Almost daily now there is news about flaws in commercial software that lead to computers getting hacked and seeded with malware. But the reality is most malicious software also has its share of security holes that open the door for security researchers or ne’er-do-wells to liberate or else seize control over already-hacked systems. Here’s a look at one long-lived malware vulnerability testing service that is used and run by some of the Dark Web’s top cybercriminals.
It is not uncommon for crooks who sell malware-as-a-service offerings such as trojan horse programs and botnet control panels to include backdoors in their products that let them surreptitiously monitor the operations of their customers and siphon data stolen from victims. More commonly, however, the people writing malware simply make coding mistakes that render their creations vulnerable to compromise.
At the same time, security companies are constantly scouring malware code for vulnerabilities that might allow them peer to inside the operations of crime networks, or to wrest control over those operations from the bad guys. There aren’t a lot of public examples of this anti-malware activity, in part because it wades into legally murky waters. More importantly, talking publicly about these flaws tends to be the fastest way to get malware authors to fix any vulnerabilities in their code.
Enter malware testing services like the one operated by “RedBear,” the administrator of a Russian-language security site called Krober[.]biz, which frequently blogs about security weaknesses in popular malware tools.
For the most part, the vulnerabilities detailed by Krober aren’t written about until they are patched by the malware’s author, who’s paid a small fee in advance for a code review that promises to unmask any backdoors and/or harden the security of the customer’s product.
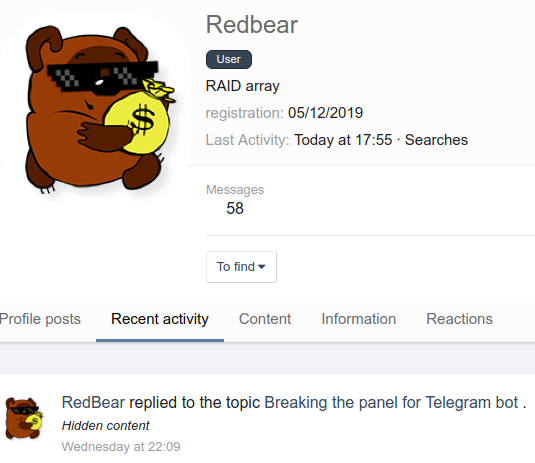
RedBear’s profile on the Russian-language xss[.]is cybercrime forum.
“We can examine your (or not exactly your) PHP code for vulnerabilities and backdoors,” reads his offering on several prominent Russian cybercrime forums. “Possible options include, for example, bot admin panels, code injection panels, shell control panels, payment card sniffers, traffic direction services, exchange services, spamming software, doorway generators, and scam pages, etc.”
As proof of his service’s effectiveness, RedBear points to almost a dozen articles on Krober[.]biz which explain in intricate detail flaws found in high-profile malware tools whose authors have used his service in the past, including; the Black Energy DDoS bot administration panel; malware loading panels tied to the Smoke and Andromeda bot loaders; the RMS and Spyadmin trojans; and a popular loan scam script.
ESTRANGED BEDFELLOWS
RedBear doesn’t operate this service on his own. Over the years he’s had several partners in the project, including two very high-profile cybercriminals (or possibly just one, as we’ll see in a moment) who until recently operated under the hacker aliases “upO” and “Lebron.”
From 2013 to 2016, upO was a major player on Exploit[.]in — one of the most active and venerated Russian-language cybercrime forums in the underground — authoring almost 1,500 posts on the forum and starting roughly 80 threads, mostly focusing on malware. For roughly one year beginning in 2016, Lebron was a top moderator on Exploit.
