Patch comes amid active exploitation by ransomware gangs
Networking hardware vendor Zyxel today released an update to fix a critical flaw in many of its network attached storage (NAS) devices that can be used to remotely commandeer them. The patch comes 12 days after KrebsOnSecurity alerted the company that precise instructions for exploiting the vulnerability were being sold for $20,000 in the cybercrime underground.
Based in Taiwan, Zyxel Communications Corp. (a.k.a “ZyXEL”) is a maker of networking devices, including Wi-Fi routers, NAS products and hardware firewalls. The company has roughly 1,500 employees and boasts some 100 million devices deployed worldwide. While in many respects the class of vulnerability addressed in this story is depressingly common among Internet of Things (IoT) devices, the flaw is notable because it has attracted the interest of groups specializing in deploying ransomware at scale.
KrebsOnSecurity first learned about the flaw on Feb. 12 from Alex Holden, founder of Milwaukee-based security firm Hold Security. Holden had obtained a copy of the exploit code, which allows an attacker to remotely compromise more than a dozen types of Zyxel NAS products remotely without any help from users.
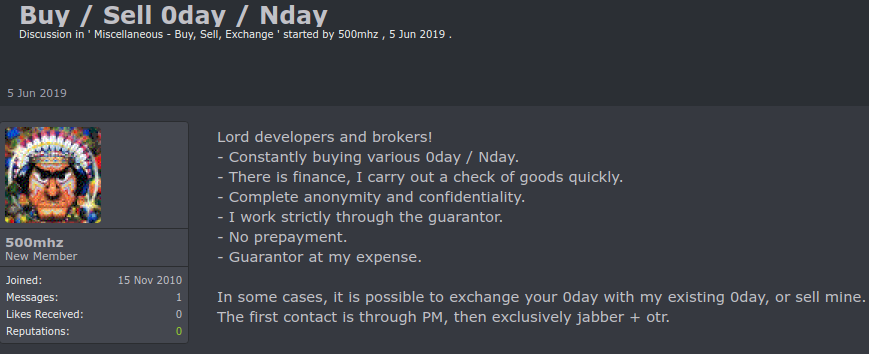
Holden said the seller of the exploit code — a ne’er-do-well who goes by the nickname “500mhz” –is known for being reliable and thorough in his sales of 0day exploits (a.k.a. “zero-days,” these are vulnerabilities in hardware or software products that vendors first learn about when exploit code and/or active exploitation shows up online).
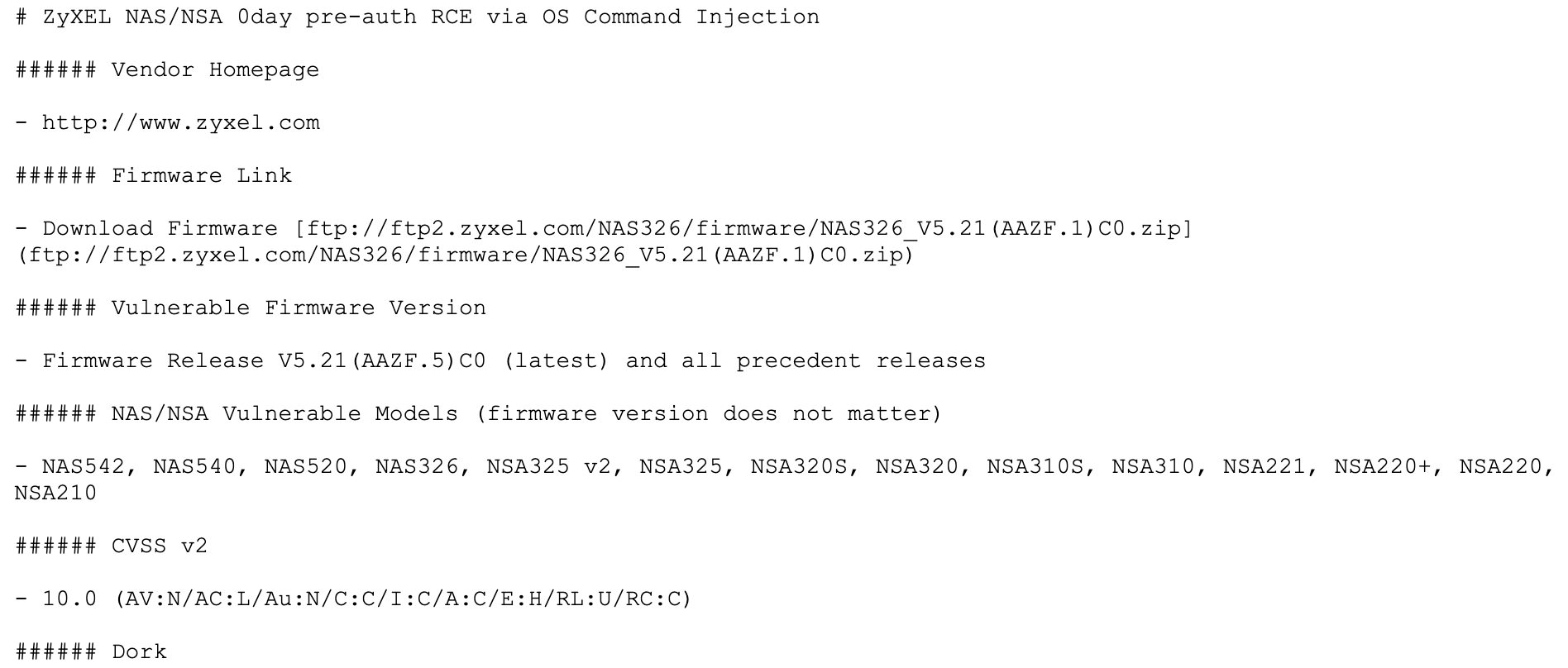
For example, this and previous zero-days for sale by 500mhz came with exhaustive documentation detailing virtually everything about the flaw, including any preconditions needed to exploit it, step-by-step configuration instructions, tips on how to remove traces of exploitation, and example search links that could be used to readily locate thousands of vulnerable devices.
500mhz’s profile on one cybercrime forum states that he is constantly buying, selling and trading various 0day vulnerabilities.
“In some cases, it is possible to exchange your 0day with my existing 0day, or sell mine,” his Russian-language profile reads.
