Anyone who’s seen the 1984 hit movie Ghostbusters likely recalls the pivotal scene where a government bureaucrat orders the shutdown of the ghost containment unit, effectively unleashing a pent-up phantom menace on New York City. Now, something similar is in danger of happening in cyberspace: Shadowserver.org, an all-volunteer nonprofit organization that works to help Internet service providers (ISPs) identify and quarantine malware infections and botnets, has lost its longtime primary source of funding.
Image: Ghostbusters.
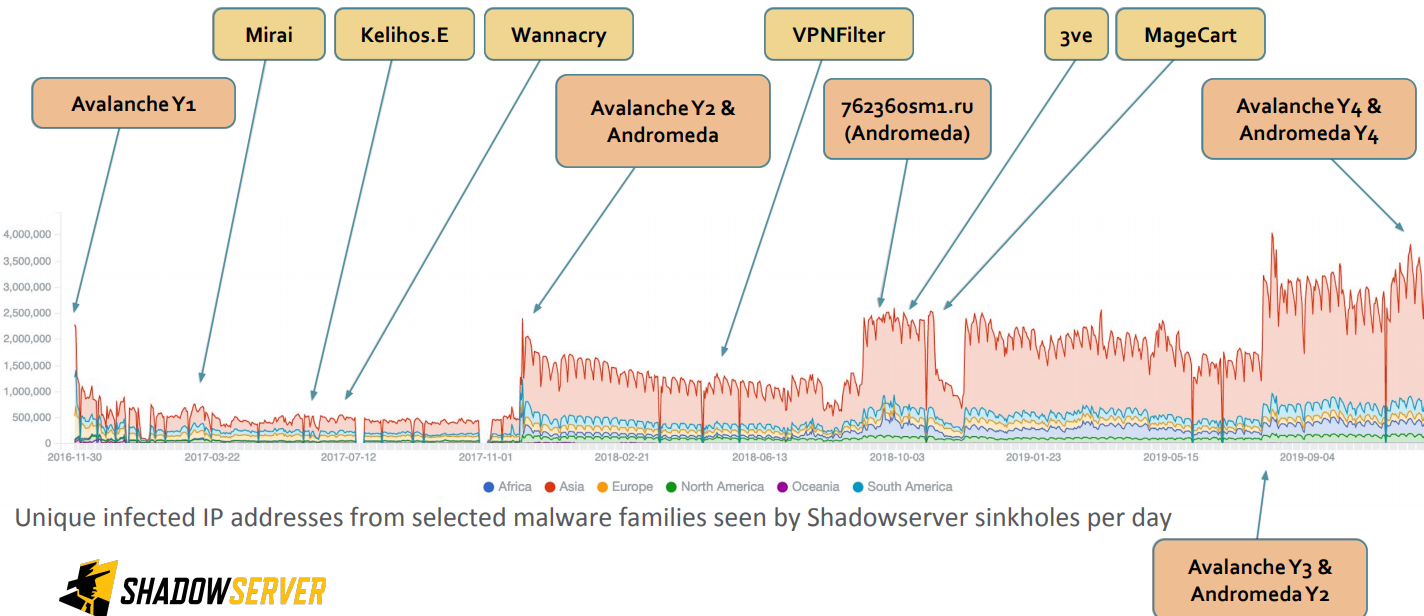
Shadowserver provides free daily live feeds of information about systems that are either infected with bot malware or are in danger of being infected to more than 4,600 ISPs and to 107 national computer emergency response teams (CERTs) in 136 countries. In addition, it has aided the FBI and other nations’ federal law enforcement officials in “sinkholing” domain names used to control the operations of far-flung malware empires.
In computer security lexicon, a sinkhole is basically a way of redirecting malicious Internet traffic so that it can be captured and analyzed by experts and/or law enforcement officials. Typically, a sinkhole is set up in tandem with some kind of legal action designed to wrest control over key resources powering a malware network.
Some of these interventions involving ShadowServer have been documented here, including the Avalanche spam botnet takedown, the Rustock botnet takeover, the Gameover malware botnet seizure, and the Nitol botnet sneak attack. Last week, Shadowserver was instrumental in helping Microsoft kneecap the Necurs malware network, one of the world’s largest spam and malware botnets.
Sinkholing allows researchers to assume control over a malware network’s domains, while redirecting any traffic flowing to those systems to a server the researchers control. As long as good guys control the sinkholed domains, none of the infected computers can receive instructions about how to harm themselves or others online.
And Shadowserver has time and again been the trusted partner when national law enforcement agencies needed someone to manage the technical side of things while people with guns and badges seized hard drives at the affected ISPs and hosting providers.
But very recently, Shadowserver got the news that the company which has primarily funded its operations for more than 15 years, networking giant Cisco Systems Inc., opted to stop providing that support.
Cisco declined to respond to questions about why it withdrew funding. But it did say the company was exploring the idea of supporting the organization as part of a broader support effort by others in the technology industry going forward.
