Data Viper, a security startup that provides access to some 15 billion usernames, passwords and other information exposed in more than 8,000 website breaches, has itself been hacked and its user database posted online. The hackers also claim they are selling on the dark web roughly 2 billion records Data Viper collated from numerous breaches and data leaks, including data from several companies that likely either do not know they have been hacked or have not yet publicly disclosed an intrusion.
The apparent breach at St. Louis, Mo. based Data Viper offers a cautionary and twisted tale of what can happen when security researchers seeking to gather intelligence about illegal activity online get too close to their prey or lose sight of their purported mission. The incident also highlights the often murky area between what’s legal and ethical in combating cybercrime.
Data Viper is the brainchild of Vinny Troia, a security researcher who runs a cyber threat intelligence company called Night Lion Security. Since its inception in 2018, Data Viper has billed itself as a “threat intelligence platform designed to provide organizations, investigators and law enforcement with access to the largest collection of private hacker channels, pastes, forums and breached databases on the market.”
Many private companies sell access to such information to vetted clients — mainly law enforcement officials and anti-fraud experts working in security roles at major companies that can foot the bill for these often pricey services.
Data Viper has sought to differentiate itself by advertising “access to private and undisclosed breach data.” As KrebsOnSecurity noted in a 2018 story, Troia has acknowledged posing as a buyer or seller on various dark web forums as a way to acquire old and newly-hacked databases from other forum members.
But this approach may have backfired over the weekend, when someone posted to the deep web a link to an “e-zine” (electronic magazine) describing the Data Viper hack and linking to the Data Viper user base. The anonymous poster alleged he’d been inside Data Viper for months and had exfiltrated hundreds of gigabytes of breached data from the service without notice.
The intruder also linked to several dozen new sales threads on the dark web site Empire Market, where they advertise the sale of hundreds of millions of account details from dozens of leaked or hacked website databases that Data Viper allegedly acquired via trading with others on cybercrime forums.
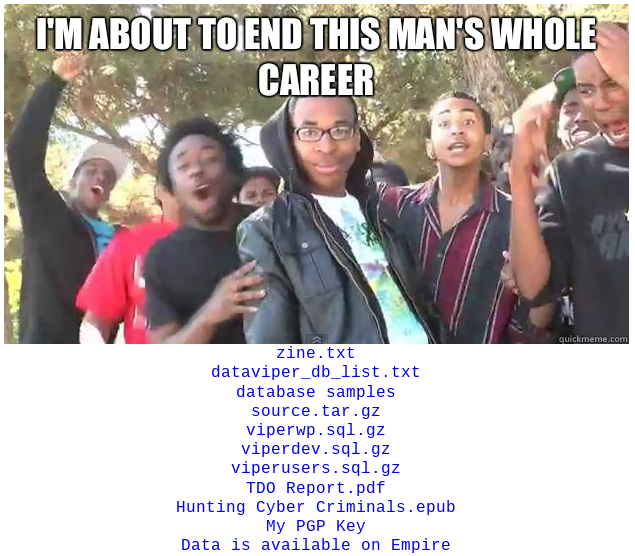
An online post by the attackers who broke into Data Viper.
Some of the databases for sale tie back to known, publicly reported breaches. But others correspond to companies that do not appear to have disclosed a security incident. As such, KrebsOnSecurity is not naming most of those companies and is currently attempting to ascertain the validity of the claims.
KrebsOnSecurity did speak with Victor Ho, the CEO of Fivestars.com, a company that helps smaller firms run customer loyalty programs. The hackers claimed they are selling 44 million records taken from Fivestars last year. Ho said he was unaware of any data security incident and that no such event had been reported to his company, but that Fivestars is now investigating the claims. Ho allowed that the number of records mentioned in the dark web sales thread roughly matches the number of users his company had last year.
But on Aug. 3, 2019, Data Viper’s Twitter account casually noted, “FiveStars — 44m breached records added – incl Name, Email, DOB.” The post, buried among a flurry of similar statements about huge caches of breached personal information added to Data Viper, received hardly any attention and garnered just one retweet.
GNOSTIC PLAYERS, SHINY HUNTERS
Reached via Twitter, Troia acknowledged that his site had been hacked, but said the attackers only got access to the development server for Data Viper, and not the more critical production systems that power the service and which house his index of compromised credentials.
Troia said the people responsible for compromising his site are the same people who hacked the databases they are now selling on the dark web and claiming to have obtained exclusively from his service.