PARTIAL PATCH
KrebsOnSecurity first contacted Zyxel on Feb. 12, sharing a copy of the exploit code and description of the vulnerability. When four days elapsed without any response from the vendor to notifications sent via multiple methods, this author shared the same information with vulnerability analysts at the U.S. Department of Homeland Security (DHS) and with the CERT Coordination Center (CERT/CC), a partnership between DHS and Carnegie Mellon University.
Less than 24 hours after contacting DHS and CERT/CC, KrebsOnSecurity heard back from Zyxel, which thanked KrebsOnSecurity for the alert without acknowledging its failure to respond until they were sent the same information by others.
“Thanks for flagging,” Zyxel’s team wrote on Feb. 17. “We’ve just received an alert of the same vulnerabilities from US-CERT over the weekend, and we’re now in the process of investigating. Still, we heartily appreciate you bringing it to our attention.”
Earlier today, Zyxel sent a message saying it had published a security advisory and patch for the zero-day exploit in some of its affected products. The vulnerable devices include NAS542, NAS540, NAS520, NAS326, NSA325 v2, NSA325, NSA320S, NSA320, NSA310S, NSA310, NSA221, NSA220+, NSA220, and NSA210. The flaw is designated as CVE-2020-9054.
However, many of these devices are no longer supported by Zyxel and will not be patched. Zyxel’s advice for those users is simply “do not leave the product directly exposed to the internet.”
“If possible, connect it to a security router or firewall for additional protection,” the advisory reads.
Holden said given the simplicity of the exploit — which allows an attacker to seize remote control over an affected device by injecting just two characters to the username field of the login panel for Zyxel NAS devices — it’s likely other Zyxel products may have related vulnerabilities.
“Considering how stupid this exploit is, I’m guessing this is not the only one of its class in their products,” he said.
CERT’s advisory on the flaw rates it at a “10” — its most severe. The advisory includes additional mitigation instructions, including a proof-of-concept exploit that has the ability to power down affected Zyxel devices.