“Cisco supports the evolution of Shadowserver to an industry alliance enabling many organizations to contribute and grow the capabilities of this important organization,” the company said in a written statement. “Cisco is proud of its long history as a Shadowserver supporter and will explore future involvement as the alliance takes shape.”
To make matters worse, Shadowserver has been told it needs to migrate its data center to a new location by May 15, a chore the organization reckons will cost somewhere in the neighborhood of $400,000.
“Millions of malware infected victims all over the world, who are currently being sinkholed and protected from cybercriminal control by Shadowserver, may lose that critical protection – just at the time when governments and businesses are being forced to unexpectedly stretch their corporate security perimeters and allow staff to work from home on their own, potentially unmanaged devices, and the risk of another major Windows worm has increased,” Shadowserver wrote in a blog post published today about their financial plight.
The Shadowserver Foundation currently serves 107 National computer emergency response teams (CERTs) in 136 countries, more than 4,600 vetted network owners and over 90% of the Internet, primarily by giving them free daily network reports.
“These reports notify our constituents about millions of misconfigured, compromised, infected or abusable devices for remediation every day,” Shadowserver explained.
The group is exploring several options for self-funding, but Shadowserver Director Richard Perlotto says the organization will likely depend on a tiered “alliance” funding model, where multiple entities provide financial support.
“Many national CERTs have been getting our data for free for years, but most of these organizations have no money and we never charged them because Cisco paid the bill,” Perlotto said. “The problem for Shadowserver is we don’t blog about our accomplishments very frequently and we operate pretty quietly. But now that we need to do funding it’s a different story.”
Perlotto said while Shadowserver’s data is extremely valuable, the organization took a stance long ago that it would never sell victim data.
“This does not mean that we are anti-commercial sector activities – we definitely believe that there are huge opportunities for innovation, for product development, and to sell cyber security services,” he said. “Shadowserver does not seek to compete with commercial vendors, or disrupt their business models. But we do fundamentally believe that no-one should have to pay to find out that they have been a victim of cybercrime.”
Most immediately, Shadowserver needs to raise approximately $400,000 by the end of this month to manage the migration of its 1,300+ servers out of Cisco’s California data center into a new facility.
Anyone interested in supporting that migration effort can do so directly here; Shadowserver’s contact page is here.
Update 10:46 a.m., ET: Added comment from Cisco.




I hope everyone of Brian’s readers/fans will help out and when you do, mention Brian sent you ;-D
Thanks for this shout-out for a worthy cause, Brian
Fully agree, thanks Brian, donated.
Shadowserver needs to start a gofundme campaign.
Brian, perhaps you could make sure the White House cybersecurity team knows about this.
Surely someone with connections to them could be hit for a couple of millions.
My 1st thought, DHS ought to be running a service like this, why can’t they fund it? 2nd thought, Shadowserver staff probly wouldn’t care for federal style in-house management
What Shadowserver is doing ought to be classified as essential public infrastructure
This kind of sinkholing service is something that I had always assumed was being done by federal entities such as US Cyber Command, or the FBI themselves
Phil, when I knew one of the shadowserver crew about eight or ten years ago he was a fed, and I suspect others were as well. So not sure your comment about accepting Federal management style is true. Thing is, a lot of that style is the inevitable consequence of the legal framework authorizing government operations. Which is why it is just not realistic to expect DHS or any government entity to take on that role.
This is a very important cause. Everyone please help if you can.
I’ll be interested in hearing Cisco’s explanation. Please update when it responds.
From the desk of Chuck Robbins: Effective immediately, signatures from Anuj Kapur, Gerri Elliott, and two other adults will be REQUIRED before implementing theoretical “cost-saving” measures.
Hey Brian,
I believe Cisco either extended the date or maybe a typo? But they have until: May 26th 2020 to get out of Cisco’s data centre.
Hi, I understand that it’s not the same container as the Prometheus, because they trashed the program and I am very angry about that, although Prometheus had a sort of self healing capability I discovered when I installed the program on my cellphone.
Do you know which servers they use by means of fake licenses? In my case was it Google uk London twice, Google California Kansas, ripencc Holland Amsterdam and that’s it I think. The problem for me is that I am probably not being attacked by that container, so I have to pick in? Hallways. I am being hacked constantly but I don’t know from where yet. I will try if you could obtain the ip adress of the used servers from which the signal appears to start, but it doesn’t.
Greets Roel Philippeth
Certainly, Giants such as Walmart, Amazon, Apple, Google, Microsoft and Wall Street big money should step up and pitch in with the funds to cover the needed expenses. Cisco…..well, shame on them for bailing on them…
“Cisco…..well, shame on them for bailing on them…”
Why shame on Cisco. Shame on the Shadowserver organization for relying on a single source of funding/facilities thinking it would never end. They should have diversified their funding sources and facilities to prevent such an occurrence like this from happening. But nope, no forward thinking about how to handle a situation like this and thus they’re stuck between a rock and a hard place now scrambling for funds to continue.