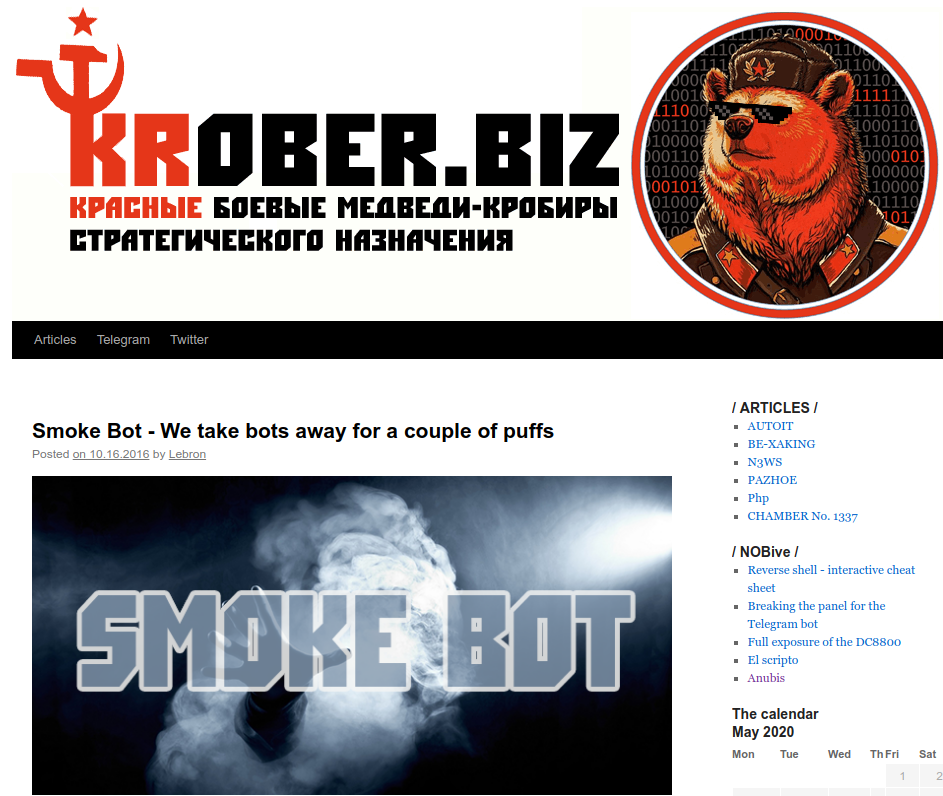
One of many articles Lebron published on Krober[.]biz that detailed flaws found in malware submitted to RedBear’s vulnerability testing service.
up0 would eventually be banned from Exploit for getting into an argument with another top forum contributor, wherein both accused the other of working for or with Russian and/or Ukrainian federal authorities, and proceeded to publish personal information about the other that allegedly outed their real-life identities.
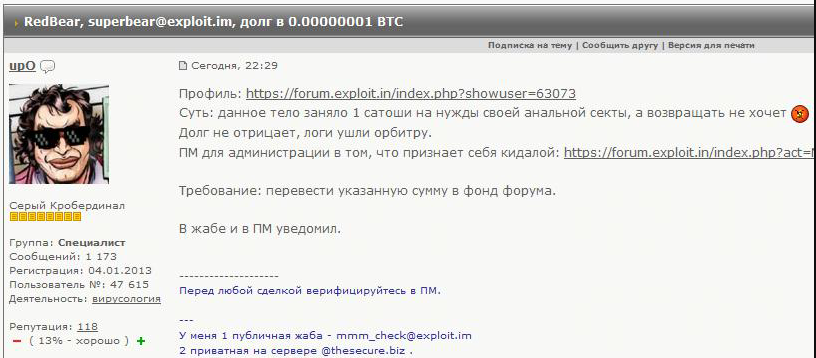
The cybercrime actor “upO” on Exploit[.]in in late 2016, complaining that RedBear was refusing to pay a debt owed to him.
His departure was prefaced by a series of increasingly brazen accusations by forum members that Lebron was simply upO using a different nickname. His final post on Exploit in May 2017 somewhat jokingly indicated he was joining an upstart ransomware affiliate program.
RANSOMWARE DREAMS
According to research from cyber intelligence firm Intel 471, upO had a strong interest in ransomware and had partnered with the developer of the Cerber ransomware strain, an affiliate program operating between Feb. 2016 and July 2017 that sought to corner the increasingly lucrative and competitive market for ransomware-as-a-service offerings.
Intel 471 says a rumor has been circulating on Exploit and other forums upO frequented that he was the mastermind behind GandCrab, another ransomware-as-a-service affiliate program that first surfaced in January 2018 and later bragged about extorting billions of dollars from hacked businesses when it closed up shop in June 2019.
Multiple security companies and researchers (including this author) have concluded that GandCrab didn’t exactly go away, but instead re-branded to form a more exclusive ransomware-as-a-service offering dubbed “REvil” (a.k.a. “Sodin” and “Sodinokibi”). REvil was first spotted in April 2019 after being installed by a GandCrab update, but its affiliate program didn’t kick into high gear until July 2019.
Last month, the public face of the REvil ransomware affiliate program — a cybercriminal who registered on Exploit in July 2019 using the nickname “UNKN” (a.k.a. “Unknown”) — found himself the target of a blackmail scheme publicly announced by a fellow forum member who claimed to have helped bankroll UNKN’s ransomware business back in 2016 but who’d taken a break from the forum on account of problems with the law.
That individual, using the nickname “Vivalamuerte,” said UNKN still owed him his up-front investment money, which he reckoned amounted to roughly $190,000. Vivalamuerte said he would release personal details revealing UNKN’s real-life identity unless he was paid what he claims he is owed.
