story was published, the sellers behind AgentTesla updated their site to say that they would be suspending sales of the product “for a while.” Here’s their full statement:
We stopped selling for a while. We will work on new measures for a few days. Some accounts will be banned in this process. Recently, Agent Tesla is being used by malicious people. Many of the detected accounts were banned indefinitely. After that, we will be more careful and take more stringent measures. No one can commit a crime by using Agent Tesla, we refuse. (Please check our terms: https://www.agenttesla-com/terms-of-use | https://www.agenttesla-com/eula [link hobbled]
No one has ever been helped for their illegal activities and will not be thereafter. If you are looking for a program for illegal use, you can leave it immediately.
I’d like to tell you about two changes:
1) We’ve decided we need to take some new measures. All files created thereafter will be saved in the database with sha256, MD5 checksums with your username. If the files reported by different people are detected, the account, IP address and HWID will be banned without question. We will follow some report and analyze sites up to date with tags. We’re doing this because people try to be famous by writing a blog post instead of sending us a file sample. If your file is in someone else’s hands, you’ve done SPREAD. You can not spread your file on the internet.
2) We remove functions that are exploited by malicious people and impossible to return.
Functions to remove:
• Webcam Capture,
• Anti AV,
• Process Killers,
• Downloader,
• Persistance




Good informative article 🙂
Well, sure. But that guy is in Turkey and not in U.S. like those last individuals that you mentioned. And I’m sure selling those Remote Access Trojans is just business-as-usual in Turkey. So good luck getting anywhere.
On the other hand, Discord can probably close his account if you contact them, Brian. The same may be true about the domain registrar for his site. (Provided it’s not registered in Turkey, or in Russia or a similar place.)
All in all, thanks for exposing those shady businesses!
It takes about 5 seconds to see that agenttesla-dot-com is registered by a Turkish registrar and shielded by a company registered to a warehouse address in Portland, OR. A quick googling of the same address shows it’s seemingly used for all kind of purposes, including as a drop for goods paid from hacked/stolen accounts.
Since when does the US of Agression care about jurisdiction? They’ve been arresting people, mainly Russians, all over the globe, mainly for computer related crime
Oh no!! Those poor innocent Russians that are being hunted by the US just for hacking,spreading malware,stealing bitcoins of people and exchanges,and and and..
Yes yes of course, it’s the US fault , the good Russians are in it for helping the world be a better place by mischief, I’m sure…
It would be helpful if the article included how to detect, avoid, and remove the Agent Tesla malware.
John, I am sure if you ask Brian nicely enough, he will come and remove if for you personally. He might even drop off your garbage for you on the way out.
I would make sure that your anti-virus is up-to-date and then run full system scan. If using Windows Defender on Windows 10 make sure to install all latest updates, then go to Start -> Settings -> Update & Security -> Windows Security -> Virus & Threat protection -> Run a new advanced scan -> select Full Scan and click “scan now.”
See my subsequent post to see how to mitigate the damage; but detecting the malware has become a losing game in most instances. Sometimes you can install something like Cryptoprevent to block the actual permissions of a Ransomware infection and prevent the damage, but if the malware is given the opportunity to install, (usually by deceitful popups, or a UAC prompt later in your session), the zero day identity will prevent any AM or AV solution from detecting the malware. You can have the best brand names on board and it still won’t detect it and remove it in time to prevent the damage. All you can to is be very aware of your desktop or cell phone behavior so that you don’t help the malware by installing it – providing it does not have administrative rights you have inadvertently given it.
The last time I purposely allowed the installation of malware on my honey pot literally damaged the operating system so badly I had to recover the image from backup to rid my machine of the “pox”. I did find that the only way I could find some of the malware was by booting to Kaspersky’s Rescue Disc 2018 (which is free to download and burn to a disc or record on USB), and remove it outside of normal boot mode that way. Usually by the time you put the disc in and it provides all the definitions, you may have luck finding the exploit and removing it. I can’t guarantee the bug hasn’t already corrupted your files by then. I have had to wait as long as 24 hours before it can find all the malware installed, providing you leave the machine offline between attempts. The malware will usually try to refresh its own code so that it can remain undetectable, so getting off line as soon as possible is required. However you will need at least an Ethernet connection to use the rescue disc while in the Linux environment provided by the disc.