What’s more, Troia believes the attack was a preemptive strike in response to a keynote he’s giving in Boston this week: On June 29, Troia tweeted that he plans to use the speech to publicly expose the identities of the hackers, who he suspects are behind a large number of website break-ins over the years.
Hacked or leaked credentials are prized by cybercriminals engaged in “credential stuffing,” a rampant form of cybercrime that succeeds when people use the same passwords across multiple websites. Armed with a list of email addresses and passwords from a breached site, attackers will then automate login attempts using those same credentials at hundreds of other sites.
Password re-use becomes orders of magnitude more dangerous when website developers engage in this unsafe practice. Indeed, a January 2020 post on the Data Viper blog suggests credential stuffing is exactly how the group he plans to discuss in his upcoming talk perpetrated their website compromises.
In that post, Troia wrote that the hacker group, known variously as “Gnostic Players” and “Shiny Hunters,” plundered countless website databases using roughly the same method: Targeting developers using credential stuffing attacks to log into their GitHub accounts.
“While there, they would pillage the code repositories, looking for AWS keys and similar credentials that were checked into code repositories,” Troia wrote.
Troia said the intrusion into his service wasn’t the result of the credential re-use, but instead because his developer accidentally left his credentials exposed in documents explaining how customers can use Data Viper’s application programming interface.
“I will say the irony of how they got in is absolutely amazing,” Troia said. “But all of this stuff they claim to be selling is [databases] they were already selling. All of this is from Gnostic players. None of it came from me. It’s all for show to try and discredit my report and my talk.”
Troia said he didn’t know how many of the databases Gnostic Players claimed to have obtained from his site were legitimate hacks or even public yet.
“As for public reporting on the databases, a lot of that will be in my report Wednesday,” he said. “All of my ‘reporting’ goes to the FBI.”
SMOKE AND MIRRORS
The e-zine produced by the Data Viper hackers claimed that Troia used many nicknames on various cybercrime forums, including the moniker “Exabyte” on OGUsers, a forum that’s been closely associated with account takeovers.
In a conversation with KrebsOnSecurity, Troia acknowledged that this Exabyte attribution was correct, noting that he was happy about the exposure because it further solidified his suspicions about who was responsible for hacking his site.
This is interesting because some of the hacked databases the intruders claimed to have acquired after compromising Data Viper correspond to discoveries credited to Troia in which companies inadvertently exposed tens of millions of user details by leaving them publicly accessible online at cloud services like Amazon’s EC2.
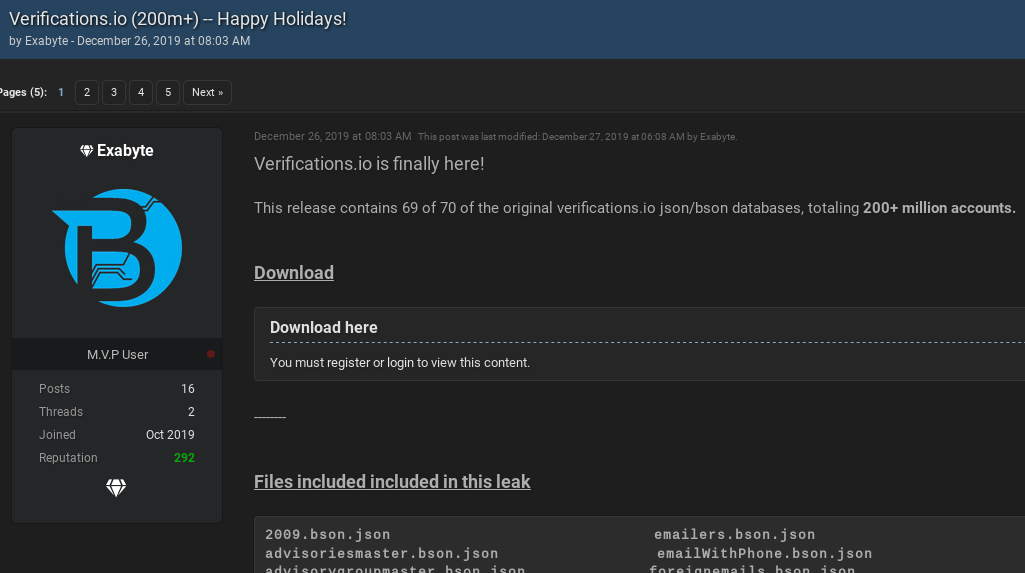
For example, in March 2019, Troia said he’d co-discovered a publicly accessible database containing 150 gigabytes of plaintext marketing data — including 763 million unique email addresses. The data had been exposed online by Verifications.io, an email validation firm.