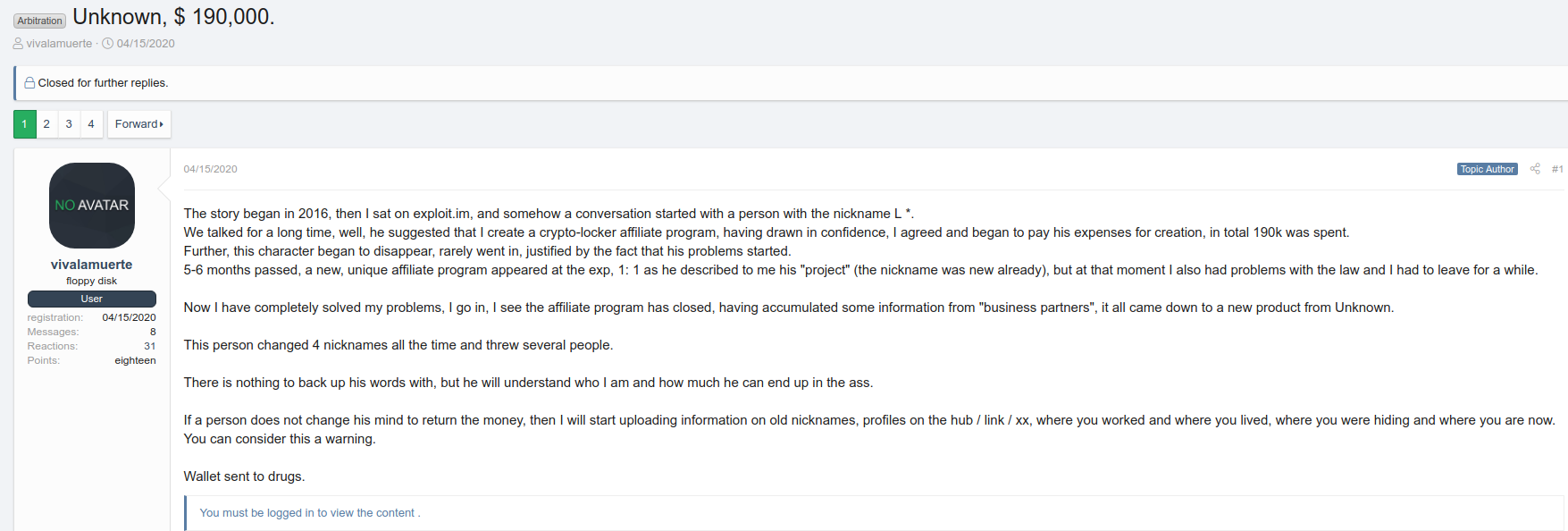
In this Google-translated blackmail post by Vivalamuerte to UNKN, the latter’s former nickname was abbreviated to “L”.
Vivalamuerte also claimed UNKN has used four different nicknames, and that the moniker he interacted with back in 2016 began with the letter “L.” The accused’s full nickname was likely redacted by forum administrators because a search on the forum for “Lebron” brings up the same post even though it is not visible in any of Vivalamuerte’s threatening messages.
Reached by KrebsOnSecurity, Vivalamuerte declined to share what he knew about UNKN, saying the matter was still in arbitration. But he said he has proof that Lebron was the principle coder behind the GandCrab ransomware, and that the person behind the Lebron identity plays a central role in the REvil ransomware extortion enterprise as it exists today.




…when I was teaching at georgetown I once had a question on a mid term that said more or less that “software professionals” wrote malware…
…I caught flak from the s/w developers in the class who said the malware writers were not “professional”…
Why are cyber criminals disproportionately Eastern European? Scum.
My Russian friend says that in the winter, it’s way too cold outside so there’s nothing to do but stay inside and hack computers.
Hey I’m Polish it’s a miracle I can even turn on my machine
Strong education programs in computer sciences and mathematics dating back to the space race.
Poor economic opportunities.
Lack of law enforcement.
Have you ever considered the geo location for russia? I mean: if it was “disporportionaly” in the USA, there would be no wonder about it, but as it is in Russia, we start wondering why.
Well, let’s consider Russia’s neighbours and near-neighbours: Russia is Europe and Asia, and then is close to India, China (sort off…), USA, Canada, Japan, South Korea. If you think it over, Russia is well connected with ALL northern hemysphere. It’s the perfect place to learn how to conduct “business” and exchange “knowledge” with all the planet.
If you look at a G8 world map, and considering Russia IS on Europe, where would you choose to locate your business?