Really the best thing to do is run any sensitive things you do on the internet through a bootable version of Linux, and avoid doing them on your main “surfing/leisure/etc” OS instance. VMs and sandboxing can help with that kind of thing too, but they’re not infallible. Particularly where a keylogger is involved.
Not that most people would be willing to do it, but a Raspberry Pi is cheap and perfect to use as a little banking box where you only use a thumbdrive Linux, and shut it down after every session.
I do not work for, or promote any software for anybody; but I have tested Rapport (IBM endpoint security) in the most popular three browsers, and as long as a website is designated under protection by Rapport, there is no way malware can help record keystrokes, video capture, or see an image of user ID entries while Rapport is in session on that site, that the user designates as under protection.
Powerful tools like this are going to be the future, because anti-malware/virus utilities just cannot catch all the miscreants out there. I can usually tell when I catch a bug on my honey pot – mostly by bad emails, but occasionally from clicking on advertisements or images at perfectly legitimate sites. I generally keep CCleaner running so malware cannot block its startup, and if I’m running as a standard account, all I have to do is close the browser and run CCleaner, and even undefined malware are dumped before they can fool the user into installing the malware by several tricks, like invoking the UAC when attempting to open another app since the bug was downloaded. The criminals have become very good at this kind of deception and social engineering; to trick the user into inadvertently installing the malware.
I use quad 9 DNS. IBM is a sponsor of quad 9, so I wonder if they employ the same database for domain filtering as Rapport.
I don’t know much about their web DNS, but I do know their blocking of the three main factors I mentioned does work. The malware would NOT be able to capture anything from the keyboard, video surveillance, or image capture from form entries on the protected site. They take over the browser from deep inside the system, and that makes people nervous, but I’ve never seen any problems from my clients (who most are indigent, and I work for free). A lot of today’s solutions work at the kernel level to subvert malware activity now.
I’ve also noticed when I’m helping people using an RDP utility, that I cannot see what is on the screen when they access a secured sight Rapport is protecting. If I’m trying to show them something, we have to turn it off to allow me to see what the client needs.
“as long as a website is designated under protection by Rapport, there is no way malware can help record keystrokes, video capture, or see an image of user ID entries while Rapport is in session on that site, that the user designates as under protection. ”
Wish they had a Linux Client
Hi JCitizen. Guess you’re a bit naïve. Trusteer Rapport does protect against most formgrabbers, though simply hijacking their trampoline makes it just as easy to grab forms with leaving Rapport running. False sense of security.
So, Turkey is US state now?
I don’t believe anyone suggested it was, including me. Plenty of people from outside the United States get arrested and extradited to the US for prosecution on cybercrimes that impact American citizens. In fact, it happened recently to a couple of guys who ran a no-report malware scanner called Scan4you. It’s worth noting that Agent Tesla’s license also bundled such a service.
This is why “Krebs” is one of my home pages. Thanks again for another great article Brian.
Correct, but the relationship between the US and Turkey is not that good at the moment. I think it might be a little more difficult than other countries they got hackers extradited from.
Same thing happened with Georgia.
The US state or the country?
Exactly.
Depending on what happens with the murdered journalist scandal, Turkey may end up being much closer to the US, and much more willing to extradite.
People seem to think in terms of black and white… as if this guy, being in Turkey, has nothing to do with US jurisdiction and law. But just as Russian hackers can be indicted/charged without being physically present for trial, so too can this person.
Being found guilty of US crimes, even without being caught or extradited to the US, still means a lot. Assets the pass through the US can be frozen and seized, other countries can similarly blacklist you from doing business too.
You can also end up on a travel watchlist, and if you do something dumb like, oh, travel to the UK, you can find yourself on a private flight to the US before you know it.
You will be watch list?? And so??
Watch list is joke.. Criminals dont care about any watchlist..
If they have to choose either starving or making money they choose the making money option.
When someone is commiting crime it means there is reasons why. So it means often the guy has nothing to lose or nothing to fear. Since if you got nothing then u got nothing to lose either.
Thats what kind of people those kind of people are
Tom, I tend to think those people are mentally ill with greed, to the point they have no empathy. These kinds of people would see someone get hit by a car, casually walk up, take their wallet and walk away while they lay dying. They aren’t hungry, or need money for medicine for their sick mother, these kind of people don’t love their mother or anyone else. They just look for opportunities to take from others. They should be exterminated.