EMOTET GOES IOT?
Holden said recent activity suggests that attackers known for deploying ransomware have been actively working to test the zero-day for use against targets. Specifically, Holden said the exploit is now being used by a group of bad guys who are seeking to fold the exploit into Emotet, a powerful malware tool typically disseminated via spam that is frequently used to seed a target with malcode which holds the victim’s files for ransom.
Holden said 500mhz was offering the Zyxel exploit for $20,000 on cybercrime forums, although it’s not clear whether the Emotet gang paid anywhere near that amount for access to the code. Still, he said, ransomware gangs could easily earn back their investment by successfully compromising a single target with this simple but highly reliable exploit.
“From the attacker’s standpoint simple is better,” he said. “The commercial value of this exploit was set at $20,000, but that’s not much when you consider a ransomware gang could easily make that money back and then some in a short period of time.”
Emotet’s nascent forays into IoT come amid other disturbing developments for the prolific exploitation platform. Earlier this month, security researchers noted that Emotet now has the capability to spread in a worm-like fashion via Wi-Fi networks.
“To me, a 0day exploit in Zyxel is not as scary as who bought it,” he said. “The Emotet guys have been historically targeting PCs, laptops and servers, but their venture now into IoT devices is very disturbing.”
DISCLOSURE DEBATE
This experience was a good reminder that vulnerability reporting and remediation often can be a frustrating process. Twelve days turnaround is fairly quick as these things go, although probably not quick enough for customers using products affected by zero-day vulnerabilities.
It can be tempting when one is not getting any response from a vendor to simply publish an alert detailing one’s findings, and the pressure to do so certainly increases when there is a zero-day flaw involved. KrebsOnSecurity ultimately opted not to do that for three reasons.
Firstly, at the time there was no evidence that the flaws were being actively exploited, and because the vendor had assured DHS and CERT-CC that it would soon have a patch available.
Perhaps most importantly, public disclosure of an unpatched flaw could well have made a bad situation worse, without offering affected users much in the way of information about how to protect their systems.
Many hardware and software vendors include a link from their home pages to /security.txt, which is a proposed standard for allowing security researchers to quickly identify the points of contact at vendors when seeking to report security vulnerabilities. But even vendors who haven’t yet adopted this standard (Zyxel has not) usually will respond to reports at security@[vendordomainhere]; indeed, Zyxel encourages researchers to forward any such reports to security@zyxel.com.tw.
On the subject of full disclosure, I should note that while this author is listed by Hold Security’s site as an advisor, KrebsOnSecurity has never sought nor received remuneration of any kind in connection with this role.




Another great article, keep them coming !
How does Emotet affect linux-based personal and corporate entities?
AFAIK, Emotet targets just Windows-based platforms. But it is not unusual for ransomware gangs to exploit flaws in non-Windows based systems as a way to get a foot in the door. This Zyxel flaw would fit that description.
Oh, and thanks for contacting CERT/CC!
Nothing hurts more than losing your data.
We’ve all been there.
Months and years worth of documents, pictures, and video vanished in thin air. seku.ac.ke
The last time it happened with me, I said to myself, never again! That is when I started looking for a NAS (Network attached storage) which can backup my data regularly.
If I understand the article correctly, the bad guys will probably get their money’s worth, since many of the NAS are no longer supported by the company.
As many reading here know; many of the potential victims probably will never know their NAS is unsupported until they get hit. That is the cost of being ignorant and unprepared. I am rather surprised this venerable company had such an obviously stupid flaw; I thought they were better than that. They also shouldn’t have had to wait until officials contacted them – just whiff of danger should have been enough to react ASAP.
Why should they react? Reacting costs money. Not reacting, and getting their customer’s data stolen doesn’t seem to hurt other companies. Look at Target, Equifax, Home Depot, and countless others. How many have gone out of business? How many executives have lost their golden parachute or better, done jail time?
What do you expect when consumers keep going back? Execs aren’t gonna do anything if the money keeps rolling in, and that starts at the consumers. So blame idiot consumers who continue to use their services. If the stock prices took permeant hits you’d see change, but now you see a 2-3% drop then within a few week it’s brushed off and up again.
