Last week, KrebsOnSecurity reported to health insurance provider Blue Shield of California that its Web site was flagged by multiple security products as serving malicious content. Blue Shield quickly removed the unauthorized code. An investigation determined it was injected by a browser extension installed on the computer of a Blue Shield employee who’d edited the Web site in the past month.
The incident is a reminder that browser extensions — however useful or fun they may seem when you install them — typically have a great deal of power and can effectively read and/or write all data in your browsing sessions. And as we’ll see, it’s not uncommon for extension makers to sell or lease their user base to shady advertising firms, or in some cases abandon them to outright cybercriminals.

The health insurance site was compromised after an employee at the company edited content on the site while using a Web browser equipped with a once-benign but now-compromised extension which quietly injected code into the page.
The extension in question was Page Ruler, a Chrome addition with some 400,000 downloads. Page Ruler lets users measure the inch/pixel width of images and other objects on a Web page. But the extension was sold by the original developer a few years back, and for some reason it’s still available from the Google Chrome store despite multiple recent reports from people blaming it for spreading malicious code.
How did a browser extension lead to a malicious link being added to the health insurance company Web site? This compromised extension tries to determine if the person using it is typing content into specific Web forms, such as a blog post editing system like WordPress or Joomla.
In that case, the extension silently adds a request for a javascript link to the end of whatever the user types and saves on the page. When that altered HTML content is saved and published to the Web, the hidden javascript code causes a visitor’s browser to display ads under certain conditions.
Who exactly gets paid when those ads are shown or clicked is not clear, but there are a few clues about who’s facilitating this. The malicious link that set off antivirus alarm bells when people tried to visit Blue Shield California downloaded javascript content from a domain called linkojager[.]org.
The file it attempted to download — 212b3d4039ab5319ec.js — appears to be named after an affiliate identification number designating a specific account that should get credited for serving advertisements. A simple Internet search shows this same javascript code is present on hundreds of other Web sites, no doubt inadvertently published by site owners who happened to be editing their sites with this Page Ruler extension installed.
If we download a copy of that javascript file and view it in a text editor, we can see the following message toward the end of the file:
[NAME OF EXTENSION HERE]’s development is supported by advertisements that are added to some of the websites you visit. During the development of this extension, I’ve put in thousands of hours adding features, fixing bugs and making things better, not mentioning the support of all the users who ask for help.
Ads support most of the internet we all use and love; without them, the internet we have today would simply not exist. Similarly, without revenue, this extension (and the upcoming new ones) would not be possible.
You can disable these ads now or later in the settings page. You can also minimize the ads appearance by clicking on partial support button. Both of these options are available by clicking \’x\’ button in the corner of each ad. In both cases, your choice will remain in effect unless you reinstall or reset the extension.
This appears to be boilerplate text used by one or more affiliate programs that pay developers to add a few lines of code to their extensions. The opt-out feature referenced in the text above doesn’t actually work because it points to a domain that no longer resolves — thisadsfor[.]us. But that domain is still useful for getting a better idea of what we’re dealing with here.
Registration records maintained by DomainTools [an advertiser on this site] say it was originally registered to someone using the email address frankomedison1020@gmail.com. A reverse WHOIS search on that unusual name turns up several other interesting domains, including icontent[.]us.
icontent[.]us is currently not resolving either, but a cached version of it at Archive.org shows it once belonged to an advertising network called Metrext, which marketed itself as an analytics platform that let extension makers track users in real time.
“Three lines into your product and it’s in live,” iContent enthused. “High revenue per user.”
Another domain tied to Frank Medison is cdnpps[.]us, which currently redirects to the domain “monetizus[.]com.” Like its competitors, Monetizus’ site is full of grammar and spelling errors: “Use Monetizus Solutions to bring an extra value to your toolbars, addons and extensions, without loosing an audience,” the company says in a banner at the top of its site.
Contacted by KrebsOnSecurity, Page Ruler’s original developer Peter Newnham confirmed he sold his extension to MonetizUs in 2017.
“They didn’t say what they were going to do with it but I assumed they were going to try to monetize it somehow, probably with the scripts their website mentions,” Newnham said.