On Oct 12, 2019, a new user named Exabyte registered on RaidForums — a site dedicated to sharing hacked databases and tools to perpetrate credential stuffing attacks. That Exabyte account was registered less than two weeks after Troia created his Exabyte identity on OGUsers. The Exabyte on RaidForums posted on Dec. 26, 2019 that he was providing the community with something of a belated Christmas present: 200 million accounts leaked from Verifications.io.
“Verifications.io is finally here!” Exabyte enthused. “This release contains 69 of 70 of the original verifications.io databases, totaling 200+ million accounts.”
In May 2018, Troia was featured in Wired.com and many other publications after discovering that sales intelligence firm Apollo left 125 million email addresses and nine billion data points publicly exposed in a cloud service. As I reported in 2018, prior to that disclosure Troia had sought my help in identifying the source of the exposed data, which he’d initially and incorrectly concluded was exposed by LinkedIn.com. Rather, Apollo had scraped and collated the data from many different sites, including LinkedIn.
Then in August 2018, someone using the nickname “Soundcard” posted a sales thread to the now-defunct Kickass dark web forum offering the personal information of 212 million LinkedIn users in exchange for two bitcoin (then the equivalent of ~$12,000 USD). Incredibly, Troia had previously told me that he was the person behind that Soundcard identity on the Kickass forum.
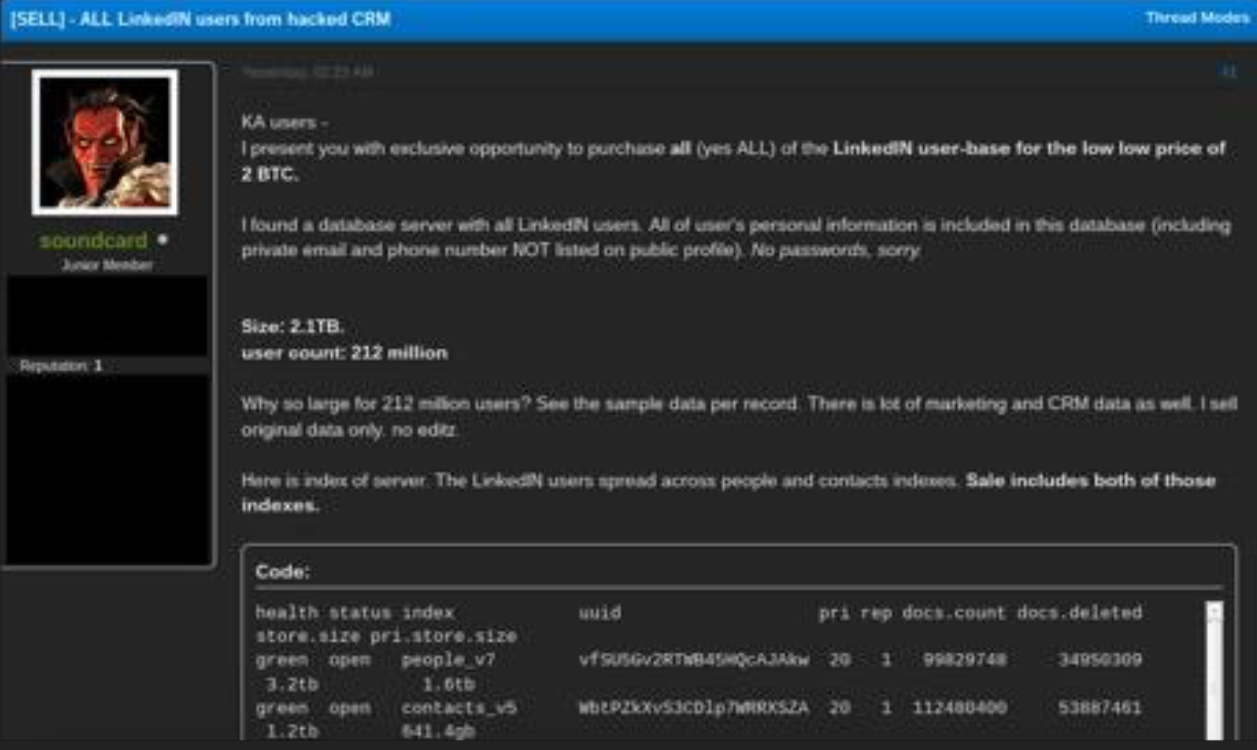
Soundcard, a.k.a. Troia, offering to sell what he claimed was all of LinkedIn’s user data, on the Dark Web forum Kickass.
