One of the most-read advice columns on this site is a 2018 piece called “Plant Your Flag, Mark Your Territory,” which tried to impress upon readers the importance of creating accounts at websites like those at the Social Security Administration, the IRS and others before crooks do it for you. A key concept here is that these services only allow one account per Social Security number — which for better or worse is the de facto national identifier in the United States. But KrebsOnSecurity recently discovered that this is not the case with all federal government sites built to help you manage your identity online.
A reader who was recently the victim of unemployment insurance fraud said he was told he should create an account at the Department of Homeland Security‘s myE-Verify website, and place a lock on his Social Security number (SSN) to minimize the chances that ID thieves might abuse his identity for employment fraud in the future.
According to the website, roughly 600,000 employers at over 1.9 million hiring sites use E-Verify to confirm the employment eligibility of new employees. E-Verify’s consumer-facing portal myE-Verify lets users track and manage employment inquiries made through the E-Verify system. It also features a “Self Lock” designed to prevent the misuse of one’s SSN in E-Verify.
Enabling this lock is supposed to mean that for the next year thereafter, if an unauthorized individual attempts to fraudulently use a SSN for employment authorization, he or she cannot use the SSN in E-Verify, even if the SSN is that of an employment authorized individual. But in practice, this service may actually do little to deter ID thieves from impersonating you to a potential employer.
At the request of the reader who reached out (and in the interest of following my own advice to plant one’s flag), KrebsOnSecurity decided to sign up for a myE-Verify account. After verifying my email address, I was asked to pick a strong password and select a form of multi-factor authentication (MFA). The most secure MFA option offered (a one-time code generated by an app like Google Authenticator or Authy) was already pre-selected, so I chose that.
