New data suggests someone has compromised more than 21,000 Microsoft Exchange Server email systems worldwide and infected them with malware that invokes both KrebsOnSecurity and Yours Truly by name.

Let’s just get this out of the way right now: It wasn’t me.
The Shadowserver Foundation, a nonprofit that helps network owners identify and fix security threats, says it has found 21,248 different Exchange servers which appear to be compromised by a backdoor and communicating with brian[.]krebsonsecurity[.]top (NOT a safe domain, hence the hobbling).
Shadowserver has been tracking wave after wave of attacks targeting flaws in Exchange that Microsoft addressed earlier this month in an emergency patch release. The group looks for attacks on Exchange systems using a combination of active Internet scans and “honeypots” — systems left vulnerable to attack so that defenders can study what attackers are doing to the devices and how.
David Watson, a longtime member and director of the Shadowserver Foundation Europe, says his group has been keeping a close eye on hundreds of unique variants of backdoors (a.k.a. “web shells”) that various cybercrime groups worldwide have been using to commandeer any unpatched Exchange servers. These backdoors give an attacker complete, remote control over the Exchange server (including any of the server’s emails).
On Mar. 26, Shadowserver saw an attempt to install a new type of backdoor in compromised Exchange Servers, and with each hacked host it installed the backdoor in the same place: “/owa/auth/babydraco.aspx.”
“The web shell path that was dropped was new to us,” said Watson said. “We have been testing 367 known web shell paths via scanning of Exchange servers.”
OWA refers to Outlook Web Access, the Web-facing portion of on-premises Exchange servers. Shadowserver’s honeypots saw multiple hosts with the Babydraco backdoor doing the same thing: Running a Microsoft Powershell script that fetches the file “krebsonsecurity.exe” from the Internet address 159.65.136[.]128. Oddly, none of the several dozen antivirus tools available to scan the file at Virustotal.com currently detect it as malicious.
The Krebsonsecurity file also installs a root certificate, modifies the system registry, and tells Windows Defender not to scan the file. Watson said the Krebsonsecurity file will attempt to open up an encrypted connection between the Exchange server and the above-mentioned IP address, and send a small amount of traffic to it each minute.
Shadowserver found more than 21,000 Exchange Server systems that had the Babydraco backdoor installed. But Watson said they don’t know how many of those systems also ran the secondary download from the rogue Krebsonsecurity domain.
