Ubiquiti, a major vendor of cloud-enabled Internet of Things (IoT) devices such as routers, network video recorders, security cameras and access control systems, is urging customers to change their passwords and enable multi-factor authentication. The company says an incident at a third-party cloud provider may have exposed customer account information and credentials used to remotely manage Ubiquiti gear.
In an email sent to customers today, Ubiquiti Inc. [NYSE: UI] said it recently became aware of “unauthorized access to certain of our information technology systems hosted by a third party cloud provider,” although it declined to name that provider.
The statement continues:
“We are not currently aware of evidence of access to any databases that host user data, but we cannot be certain that user data has not been exposed. This data may include your name, email address, and the one-way encrypted password to your account (in technical terms, the passwords are hashed and salted). The data may also include your address and phone number if you have provided that to us.”
Ubiquiti has not yet responded to requests for more information, but the notice was confirmed as official in a post on the company’s user support forum.
The warning from Ubiquiti carries particular significance because the company has made it fairly difficult for customers using the latest Ubiquiti firmware to interact with their devices without first authenticating through the company’s cloud-based systems.
This has become a sticking point for many Ubiquiti customers, as evidenced by numerous threads on the topic in the company’s user support forums over the past few months.
“While I and others do appreciate the convenience and option of using hosted accounts, this incident clearly highlights the problem with relying on your infrastructure for authenticating access to our devices,” wrote one Ubiquiti customer today whose sentiment was immediately echoed by other users. “A lot us cannot take your process for granted and need to keep our devices offline during setup and make direct connections by IP/Hostname using our Mobile Apps.”
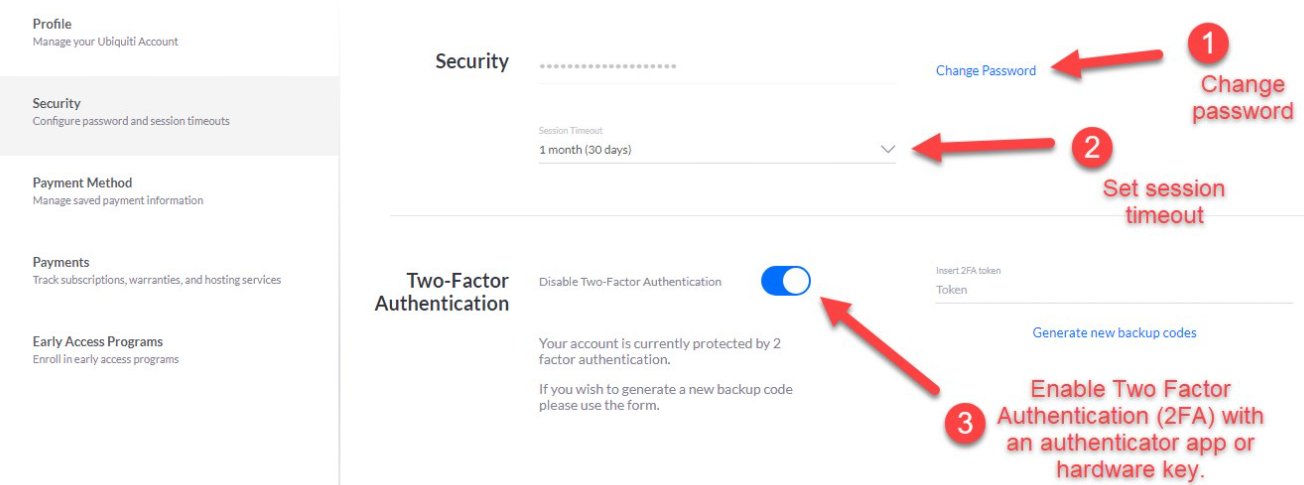
To manage your security settings on a Ubiquiti device, visit https://account.ui.com and log in. Click on ‘Security’ from the left-hand menu.
1. Change your password
2. Set a session timeout value
3. Enable 2FA
According to Ubiquiti’s investment literature, the company has shipped more than 85 million devices that play a key role in networking infrastructure in over 200 countries and territories worldwide.
This is a developing story that may be updated throughout the day.




This is in regards to the UI breach. While changing my password and turning on 2FA this afternoon, I discovered that the store.ui.com website does NOT ask for the 2FA answer and logs in with only the username and password. Luckily the authentication doesn’t allow access to the rest of the UI sites (Unifi, Protect, Account).
I previously returned a Unifi Dream Machine specifically because they required it to be activated through their cloud service.
I’m glad to no longer have any of their devices, but I still received their change password email.
Yeah, this about sums it up. Thanks for the reminder on how to change it. Was Googling steps on how to change the password. As a rule of thumb, I don’t use the links in emails to change passwords.