The site requested my name, address, SSN, date of birth and phone number. I was then asked to select five questions and answers that might be asked if I were to try to reset my password, such as “In what city/town did you meet your spouse,” and “What is the name of the company of your first paid job.” I chose long, gibberish answers that had nothing to do with the questions (yes, these password questions are next to useless for security and frequently are the cause of account takeovers, but we’ll get to that in a minute).
Password reset questions selected, the site proceeded to ask four, multiple-guess “knowledge-based authentication” questions to verify my identity. The U.S. Federal Trade Commission‘s primer page on preventing job-related ID theft says people who have placed a security freeze on their credit files with the major credit bureaus will need to lift or thaw the freeze before being able to answer these questions successfully at myE-Verify. However, I did not find that to be the case, even though my credit file has been frozen with the major bureaus for years.
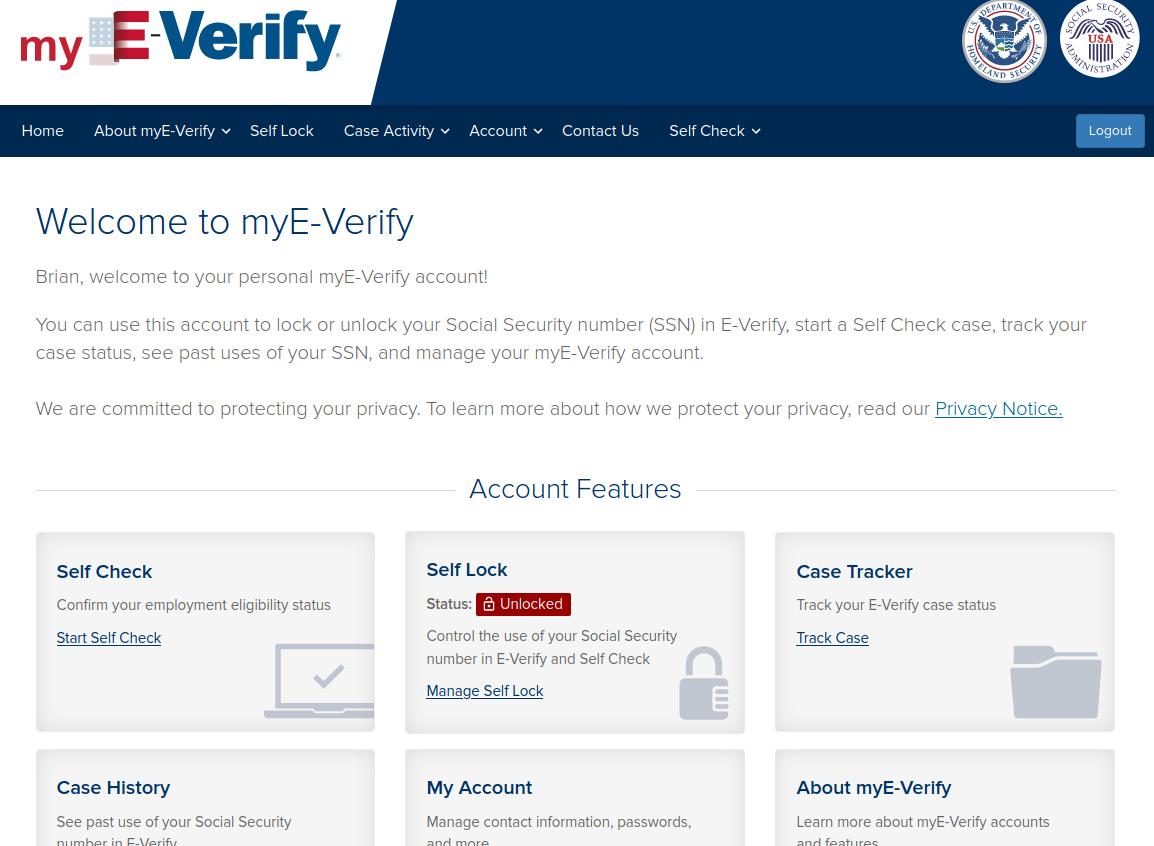
After successfully answering the KBA questions (the answer to each was “none of the above,” by the way), the site declared I’d successfully created my account! I could then see that I had the option to place a “Self Lock” on my SSN within the E-Verify system.
Doing so required me to pick three more challenge questions and answers. The site didn’t explain why it was asking me to do this, but I assumed it would prompt me for the answers in the event that I later chose to unlock my SSN within E-Verify.
After selecting and answering those questions and clicking the “Lock my SSN” button, the site generated an error message saying something went wrong and it couldn’t proceed.
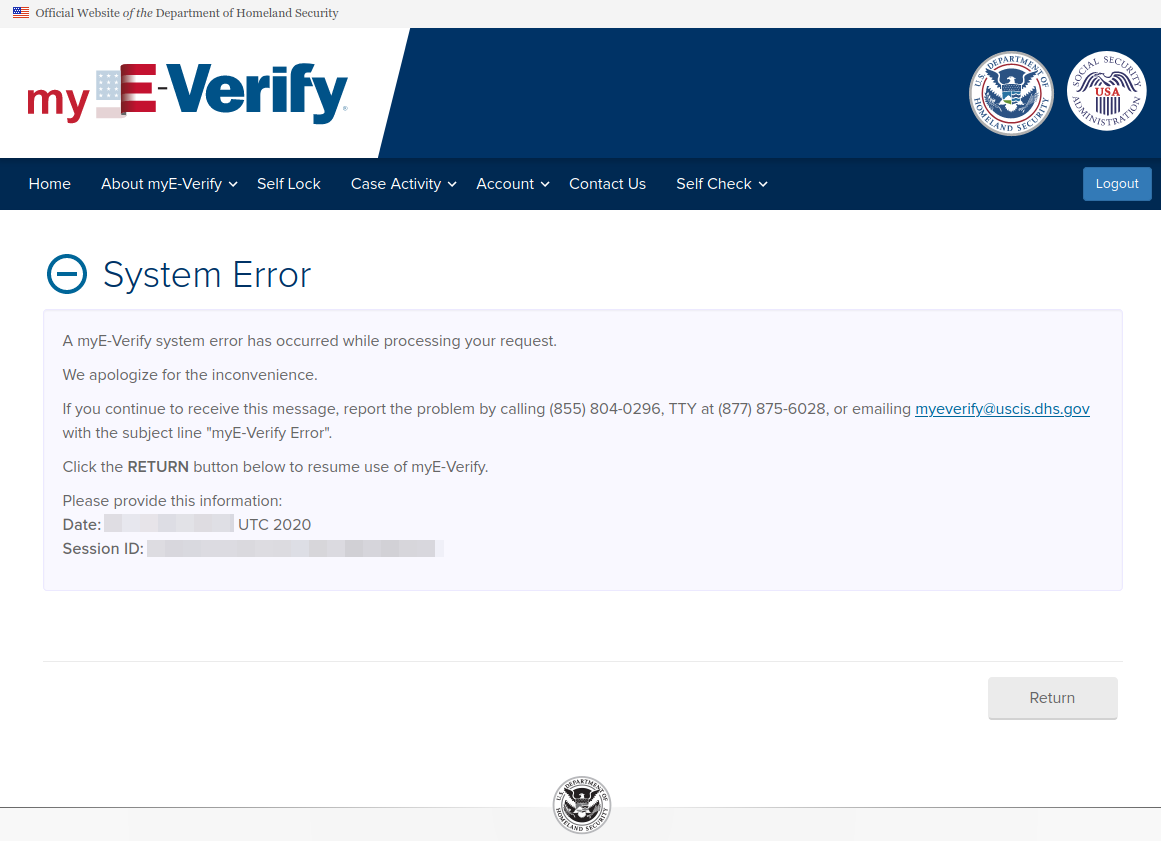
Alas, logging out and logging back in again showed that the site did in fact proceed and that my SSN was locked. Joy.
