Sources tell KrebsOnSecurity that Microsoft Corp. is slated to release a software update on Tuesday to fix an extraordinarily serious security vulnerability in a core cryptographic component present in all versions of Windows. Those sources say Microsoft has quietly shipped a patch for the bug to branches of the U.S. military and to other high-value customers/targets that manage key Internet infrastructure, and that those organizations have been asked to sign agreements preventing them from disclosing details of the flaw prior to Jan. 14, the first Patch Tuesday of 2020.
According to sources, the vulnerability in question resides in a Windows component known as crypt32.dll, a Windows module that Microsoft says handles “certificate and cryptographic messaging functions in the CryptoAPI.” The Microsoft CryptoAPI provides services that enable developers to secure Windows-based applications using cryptography, and includes functionality for encrypting and decrypting data using digital certificates.
A critical vulnerability in this Windows component could have wide-ranging security implications for a number of important Windows functions, including authentication on Windows desktops and servers, the protection of sensitive data handled by Microsoft’s Internet Explorer/Edge browsers, as well as a number of third-party applications and tools.
Equally concerning, a flaw in crypt32.dll might also be abused to spoof the digital signature tied to a specific piece of software. Such a weakness could be exploited by attackers to make malware appear to be a benign program that was produced and signed by a legitimate software company.
This component was introduced into Windows more than 20 years ago — back in Windows NT 4.0. Consequently, all versions of Windows are likely affected (including Windows XP, which is no longer being supported with patches from Microsoft).
Microsoft has not yet responded to requests for comment. However, KrebsOnSecurity has heard rumblings from several sources over the past 48 hours that this Patch Tuesday (tomorrow) will include a doozy of an update that will need to be addressed immediately by all organizations running Windows.
Update 7:49 p.m. ET: Microsoft responded, saying that it does not discuss the details of reported vulnerabilities before an update is available. The company also said it does “not release production-ready updates ahead of regular Update Tuesday schedule. “Through our Security Update Validation Program (SUVP), we release advance versions of our updates for the purpose of validation and interoperability testing in lab environments,” Microsoft said in a written statement. “Participants in this program are contractually disallowed from applying the fix to any system outside of this purpose and may not apply it to production infrastructure.”
Original story:
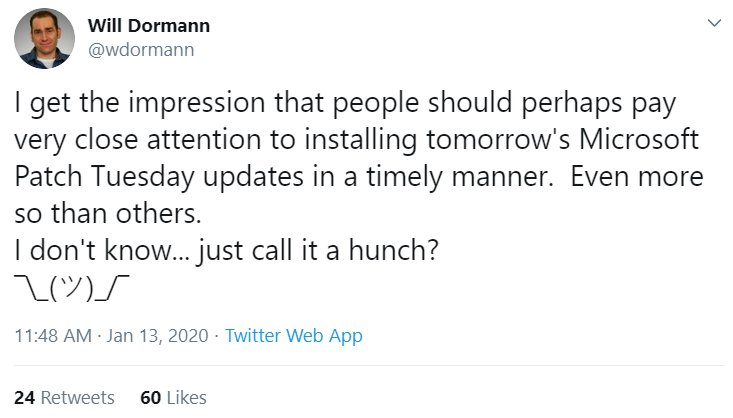
Will Dormann, a security researcher who authors many of the vulnerability reports for the CERT Coordination Center (CERT-CC), tweeted today that “people should perhaps pay very close attention to installing tomorrow’s Microsoft Patch Tuesday updates in a timely manner. Even more so than others. I don’t know…just call it a hunch?” Dormann declined to elaborate on that teaser.
It could be that the timing and topic here (cryptography) is nothing more than a coincidence, but KrebsOnSecurity today received a heads up from the U.S. National Security Agency (NSA) stating that NSA’s Director of Cybersecurity Anne Neuberger is slated to host a call on Jan. 14 with the news media that “will provide advanced notification of a current NSA cybersecurity issue.”
The NSA’s public affairs folks did not respond to requests for more information on the nature or purpose of the discussion. The invitation from the agency said only that the call “reflects NSA’s efforts to enhance dialogue with industry partners regarding its work in the cybersecurity domain.”
Stay tuned for tomorrow’s coverage of Patch Tuesday and possibly more information on this particular vulnerability.
Update, Jan. 14, 9:20 a.m. ET: The NSA’s Neuberger said in a media call this morning that the agency did indeed report this vulnerability to Microsoft, and that this was the first time Microsoft will have credited NSA for reporting a security flaw. Neuberger said NSA researchers discovered the bug in their own research, and that Microsoft’s advisory later today will state that Microsoft has seen no active exploitation of it yet.