“I could have probably made a lot more running ad code myself but I didn’t want the hassle of managing all of that and Google seemed to be making noises at the time about cracking down on that kind of behaviour so the one off payment suited me fine,” Newnham said. “Especially as I hadn’t updated the extension for about 3 years and work and family life meant I was unlikely to do anything with it in the future as well.”
Monetizus did not respond to requests for comment.
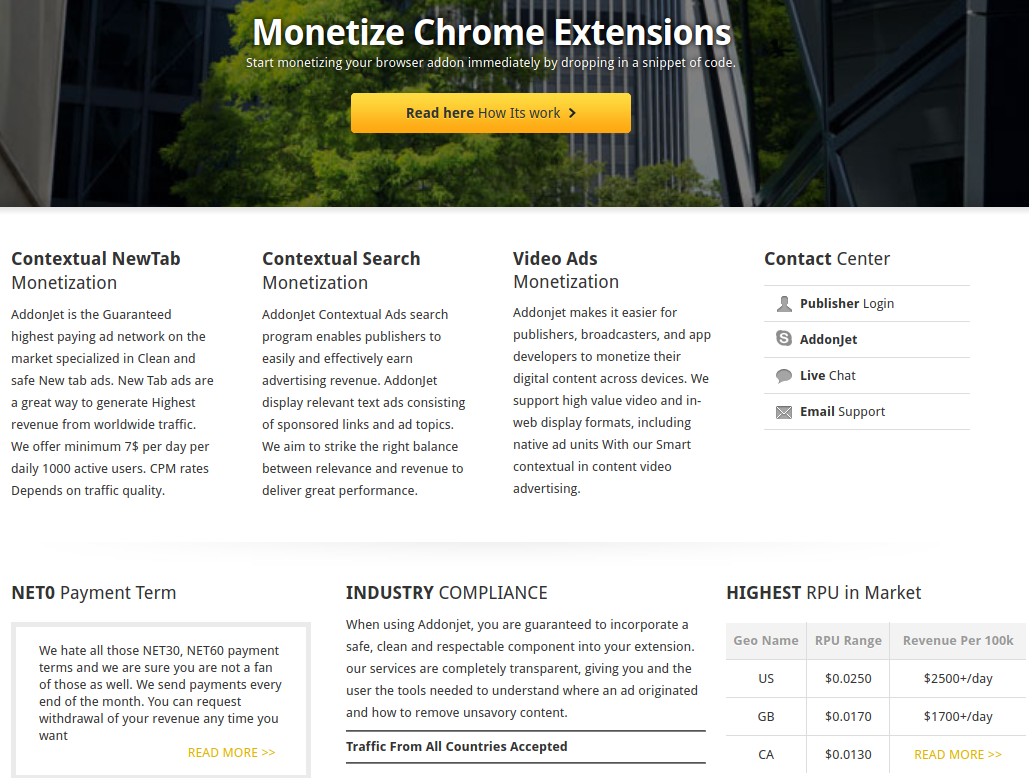
Newnham declined to say how much he was paid for surrendering his extension. But it’s not difficult to see why developers might sell or lease their creation to a marketing company: Many of these entities offer the promise of a hefty payday for extensions with decent followings. For example, one competing extension monetization platform called AddonJet claims it can offer revenues of up to $2,500 per day for every 100,000 user in the United States (see screenshot below).
I hope it’s obvious by this point, but readers should be extremely cautious about installing extensions — sticking mainly to those that are actively supported and respond to user concerns. Personally, I do not make much use of browser extensions. In almost every case I’ve considered installing one I’ve been sufficiently spooked by the permissions requested that I ultimately decided it wasn’t worth the risk.
If you’re the type of person who uses multiple extensions, it may be wise to adopt a risk-based approach going forward. Given the high stakes that typically come with installing an extension, consider carefully whether having the extension is truly worth it. This applies equally to plug-ins designed for Web site content management systems like WordPress and Joomla.
Do not agree to update an extension if it suddenly requests more permissions than a previous version. This should be a giant red flag that something is not right. If this happens with an extension you trust, you’d be well advised to remove it entirely.