But I still had to know one thing: Could someone else come along pretending to be me and create another account using my SSN, date of birth and address but under a different email address? Using a different browser and Internet address, I proceeded to find out.
Imagine my surprise when I was able to create a separate account as me with just a different email address (once again, the correct answers to all of the KBA questions was “none of the above”). Upon logging in, I noticed my SSN was indeed locked within E-Verify. So I chose to unlock it.
Did the system ask any of the challenge questions it had me create previously? Nope. It just reported that my SSN was now unlocked. Logging out and logging back in to the original account I created (again under a different IP and browser) confirmed that my SSN was unlocked.
ANALYSIS
Obviously, if the E-Verify system allows multiple accounts to be created using the same name, address, phone number, SSN and date of birth, this is less than ideal and somewhat defeats the purpose of creating one for the purposes of protecting one’s identity from misuse.
Lest you think your SSN and DOB is somehow private information, you should know this static data about U.S. residents has been exposed many times over in countless data breaches, and in any case these digits are available for sale on most Americans via Dark Web sites for roughly the bitcoin equivalent of a fancy caffeinated drink at Starbucks.
Being unable to proceed through knowledge-based authentication questions without first unfreezing one’s credit file with one or all of the big three credit bureaus (Equifax, Experian and TransUnion) can actually be a plus for those of us who are paranoid about identity theft. I couldn’t find any mention on the E-Verify site of which company or service it uses to ask these questions, but the fact that the site doesn’t seem to care whether one has a freeze in place is troubling.
And when the correct answer to all of the KBA questions that do get asked is invariably “none of the above,” that somewhat lessens the value of asking them in the first place. Maybe that was just the luck of the draw in my case, but also troubling nonetheless. Either way, these KBA questions are notoriously weak security because the answers to them often are pulled from records that are public anyway, and can sometimes be deduced by studying the information available on a target’s social media profiles.
Speaking of silly questions, relying on “secret questions” or “challenge questions” as an alternative method of resetting one’s password is severely outdated and insecure. A 2015 study by Google titled “Secrets, Lies and Account Recovery” (PDF) found that secret questions generally offer a security level that is far lower than just user-chosen passwords. Also, the idea that an account protected by multi-factor authentication could be undermined by successfully guessing the answer(s) to one or more secret questions (answered truthfully and perhaps located by thieves through mining one’s social media accounts) is bothersome.
Finally, the advice given to the reader whose inquiry originally prompted me to sign up at myE-Verify doesn’t seem to have anything to do with preventing ID thieves from fraudulently claiming unemployment insurance benefits in one’s name at the state level. KrebsOnSecurity followed up with four different readers who left comments on this site about being victims of unemployment fraud recently, and none of them saw any inquiries about this in their myE-Verify accounts after creating them. Not that they should have seen signs of this activity in the E-Verify system; I just wanted to emphasize that one seems to have little to do with the other.




Once again, some very helpful and practical information. Thank you.