I dont agree with you.
Those people might be nice people but this kind of things is just their way of making money.
But just think about it if you live in some poor country or some bad country.. You cant get the good job even you get job its not good enough to live like normal person.. Right?
So those kind of people are most dangerous for society.. They will commit crimes since they got nothing to lose, just think abput when soviet union collapsed the most hard core criminals released from prisons.. They traveled to west.. Same tjing 7with sicialians.. They was from hardcore conditions.
Western people has no idea how tough is to live in country where is strong mafia.. And goverment dont support you at all.
Those people who come from those countries they have no fears and nothing to lose, i seen those kind of people
They are brutal and hardcore.. Coz they been treated in bad way.. If you fighting with the monstrum you become one.
I think we need more love and caring about other people too only then the world can be better place.
.. And people should ask would you rather get stabbed kid napped tortured or we will take hit by cyber crimes.. Frauds scams.. If you take cyber crimes frauds away then those hard core criminals will do violant crimes.
Offcourse violance will be direct threat.. To most rich people.
So they rather live with scams frauds instead violant crimes.
People ask yourself do we want same life as in brazil?? People getting robbed day light.
So we need to do more good, usa instead of sending military troops in middle east to kill innocent people should use his power money and resources to go to russia south korea, africa brazil and fix the countries.. Bring some love and humanity.
Criminals are not afraid prisons.. For them its a vacation.
But why we punish… Some small Cyber criminal , but big drug cartells walking with suits.. And making investment companies. And funding start up projects..
Its hypocracy to punish one but not other one?
Coz they are too big?? Cant touch?? Are they special??
If they are special then dont forget the big guys who can just buy freedom and never police not gona touch them.. They made their business success same way, the criminal way is criimnal way.
So usa should go to around to world and clean up the real criminals who are in goverments and police.. Once those places are cleaned up then the small criminals will disapere..
Give people good wages and good jobs, stop stealing from people and criminal activity will be stopped.
Sounds like your making excuses for your own such activity, trying to justify it. Pure BS. 25 years ago I was so poor I lived outside for 3 years. I never even considered stealing. Are there lots of bad people in government – well duh, greedy people take what they can, and slightly smart greedy people will lead governments and companies – but don’t try and BS anyone about excuses to steal and think your not a bad person.
Bro, you literally said, in nearly the same breath, that these criminals are “nice guys” who, if not permitted to commit cyber crime, would become “violant (sic)”. So … which is it? Are they nice guys, as you say, or are they hardened criminals who will commit violence against people … as you also say. They can’t be both.
I think you need to spend a little time re-evaluating your position. Think it through completely, don’t stop when something feels good or right, keep pushing past those moments and see what you find. You’re very clearly not thinking very clearly, savvy?
I took it to mean that people who were once “nice”, law-abiding citizens took to a life of crime due to lack of opportunity to make a legal living. He makes some good points even if your seemingly unable to read between the lines and some broken English to see them.
Nope. He literally said they (meaning cybercriminals) were nice people who just happen to make their money in a not so nice way. He then suggested that if we stopped them from stealing from people via cyber means, they’d start doing it physically (along with stabbing, kidnapping and torture).
There’s a very apparent contradiction here – language barrier be damned.
Say my name.
“Heisenberg. You’re Heisenberg.”
Nonsense. Pretty much every account Ive read of people running these services, has them making 100’s of thousands doing so in a rather short amount of time. These are not poor people stealing to feed their families, these are people showing off their wealth and fancy cars they got through the proceeds of crime. And, we’ll see if they care that they can not travel to any country that has an extradition treaty with the US, or even some that dont(Maldives).
That’s a dangerous assumption & false stereotype John
There seems to be another black and white, over simplification going on here.
Laws don’t just exist as a deterrent. There will of course be criminals who wouldn’t care even with the death penalty.
By imposing sanctions against criminals in foreign countries (where they can travel, where their money can travel)… you limit their criminal enterprise significantly. It may or may not stop the criminal activity, but it mitigates the extend it will spread. It puts a higher cost of conducting that activity, and it increases the barrier to entry.