I dont think its the right way to look at the real problem when you put them all together.
People forget and doesnt really know about the geo-political rules from the area.
“Why should they react? Reacting costs money. Not reacting, and getting their customer’s data stolen doesn’t seem to hurt other companies. ” <– Canadians are listed as "over-confident" with their actual "setup", and because of that we are just few caring about users data and the network quality.
As CIRA reveal from a survey that only 7% IT managers reported 50 or little more attacks per year.
I had to left my old job because fighting with Senior Tech (paid as 10x times more than me) that wasnt using any "automation and good monitoring system" like we all can see on any average IT company living elsewhere in this world.
in 2017 , i was reporting to Videotron (local ISP) a bug ( https://twitter.com/vraiexpert/status/840119544295251968 ) with Zyxel that lead me in finding a botnet residing in over 50 000+ on the same ISP (botnet was related to Antminer pool)
They never really answered something positive and it tooks at least over a year before they decide to replace the model.
Same case with Cogeco (another local ISP) https://twitter.com/vraiexpert/status/1223756669836021760 | | It was my first meet with an Arris interface , so after few googles search i found old bugs explaining the very powerfull "one day password" still able to exploit with just a small update on the last generator you can still find on the arris website. Requesting Shodan trying to find DOCSIS3 UTM in my local area open i noticed by default Cogeco installing remote-open modem to customers (not aware of that). From the DOCSIS you can easily find default subnet config for the modem and the one for Arris.
They already lost over 60millions+ in court this year , and they are using a new internal CRM that came with a lots of bugs.. As result they lost too many customers. I still didnt received any answers from them, and they did the samething over 8 years ago, D-Link warned them about an RCE abused on the D-Link and by ignoring them was resulting as today they got 80% of their IPS still list in most popular RBL .
Equifax to pay $700m in fine and in the last weeks they now know the breach was made by Chinese hackers well-known. Those hackers today know for sure more things about equifax customers.
As for 2020 Canada is already listed as TOP 3 country receiving the most expensive attacks. (And the year is just starting).
Reading from a good CIRA survey , you can easily understand and notice that IT have so much to do.
looked at organizations with up to 500 employees. That said, we do understand that in the Canadian context an organization with more than 250 employees is actually pretty large. Importantly, these companies also serve, supply and partner with individuals and larger organizations. They may not have the resources to deploy complex security stacks and this makes them easier targets. As we saw way back in 2014 with the attack on Target that leveraged the HVAC system to get millions of credit card numbers, any sized business can be a conduit into hacking a larger one.
The attention around cybersecurity breaches is only going to grow thanks to the upcoming changes to privacy regulations in Canada. It is estimated that70 per cent of data breaches happen against companies with fewer than 100 employees which means that a problem that once only kept IT managers of large corporations up at night, will now be causing insomnia for many more.
And why do hackers want the information that you are in control of? Simply put, personal data is valuable. Personal information is being sold on the dark web for as little as $5 for a credit card number, $30 for an entire identity, or up to $1,000 for medical records. Do you still trust those older computers with the open USB ports that sit unattended in the little waiting rooms at your doctor’s office? There are hundreds of examples of low hanging fruit for hackers in everyday interactions Canadians have with small businesses every day. All these situations are potential breaches and many businesses don’t even know the risks.
If it was such an “obviously stupid flaw,” why didn’t you or any other security or computer science professional find it first?
And what makes you believe it’s a flaw, rather than a backdoor?
/not sarcasm
@Readership1, a security researcher *did* find the flaw and *did* report it to Brian, who *did* do the right thing with the information.
Even to find stupid-simple flaws, somebody has to probe and evaluate the results. Finding this stuff is part science, part art-form.
And here’s a blog post from way back in 2014 about proper disclosure.
https://www.dgregscott.com/right-way-deal-security-vulnerability-disclosures/
Scott,
You may have missed the first paragraphs of the article. The exploit was being actively sold, then Hold caught wind and alerted Krebs and the manufacturer.
The hackers found it first, not professionals.