The use of extraneous ‘challenge questions’ might seem like poor security, but it’s always been my impression that these questions are a potential gold-mine of personal data freely given by consumers
Your use of ‘long, gibberish answers’ is somewhat like what I’ve been doing. I treat each one just like any password, recording it for later re-use at each website that requires such. But I haven’t yet tried using a straight copy/paste from GRC’s password generator. I bet the challenge site code wouldn’t care what I enter
I always lie on security questions. I had contacted citibank yesterday because I found a minor software problem and I was asked for a security question. The citibank employee was surprised when my reply was “I need to boot a computer to see what lie I used.” He never heard of anyone doing this. Then it was my turn to be surprised when a substitute for not answering the security question was to read back a number sent via SMS to my cellphone. I could have been a sim-jacker.
The last bank I contacted about a security issue told me that as a non-customer I am not eligible to to so.
I had a bank try to go down that road with me once. I suggested that they either talk to me now, or they will be answering to my lawyer. Amazingly, they then decided that they could talk to me, “this time”.
Than at that point you bring up the security issue on Facebook, Twitter, Nextdoor or whatever social media platform you find most efficacious. Corporate America hates to get shamed on social media, especially banks…
You certainly can use random alphanumeric strings – often including special characters; there’s usually no input validation on those things. But as Gary mentions, you may be asked them over the phone, so it may be better to use a string of random words for ease of use.
Back in my student days I used to pick up whatever book was on my desk and use a random phrase from a random page. There’s nothing like telling a confused CS rep that your first holiday was in the socially (re)produced construct of childhood, or something.
What could be more satisfying than spending an hour or so, describing 128 random characters to some helpdesk drone?
“That’s upper case g, tilde, lower case u, underscore. ampersand, zero, upper case o, backtick, lower case l, circumflex, …”
All this got me thinking.
Even with normal words, unless the drone and customer are using the same language/keyboard, stuff like the acute accent could be lost in translation.
I use random character strings and frequently get to recite them to CSRs. It isn’t a big deal / doesn’t seem to phase them. Although it’s pretty clear it’s atypical.
I’d definitely recommend against special Unicode (especially non Latin characters) or Emoji.
“Security Questions” are always a hoot. I never answer truthfully, of course, and I used to have “Mothers maiden name” set to “Garlic Boulder” at one bank. The clerk who had to ask me the Q/A was perplexed. After some back-and-forth, we resolved it, and the transaction completed. At the end of the call, the clerk said “Excuse me for asking, but is your mother Native American, or where is that name from?” 😀
I’m guessing the reason the answers to your credit questions were always “none of the above” was that it couldn’t get to your credit reports since they were locked. It made up n-1 wrong answers and had to use “none of the above” for all the right ones.
Which is TERRIBLE. If a bad guy knows you lock your credit reports, he can easily impersonate you because he knows all the answers will be “none of the above.”
Yeah, that was my take as well. Which makes me wonder what happens if the “random wrong answer generator” accidentally generates the right answer? It would be unlikely, but certainly possible.
The best website for I’ve seen on the internet for the best secure login is the global bank HSBC , where they send you a security token that provides the 6 digits codes for the two factor authentication .
The United States government could be doing this type token based security setup with the IRS , V.A. and Social Security websites
I would highly recommend people check out HSBC security practices. I had to send them a rent credit report on myself , by way of a verified email account to identify that I was the real person applying for the credit card. I never seen any bank do this in the last thirty years of me applying for credit.
I’m banking with HSBC and also thought that token was a good thing.
Only that they’ve effectively taken it out of service again, reverted to passwords, telling their customers that’s a good thing. When I inquired about that, they essentially told me that it’s just as secure with the password as it was with the token. Not much point in taking that discussion further, because the people replying to customer questions clearly work from a script and have no clue themselves.
Further, the limits on the password are pretty grueling: no spaces, no capitalization, no special characters.
Further, as soon as I enter my account number, I’m greeted by name. That’s just bad.
A couple of years ago, I asked to get the certificate fingerprint of their login server, quite possibly prompted by an article on this site. They clearly didn’t know how to deal with that request – it went back and forth a bunch of times, until they asked me to fax my request to their security team. Which I didn’t do.
So, yes, maybe someone should check out their security practices – I, for one, would find that highly interesting.
HSBC tried hard to induce me to use a phone app instead or replacing the dead-battery token generator. I told that I won’t link my bank to my phone for security reasons, and that stopped that.