Mustafa’s Twitter account and YouTube page are still up w/ photos. The Facebook page however, is down.
The guy used bitcoins.
Bitcoins has no names its privacy transactions.
The guy should get just the good lawer and thats it.
They cant proof nothing.. He did not use his passport along with his actions online.
Guy can just say its all pointless and show me strong proof..
The guy means zero here. It’s the judge/juri that has to see the proof.
LMAO, bitcoin is not private at all. Every single transaction can be traced through the blockchain, thats what the blockchain is, a digital record of every transaction ever made and which wallets it went to. If he is caught with those wallets, every transaction that went into that wallet can be traced back to its source. Just because its anonymous doesnt mean its private.
Posts like these make it clear why so many of these guys get caught. It’s their own stupidity and warped sense of ethics. They believe this nonsense about not being able to be caught/prosecuted because they use Bitcoin.
Also the false narrative about people so poor they have NO other choice than to steal. Sorry, these aren’t reports about Jean Valjean stealing a bit of food to feed his family. These are about the systematic criminal activity. Anyone who resorts to stealing from/violating others, over time, is simply a criminal. The thing all of these cybercriminals have in common is this: They are scumbags.
But … but … he was so poor he was only able to buy a domain, spin up a website and have a computer to code with!
Interesting troll comments. I haven’t heard of this vatiant of a rat. But an interesting article.
I thought rats were in on the bios level of the ones. Even before the virus checker loads. I’m a geezer, and was in on the old card punch entry systems, by ibm, in the school, we had to load a rat to debug. So they had to hide them now? Interesting. And autoruns, which I hate, on a system level, durn. And win10 depends on autoruns. Even worse. DD.
Solid factual reporting as usual!
Thanks for the great read!
One minor correction though – “prices ranging from $15 to $69 per month depending on the desired features.” contradicts the screenshot where prices range from $15 a month to $69 per year (not per month)
Thanks, you’re right. Some of the models are monthly, some are multi-month or annually. I’ve updated the story.
This problem should fall at the feet of Microsoft. It’s far too easy for malware to be installed. There are far too many exploits. The operating system should be able to detect something as pervasive as the installation of an unauthorized RAT. Also, the exfiltration of large amounts of data should be something the operating system can detect and alert the user.
>The operating system should be able to detect something as pervasive as the installation of an unauthorized RAT.
It already does but most modern malware is purposely designed to avoid being detected and bypass any anti-malware measures already in place.
I disagree about it should fall at the feet of Microsoft for responsibility.
I disagree with your disagreement: if you’re going to write an OS, then make sure users can’t screw up the system, or each other. Windows from Day One was written as a non-connected, single user system. From then on, priority was given to flashy functionality, NOT security.
> if you’re going to write an OS, then make sure users can’t screw up the system, or each other
Then we’d go back to paper and pencil. There’s no operating system ever written that would withstand a determined and knowledgeable attack. Not the least because every X86 processor made since 1990 through today is vulnerable to some variation of Spectre and/or Meltdown.
Except that MS is quite well known for designing a system full of holes with seemingly little care put into security. An example of which would be the zero day just posted to twitter that affects a brand new system present only in Win10. While difficult to exploit, it is yet another example of a MS designed software package that doesnt do proper authentication. It would have been nice if MS put a little more effort into making their OS more secure, especially in years past.
Not to worry ! Microsoft is buying GitHub !
https://www.businessinsider.com/the-fastest-growing-programming-languages-according-to-the-facebook-for-programmers-2018-10
Microsoft will acquire GitHub for $7.5 billion, which has been seen as a smart move for the tech titan.
Bollocks! Microsoft spends more on Security R&D than nearly any company on earth. The reality is their success is the reason that hackers target them. I mean if you’re going to expend the effort to create a hack, do you want to target the 100’s of millions of users on Windows or the 1200 people running some obscure version of Linux on a raspberry Pie? you might have a point that they need to spend even more on security, but to state that they spend very little is just inaccurate
Reported the sales thread to the site administrator on the main site that he sells on. Was able to get his sales thread shut down. Hopefully that slows the amount of new users he gains using his malware.
Remember, Brian, the U.S. Federal government doesn’t like competition.
You’re thinking of the FSB.