“Despite the abuse, this is potentially a good opportunity to highlight how vulnerable/compromised MS Exchange servers are being exploited in the wild right now, and hopefully help get the message out to victims that they need to sign up our free daily network reports,” Watson said.
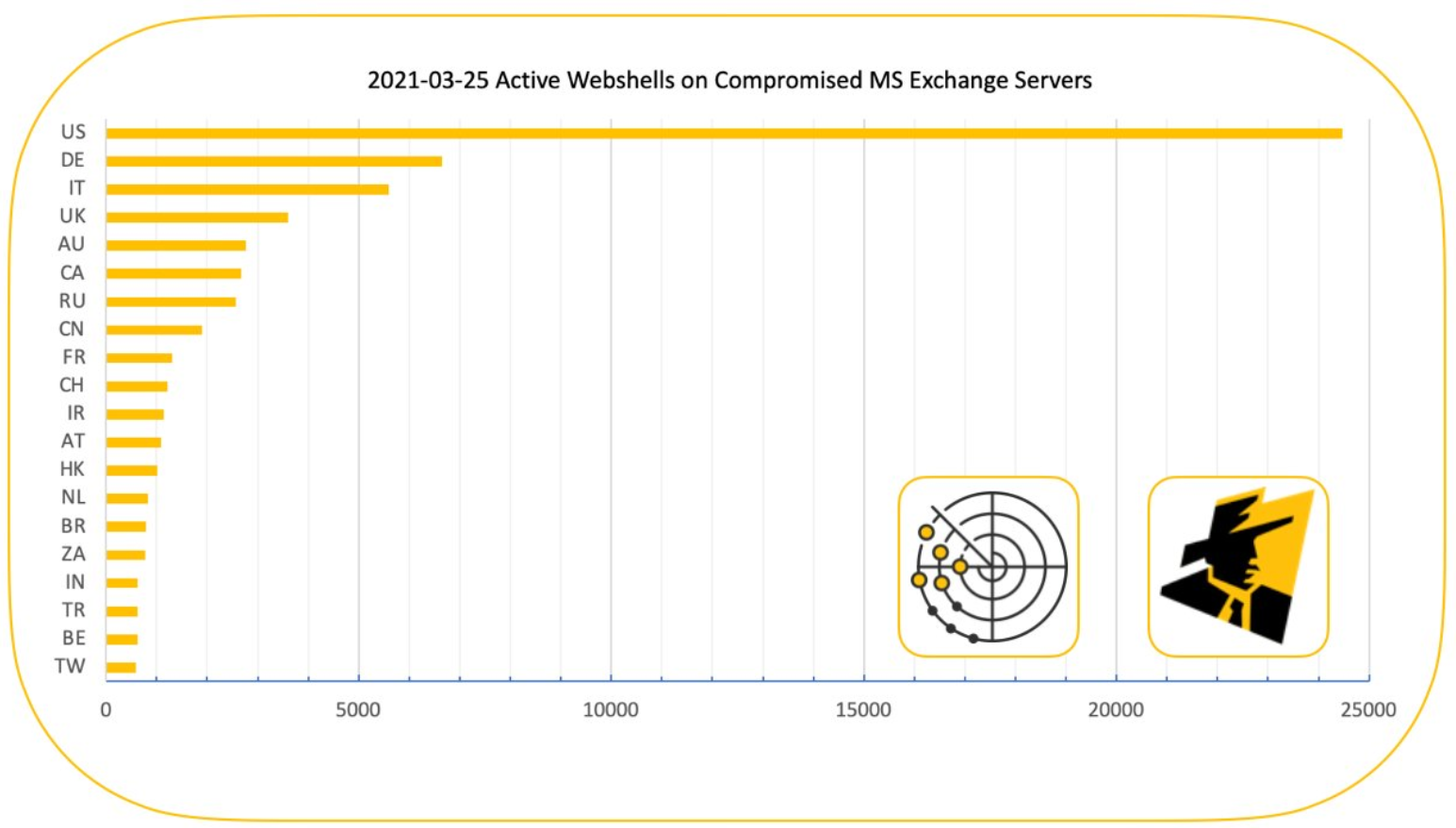
There are hundreds of thousands of Exchange Server systems worldwide that were vulnerable to attack (Microsoft suggests the number is about 400,000), and most of those have been patched over the last few weeks. However, there are still tens of thousands of vulnerable Exchange servers exposed online. On Mar. 25, Shadowserver tweeted that it was tracking 73,927 unique active webshell paths across 13,803 IP addresses.
Exchange Server users that haven’t yet patched against the four flaws Microsoft fixed earlier this month can get immediate protection by deploying Microsoft’s “One-Click On-Premises Mitigation Tool.”
The motivations of the cybercriminals behind the Krebonsecurity dot top domain are unclear, but the domain itself has a recent association with other cybercrime activity — and with harassing this author. I first heard about the domain in December 2020, when a reader told me how his entire network had been hijacked by a cryptocurrency mining botnet that called home to it.
“This morning, I noticed a fan making excessive noise on a server in my homelab,” the reader said. “I didn’t think much of it at the time, but after a thorough cleaning and test, it still was noisy. After I was done with some work-related things, I checked up on it – and found that a cryptominer had been dropped on my box, pointing to XXX-XX-XXX.krebsonsecurity.top’. In all, this has infected all three linux boxes on my network.”
What was the subdomain I X’d out of his message? Just my Social Security number. I’d been doxed via DNS.
This is hardly the first time malware or malcontents have abused my name, likeness and website trademarks as a cybercrime meme, for harassment, or just to besmirch my reputation. Here are a few of the more notable examples, although all of those events are almost a decade old. That same list today would be pages long.
Further reading:
A Basic Timeline of the Exchange Mass-Hack
Warning the World of a Ticking Timebomb
At Least 30,000 U.S. Organizations Newly Hacked Via Holes in Microsoft’s Email Software
Microsoft: Chinese Cyberspies Used 4 Exchange Server Flaws to Plunder Emails




Brian,
Are you able to secure a trademark for your name as a business enterprise to protect it?
