Hardly a week goes by when I don’t hear from some malware researcher or reader who’s discovered what appears to be a new sample of malicious software or nasty link that invokes this author’s name or the name of this blog. I’ve compiled this post to document a few of these examples, some of which are quite funny.
Take, for example, the login panel for “Betabot“: Attempt to log in to this malware control panel with credentials that don’t work and you’ll be greeted with a picture of this author, accompanied by the following warning: “Enter the correct password or I will write a 3-part article on this failed login attempt.”
The coders behind Betabot evidently have several versions of this login panel warning: According to a threat intelligence report being released tomorrow by RSA, the latest iteration of this kit uses the mugshot from my accounts at Twtter (follow me!) and Facebook (like it!).
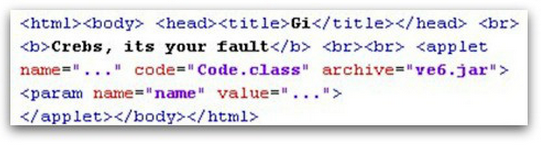
As first detailed by Sophos’s award-winning Naked Security blog, the code inside recent versions of the Redkit exploit kit includes what appears to be a message blaming me for…well, something. The message reads: “Crebs, its [sic] your fault.”
The one I probably hear about most from researchers is a text string that is built into Citadel (PDF), an offshoot of the ZeuS banking trojan botnet kit that includes the following reference: “Coded by BRIAN KREBS for personal use only. I love my job and my wife.”
Those are just the most visible examples. More commonly, if Yours Truly is invoked in the name of cybercrime, it tends to show up in malicious links that lead to malware. Here are a few just from the past couple of weeks:
hxxp://hecked-by-brain-krebs.biz/.h/.t/.t/.p/install, a sanitized version of a site that is foisting malware, according to link checkers from 7 out of 39 antivirus vendors at Virustotal. The malware foisted by this link is detected as nasty by malware scans from 33 out of 47 vendors at Virustotal.
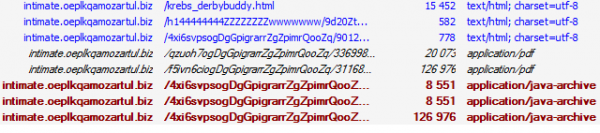
Security blogger Kafeine has been chronicling the emergence of an exploit kit variously named “Stamp EK” and “SofosFO” which has apparently added my surname to a URL generator for new malware links. Here’s a screenshot of what that looks like (avoid visiting the IP addresses or URLs shown in the image below unless you know what you’re doing).
Kafeine also shared some information about Citadel botnet controllers recently found invoking my name, including this one (“mudak” is transliterated Russian for “fuc*er).
While not strictly malware-related, the references to this blog and author that have been reported most frequently by readers over the past few weeks come from an Internet meme that someone started about a month ago, using Memegenerator.net. Some of these are a bit crude, but a few of them made me laugh out loud. I’m sure the act of just blogging about this meme will cause more entries to be added (there are currently four pages worth).
To some extent, this silliness has been going on for several years now. In June 2011, someone hacked a news site and planted a story falsely claiming that F-Secure researcher Mikko Hypponen and I had been arrested for selling stolen credit cards. That same month, a Trojan downloader which peddled adult Web sites included a reference that I had somehow gotten married to security blogger Dancho Danchev.
In 2010, Fortinet found a variant of the spam botnet installer Pushdo that was controlled by a domain name called “fuckbriankrebs.com.” In 2009, Sophos wrote about a new email malware campaign disguised as an alert about a wayward DHL package: The message included a “tracking number” that was essentially the same sentiment, only spelled backwards.
Update, 1:31 p.m. ET: Updated the screen shot used in Kafeine’s example.





BetaBot isn’t an exploit kit, you might want to fix that. It’s a publicly for sale bot on hackforums lol. I can link you to the sales thread if you would like to see it.
Heh, yeah, I’m aware of that, thanks. I just tweaked the sentence and added a link to a description of what it is.
Its no problem, I enjoy reading your blog, glad to help. Whats funny is I can’t tell whether the people who design these pieces of malware despise you or admire you. Maybe its a mixture of both? hah
I’d hazard a guess that it’s more the former than the latter :p
It’s an open question, since I doubt there’s a way to know, but I’m with Neej on this one.
It’s often said that, unlike the malicious hackers of yesteryear, today’s bad guys seek riches over renown. But I don’t fully agree with that; sure, some of the more seasoned and organized crooks really don’t like being known at any level for what they’re doing. On the other hand, it’s been my experience that a great many fairly talented malicious hackers also have tremendous egos, and secretly crave the attention — if not attribution — that their work brings.
Would it be fair to say that the ones with the biggest egos are the quickest to fall? I think a great example of this is lulzsec, but I am sure you have encountered many others. Its not very often you see hackers and malicious coders going to prison, so my guess would be that the ones with the least skill get caught way more often than those who do.