Also, never download and install an extension just because some Web site says you need it to view some type of content. Doing so is almost always a high-risk proposition. Here, Rule #1 from KrebsOnSecurity’s Three Rules of Online Safety comes into play: “If you didn’t go looking for it, don’t install it.” Finally, in the event you do wish to install something, make sure you’re getting it directly from the entity that produced the software.
Google Chrome users can see any extensions they have installed by clicking the three dots to the right of the address bar, selecting “More tools” in the resulting drop-down menu, then “Extensions.” In Firefox, click the three horizontal bars next to the address bar and select “Add-ons,” then click the “Extensions” link on the resulting page to view any installed extensions.




Brian, I want to add a “me too” to Brendan Ryan’s comment. I’ve just set up in the business of building websites on WordPress and I had Page Ruler installed — until today. How can I check my built site to see if the malware has been injected?
Raymond, you could navigate to your website, hit F12 and then Ctrl + R (to refresh the page). Under Network and below that, All would show you more of what is happening. That would be a good place to look for the domains Brian mentions, and the javascript file he named.
There’s an overarching difference between how Firefox handles extensions compared to Chrome / Chromium-based browsers. Firefox lets users view available updates for extensions before they’re downloaded and installed; Chrome / Chromium-based browsers do this automatically.
This doesn’t — in and of itself — protect Firefox users, but at least it informs them of what’s being “updated”.
I don’t trust a gotsdarn one of our modern browers – Chrome, FireFox, Edge, Safarii- heck sometimes I question Opera and Puffin too for that matter…
As an old-school software developer I’ll admit I’m woefully ignorant about what the full unbridled reach of browser extensions has convoluted into these days lately but the more I learn as I continue my gravitation towards specialization in security, the more I have seen all of the damn browsers letting extensions slip-in underneath the covers…
Ironically my latest tool in investigating WTF is going on extension-wise are the Developer Tools in Chrome LOL… I’ve had so many problems with bad FireFox DLs PACKED WITH PAYLOADS COMING STRAIGHT FROM MOZILLA.COM that I haven’t even bothered cracking open FireBug in sheesh 4 years prolly now. I love Chrome as much as a browser but I don’t trust it but it does have the best dev tools right now I think (?)
Great article as usual Brian, I’m still publicly declaring you one of the first, along with Schneier of course, official Cyberheros…
The s#!t you and your family and friends and colleagues and ISPs (LOL sorry that s#!t’s not funny really) taken from all of the pieces of cyberpuke gangs and script-idiots that you helped take down over the years is the stuff of legend, friend. Anybody who pisses thugs off enough for them to want to conscript an army of 200,000 IoT fridges and toasters and what not to DDOS you to the point of almost crippling a good chunk of the entire backbone for like 20 mins or whatever the heck it was is for sure a hero in my book. Dude you’re a journalist just dig how this stuff just almost really writes its own darn self right?!
Thanks again BK, I’ve literally become like one of your evangelists – anybody who asks me anything even remotely about security these days just basically gets a good healthy dose of the URL https://krebsonsecurity.com/ imprinted into their auditory cortices…
… not gushin at or over ya or nothing like that – sorry buddy, I don’t wanna date ya or nothin like that ROTFF… Just tellin you again that your work is most appreciated, BK – fight on with that good fight friend…
And so of course upon reading this article I could not help but take a look at what extensions slimed their way onto this version of Chrome on my father’s computer and jee guess what was there:
The extension “was” called : Chrome Apps & Extensions Developer Tool
It showed up right on the extension page. It offered a “background page” which I opened into Developer Tools. I so did not like the look of this thing that before I even bothered to probe too much in Dev Tools I clicked the link to complain about extensions to Google where I selected the “I did not install this and don’t know how it got installed” radio button.
– Did not even yet click submit on the complaint form because I first wanted to switch back to the Extensions tab so I could copy the cryptic sdfasdfasfasdfa or whatever string name was listed for this extension AND THE EXTENSION WAS GONE. I DID NOT REMOVE IT. IT REMOVED ITSELF DURING THE PROCESS OF ME TRYING TO REPORT IT! I’M NOT CRAZY, I MAY BE AN IDIOT BUT I’VE BEEN PROGRAMMING PROFESSIONALLY FOR 28 YEARS AND OVERALL FOR 42 YEARS AND THIS REALLY JUST HAPPENED TO ME.