Good point, trusting emailed links is a teachable moment itself.
Internet of One damned Thing after another strikes again!
Do you think the new US policy will help at all?
And this:
https://krebsonsecurity.com/2015/08/tech-firm-ubiquiti-suffers-46m-cyberheist/
It’s not clear to me, a home user with a single product (wap) who has never accessed their cloud. Do I need to follow this alert? Furthermore it seems I must have a device or app to use 2FA, I have neither. Would appreciate a clarification from someone “in the know”.
Jon, we’d need more info to answer your question.
1) Which Ubiquiti access point do you own?
2) Are you using UniFi controller/what version is it?
General info: Almost any somewhat recent UniFi-series device would have required you to make a Ubiquiti account during setup. The easiest way I can think of to see if you need to do anything is to go to ui.com and click forgot password. If you get a reset email after entering your address, it usually you do have a Ubiquiti cloud account.
As far as a 2FA device, they support using your usual iOS or Android authenticator app (Google/Authy) so you would not need to get any sort of hardware key or device.
Of course, if you learn via the reset password technique that you don’t have a UI account, then nothing to worry about!
Travis: Thanks for info. I have an AC Pro on controller 6.0.36
The AC Pro hangs off my LAN behind a firewall & router, not directly exposed to a WAN.
I don’t use the controller for dns or dhcp. I only use it to define wifi networks.
I know there is a controller update but I decided to wait on the update because the new UI is really annoying and I don’t need all that extra stuff. There is also a firmware update pending and based on the email I got from ubnt.com I guess I have to assume I do have a login. I do have a userID at community.ui.com.
Thanks for clarifying the 2FA requirements.
As a home user i wouldn’t be concerned. I actually turn off my remote access for my Ubiquiti equipment. If you are just using it at home with no need to edit things remotely its the best way to go.
Exactly…remote admin for *any* Internet facing device should be disabled, most vendors of home + small/medium office routers have been found with their security pants down in recent years… Setup a VPN if you need access remotely.
Thanks. I never turned on RA. So I guess I’m good to go.
Seconded. I’d distrust remote access on any bog-stock gateway,
given what we’ve seen from Cisco, Netgear, Dlink etc etc.
Not just the vintage gear, the new stuff has brand new vulns.
Arrayed FPGU’s and digital diodes, that’s the only way to be sure. /s
Just deployed a Cloud Key Gen2 as was annoyed about the mandatory tie-in to ui.com. Thankfully [I think], I never would put an “app” on my cell phone for anything like this. Additionally, searching for too long, I found the toggle in the browser management tool to disable the cloud hook. It’s off now.
There is usually no reason to even sign up with Ubiquiti cloud service for home users. I found it was better to just install Unifi package on a linux server to manage the devices. Of course, this trend of “Everything Cloud” means Ubiquiti’s setup defaults to using their Cloud Key, which is how they allow remote access.
Security best practice: Use VPN and local administration for smaller non-enterprise networking devices.
I’ve requested my password be reset about 10 times since I got the notification and still haven’t received a single password reset email. Great job Ubiquiti.
Same here, this is ridiculous
The password reset email was slow to come through, however it did finally come through about 15 minutes later.
The request to change password in the Ubiquiti controller returns a reset via the registered email address. If no email address is left with Ubiquiti, no reset email will be sent.
Full email received from Ubiquiti below:
Dear Customer,
We recently became aware of unauthorized access to certain of our information technology systems hosted by a third party cloud provider. We have no indication that there has been unauthorized activity with respect to any user’s account.
We are not currently aware of evidence of access to any databases that host user data, but we cannot be certain that user data has not been exposed. This data may include your name, email address, and the one-way encrypted password to your account (in technical terms, the passwords are hashed and salted). The data may also include your address and phone number if you have provided that to us.
As a precaution, we encourage you to change your password. We recommend that you also change your password on any website where you use the same user ID or password. Finally, we recommend that you enable two-factor authentication on your Ubiquiti accounts if you have not already done so.
Does 2FA on their site also need to be reset? It makes me wonder, where do these types of sites store their 2FA keys that generate the secret key? Is it on their servers? They do not seem to say.
still waiting for the logon email (2FA)
Hope this means there is just a flood of requests to log in and not a hacked account
I ordered my first Unifi AP last week actually, unaware of the online account requirement. I totally wouldn’t want my networking gear to have any cloud dependencies, or even vendor pushing that direction. Other than being insecure, that’s a circular dependency.
Glad this is exposed now before my order arrived. I will just return it without opening the shipping box…
It’s a disgrace!
First they changed the way you authenticate *locally* – without any big announcement. I was having trouble to log into my own UI hardware using local credentials. Then I realized they bundled that with the UI server account. All “introduced” by a simple firmware update. Now this.