I guess its either that or they don’t publish often when big fish get caught, but that doesn’t seen likely considering they big story about the guy who made butterfly bot a few years ago.
Having someone register a domain with your name and an obscenity in it is a fame that few people ever get to experience. 🙂
one time, someone referred to me on the internet.
i felt pretty important for a day.
One time Spamford Wallace thought I brought down his spamming operation because I wrote him a nasty email a shortly before his servers started recursively spamming themselves in an endless loop that actually brought them all down. He had big dollar signs in his eyes because I worked for a multinational, but it turned out he brought them down all by himself.
All I did was send his contact info up to corporate so they could start harassing him every 15 seconds like only a multinational corporation’s legal department can.
there is one one coder of “BetaBot” its a US citizen in his mid 20s that apparently has a job working as a programmer in real life. he idles in few public irc servers, not really hard to find. last time i checked he was going by the alias “Batmayne” on a few irc servers and “betamonkey” on hack forums.
regards
It doesn’t matter if you can find where he idles… If he is hiding behind tor and a few vpns and covers his tracks decently he will be next to impossible to find.
The only way to find people like this is to follow the money, which is a job for the feds.
He spends all his “BetaBot” profits to pay for his crystal meth and crack addiction. Why else would someone with a full-time job need additional income?
Lol… maybe to buy luxury stuff that their full time income can’t afford?
Yeah, underground bunkers don’t build themselves for free.
The world’s oldest reason – a woman. Or women.
Bitcoins?
Buttcoins
Wow… thanks for not featuring the one I submitted(GETS DDOSED/DOESNT CARE).
Enough of the good laughs about immature humor about Krebs. Krebs, get back to work! 🙂 (this is all in good fun, of course)
That krebsloh.uni.me link definitely has its origins in Russia. “Loh” is “looser” in Russian.
“‘Loh’ is ‘looser’ in Russian.”
I suspect you mean ‘loser,’ unless Brian has lost a good bit of weight recently, in which case he would be known for wearing loose clothing.
Or he lets “loose” once’t and a while! 😀
Obviously malicious, but have you seen this yet: hecked-by-brain-krebs.biz ?
Some malware on my network was going out to that hostname. Good times..
Derp, I can read good.
Keep up the good work Brian. If the bad guys are noticing you, then you are most likely doing something right. You got some stones, boy.
LT
Making Friends , influencing people LOL
As Oscar Wilde once famously observed, “The only thing worse than being talked about is not being talked about.”
Oh, never thought I would know anyone that *was* a meme. Keep it up brother
I prefer to achieve Internet success by having my tweets to celebrities re-tweeted or favorited or responded to by them – preferably all three. 🙂
Being notorious enough to be SWATed, or having my name inserted into malware doesn’t interest me – although I have to admit my last name is perfect for such endeavors. 🙂
The only thing left for Brian now is to be featured as himself on Big Bang Theory – like Summer Glau. 🙂
How did you feel about having your name paired with a picture of a writer in a dialogue that implied you’d been murdered by the T1001?
Oh, you saw that, did you?
That was hilarious! I loved it! My one second of television fame!
Considering the rep I got on the Fox Terminator Wiki and the Sarah Connor site for criticizing the second season of the show, it was an honor.
Of course, the writer probably thought he was slamming me, but it worked out the opposite. 🙂
I love that Sarah Conner Chronicles! I think it is one of the BEST all time series on TV – EVER! Well that shows you what kind of taste I have! 😀
Wow! Are we off topic or what!!
@Brian, you’re missing a space been `been` and the linked `arrested` in the article :(.
Time to face it Brian, you’re the Chris Hansen of Cyber Security.
“Why don’t you take a virtual seat over there. What do you think you were doing? What were you going to do? Money mules? I think you should wait here for the police. Yeah, why don’t you do that.”
Either they are having a laugh at/with you, or trying to Joe Job you, or both…
Chris Hansen, eh? Well, I certainly hope these guys don’t show up with a six pack of coolers and some rubbers.
Now that’s funny right there.
Dem eyes. Dem beautiful, gorgeous eyes.
I lold 😀 😀
What a pity we probably won’t get to see hilarious double takes and lines like “I was just walking past and I saw the door was open so I thought, what the hell, I might as well just walk that way” :p
Hey krebs,
Where is this RSA security report that was supposed to be released today? I checked their twitter and don’t see anything about malware analysis.
Krebs is agent of FSB (exKGB)
http://krovaviyliver.livejournal.com/2096.html
We got u Krebs! or should I say Kriebz?
Having your name or referencing yourself was a common trait of the old days of Dos viruses, for example Dark Avenger has used the name of Vesselin Bontchev in some – in an antagonistic prose, and in the Dedicated series of Viruses, he added Sarah Gordon’s name.
Keep up the good work.
That hxxp://hecked-by-brain-krebs.biz/.h/.t/.t/.p/instal
Is from “Slacker” I can proove if you want