Why would criminals care about trademarks anyway?
It’s not about asking the criminals nicely, it’s about having a tool to issue a takedown request with the host or registrar.
Takes a long time to utilize squatting laws.
As the other commenter explained, a trademark gives you certain legal powers. It’s similar to what happens when (this is a made-up example but it happens all the time) a huge company like Burger King sues some startup in Alabama who named his roadside burger stand Mr. Burger King.
… and people with the last name “McDonald” are sued if they try to open a restaurant with that name.
Me and the McDonald’s people, we’ve got this little misunderstanding. See, they’re “McDonald’s”. I’m “McDowell’s”. They’ve got the golden arches. Mine are the golden arcs. They’ve got the Big Mac. I’ve got the Big Mick.
Haha that was a blast from the past!
Common Law Trademark Rights exist in the United States. So yes, he already has them…. and IP rights generally as you can see by the (C) on this website footer.
https://www.justia.com/intellectual-property/trademarks/unregistered-trademarks/
Do you think hackers care about laws? Hacking is against the law a federal crime, also these hackers are probably the same chinese hackers that breached microsoft earlier in the year , this is the fourth time microsoft has had a breach in less than 6 months.
However I think when storing trademark in a world that you can literally steal files from the seat of you home , heck from a seat across the sea thousands of miles away, well they should be stored by a different name than the original trademark.
Also again just like Sony how doesn’t these companies guarding sensitive information so close and tight , like a celebrity with 8 bodyguards? .
Can’t stop the hackers but the company can do a better job at protecting their systems . Specially when in is not a local dollar store , this is billion dollar company
Criminals don’t care, but there is usually a law abiding person or organization somewhere in the chain that does care.
As was mentioned, takedown notices do work… and no, they don’t need the criminal to do anything, but rather the law abiding entity can and will comply.
Except the problem is that under the law a trademark that isn’t defended eventually loses its trademark status. Just saying.
Well, at least they’ve stopped SWATTING you, thank God. Thanks for all you do. I always say the same thing, when will all this nonsense ever end? We can come up with a vaccine for covid in one year but we can’t figure out how to stop malware once and for all.
Well, not using Windoze would go a long way to achieving that aim.
Of course, bulletproof Open Source Linux is the answer!
To quote from the article at hand:
“..I checked up on it – and found that a cryptominer had been dropped on my box, pointing to XXX-XX-XXX.krebsonsecurity.top’. In all, this has infected all three linux boxes on my network.”
“What was the subdomain I X’d out of his message? Just my Social Security number. I’d been doxed via DNS.”
——————–
Every week alerts are sent out by CERT-CISA revealing new vulnerabilities in various OS software, such as OpenSSL and Linux.
https://us-cert.cisa.gov/
Subscribe here to become enlightened:
https://www.cisa.gov/subscribe-updates-cisa
That’s right. Therefore:
1. we have to distinguish between server from client operating systems.
Comparing server vulnerabilities number and user apps vulnerabilities number in an client operating system is really a dumb idea.
2. Linux is not one operating system, it is a different one each distribution.
So, if you insist in comparing, please be fair and do it between two operating systems, not one on a side and +500 as a whole on the other.
3. For a good reason, lets compare and evaluate vulnerabilities not as a total number, but as important vulnerability casualities. We can than count how many severe vulnerabilities are discovered say in one year…
This would male sense.
4. Please, please… be fair and compare one server on one side and one another server on the other.
Otherwise any discussion makes no sense.
So your thought is to question why we can’t find a permanent fix for cybercrime in 50+ years, Other then question the vaccine that was completed in 1 year?
In order to fix cybersecurity, you’d have to first fix the increasingly unregulated free market. You would have to convince politicians to not just tick the box indicating they have installed the latest security updates, but to actually install the updates. Finally you would have to convince everyone else to do the same.
Politicians have no security qualifications, often fall asleep in security briefings, and ignore them when they don’t. Worse still, they will fire you if you point out the truth to them. Telling the truth is actually a sack-able offense if you work for the government.
Money changes hands.
Spies hire black hat hackers to hack systems, politicians/bureaucrats leave those systems vulnerable so they can.
