On Thursday evening, KrebsOnSecurity was the subject of a rather massive (and mercifully brief) distributed denial-of-service (DDoS) attack. The assault came from “Meris,” the same new botnet behind record-shattering attacks against Russian search giant Yandex this week and internet infrastructure firm Cloudflare earlier this summer.

Cloudflare recently wrote about its attack, which clocked in at 17.2 million bogus requests-per-second. To put that in perspective, Cloudflare serves over 25 million HTTP requests per second on average.
In its Aug. 19 writeup, Cloudflare neglected to assign a name to the botnet behind the attack. But on Thursday DDoS protection firm Qrator Labs identified the culprit — “Meris” — a new monster that first emerged at the end of June 2021.
Qrator says Meris has launched even bigger attacks since: A titanic and ongoing DDoS that hit Russian Internet search giant Yandex last week is estimated to have been launched by roughly 250,000 malware-infected devices globally, sending 21.8 million bogus requests-per-second.
While last night’s Meris attack on this site was far smaller than the recent Cloudflare DDoS, it was far larger than the Mirai DDoS attack in 2016 that held KrebsOnSecurity offline for nearly four days. The traffic deluge from Thursday’s attack on this site was more than four times what Mirai threw at this site five years ago. This latest attack involved more than two million requests-per-second. By comparison, the 2016 Mirai DDoS generated approximately 450,000 requests-per-second.
According to Qrator, which is working with Yandex on combating the attack, Meris appears to be made up of Internet routers produced by MikroTik. Qrator says the United States is home to the most number of MikroTik routers that are potentially vulnerable to compromise by Meris — with more than 42 percent of the world’s MikroTik systems connected to the Internet (followed by China — 18.9 percent– and a long tail of one- and two-percent countries).

The darker areas indicate larger concentrations of potentially vulnerable MikroTik routers. Qrator says there are about 328,000 MikroTik devices currently responding to requests from the Internet. Image: Qrator.
It’s not immediately clear which security vulnerabilities led to these estimated 250,000 MikroTik routers getting hacked by Meris.
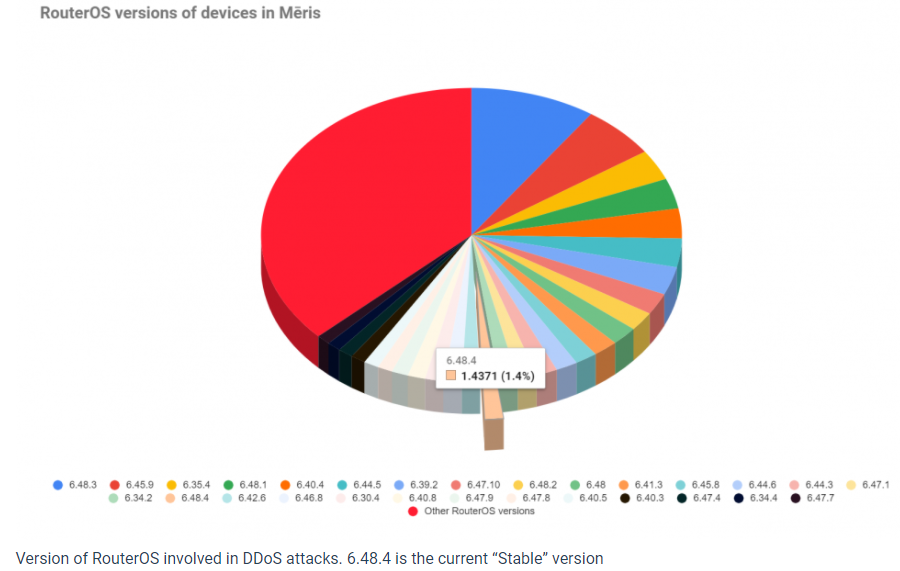
“The spectrum of RouterOS versions we see across this botnet varies from years old to recent,” the company wrote. “The largest share belongs to the version of firmware previous to the current stable one.”
It’s fitting that Meris would rear its head on the five-year anniversary of the emergence of Mirai, an Internet of Things (IoT) botnet strain that was engineered to out-compete all other IoT botnet strains at the time. Mirai was extremely successful at crowding out this competition, and quickly grew to infect tens of thousands of IoT devices made by dozens of manufacturers.
And then its co-authors decided to leak the Mirai source code, which led to the proliferation of dozens of Mirai variants, many of which continue to operate today.
The biggest contributor to the IoT botnet problem — a plethora of companies white-labeling IoT devices that were never designed with security in mind and are often shipped to the customer in default-insecure states — hasn’t changed much, mainly because these devices tend to be far cheaper than more secure alternatives.
The good news is that over the past five years, large Internet infrastructure companies like Akamai, Cloudflare and Google (which protects this site with its Project Shield initiative) have heavily invested in ramping up their ability to withstand these outsized attacks [full disclosure: Akamai is an advertiser on this site].
More importantly, the Internet community at large has gotten better at putting their heads together to fight DDoS attacks, by disrupting the infrastructure abused by these enormous IoT botnets, said Richard Clayton, director of Cambridge University’s Cybercrime Centre.
“It would be fair to say we’re currently concerned about a couple of botnets which are larger than we have seen for some time,” Clayton said. “But equally, you never know they may peter out. There are a lot of people who spend their time trying to make sure these things are hard to keep stable. So there are people out there defending us all.”