According to the NSA, the problem exists in Windows 10 and Windows Server 2016. Asked why the NSA was focusing on this particular vulnerability, Neuberger said the concern was that it “makes trust vulnerable.” The agency declined to say when it discovered the flaw, and that it would wait until Microsoft releases a patch for it later today before discussing further details of the vulnerability.
Update, 1:47 p.m. ET: Microsoft has released updates for this flaw (CVE-2020-0601). Their advisory is here. The NSA’s writeup (PDF) includes quite a bit more detail, as does the advisory from CERT.




As of this moment, a “January 2020” search of the Microsoft Update Catalog shows only 4 updates to the Malicious Software Removal Tool, two each for Windows 10 and Windows 7.
search the catalog for “2020-01” not for “January 2020”
Microsoft changed the naming format starting with 2017-05 so that it’s easier to sort strings and updates.
Mixed alphabetic + numerical sorting was a headache when managing WSUS / SCCM updates, it’s MUCH easier with the YYYY-MM format.
imho the real “WTF ?!!” bug there is the fact that the Malicious Software Removal Tool still uses the old pre-2017 naming format.
Thanks! Info only good for this month, but better late than never! It’s a small, cold comfort when Redmond does even a small thing rationally.
See if your PC floats and buy a Mac.
Better yet, keep your Windows machine, wipe it and install Linux.
Old jokes are old.
Don’t play stupid games, and you are vastly more likely not to win stupid prizes. Not this specific instance, but most are entirely user preventable. No operating system change will fix that.
Some other guys found the curve parameters so we had to plug the plug. It was great while it lasted!
The age of the vulerability suggests win 8 could also be affected? There is no update for win 8.
From the CERT bulletin: “Windows 8.1 and prior, as well as the Server 2012 R2 and prior counterparts, do not support ECC keys with parameters. For this reason, such certificates that attempt to exploit this vulnerability are inherently untrusted by older Windows versions.”
Windows is a big target, no doubt its full of old code and has plenty of potential for exploiting holes still not discovered. Mac’s are safer purely on their weak user numbers, because Apple is terrible at pushing out updates in a timely fashion. I would not want to depend on Apple to fix a major security issue with Mac OS or IOS very quickly. Honestly if you really are concerned about security install Linux desktop OS, or possibly get a Chromebook. Both have relatively minuscule numbers for users and probably are the least attractive for bad actors.
Wowza, somebody admitting that attackers target systems based on their share of the market, rather than because their “security sucks”
John, take a moment of personal stock here. You’re giving security advice to the world consisting of generalizing based on user base. Nothing else. (“No doubt. Honestly.”) Everyone knows that part. It’s not useful in reality. There is no predicting which platform “is due” for a major flaw discovery or abuse in the wild. It doesn’t help even as a guess-essment. Nobody is going to move platforms if they weren’t already going to do so, see : “Year of Linux on the Desktop” since what, 1998?
“Bad actors” are on every platform. “honestly” “no doubt”
https://www.tomsguide.com/us/chrome-extension-security-problems,news-26082.html
Windows comes with autoplay: A feature that automatically starts executable files just becaise they are in a memory stick you happen to plug into your system. If a piece of hardware yiu buy contains a virtual embedded memory stick Windows is wilking to install driverd from there and by default Windows doesn’t show filename extensions but the file’s icon that can be set to something like the PDF logo if the file wants. My personal guess would be that in many cases decision makers have decided against security if that would mean gaining a bit of usability.
@ Jingleheimer S
But I think John S has a legitimate point in that if your using Linux (desktop/laptop) vs Windows/Android/iOS/Apple(desktop/laptop), which one is the all-around safest in the real world?
I think it’s safe to say Linux desktop is since I have heard there is barely any viruses for Linux to the point they are largely a non-issue so far. hell, many say you don’t even need anti-virus software and the like for Linux, which says a lot. so while I realize one could still be vulnerable on Linux from Phishing scams, since those are not OS specific, I think the common person is generally going to be safer browsing random websites on Linux than they would be on Windows simply because they are much less likely to get a virus on Linux vs Windows etc and as a added bonus, you ain’t got to worry about someone installing a random .exe or other shady files on accident simply because they won’t work on Linux by default. so Linux sort of stops those more computer illiterate types from screwing themselves by running suspect programs on their computer since dang near all of those programs will target Windows.
so as long as they keep their browser up to date on Linux, they should be generally quite safe online. I would also suggest people run Firejail (a sandboxing program) on their Firefox/Chrome browsers on Linux as it just makes one that much safer online as even if one got hit with say a drive-by download, it would likely be stopped by the Firejail sandboxing program since that really limits what can be accessed in the Home folder on Linux.