If you want any information about the security certificate for their login server, the most direct way is to simply click on the lock icon in your browser and navigate from there.
One of the most surprising things to me is that some hosting sites can use a certificate issued to their server name but with an alias for any URL they need to act as via DNS.
I’ve been told Lexus-Nexus was a way of freezing credit data (SSN etc). True or ?
Actually Lexus is a carmaker.
I call your pendantry and raise you: Lexus is actually a brand of the carmaker Toyota!
You would not believe how well my new Nexus handles.
Nexus is useless while the border’s closed.
No one is calling you on “pendantry?”
No-one could afford to call after I raised…
Actually LexisNexis is a very extensive data aggregator of public and law enforcement records. They also provide search engines for various research publications.
LOL, I think they were spoofing on the mis-spelling of “Lexis” as “Lexus”.
Either way, we had fun 🙂
One of the prompts said the KBA comes from Experian, but I also have a lock on my credit report, and it asked me a bunch of questions correctly answered none of the above, and there I was.
On the other hand, I did a self check to see if I’m eligible to work in the US, and it came back as I Dunno, both with my SSN and my passport. I know my passport is OK, it’s linked to my NEXUS card and the DHS trusted traveller site assures me everything is dandy.
Since I’m not planning to look for a job any time in the next decade, I Dunno is probably a good answer.
I like challenge and response when you get to make up your own questions… the answers are burned into your brain but unguessable
then your security is as good as the website that is going to save your answers as plaintext and then get hacked..
I missed the earlier tip to claim the eVerify site (having claimed all the others and locked my credit report as suggested by you.) Thanks for this article.
The only KBA that wasn’t NOTA would have been easy for a crook to figure out (what state was your SSN issued in?)
As for the challenge questions, I too use inaccurate alpha answers combined with numerics, then store them in my iCloud Keychain for easy retrieval.
Should also note the set up discriminates against expats as the phone number is limited to a US-centric 10-digit number. I used 777-777-7777 (this is an unused area code and chose to get the 2FA code sent to my email address) and the setup accepted it.
I’d suggest using 777-555-0100 in the future [1].
There was a time when xxx-555-xxxx was assumed to be reserved. But then exchanges got desperate and started releasing things. If they aren’t validating the number, then you’d want to use a number that will never be released, otherwise someone might eventually get the number and be able to take over your account.
Personally, I have a GVoice number (which I got after I became an expat) which works pretty good for most things.
[1] https://en.wikipedia.org/wiki/555_(telephone_number)#Fictional_usage
Better to also keep that unique pw in a reputable pw warehouse that syncs with all ur devices
Brian, Did you contact E-Verify to see what they had to say for themselves about this obvious vulnerability?
Mr. Rose asks the obvious question. As thorough as Mr. Krebs is, I am surprised that he made no mention of at least an attempt to reach out to the DHS eVerify folks.
In any event, keep up the great work, Mr. Krebs. I learn each time I read one of your posts and on top of that, you remind often of me how careful I need to be with my online accounts, etc.
David! Ugg.
Giving a long gibberish answer is a very bad thing to do from a security perspective. After you do that, if I try to impersonate you, I’ll be challenged with a question such as this:
In what city were you born?
A. Philadelphia
B. Los Angeles
C. xlk9807sdflkj33332-3
D. Dodge City
Faced with that choice, I’ll pick C of course.
Franklin, the answers aren’t shown as multiple-guess when the secret question is asked. I think you’re confusing that with the knowledge-based authentication questions.
Correct, ‘sensei’
It worse than that.
A lawyer acquaintance of mine has had his SSN payments redirected twice despite:
1) Locking his account
2) Removing all online access to said account
What he finally did, on my advice, was to have SSA put a completely unique identifier in his file and to only change payout info if that identifier is correctly repeated.
He didn’t lose any actual payments because he reads all his mail – and saw both SSA physical notifications that his payee info was changed, but I can easily see how that could have been circumvented as well.
c1ue:
Re: “… have SSA put a completely unique identifier in his file and to only change payout info if that identifier is correctly repeated …”
Can you possibly expand on your recommendation re: a “unique identifier” on-file w/ SSA ?
The concept seems quite sound and understandable, what what … EXACTLY … does one request when dealing with the SSA?