Asked about the Exabyte posts on RaidForums, Troia said he wasn’t the only one who had access to the Verifications.io data, and that the full scope of what’s been going on would become clearer soon.
“More than one person can have the same name ‘Exabyte,” Troia said. “So much from both sides you are seeing is smoke and mirrors.”
Smoke and mirrors, indeed. It’s entirely possible this incident is an elaborate and cynical PR stunt by Troia to somehow spring a trap on the bad guys. Troia recently published a book on threat hunting, and on page 360 (PDF) he describes how he previously staged a hack against his own site and then bragged about the fake intrusion on cybercrime forums in a bid to gather information about specific cybercriminals who took the bait — the same people, by the way, he claims are behind the attack on his site.
MURKY WATERS
While the trading of hacked databases may not technically be illegal in the United States, it’s fair to say the U.S. Department of Justice (DOJ) takes a dim view of those who operate services marketed to cybercriminals.
In January 2020, U.S. authorities seized the domain of WeLeakInfo.com, an online service that for three years sold access to data hacked from other websites. Two men were arrested in connection with that seizure. In February 2017, the Justice Department took down LeakedSource, a service that operated similarly to WeLeakInfo.
The DOJ recently released guidance (PDF) to help threat intelligence companies avoid the risk of prosecution when gathering and purchasing data from illicit sources online. The guidelines suggest that some types of intelligence gathering — particularly exchanging ill-gotten information with others on crime forums as a way to gain access to other data or to increase one’s status on the forum — could be especially problematic.
“If a practitioner becomes an active member of a forum and exchanges information and communicates directly with other forum members, the practitioner can quickly become enmeshed in illegal conduct, if not careful,” reads the Feb. 2020 DOJ document.
The document continues:
“It may be easier for an undercover practitioner to extract information from sources on the forum who have learned to trust the practitioner’s persona, but developing trust and establishing bona fides as a fellow criminal may involve offering useful information, services, or tools that can be used to commit crimes.”
“Engaging in such activities may well result in violating federal criminal law. Whether a crime has occurred usually hinges on an individual’s actions and intent. A practitioner must avoid doing anything that furthers the criminal objectives of others on the forums. Even though the practitioner has no intention of committing a crime, assisting others engaged in criminal conduct can constitute the federal offense of aiding and abetting.”
“An individual may be found liable for aiding and abetting a federal offense if her or she takes an affirmative act — even an act that is lawful on its own — that is in furtherance of the crime and conducted with the intent of facilitating the crime’s commission.”




Good article !
Instead of describing Data Viper as “a cyber threat intelligence company” it should be just “a cyber threat company.”
Red — This forum needs a Like or Spice button! Thanks for the LOL.
This was solid. Thank you.
Indeed. Can’t wait for your arrest!
Better stock up on some lube. You’re gonna need it when the bruthas check you out.
So the question is who’s next. Is it going to be have-I-been-pwned? It always worries me when those stolen-data-aggregators collect too much data. It becomes such a juicy target for the bad guys, especially if it’s a one man operation. No matter how careful they are themselves there are also other services that have access to their cache. And this is especially true when they themselves start charging for their service. It gives more incentive for the bad guys to hack them.
That’s why Troy Hunt (who runs HIBP) has always refused to load anything other than email addresses into his service. If someone was to break in, all they would get is a list of email addresses, no other personal information.
HIBP includes password hashes. Otherwise, you wouldn’t be able to look them up.
Indeed. Anyone can download haveibeenpwned’s entire list (11Gb!) of password hashes, for free, from the links on his site – see the bottom of this page:
https://haveibeenpwned.com/Passwords
For obvious reasons, he doesn’t store which accounts used which hash, just a count of how often they were used.
Yes, indeed he runs the service that’s called pwned-passwords. And yes, you can download sha1 hashes for passwords. But do you guys seriously believe that he doesn’t store those passwords somewhere in plaintext? How else would he update his sha-1 database, especially when it also includes password match count?
C’mon don’t be a bunch fan-boys. Use your nobbin.
