On Tuesday, KrebsOnSecurity warned that hackers increasingly are using compromised government and police department email accounts to obtain sensitive customer data from mobile providers, ISPs and social media companies. Today, one of the U.S. Senate’s most tech-savvy lawmakers said he was troubled by the report and is now asking technology companies and federal agencies for information about the frequency of such schemes.

At issue are forged “emergency data requests,” (EDRs) sent through hacked police or government agency email accounts. Tech companies usually require a search warrant or subpoena before providing customer or user data, but any police jurisdiction can use an EDR to request immediate access to data without a warrant, provided the law enforcement entity attests that the request is related to an urgent matter of life and death.
As Tuesday’s story showed, hackers have figured out there is no quick and easy way for a company that receives one of these EDRs to know whether it is legitimate. After all, there are roughly 18,000 distinct police organizations in the United States alone, and many thousands of government and police agencies worldwide.
Criminal hackers exploiting that ambiguity are enjoying remarkable success rates gaining access to the data they’re after, and some are now selling EDRs as a service to other crooks online.
This week’s piece included confirmation from social media platform Discord about a fraudulent EDR they recently processed. On Wednesday, Bloomberg published a story confirming that both Apple and Meta/Facebook have recently complied with fake EDRs.
Today, KrebsOnSecurity heard from Sen. Ron Wyden (D-Ore.), who said he was moved to action after reading this week’s coverage.
“Recent news reports have revealed an enormous threat to Americans’ safety and national security,” Wyden said in a statement provided to KrebsOnSecurity. “I’m particularly troubled by the prospect that forged emergency orders may be coming from compromised foreign law enforcement agencies, and then used to target vulnerable individuals.”
“I’m requesting information from tech companies and multiple federal agencies to learn more about how emergency data requests are being abused by hackers,” Wyden’s statement continues. “No one wants tech companies to refuse legitimate emergency requests when someone’s safety is at stake, but the current system has clear weaknesses that need to be addressed. Fraudulent government requests are a significant concern, which is why I’ve already authored legislation to stamp out forged warrants and subpoenas.”
Tuesday’s story showed how fraudulently obtained EDRs were a tool used by members of LAPSUS$, the data extortion group that recently hacked Microsoft, NVIDIA, Okta and Samsung. And it tracked the activities of a teenage hacker from the United Kingdom who was reportedly arrested multiple times for sending fake EDRs.
That was in March 2021, but there are similar fake EDR services on offer today. One example can be found on Telegram, wherein a member who favors the handle “Bug” has for the past month been selling access to various police and government email accounts.
All of the access Bug is currently offering was allegedly stolen from non-U.S. police and government email accounts, including a police department in India; a government ministry of the United Arab Emirates; the Brazilian Secretariat of Education; and Saudi Arabia’s Ministry of Education.
On Mar. 30, Bug posted a sales thread to the cybercrime forum Breached[.]co saying he could be hired to perform fake EDRs on targets at will, provided the account was recently active.
“I am doing LE Emergency Data Requests for snapchat, twitter, ig [Instagram] and many others,” Bug wrote. “Information we can get: emails, IPs, phone numbers, photos. Account must be active in the last week else we get rejected as shown below. Have gotten information only on Snapchat, Twitter and IG so far.”
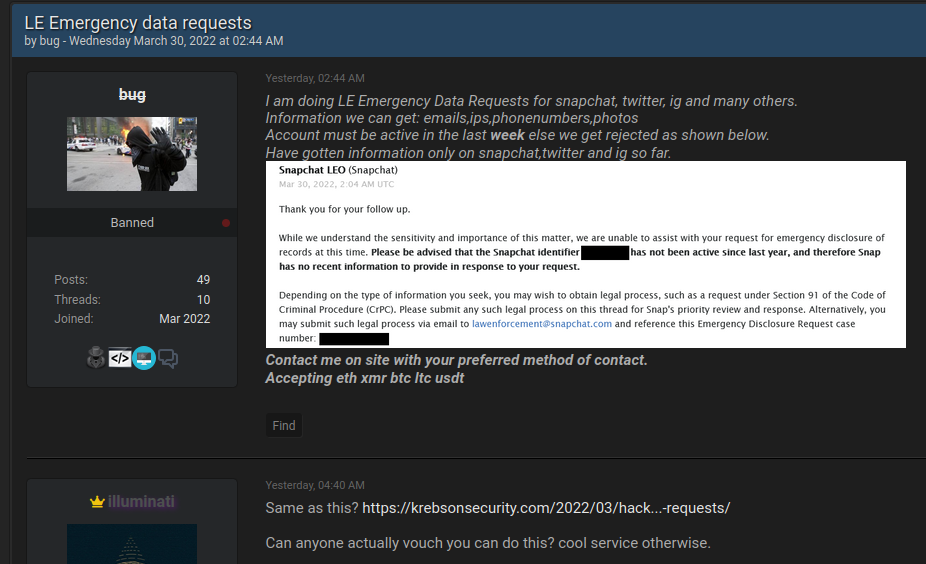
An individual using the nickname “Bug” has been selling access to government and police email accounts for more than a month. Bug posted this sales thread on Wednesday.
KrebsOnSecurity sought comment from Instagram, Snapchat, and Twitter. This post will be updated in the event they respond.