(assuming that it’s the first time any particular SSA agent might have ever heard of it)
I’m sure others on this forum would be interested as well.
@JLW
the standard SSA security questions are laughably simplistic and almost all are open source accessible.
What was done in this case was to insert a specific question and answer which was unique to just this SSA verification into this user’s file, and to lockout any and all other methods to change payment details.
I won’t say what this particular question and answer is, but you can determine one for yourself: something which is not on social media, is not documented publicly and is not used elsewhere.
C1ue:
Thank you.
I have learned more about security to help protect myself from Krebs On Security than anywhere else on line. What a great job Krebs does.
Why do you have to protect yourself from Krebs on Security
Well if he’s a criminal, that would be pretty obvious wouldn’t it? 🙂
Well, a SWAT team once felt that mischief was afoot at his house.
i just wish Kerbs would stop asking email address when posting comments.. just good practice..
Not sure what you’re complaining about. You seem to have figured out that I don’t care if you put a real address in there or not. You can still leave a comment.
…yeah, santa@northpole.com must get a lot of email…
some of us do actually live in north pole, ak. please do not disrespet the bearded fat guy with the chainsaw. he’s waiting for the mail thieves so he can follow them home and sign their address up for christian newsletters, mormon visits, etc
I think the main thing is to allow people to use a gravatar if they please…
Sounds like you deserve a bug bounty payout.
Again, the USA who claims to be leading in IT is way behind.
Where is your digital ID ? In Denmark all citizens (with the exceptions of a few older, homeless etc) do have a national digital ID.
When I log on to a site that needs to verify my identity (being bank, govenment, health etc), I log on with my personal selected userid (or SSN), password, and then I get a push message to the digital ID app, saying that website X wants to log you on – Accept ?
All websites must be registered, and pay a fee of either $0.15/logon or pay slightly more (< $1) per named user for unlimited logons per year.
This works, and even the local eBay supports it, giving the seller the option to register as a "Verified" account. Then eBay pays that one-time government logon for of $0.15.
Many folks here are opposed to the creation of any type of national identification. The creation of the “Real ID” program has somewhat created one already though so. ♂️
…you already have a national id in the US – it’s your SSN…
So… how many states does Denmark have?
What? Denmark isn’t made up of dozens of individual sub governments, each with their own unique history and systems for administration? Denmark didn’t fight a war for independence from a foreign monarchy and thus doesn’t have a deep rooted suspicion of concentrated power structures?
Yes, the US does lead in IT
But our history is simultaneously the reason for being a world superpower, practically inventing the Internet,… and the reason why something so “simple” as a national ID is very difficult to swallow.
Sorry, this is pure American redneck insanity. European countries do have this history of “subgovernments” on a most spectacular level like ie Germany, and some countries with national id cards were occupied by a ton of foreign powers. The data strategy critical for day-to-day life and also in the case of loss of territorial integrity. And no, you can not find this data on any darkweb.
National ID sounds great in theory; in practice, it is terrible. Because it is just like any other common and repeatedly used form of ID: once compromised, it is forever compromised.
And it is worse than that: a national database is incredibly valuable to fraudsters, meaning they will go through enormous efforts to attack it.
The national ID databases for every single country have likely already been compromised multiple times.
It would be super helpful to have a list of these websites:
““Plant Your Flag, Mark Your Territory,” which tried to impress upon readers the importance of creating accounts at websites like those at the Social Security Administration, the IRS and others before crooks do it for you. ”
I especially enjoyed getting the credit questions incorrect 3 separate times and now having to wait 72 hours before trying again to prove my own identity. Then I wondered if maybe all my adblockers and script blockers were the culprit behind this. I guess I’ll find out in 3 days, but at least any one else who wants to try will have to wait as well, right?
As always superb security info from Mr Krebs.
As I read thru the article, I kept anticipating DHS’ “response” to Brian’s inevitable query.
However, it never came.
Brian … what does DHS (the owner of E-Verify) have to say about this?
How does one detect unemployment fraud?
Regarding security Q&A, starting a few years ago I always create random-ish UNIQUE answers to security questions and store the Q&A pairs in a password manager’s corresponding entry that already contains the user/name password for the site. For example: if the password manager has a stored entry for insurancecompany.com, that entry shows the user id and password and it also shows a notes field, which is where I paste the Q&A pairs.