Er – you run the same password through SHA1, you get the same hash. So why would you need the plaintext, to update the count?
Yes and many of these aggregators companies STORE and SELL their data in plaintext with the argument that the data is already public. Some do not and maintain stringent security around that type since it is so sensitive. Companies/organizations need to be careful which security vendors they do business with and make sure that vendor protects the data.
lol ok “dev env” my ass…
the source is on that same ezine website along with user table. This guy is a joke. Shame how these companies handle our data. Same guys who are considered good guys are also acting as bad guys. This vinny guy needs to be in jail.
The fact that digital smash’n grab will always exist under the current environment it seems we need a total top-to-bottom revamping of digital credentialing. Clearly, the systems we have now do not work. Instead of trying to keep the criminals out how about a new way for consumers and companies to exist online and transact that is immune to break-ins in the first place. Surely, someone can come up with a modern, novel (revolutionary?) approach to this.
Makes me wonder about online password management services ..surely these must be a juicy target too.
Aren’t voter registration databases from gov agencies? If so aren’t these federal or state crimes?
US Voters Database (2016) 62054321
2018 voters Florida 13939029
2018 voters North Carolina 8114702
2018 voters Ohio 8020668
2018 voters Washington 4792982
2018 voters Colorado 3692309
2019 colorado registered voters 3821719
2018 voters Connecticut 2289729
2018 voters Kansas 1822585
2018 voters Nevada 1743937
2019 nevada voters 1268413
2019 michigan voters 7523476
2019 rhode island voters 780490
2018 voters Rhode Island 770422
2018 New York Voters 18158506
2018 Maryland Voters 4286735
2018 Missouri Voters 4130523
2018 Oregon Voters 3179344
2018 Washington DC Voters 493217
I didn’t check all of them (checked 7, all make the list available to the public). Many states will provide some of the information to the public, unless it contains non-public content (SSN, DOB , etc depending on state) there is no crime required to obtain the lists.
Voter roles and at least in some cases, the date of the last election in which the individual is recorded to have voted are public information.
Thanks for sharing.
An, good story. Interesting.
Yes, databases are interesting. And parts of databases should be protected. As in encrypted other then the usual safeguards. But, such is business and security. I look at databases almost on a daily basis. But, it’s the use of the database that is being criminalized. Unfortunately, that.leads to use issues. Such as hiding geanology databases. Sites that refuse a web scraper to organize for searches. But many of the data collectors have yet to progress from an old db2 protection. Or program style. Interesting.
I quote:”a federal offense if her or she takes an affirmative act ”
I always knew women were sneaky! Just kidding, we know it should have been “he or she”. 😀
Thanks Brian, Great write-up and I agree with the early posters, would be nice to have a +1/like on comments. lol
I used to have a plugin that allowed up and downvotes, but it stopped being supported and also had security weaknesses, so we got rid of it. Also, I don’t like to rely on too many plugins because each one comes with its own security risks.
we prefer you focus on the awesome research/write ups vs features in the comment section… as always, ty for all you do!
Vinny could not help but get involved with the wrong crowd.
It is Vinny’s parents fault for naming him Vinny.
I just realized that his name literally means “guilty” in my language (spelled “winny” but the pronunciation is the same)
Getting pretty dang interesting.
It’s laughable to claim that “attackers only got access to the development server”
Many development servers use the production database, or a close copy of the production database. It’s nearly the same thing as accessing the production server.
Development servers often have an abundance of test code and data. The attackers “only got” a lot of stuff.
Nice… Thank You For Sharing…..
Hacker: I stole and made a copy of the exam answers. Its for sale.
Students: I’ll pay so I can cheat.
Threat Intelligence Co: I’ll pay so I can sell exam prep.
Some Journalist: Someone stole something from the teacher and it may affect the exam.
Brian Krebs: Jim distracted Mrs. Jones with his fake injury while Tom snuck in the classroom and cracked her laptop password using HIBP database that he decrypted the hash on the same password she used on Bumble to exfiltrate the exam keys for next weeks’ final exam and is selling it by way of a advertisement above the boy’s room middle urinal which reads “Send $10 to 667#### for a passing grade”
A witch! 😀
He’s got more patience for forum diving than any man ought.
For those reading the comments, the report in question exposing the group’s identities has been published to http://www.thedarkoverlord.info.
The actual data surrounding the “hack” will be published monday, along with all relevant evidence (server logs, etc).
The interesting Information Thank You