So shout out and heads up: what is up with this “Chrome Apps & Extensions Developer Tool” extension folks? Anybody know? When I googled it the first couple of listings that came up were littered with Chinese or Asian characters (not reassuring).
I’m about to check my own Chrome on my own machine to see if that extension is there (but BTW on this, my father’s machine I am logged into Chrome under my father’s Google ID he does have the Chrome Sync awesome/evil feature enabled…
Thanks everyone, just a heads-up and query for fellow experience with this nonsense…
I was using Page Ruler and I have a WordPress website, although after chrome flagged it I immediately uninstalled. Is there anything should I worry about now? Or any way to check whether my website is safe?
You could check your pages for a callout to that domain I mentioned in the story.
Hey, I can check your website to see if the extension injected any code into your website. Message me here: https://ca.linkedin.com/in/baber-pervez-cissp-3aa4b615
Recently I’ve started getting malware security center popups when browsing “https://abcnews.go.com/” using Windows Edge. I checked my computer using the instructions that are listed here: https://malwaretips.com/blogs/remove-windows-security-center/
The popups continued until I disabled Adobe Flash Player on Edge. Does this indicate that the abcnews website might be compromised? I don’t think I’ve seen this on other sites.
Thank you.
Speaking of plugins, your post prompted me to review what I have installed, thanks. I run the retire.js Firefox plugin to keep an eye on the vulnerabilities in JavaScript libraries by various sites. Retire.js is highlighting jquery 1.12.4 used by kerbsonsecurity.com as *potentially* having/allowing 3 medium level CVEs. Jquery 1.12.4 was released on 5/20/2016. It’s possible none of them apply to your site, but worth a look?
“Do not agree to update an extension if it suddenly requests more permissions than a previous version. This should be a giant red flag that something is not right. If this happens with an extension you trust, you’d be well advised to remove it entirely.”
In general that’s good advice but I don’t think it’s always true as a popular ad-blocking extension (uBlock Origin by Raymond Hill (which is a recommended extension by Mozilla)) did that not all that long ago (i.e. https://github.com/gorhill/uBlock/wiki/Permissions#access-ip-address-and-hostname-information ) and it’s legit (even though when I first seen the Firefox browser asking me to give permissions I was a bit concerned initially as I never seen that happen before and looked into it a bit before allowing it). but in general I figure keep ones extensions minimal as it limits the attack surface as those people who randomly install a bunch of extensions are just asking for trouble. a person should not need more than a few or so tops. but I consider a ad-blocking extension to be a must (I suggest uBlock Origin by Raymond Hill) and I figure while it increases the attack surface, it’s probably worth the minimal risk because of the junk it blocks online and can be further tweaked to block even more junk but the risk of breaking sites increases. but it’s default state is pretty good with no configuration needed.
I figure for the more paranoid types one can run their browser in a sandbox and use a separate browser (in a sandbox) with NO extensions installed for doing more sensitive things online like banking. I am just assuming ones computer is virus/junk free to begin with.
hell, if a person has more than one computer, especially if one has a bit of a older computer I suggest one installs Linux to it as that should give a person a secure internet machine for doing more sensitive things online and I would assume the average person is a lot less likely to get a virus or other random junk on their computer using that than Windows. so by default, it’s sort of protects the user against themselves to some degree vs Windows.
I have always been SUPER afraid of any chrome extensions.
Something many dont think about, is that there is no way to DISABLE auto extension updates.
So just because xyz extension is safe/trusted today, does not mean that TOMOROW the author of the extension wont add some malicious code to xyz extension that quickly gets pushed to ALL users of xyz extension. (or a malicious actor who gains access to the author’s pc or their google dev account).
I have asked google about this directly several months ago, and they said there is no way to disable auto extension updates (for “security” purposes), but that google does have a “extensive” auditing process for all code that appears on its chrome extensions store. I dont trust that!
tks brian!