When someone exfiltrates the hashes, have fun cracking them Q&A or doing anything with them if cracked, which would result in polluted useless data being associated with my stolen info already accumulating in online databases of stolen material.
“Either way, these KBA questions are notoriously weak security because the answers to them often are pulled from records that are public anyway, and can sometimes be deduced by studying the information available on a target’s social media profiles.”
Absolutely.
A couple of years ago one of the KBA questions posed to me was an OLD address of mine. I could not recall the address, but found it on the internet in a few minutes.
So, when it comes to “planting one’s flag”, I gather it’s a complete waste of time to do it with the DHS E-Verify, correct?
Is there a list of places where one should plant ones flag?
Thank you
I wonder if the “none of the above” KBA answers weren’t *because* your credit bureau information was locked. I can imagine a programmer who gets a null/failure response from a credit query might choose a random answer rather than going to the trouble of writing an elaborate error UI.
Curiou as to how this relates to the Equifax and Experion login verification system. I have been frustrated to no end by the security question ‘Our records indicate you recently took out a loan on your property. Please verify the banking institution that financed this loan:’
The multiple choice system then lists several banks and the ‘none of the above’ option.
As I have no mortgages or lines of credit attached to my property I find this question troubling. Does the verification system know something I don’t know? I have attempted to contact both major credit card companies about this (since 2015) and get only this response: The verification system is operated by a separate company. We have nothing to do with it and can’t answer your questions. We do not have any contact information for the verification services company.’
As I recall, the verification system was blamed early on in the Equifax breach as having been the intrusion avenue.
Have these companies become the scapegoat (liability shelter) for larger
companies?
I suspect in my situation that the ridiculously misleading question was written by someone who believes everyone lives on credit and that everyone carries a mortgage.
Thanks to all for the insight. As a small business person who does not have the resources (time or money) to put a full time security team in place, and appreciate all of the articles and discussions that take place here.
Curio s/b Curious. Sorry,
…the attacker does not know if you have a mortgage or not…
…the intent is that if you pull random factiods out of your credit record only you will know if they’re true and which one is true…
…it’s not perfect but it’s not bad either…
…multiple email addresses to one SSN – now that’s a problem…
‘Our records indicate you may have taken out a mortgage…..’ would be just as effective and not so alarming.
The phrase ‘Our records indicate you have taken out a mortgage’ was written by someone who did not put much thought into it.
…the current message is “According to your credit profile, you may have opened a mortgage loan in or around month year.”…
…not sure what you saw but that’s plain…
I tested the system last month. If the wording has been changed it was done only recently.
I cannot respond to your other comments as I have trouble understanding fragmented sentences, and elipses offer too many variables.
The whole system needs a revamp. My whole identity was stolen, numerous credit cards applied for while I was overseas. Mail stolen, etc. I can’t even get the 3 credit reporting agencies to put a credit freeze on my SSN. Only 2 of them would even do it without requiring endless additional impossible verification for someone that isn’t even in the US such as sending copies of social security card and utility bills for my “address” that isn’t even mine because I live overseas not in the US where these people are applying for the cards. It’s pathetic. Just waiting for my brokerage account and everything else to be drained. No wonder everyone is investing in bitcoin. It’s the only account which you control the security not some third party. I sent letters to the irs, ssa, 3 credit report agencies and chex systems. Chex systems stop them from cashing checks with your info.
Thank you!
Thank you for your work and your identification of the many issues with security questions. The site asks for this cognitive effort, and then what does it provide? A way to find out if my identity theft has been successful?
What is the actual benefit?
And when there is no benefit what does that do to people’s trust in security advice?
Asking people to complete cognitively infeasible task is an excellent way to ensure they do not do so.
MFA can be used by humans. Creating multiple random answers for security question is not feasible. So we have basically one password – our email – for recovering all these accounts.
Password creation and recall is only feasible for humans to the extent it is worthless as passwords in the absence of a password manager.
People will not do cognitively impossible things to ensure their security.
So don’t ask them to.
Thanks for the info, Brian.
What’s the likelihood that blockchain will be leveraged soon to enhance security, decentralize these legacy databases and prevent these issues?
I know I’m late to the party here, but did you contact and responsibly disclose this first or do you subscribe more to the idea of full disclosure?