Security through obscurity shouldn’t be the reason that “Linux is more safe”. It’s just the same as when people have SSH running on an obscure port other than 22. Is it harder to find? Not really, a quick port scan can do this in seconds/minutes. Is it just as vulnerable even though it’s running on a different port? You betcha.
The same can be said here. Just by a quick CVE search, I found 600+ vulnerabilities in the Linux kernel alone. All of which have at least a base score of 7. Not to mention, everyone seems to quickly forget Shellshock — which is still seen today.
The scope of attacks are much, much different between Windows and Linux. I think this is what you’re failing to realize. Windows and Linux use different services, which means the scope of attacks or vulnerabilities are going to be different between the two. No OS is more secure than another just because less people use it.
Ref:
https://www.cvedetails.com/vulnerability-list/vendor_id-33/product_id-47/cvssscoremin-7/cvssscoremax-7.99/Linux-Linux-Kernel.html
“which one is the all-around safest in the real world?”
THE PROBLEM WITH THIS QUESTION is it implies everyone uses their OS in the same way. That’s unrealistic in every direction.
Every core OS is always going to have xyz vulns. Will you discover and be impacted by them personally? Most never will. What criteria is the most weighted, number of bugs, severity of bugs, ease or triviality in exploiting of bugs? And then on top of that, NOBODY uses JUST the OS. Everyone loads 3rd party on top.
If you go to the Chrome store and browse THEIR CULTIVATED APP COLLECTION, you can STILL get a nasty malware infection. Same with any linux distro, you can find malware inserted into long-trusted packages everyone relies on – constantly it happens.
The point is this code-signing bug will NOT be the most serious flaw discovered in Windows this year, guaranteed, nor will it be the most serious or abused flaw generally among any and all OS’s.
The idea of “mac is better because there are fewer users to target” and that entire logic line is just vague bullsh!t guesswork in lieu of having any actual concept of the underpinnings of the platforms and the general usage cases of the vast masses. In reality, trying to calculate “which is more secure” is equivalent to “is this dress blue or gold or black?” It’s in the eye of the beholder. It’s almost entirely meaningless beyound that really in terms of ACTUAL security.
@ Jingleheimber S
I still feel confident in saying Linux(desktop) is safer for the common person online than Windows is simply because a lot of threats that effect Windows users, do not effect Linux(desktop) users. so given the real world, the attack surface is more limited currently.
or look at it this way… get a bunch of random average people and give them a Windows computer and a Linux (desktop) computer and have them start using it however they want. those who are a bit software installation happy (probably the types more likely to get hit with a virus etc) will likely be pretty well protected simply because a lot of crap they attempt to install simply won’t work on Linux. so it sort of protects them from themselves in that regard.
do you honestly disagree with this? ; if so, I don’t see how one can given there is less nasty programs and the like that effects Linux(desktop) than Windows. there is just less to attack Linux(desktop) with than there is with Windows given current real world use. maybe that will change years from now, who knows, but until then I think a average person is noticeably safer online using Linux than Windows for browsing the web etc, especially those more computer illiterate type.
“Same with any linux distro, you can find malware inserted into long-trusted packages everyone relies on – constantly it happens.”
Constantly on Linux(desktop)? ; I doubt that happens much when it comes to software available through the Linux OS’s official repositories for any given Linux(desktop) distro. venturing outside of those the risk would increase some though, but probably not much given people largely don’t attack Linux desktop users as it seems only about 2% of the market share is Linux(desktop) where as Windows has something like 87%.
I am not saying Linux is immune to viruses and the like, as if it was more popular I suspect it would be more attacked in general and all, but as is, one is much less likely to get a virus (or the like) on Linux desktop than they would on a typical Windows computer and it’s likely to stay this way for the foreseeable future simply because not enough average people use Linux so the cyber criminals don’t bother with it and I suspect your typical Linux user is a bit more tech savvy than a average Windows user.
Actually, Linux is huge in the business world and has been a target as well. As Snowden revealed years ago, all of these major tech platforms have vulnerabilities, some purposeful. If it’s connected to the internet or has WIFI or allows software to be installed, it can be exploited.
John S, it is funny you say that go to Linux. Surely you are fully aware the backbone of the MacOS is same as Linux / Unix. So nothing is really that different being on Linux/Unix or Mac OS. They are almost on the same boat in contrast to being on Microsoft. Surely if people would want to infiltrate the Linux/Unix/Mac OS, they would see vulnerabilities as well. It was only reported and done as much as you said, the Windows consumer is bigger, probably easier and worth the effort over others.