I thought as much since I was unable to contact your website for a while. You may have named a name (person or group) that made someone mad.
Regards,
If you were unable to contact his site despite Brian using Google as a shield against ddos attack.
Then of what use is paying google for their ddos service since they are only playing “catchup”
Project Shield is a free service, but it’s only available for selected news sites, human rights organizations, and election monitoring sites.
But did they really manage to knock it offline? I assume Google mitigated it and that’s why they gave up so quickly anyways.
Or your router was one of the botnet members and got blocked 🙂
Maybe “The Manipulaters” didn’t like your recent article.
They’re just the latest to join the fail club. Who knows.
This attack just proves the importance criminals attribute to Mr. Krebs.
Perhaps the Krebs website is not out of the woods yet. It’s a sunny Saturday in lovely Belgrade, Serbia. About 20% of my requests from Krebs links (the tabs, and hot links), including the main page, returned 502 server errors over a 30 minute period. I’m not using a proxy server, and I’m using Firefox with some security add-ons, one of which is a canvas spoofer (spoof value: “true” according to analytics) which sometimes appears to servers as an attack. But, if this is the case, then I was able to get through any possible Google security at least 80% of the time, and didn’t trigger any Clouflare or Recapcha obstacles. But I do get this notice when I use the quad address for Krebs: “Project Shield Logo, 502. 130.211.45.45 is being configured. The page you are trying to access is protected by Project Shield, but recent configuration changes are propagating through our system. Try reloading the page in a minute.” At least the Smurfs are working overtime!
The canvas spoofing is likely not related.
Sounds like maybe the attack wasn’t short lived?
I guess only Brian can answer since he has access to the Shield analytics, but maybe it has been continous and Google just mitigated it.
As for the canvas spoofer, that just makes things worse for you. Fingerprinting solutions detect that you’re interfering with the canvas (e. g. retry several times and compare, or statistical analysis), and just add that as another identifier. I know at least FingerprintJS Pro does it, and I assume recaptcha as well.
It’s a bad signal for fingerprinting anyways, webgl and webaudio are much more reliable (but just as easily handled if the extension authors knew what they were doing).
The canvas spoofing is likely not related.
I just got this trying to post the above :
Error: Server Error
The server encountered a temporary error and could not complete your request.
Please try again in 30 seconds.
“More important” is perfectly adequate without the “-ly” tacked on, turning it into a pointless adverb.
How, when, where and sometime WHY. It bothers me that some people cannot conjugate a verb.Is that you? But some people are lackadaisical about the issue of DDOS and other planned attacks and will lose their ass, if you know what I mean.
Perhaps asses would be the correct description. What say you?
MicroTik is claiming it’s a public vuln from 2018 (CVE-2018-14847).
Considering skids have had access to full PoC for 3 years and the botnet’s size – it’s likely they’re also doing something else.
Funny scum bags hate being exposed so much, they can’t help but draw more attention to themselves.
Like a drunk being told to leave a bar, that starts a fight to prove he’s even stupider than anyone thought.
Typo in paragraph 5 – “The traffic deluge from Thursday’s attack on this site was was more than four times what Mirai threw at this site five years ago.”
Nichteinmenschlichfrau botnet as Niles calls it.
Who doesn’t like to play Wack-A-Mole on the weekend?
Strange but true. Founder of company axiomcyber (.) com was found to have colluded with war criminals from Kosovo Albania. They white label their own equipment from Microtik and also sell “security” for Microtik equipment. Usually botnets and ransomware avoid Russian and nearby countries. Albania has no love lost for either.
Shannon and Troy Wilkinson both worked for the U.N. in Kosovo. They started axiomcyber shortly after returning from Kosovo and have also started Tego Cyber. He was accused of bribery by the Limaj group. One of those things I would have thought the SEC would ask to be disclosed when Tegocyber went public.
Le botnet meris a déjà été identifier il ya quelque mois sous le nom de botnet katana !
you’re right the meris botnet looks a lot like the katana botnet
*Laughs at Mikrotik*
15 million hacked routers turn and stare at you simultaneously.
Green LEDs flashing intermittently suddenly go solid red.
You have angered the hive. A coil begins to whine at 800 hz.
You write that the 2016 attack was 450,000 requests per second. But in 2016 you described it as 620 Gbps. That works out to about 170KB per request. Is that correct? That’s a dozen full-sized packets worth. My understanding is that, *in general*, HTTP requests run around less than 1 KB, though perhaps the larger requests were part of the attack.