Well, okay, fair enough. I went back and re-read it. You’re right about the sequence of events.
But if we’re assigning blame, let’s put it where it belongs, with the people who built a device apparently with obvious flaws. And with customers who directly expose a NAS device to the internet. Makes you wonder what kind of wackybacky those customers are smokin’. Let’s not fault the researcher (Holden) and the reporter (Brian) who exposed this flaw.
What’s important for our discussion is, after a device is in the field, it’s just not realistic to expect good guy security researchers, or security reporters, or any outsider to find every flaw before bad guys find it. If you’re attacking the apparently stupid-simple nature of the flaw, well, this is hardly the first time a device with obvious flaws has been in the field. And whether it’s a backdoor or not is irrelevant.
If you look back at history, pretty much vendor goes through a period of denial when somebody tells them about a flaw in their product. I’m not defending that reaction – in fact, it still makes me mad – I’m just saying Zyxel’s reaction in this case is nothing new.
There are always three players in every scenario like this – good guys, bad guys, victims, and the clueless. Well, okay, four players. In this case, the good guys all behaved properly. We don’t know the bad guys and victims, and Zyxel was clueless.
But c’mon – if you put your NAS device on the internet for the whole world to probe, you’re pretty much begging for trouble.
– Greg
This exploit seems to be a developer backdoor that shipped with the device’s production code. I know that developer backdoors are common in China. I presume that Taiwanese developers have the same bad habit.
Until the developer culture in China changes, I figure that every hardware device made in China has at least one developer backdoor that was used for unit testing and ultimately shipped in the production device.
I would have thought Taiwan would have a great enough political difference from main land China, that security would be more important – especially since they used to be mortal enemies.
Maybe I’m reading too much into it, but Zyxell used to be regarded as a security conscious company.
Zyxel products are largely developed in Taiwan. Not sure the country of manufacturer, as most things are contracted elsewhere regardless of company.
The NAS devices are part of the residential product line, which is different than their business or carrier products. I always thought that the NAS devices were OEM’d to someone else.
The big maker in NAS for Taiwan isn’t Zyxel. It’s Synology.
That would maybe help explain it. Probably rebadged.
Yeah, that’s what happens when people buy those cheap NAS devices. There’s no guarantee that your files won’t be shared with someone in China is they put 2 null bytes at the end of the user name. Just amazing 🙂
Consumers needs an Underwriters Laboratory type certification that provides confidence that a manufacturer (hardware or software) has avoided this kind of basic flaw.
What’s a “security router?”
…a device with ACL’s in it…typically a router…no unsolicited inbound connections…back in the day before firewalls as dedicated devices that’s how it was done…
Looks like we’re beholden to this researcher from Milwaukee…
… and Krebs for pressuring the manufacturer to pay attention.
I see what you did there 🙂
The Zyxel devices support FTP. Would this exploit also work through that? Would the same patch have fixed it?
I was referring to Zyxel NAS devices, of course.
Zyxel used to be the Rolls-Royce of modems in the 90s, those things were practically indestructible. Then they went for the low-cost market in the 2000s and produced gear that was barely better than the other mass-market manufacturers, my last Zyxel product was their 642 router before switching to Draytek, who have taken over from what Zyxel used to be. Interesting that whenever another shopping-list of vulnerable router manufacturers is posted, Draytek seem to be absent. Not sure if that’s because they’re that good, or just because no-one bothers attacking them.
That’s helpful for us.. But if we’re assigning blame, let’s put it where it belongs, with the people who built a device apparently with obvious flaws. And with customers who directly expose a NAS device to the internet. Makes you wonder what kind of wackybacky those customers are smokin’. Let’s not fault the researcher (Holden) and the reporter (Brian) who exposed this flaw
Finally, you will find the Pots of Gold free. You can find
50 lion slot online for messing around with real money or thrilling.
You knows your good fortune wnen you play together with. http://www.nightshift.probaljaki.hu/index.php?action=profile;u=623
500mhz=Oleg Kucherov
https://www.linkedin.com/in/oleg-kucherov-0121b995/
bindump.com
dev@bindump.com
@BindumpSecurity