Someone gains a promotion.
Intelligence organizations can’t comment publicly on anything restricted.
Police are hesitant to get involved in anything involving espionage.
HSBC posts yet more record profits.
The government lets a bunch of positions go at FinCEN.
The government passes some new laws on shell companies and money laundering with holes big enough to drive a truck load of cash through.
https://gfintegrity.org/report/enhancing-national-security-by-reimagining-fincen/
True meanwhile multi-million dollar companies should be guarding their systems like a celebrity with 8 bodyguards, for one store it in a different name like lola, and have different large files with a different name and not show the size .
C’mon microsoft teaches free classes on coding and give their interns and students a way to show their coding creations.
Some being highly impressive I call microsoft being lazy in a time where hacking in any company is high , because of a pandemic they know they got less help and they are laid back because is calmer .
The cost to fix the world is too high compared to making a vaccine
we didn’t come out with a covid vaccine in a year.
that work started years ago after SARS and MERS.
And HIV as well – plus big advances in gene research
Clearly an opportunistic attempt to leverage Krebs’ good name. A take down is clearly appropriate.
The tech for the vaccine has been around for quite some time
https://www.statnews.com/2020/11/10/the-story-of-mrna-how-a-once-dismissed-idea-became-a-leading-technology-in-the-covid-vaccine-race/
It took a year to make it work, but the tech for it is old
Keep up the Good Work.
Brian,
This is just an indication of how much these slime fear and hate you for the good work you do.
Thank you for taking a place on the front lines in this war against the turds who attack us all every day.
If it wasn’t you, are you saying it was Shaggy?
It’s a dubious distinction. Stay cool.
If this is what their fear of you materializes as then you must be making a difference.
I’m curious to hear something about what flack (if any) you have have encountered from those who believed the accusation.
For example, victims, law-enforcement, security firms.
-P.
Probably none at all.
These criminals like to think they are getting under his skin, or causing him problems with the law… But that’s wishful thinking
Law Enforcement agencies at several levels are very much aware that criminals try to frame Brian all the time. Even the post office knows, since they have tried sending him drugs.
The more they try to frame him, the more law enforcement knows not to take it seriously.
Looks like the “Michael Corleone Rule”: Keep your friends close, but your enemies closer.
I see the dot-top TLD is Chinese. Do you imagine you should therefore infer you are an adversary to the Party ?
Brian Krebs, internet security journalist by day, Black-Hat hacker by night ! LOL
Interesting that you felt you had to deny the hacking. If you were doing the hacking, would you admit it?
Well, if he was behind it, he probably wouldn’t have published a story calling attention to it! Just sayin’!
Unless… that what he *wants* us to think…
Thanks again, Brain, always an informative treat!
Interesting that you felt you had to point out the denial of the hacking. If you weren’t doing the hacking, would you ask this?
I would like to imagine that whatever organization is in charge of that .TLD would have not problem handing this particular domain name over to you. I have also been told that I see the world through rose colored glasses. Maybe try to get this domain name seized anyway?
In regards to Brian’s comment that “Oddly, none of the several dozen antivirus tools available to scan the file at Virustotal.com currently detect it as malicious.”
I selected that link and if I’m reading the latest Virus Total detection report correctly… as of 3/29/2021 it appears that “Kaspersky” is now detecting it as “UDS:Trojan.Win64.GoBot.a”
FYI – Detection as of this morning is now up to 6 AV Company listings on the VirusTotal report and hopefully growing.
What I love is that Brian still needs to explain that it’s not actually him. After all this time. Too funny.
Thank you Mr Krebs!
If not exist hackers Krebs will be out of the business and money, be sure they share zerodays to hackers to be able to eat their McDonalds 😉 , cheers
Brian,
thank you so much for the work you do. It is a pity you probably cannot see all the good will you are creating. If every grateful reader were a little lighted dot on the world map, you would have created a nice starry sky spanning most of this globe.
As we see from this article, probably the same might hold true for angry villains. But then, I think in general there are way more non-criminal average joes in the world than otherwise, in most cases they just keep quiet so may be less visible.
Should you ever come by this part of the world, I will gladly bake a thank you cake just for you.
Grateful readers in gold, angry villains in red. So pretty!