Shadowserver here. No shame on Cisco at all – they have been very generous sponsors over many years, and we will be eternally grateful that they valued our public benefit mission so highly for so long. It is simply unfortunate that they are no longer in a position to continue at the same level now. If you have a read the announcement we made on our website today that Brian references in his blog post, you will see that we were actually moving to an neutral governance industry alliance model for 2020+, where many more organizations will help share the cost of funding Shadowserver’s free public benefit services. Obviously in the perfect world, we would have have already had fully diverse funding, multiple failover data centers, etc and no risk. But please remember that we started out as volunteers and have had to build everything up from scratch ourselves to the current scale, without the usual corporate budgets, levels of support, cash buffers, etc. There has been a lot of hard work to get this far. Simply keeping up with data/server growth, hard drive failure rates (see our blog posts) and ensuring that everyone around the world gets our free daily network reports can be a difficult task. Plus our strategy was always to keep our heads down, work hard to serve our constituents, support LE operations quietly and without much PR and focus on successfully fighting cybercrime. Hence the urgent challenge when our funding and data center situation suddenly changed. But hopefully with the community’s help, we will over come this temporary bump in the road, and get to exactly the model you are suggesting. Thank for the interest everyone, hopefully we can solve this current situation together.
Funny how some people are all too happy to criticise volunteers, but won’t lift a finger to help them; of course, that requires actual effort instead of just mouthing off.
Thanks for the excellent work you have been doing, and I hope that you’ll be able to make the transition without too much difficulty.
Thanks for your efforts. I chipped in (set to monthly). I know it’s not a huge amount, but I know that every bit helps.
Hey Shadowservers.
I don’t know if it helps at all, but i’m a UK based infrastructure engineer. Without knowing anything about your data centre move project, if there’s anything i can help out with, even if you just need a warm body on this side of the pond to rack and stack equipment, please let me know
Glad you were able to help!
The ISPS and the countries CERT should be funding this. They are the customers. It’s silly to ask the public.
…yes and no…the main “customer” is law enforcement and again they have no spare money for this…a small tax on the registration of domains, like how icann is funded, is the way to go…
Maybe somebody like Fortinet would like to step up? It would show up their competitor a little bit.
I can understand Cisco deciding to stop supporting ShadowServer (kinda sorta). What I cannot comprehend is their doing so suddenly, with a short drop-dead date. Cisco should behave responsibly and give ShadowServer six months to a year to find a better funding solution. At this point, I intend to avoid Cisco products until they behave more responsibly and compassionately.
This has been Ciscos plan for some time as they’ve begun to massively push their own product, Cisco Umbrella, into the market.
I’m just a cybersecurity hobbyist and I just donated $500.00. Certainly you cybersecurity professionals can step up and donate a few bucks.
If, as you say, this organization is so important to so many countries, why would they not fund this organization themselves? Seems they would be like an Interpol for computer security. (Just a lay persons opinion)
You don’t buy the dairy farm when you’re drinking free milk.
Problem with accepting funding indiscriminately is that the sources often attach strings. Pretty soon the priorities you’re following are theirs not yours, and your mission creeps from doing good things to satisfying the desires of your money sources. Remember that cyberspace is a battleground, some of those countries could make a strategic decision that there is more benefit to their interests from emasculating shadowserver to help their offense than there is to having effective help for their defense (CERTs).
Ask Bill Gates since he is complicit in pushing a defenseless Personal Computer out into a no rules death match with the Internet. He just retired from M$ to devote his full time to philanthropy so what better cause.
If there’s no way to return a profit, there won’t be any investment from Bill Gates. You don’t maintain your status as richest (1 or 2) men in the world by actually donating money.
I get the gist of what you’re saying, but Bill Gates has for many years been among the biggest giver-awayer of monies on the planet. He’s donated more than $36 billion to a charity foundation he and his wife started years ago. If more billionaires followed suit this planet would undoubtedly be much better off.
Or, you know, you could just tax (m|b)illionnaires some mote and spend the monies in a democratic fashion instead of to the beat of the few willing out of the 1%.
No diss on philanthropy, but ideally it wouldn’t even exist.
Amen. The rich are so under taxed in what is supposed to be a progressive income tax system. I’ve paid a higher total percentage on a moderate joint income than a rich politician who made $30 MILLION. Warren Buffet has said his secretary pays a higher percentage of income than he does. And I won’t even go into the 2017(I think) tax cut which was so favorable to the rich.
I’d like to try to volunteer some time and resources if I’m able to assist. I run a cyber security team for a large IT org – ie I have some hands on exp and organizational skills.
Thx
-M
A few details needed.
-Is Shadowserver listed on the Charity Navigator site?
-Is Shadowserver a 501(c)(3) organization?
-If I need to send a check, how would I do that?
The entire planet is run by extremely rich, cheap SOB’s. Does the under investment in ShadowServer remind anyone of the under investment in pandemic strategic supplies to have on hand for an emergency that lots of intelligent people knew for years would one day happen? Maybe, when the entire planet’s internet system collapses one day from a well planned massive attack, then those SOB’s will realize how cheap they really could have gotten off.