I feel the right question is: why isn’t it more powerful? It does not strike me as a wonder, the amazing connections they have. (Apologies for my English)
Sorry Brian but it all looks like a guess-work.
Any real proofs?
You either didn’t read the caveats in the article or you don’t understand how this kind of investigation works if you expect to have “proofs” of every single thing Brian is talking about without having any of it in front of you, or going to look for any of it, or knowing anything about it.
It’s like saying “Prove the sky is blue or you’re a liar”
There’s real “proofs” that he’s investigating the various alleged pseudonyms of a malware author by people who would know.
What exactly would satisfy you besides “a breath of blue air”?
You want Krebs to dox them? That’s not how this works.
Read the caveats at the beginning over again. No training wheels.
great post. That’s very true
Yeah tttyy95 Brian Krebs made this whole thing up… So he’s an award-winning fiction author now instead of award-winning investigative journalist?
“Sorry Brian but it all looks like a guess-work.
Any real proofs?”
Sorry ttty95, I’m not usually one to make fun of anybody’s English, but you earned this one: next time you decide to take on a professional journalist you’ll do better right out of the gate at least trying not to sound like you’re writing from one of the Commonwealth of Independent States and/or Syria.
Troll off ttty95
I love it, CBK – I know you put ALOT of time and work into rooting out these professional ne’r-do-wells but you have to admit that this stuff almost writes itself:
“In 2016, several members began accusing upO of stealing source code from malware projects under review, and then allegedly using or incorporating bits of the code into malware projects he marketed to others. up0 would eventually be banned from Exploit for getting into an argument with another top forum contributor, wherein both accused the other of working for or with Russian and/or Ukrainian federal authorities, and proceeded to publish personal information about the other that allegedly outed their real-life identities.”
Recursive idiocy at its best! I say we just give up the war on cybercrime and watch these fools take their own damn selves down 😀
Sorry, but judging by your writing it seems you are extremely affectionate of the author, and blatantly ignoring and putting down other peoples comments in an attempt to protect the author from critics.
It sure looks like you would do anything to please Brian.
I must say it quite annoys me when people respond the way you do.
Without taking side with malware authors, I would like to pinpoint that most malware authors highly likely started developing malware by wanting to learn. Malware being what made the learning exciting. Some people however go too far, like what has possibly happened in this case.
In addition, some of the commenters of this blog seem like they want to punish malware developers by sentences worse than the sentence of mass-murderes, and that these people are portrayed as the worst kind of scum.
Come on, take a break. If my computer got hacked, sure I would like the people who carried it out to get an appropriate punishment, but not to the extreme level most of the people in this comment section would. It is ridiculous reading the replies in the comments.
The way I view your anger and desire to punish these malware authors is like wanting to stone someone to death for stealing your bicycle. Please try to be a little more reflected in your unilateral opinions. I honestly dont understand where your extreme anger towards malware developers is originating from.
Quote “I honestly dont understand where your extreme anger towards malware developers is originating from.”
Ransome ware on hospital computers that result in patient death is murder. Involuntary manslaughter if you want. When you completely shutdown a medical network, it is not just inconvenient, like someone taking your bicycle.
When it comes to ransomware I totally agree with your statement. No questions asked.
Perhaps I should have been more clear in my first comment; Regardless of the level of destructive behavior done. I.e. some people (in this comment section) want the threat actor(s) almost sentenced to life imprisonment for having orchestrated a DDoS attack on a website causing a few hours downtime, or for having sold leaked credentials/databases, or harvested devices for a botnet.
Although this is against the law and considered unethical, it is just virtual damage/disruption, and this is what I feel people generally tend to forget.
Who cares if virtual damage and disruption is against the law? It’s uncool no matter which way you choose to look at it…
“Although this is against the law and considered unethical, it is just virtual damage/disruption, and this is what I feel people generally tend to forget.”
But what should people be “remembering” from your example?
Yes, “cyber” attacks have “virtual” damage. But also real damage.
People lose money. Companies lose money/reputation.
Individuals lose control over PII, sometimes their finances.
Right now millions of fraudulent claims are being filed with people’s individual information found on the dark web.
Senior citizens are having their accounts emptied.
You’re right that “some folks” want to see draconian and severe consequences for “virtual” bad actors – but they’re bad actors.
People robbing convenience stores or old ladies get shot at.
Why shouldn’t the idiot DDOS/SWATTERs get shot at too?
You seem to be upset that Brian Krebs is in the business of outing and exposing these miscreants-&-worse to wider public scrutiny.
Why would that be though? What is gained by not exposing them?
Everything is not black and white.