Linux definitely has a less attractive user footprint, but I can tell you from managing a next gen firewall for years that the exploit attempts I see are ten to one in favor of open source.
Complain about Windows all you want, but thems the facts, at least in my neck of the woods.
Note: Microsoft has been known, like understatement & no brainer like it’s somehow the norm – normal but having $ sold out nevertheless – carelessly themselves but any & all user’s per / via giving the any & all known Microsoft (as it’s not just limited to them, but it’s human nature centuries – TO DATE), Microsoft giving the known vulnerabilities of it’s product’s let’s say, TO the security agencies (for their tool box) therefore so they then they in turn can be like WHAT? Flies on human / animal solid waste?
Huh, lost in transition, misc else nevertheless, humanity as a whole (itself) NO still ‘GETS’ what this is & what it has been for 70 centuries – to date, Holy War against God that Satan devil solely started, humanity has NOT changed, I’m not stupid to just give my email address to public since I have Holy info intel to put out like those before us – centuries ago BUT, huh, you humanity REALLY NEED to get a clue.
Had to have known from your incoherent phrasing that you’d have to be a religious nut.
You really need to get a psychologist.
Just a reminder that you’re preaching incoherent religious nonsense on an article about a Windows operating system security flaw. I have no clue why you’d be doing that but it seems as if you don’t know where you are. Hope this helps. Good luck in your holy battles.
Hey guys, as a flesh and blood religious nut, I’m 95% confident this is a bot. I bet it read the title and saw ‘cryptic’ in the headline and thought this was a good place to post. Tacking about any big name to “sell out to the government” is about as standard conspiracy theory as you can get, so it’d be easy to see “Microsoft” and “NSA” as keywords filling in this bot’s Mad Libs style program. Heck, the guy underneath this post’s parent is wondering if the NSA was using this vulnerability until someone else caught wind of it.
Give us religious nuts some credibility. We can form coherent sentences. If I’m right, this bot just passed an interesting Turing Test.
Commmon now, if NSA “found” this patch and reported it… I simply wonder if it was exploited by them or other agencies. Some one caught wind of its use and “now” they report this super huge vuln. I wonder how many other patches could have been done this way. Or, simply put, how many “patches” are created to allow agencies to fly into systems, and they are silently closed or announced a few months…or years later?!
thats what i wonder…The Imitation Game
It’s very rare, the feds have issued an emergency directive for federal government agencies to patch.
Their guidance, must be patched within 10 days.
Wonder if that’s arbitrary, or if NSA knows something about someone working on it.
https://cyber.dhs.gov/ed/20-02/
I suggest adding this link to the story.
The NSA developed its own ECC suites (Suite B and CNSA) that are likely used throughout US government systems. This is an exponentially bigger problem for them compared to a government or organization that isn’t using ECC suites for their in-house trust certificates.
Is Windows 10 vulnerable to this problem? What is needed to do?
Hi
To be clear , is it that a threat actor compromises an app and “re-signs” it using this exploit then Windows end points connecting to the exploited app are at risk because they will trust the app and anything the threat actor includes in it.
Just want to clarify the statement ” the attacker would need to compromise in another way to run the exploit” this is not true for the unpatched end point. Correct ?
Microsoft needs Cryptowall criminals to write their software
I installed all the new Win 7 updates earlier, and now it keeps taking 10 minutes to boot and the system keep locking up. I had to do a System Restore in order to get it working again.
Is there patch Windows 10 build 1607? I was told MS did not create one for this build.
@ HAS
You should not still be using Windows 10 1607 at this point as Microsoft dropped support of it April 2018. Upgrade to say Windows 10 1909 now.
I think Microsoft supports each new version they release for 18 months.
Sorry – late to the game, been under a rock.
Fascinating that there are 140 plus posts most focused on which is the better or more secure or less attacked OS when that does NOT play a role in the majority of incidents and breaches from 2019 (or prior years).
As per 2019 Verizon DBIR – https://enterprise.verizon.com/resources/reports/dbir/2019/results-and-analysis/
Heading “Threat action varieties”
Exploit Vuln – does not appear in the in the top 15 for Incidents and is number 14 for BREACHES.
Heading “HACKING”
“At most, six percent of breaches in our data set this year involved exploiting vulnerabilities.”
Patch the OS
Run your risk assessment
Map your company to the proper vertical
Build your attack vectors
Use something like MITRE ATTACK and RedTeam Exercises
Focus on largest risk reduction areas