Cool article and interesting discussion in comments:)
Brian, on a side note: https for your RSS feed seems broken.
I join in with the opinion that remote access tools are tools only.
It is inconsistent with a libertine government’s promotion of a common good to prosecute those who make, sell, or possess tools. It’s also inconsistent with such philosophy to prosecute based on sales techniques.
To illustrate: it is reasonable to prosecute a person who stabs a roommate with a screwdriver. There’s harm.
But it’s unjust to prosecute the screwdriver manufacturer or seller, even if he whispered “it’ll tear right through flesh” in his ear.
You’re right. Why is everyone talking about this kid as a cyber criminal? I don’t understand. Do governments who can’t catch cybercriminals want to put the software developers in jail? I think the next generation of journalists will be software developers. Make room for developers in jails.
It is not simply a remote access tool. Its very design is for malicious intent.
It is closer to building a screwdriver that is sharpened to be better at stabbing than driving screws… and is made of non-metal composite to evade metal detectors.
And also includes finger holds.
Sure, it could be still be used as a benign screw driver… but the law is not supposed to be fooled by such tactics.
Let’s assume for a moment that a remote access tool was not a blunt tool, but more like a rifle, a bomb, or a sword.
Call it a weapon.
Call it an explosive.
Call it a collectible.
Whatever you wish to call it, it remains unjust to prosecute based on how something looks or its potential for danger.
It’s unjust of a government to treat its citizenry as incapable of making responsible choices through prohibitions.
And it is unjust to prosecute the seller, who caused no intentional harm, but ignore the buyers who actually caused harm by installing this software.
I can agree to that. Making weapons should not be a crime.
But AFTER making the weapon… providing direct customer support and assistance to someone who is obviously using it for illegal purposes… is aiding and abetting a criminal.
“..begins instructing customers on how to install the product in ways that are arguably deceptive (such as through the use of software exploits, spam or disguising the tool as another program), the proprietor has crossed a legal line and can be criminally prosecuted under computer misuse laws.”
Joe,
I don’t know if you’ll see this, but if you do, consider this question: what separates helping a sinner from helping a saint?
The answer: nothing. They’re all worthy of help.
Therefore, it unjust for government to punish those who help sinners.
Still checking the thread occasionally.
I do agree with you, in general. Creating tools in itself should be legal as you say.
In this case, with these specifics, there are details which show he is NOT agnostic between sinners and saints. It is not like his help can be used either way here.
He is helping with full knowledge and awareness that the tactics being used, can only be nefarious. Saints don’t try to be so sneaky.
Response read.
It doesn’t suit you. You’re pointing a young man on target without any proof.
First: You sent a message, but you published it without confirmation. Is Mustafa really Agent Tesla? You didn’t prove it. You said “was registered in 2014 in Antalya, Turkey named Mustafa can Ozaydin”. We are living 2018 right? Did you checked for today?
Second: Why does everyone talk about this kid as a cyber criminal? No evidence has been submitted that he committed a crime. If you already have evidence, you can go to the prosecutor’s office instead of writing the blog. Developing a software and selling it for profit is not a crime. You will be guilty if you help criminals knowingly and willingly. I don’t see any evidence that this kid helped criminals. Taylor Huddleston wasn’t punished for selling NanoCore only. Taylor Huddleston was hosting a lot of malware with NetSeal. Taylor Huddleston was alleged to have a conversation with criminals. So he knew who committed what crime.
Third: You said “…is replete with instances of support personnel instructing users on ways to evade antivirus software detection, use software vulnerabilities to deploy the product, and secretly bundle the program inside of other file types, such as images, text, audio and even Microsoft Office files.” Exploids are not only used to attack people. Maybe you’re right, but if it is replete with instances, why didn’t you share any instances?
In summary, you should remove Mustafa’s name and photos from this article. We can’t target a young man here. You’re not a prosecutor or a judge. As a respected writer, I expect you to respect people’s privacy and rights.
It suits Mr Krebs just fine. He’s accurately uncovered many black hat hackers using the same methodology, and sometimes with less evidence.
Also, Krebs is not putting him on trial or convicting him… so he is not bound to a preponderance of evidence or beyond reasonable doubt.
There is enough evidence to at least put his name out there. And I am sure he has also given this info to his contacts in law enforcement.