What a nightmare. If I would not have spend hundreds of Euros for my home infrastructure I would throw all of this out immediately.
Shame in UI!
The easiest way to fix this is to install OpenWRT on your hardware. Corollary: don’t buy hardware that doesn’t support OpenWRT; fortunately my Ubiquity APs are supported. Quite well in fact.
You can’t hijack remote management on a device that doesn’t have any.
In my experience OpenWrt is really nice but rarely fully supports all the proprietary chipsets involved, thus leaving your with a device at a fraction of its stock capabilities.
I look at the openWRT “supported hardware” list and make purchases based on that.
I have a few UAP-AC-LITE APs that I don’t recall having to sign up to a Ubiquiti account for.
I’ve put a few of the possible emails that I might have used if I did indeed sign up and all have come back as ‘Not found’
I managed the APs by using the Unifi Controller (5.9.29) that opens the dashboard on a locally hosted website. I’ve changed the password to log into this just in case.
I’ve seen in a few places that Remote Management should be turned off but in the settings, there isn’t an option for Remote Management, only Cloud Access which is disabled.
I am concerned I might have overlooked something so am wondering if there’s anything I can do to ensure I am not exposed?
I left Ubiquiti due to their obsession with making everything SSO through the cloud, in addition to the shady way they handled the device phone-home fiasco…
The UniFi Protect mobile apps could not log on to see your CCTV cams without internet, even if you were on the same network…
Looks like Cisco are going after the UniFi markets though with their new SMB AP/Switch/Router range, so be interesting to see how this plays out…
If there was any doubt about whether UI and every single one of their products are amateur hour before…
Another OpenWRT user here, I will only buy devices that are on their supported hardware list.
Also, remember to generate backup codes from the settings pannel. I lost my phone with my authenticator 2FA app on it and had to work with customer support to turn off 2FA and then log in, re-enable it with my new phone/google authenticator app. So once you enable, make sure you store the hard coded backup passwords…
If you use LastPass authenicator, a separate app, and is compatible with Google Authenicator and others, the 2FA codes are encrypted locally and backedup to their cloud server so you won’t lose them when your old phone craters or lost or stolen. Now if you don’t trust cloud servers in the first place, then so be it.
“authenticator”
It is curious that 2 days after this change your password email I get a spoofed blackmail from a korean IP address…I cannot prove the link between the two fact however. Lucky Ubiquity.
“We take the security of your information very seriously…”
If they did, then why the [redacted] was the data on a “third party cloud provider” service in the first place?
Seriously? If it’s not on your hardware, you don’t own it. That applies not just to you and me, but to businesses as well.
I don’t have two factor authentication and Facebook is requesting it for me to login, help
hey Krebs, according to this post, someones creds were in a dump back in September of last year.
https://community.ui.com/questions/possibly-breach/55bc757a-9caf-4889-a2c4-9ad5d8af75ce#answer/f2322adf-d9b6-47dc-9183-abe6e4c9c3b5
Can you check the sites like you normally do on this one to see if anyone is selling the dump or if they are included with other dumps? I smell something fishy here with how UI is handling this. They are ghosting their community on their own forums lol
AFAICT, that’s not a warning from UI but from Safari, which is saying the email address and password the person who posted that screenshot was using for their UI account was found in another database that was exposed and leaked online. Usually, this is a warning served to someone who is trying to re-use credentials they used at another site that got hacked. This is a poor security practice by the user and is probably the #1 cause of account takeovers online.
yes that may be the case, or it could be they used a unique password for ubiquiti. however, i would assume many others would be posting screenshots like this if that were the case.
I have tried to avoid their cloud service as long as possible and just recently decided to use it to access my UI Protect Cameras (Cloudkey gen2 + a few G4 cameras)
After their announcement I immediately changed my password and activated 2FA. Web Login/iOS Apps required me to enter my new credentials, which was expected of cause, my UI Protect App on my AppleTV however is still accessible w/o entering my new pw +2FA even two days after. Can still access my camera streams and the controller with the old, possibly compromised login. Great – this gives me so much confidence in UI… How can this happen?? Luckily I only use their protect stuff and Access Points… looks like I need to replace these all and block internet access for all UI stuff until then.
I keep remote access disabled on my Amplifi HD, for precisely scenarios like this. I also turn off “find my device” functionality on all my phones and tablets, so even if someone hijacks my Google account, they can’t lock me out or wipe my files.
trying to get 2fa
Web Login/iOS Apps required me to enter my new credentials, which was expected of cause, my UI Protect App on my AppleTV however is still accessible w/o entering my new pw +2FA even two days after.
Thanks for sharing this nice article. How can change my password ?