“Oddly, none of the several dozen antivirus tools available to scan the file at Virustotal.com currently detect it as malicious.” <—Why doesn't this surprise me? I'm highly disappointed in VT anymore. I've found multiple malicious links and files it said was "clean" that were anything but.
Given that VirusTotal is just an antivirus aggregator, the lack of hits on things is just a point on the state of antivirus.
Heuristics seem nearly useless at this point, so until one AV company receives a marked sample, things just fly under the radar. Once one gets a hit, I imagine it’s shared with other AV makers, or they copy from each other.
This isn’t to say that AV is useless, but it can’t keep up – it has to walk a very fine line between detection and spam. Heuristics strong enough to catch things early would be very annoying to sys admins and end users because of false positives.
https://support.virustotal.com/hc/en-us/articles/115002126889-How-it-works
Virustotal implies that your submission is used to help the AV firms so it is more than just a means to run various AV on your submission. I don’t do anything with VT other than submit links so all I am doing is reporting what they say.
I have found that VT vendors often do not tip their hand for known malware or bad sites until several days after the same vendors flag the software or site, if ever.
For example, Google Safe Browsing will not show a hit on VT but will flag a bad site when the URL is submitted directly here:
https://transparencyreport.google.com/safe-browsing/search
The bad guys likely use VT to test the software to see if it can pass under the radar. Meanwhile the vendors may have already come up with a same day fix in their products using AI, etc.
As @Gary previously posted, VT is used to obtain code samples & URLs to all of the various vendors. Many of them may have determined the sample is malware within minutes to a few hours. They just don’t reveal this publicly. Smart IMO.
Where is the report on the annual anti-Krebs Donation marathon of pr0gramm this year?
Keep up the good work Brian. Your posts are excellent. The irony about Russian and Asian hackers is that they secretly admire the West and its achievements. They will never admit it and they will also never have the confidence to move beyond crime. All their cyber vandalism is rooted in envy.
Impersonation is the highest form of flattery.
I’d say that’s a dubious honor at best. And sorry you’re probably considered a “public figure” by now..
You’re a threat to them, Brian. You speak the truth and uncover their misdeeds. It’s a terrible way to compliment you for being such a threat to them. Keep up the good fight! While not always easy, those of us without your knowledge and experience appreciate you!
Am I the only person who gets crazed when new TLDs are released – nothing but spam comes from them – plus the risk to my own domain – OR expenses of keeping silly tlds registered. .top, .online sheesh – I don’t need them and do not want them – and yet there is a risk and cost in not havening them…
My friends for protecting mail are:
Exim, as a bridge/gateway server to hide Exchange.
https://www.spamhaus.org/ with Exim, using
“dnslists = zen.spamhaus.org”
fail2ban Linux scripts.
I have, in the past configure squid as a reverse proxy for Exchange ActiveSync – it is possible.
One of the most curious aspects of this story would be that somehow a hacking group (or was it multiple, somehow discovering and exploiting in parallel) managed to break in to so many web servers and then use them to pull a stunt like this.
We’ve learned from following this site that useful, exploitable vulnerabilities change hands for large sums of money on the dark net. So it seems more than a trifle odd that something which by the sound of things could be used to host spam generation on literally tens of thousands of mail servers was being spent to target Brian.
Just stop and think about that for a second… You’ve discovered a vulnerability which, if you exploited it sensibly, could probably fly under the RADAR for a reasonable amount of time [i.e. if you ran only a handful of spam messages a day]. So you use the exploit to mount something like this, basically sacrificing a pretty lucrative pay-day.
Brian has experienced this before and is quite used to attracting the ire of the criminal underground. But this strikes me as being perpetuated by someone who has a real metaphorical axe to grind.
Stay safe, Brian.
When Skynet becomes self aware and starts taking down the world’s systems, they’ll name it “krebs.exe”
More krebs memes! Malwaretech and the betabot people (Lord Huron/BV1 and betamonkey) thought including your picture on betabot’s login page was hilarious.
The part about your social is unfortunate. I guess you really annoy some people!
159.65.136[.]128 is yet another bad actor using Digital Ocean hosting services. We go through every few months to see what IP ranges Digital Ocean has added and block them at the firewall.