It indeed is bad, but the severity of it depends on what has been done. And this exactly is my point.
My initial rant was that regardless of the severity, some people just want to watch these individuals “burn”, even though the damage they caused leave no significant damage (in my opinion) or only virtual damage.
For instance, if I was too lazy to secure my router and an actor dropped malware on it resulting that it became part of a botnet, I would not go nuts and take it personally. I would simply fix the problem and stop being bu**h*rt about it. The same goes for anyone attacking my web services, since you mentioned DDoS as an example. I would never want someone to spend years of their lifetime in jail for carrying out any of the examples above. That is just too much. Everyone makes mistakes.
Unless its very large scale and it actually causes significant damage, why be so extremely mad and vindictive over what happened?
When it comes to the very obvious examples, such as the ones you and others have mentioned, then I fully agree that it should not be taken lightly.
Lastly, I am not upset at Brian exposing anyone at all. Quite the opposite actually, as I enjoy reading his articles.
And to answer one of your last statements: “You seem to be upset that Brian Krebs is in the business of outing and exposing these miscreants-&-worse to wider public scrutiny.”
Perhaps we should also bring back the public pillory from the 1800s, which was used to out miscreants who performed the crimes of blasphemy and fortune telling to wider public scrutiny? It would be exactly the same, except that we are now in the 21st century.
Hooray for pointing out the flaws in others, and making money off of it…
Interesting argument. Because what you’re saying makes kind of sense, in that the punishment should be the same whether you are a white collar business criminal or a malware developer.
But I also have a prejudiced opinion against malware developers as the individual responsible for IT Support at my organization. And you know what happens to that fly that keeps flying around your face, right? But it’s not personal, it’s professional! I promise not to rip the wings off first…
An excellent post. But, it would be better if you explained it with real proofs.
So this Master Mind (big blue head) bad guy, helped other bad guys with their powers (software) in order to take the best parts of their coding to make himself more powerful to become the most powerful evil villain ever.
People like this make powerful enemies, karma will get ’em.
Do the malware guys have a CVE on the dark web where vulnerabilities in malware code get a risk rating? And is there an upside down equivalent to PCI where you can fall out of compliance to it if you haven’t patched high risk vulnerabilities in your malware code in a month of their publication date?
…the same cve applies since they use, by and large, the same underlying tools to build their software…and have the same set of bugs to deal with…software is after all, designed and built by humans in the end…
…but there’s a good money making opportunity for the daring – the “bad” housekeeping seal for malware…hmmm…maybe I should protect that idea…
I would think those miscreants are fully supportive of the ongoing pressure by some in the current and past Administrations that would impose some requirement of Apple and other software developers to incorporate a backdoor in their OS’s in order to facilitate “official” investigations of terrorists and other criminals…
It would produce exploit heaven for them.
…what goes around comes around…
…during the Clinton era the NSA tried to get industry to use skipjack for commercial encryption for similar “backdoor” needs…scotus killed that…now doj/fbi is trying again…
Begs to wonder how Schneier (https://www.schneier.com/) would weigh in on this…?
i think i agree with you on this one.
When was the last time a terrorist crippled a nation’s healthcare system? Clearly, we’re using our drones against the wrong group of people.
They sound like they are related to fancy bear any thoughts post a reply?
You got to love those Russian cyber-criminals who work for Putan !
It’s time we got really serious about jail penalties for perps! 20 years without parole for Internet misfits! No internet, books, or games allowed!
I read a few articles on krober. Very funny. Someone asked why malwar (purposely mistyped, we pronounce it that way) comes from Europe. You need to know who is the guy on the main banner on the main page. It is a frame from a movie. If you are interested watch 2 movies. Brat and Brat 2. You can find them on YouTube with subtitles. Brat 2 will be more understandable. All authors want to be like that guy.
I wrote a few viruses for DOS. Then dropped. We had a lot of white work. It is better to build coliseums then nuclear bombs. Those kids were never invited to build something meaningful. And only because of where they live.
CIA excels at cyber attacks and counter attacks, as does KGB. Best minds of the children of the richest families as well, send the to the finest schools to learn to engage in cyber espionage. Many do it for bragging rights. Most all do it for the money. Some deal in global monopoly of pure opium or pure cocaine, distribution, harvesting, processing and money laundering operations. Only one or two perhaps three a best in the world are just that. One defined the world ‘hacker’ but in the realm of US military intelligence and making patches seat of the pants in machine language in a critical situation to save many lives. Not what the derogatory term ‘hacker’ has become. One greater than he is the world’s best and former CIA, but does it as a hobby to protect US National Security interests and his own sacred honor.