The current scourge of fraudulent EDRs illustrates the dangers of relying solely on email to process legal requests for privileged subscriber data. In July 2021, Sen. Wyden and others introduced new legislation to combat the growing use of counterfeit court orders by scammers and criminals. The bill calls for funding for state and tribal courts to adopt widely available digital signature technology that meets standards developed by the National Institute of Standards and Technology.
“Forged court orders, usually involving copy-and-pasted signatures of judges, have been used to authorize illegal wiretaps and fraudulently take down legitimate reviews and websites by those seeking to conceal negative information and past crimes,” the lawmakers said in a statement introducing their bill.
The Digital Authenticity for Court Orders Act would require federal, state and tribal courts to use a digital signature for orders authorizing surveillance, domain seizures and removal of online content.




This is just ridiculous. How are ‘police’ from s**thole regimes like the United Arab Emirates or the United States of America allowed to request sensitive data?
Was reading that thread out of curiosity and it turns out the OP is a scammer?
Are you asking a question or showing your ignorance?
It’s our own government themselves putting out to look like it’s us.cause they are doing it to me.since 2017 and before me they were doing it to my daughter mari.for the fact that they let nothing go by them let alone info like that.irs impossible.thwy are on everyone’s device and watching us thru our devices.just like they take over everyone s websites like mine.they are lieing
lol
Just out of curiosity, is there any specific address that an ISP must monitor to receive those requests? When they send the requests, how do they even know that someone will bother to read them?
All the major providers have portals or pages where they explain how legal process can and should be filed. Some want you to fax the request, others are fine with email, and some of the bigger companies like Facebook and Coinbase have their own dedicated portals.
FYI the FCC has an interesting feature in their complaint system not found elsewhere in government agencies. It’s called ‘My Story’ and served me well in the last few years. You can tell your story and choose to request that details and documentation be restricted to internal distribution. Petite fraud is rampant these days, and combined with shameless demands for information RIGHT.NOW is a loss for the consumer. Frankly I wish Medicare would borrow the software because health insurance is a much different experience than health care and has been for a while. For example: I got my second COVID booster yesterday. The line was short, two of us. The other guy for whatever reason had been “vaccine hesitant” and was in for his second jab, and will be back for the 1st booster in four months and the 2nd in eight months. He may lose a few “friends”, but he’ll save a bundle on misguided political campaign contributions this year, he observed almost cheerfully.
Once the data is in the systems of the large social media companies featured in this article, look out! You can request the restrictions through the FCC option you mention, which is a start, but copying that modality in privately owned corporations whose profits rely on selling data, maybe without more than that, it is already too optimistic? Probably the legal penalities for evading already existing requirements need to be examined, to see if they are sufficiently onerous to deter illegal sharing of private information.
Not that it would deter people like “Bug,” mind you.
Payment for crime in crypto currency. No surprise there except Wyden is a fan of crypto currency.
https://fortune.com/2022/03/07/crypto-regulation-ron-wyden-internet/
What did anyone expect, cash-in-mail?
I’ve never run Windoze, and I’ve never been “hacked”; could there be a connection? I predict a class action against M$ some time soon, for knowingly selling defective goods.
Specious Reasoning defined.
Homer Simpson buys a rock that keeps bears away.
In the interest of K.I.S.S. – why can’t the providers make an out of band call to the requesting law enforcement agency to verify the veracity of the request? Seems like a simple measure to look up the contact information and call the L.E..
“One of the problems you have is there’s no validated master list of people who are authorized to make that demand,” Rasch said. “And that list is going to change all the time. But even then, the entire system is only as secure as the least secure individual police officer email account.”
“Validating a master list is impossible” is not in there however.
“Words surrounded by quotation marks should mean that someone actually said/wrote those exact words”
I forgive you if English is not your native language, but just because something is infeasible or impractical in the real world, doesn’t make it impossible.
Read this article and the previous article on the topic (use Google translate if you need), neither has suggested it is impossible. So please do not bother with the straw man.
The quote was denoted appropriately. Learn English indeed?
What did you quote? I use the search function, but can’t find your quote source. Did you make it up?
Poor David. Struggling with a search function is not necessary if you can simply read it, as it literally says the quote was NOT said originally. Bitte.
Ah okay.
So you’re one of those people who say literally, when they mean figuratively. Just to add drama. And here you are using quotations to make up an opposing argument that was never actually said.
This really isn’t so difficult unless you need it to be for whatever reason, David. If it’s too confusing just move along. No drama required.
“Validating a master list is impossible” was not said, and really there’s no reason to think it is impossible. Someone claimed it’s impractical and perhaps to them it is, but it’s not impossible and to my eyes it’s necessary given the scope of the issue. How exactly that gets done to scale is the meat of the issue, and it would be effort requiring but no other solution seems apparent. Unless you have a novel suggestion to offer?
There were several people that Brian Krebs quoted in the last two articles (not just the comments) that suggested that it’s impractical to build and maintain a global database of all cops authorized to submit an EDR.
I don’t know why you’re making up quotes to sound smart, but you’re arguing against the content of these articles, not this fictitious person who claims it’s impossible.
Oh, and the “novel suggestion” has been restated several times and was similarly discussed as Senator Wyden’s bill proposed, “digital signatures”.
If putting “something in quotes” is in your estimation always “trying to sound smart” then good luck to you with the English language. It’s smartypantses on down using such punctuation that you apparently read way too far into to comprehend their otherwise obvious points, as if intentionally so. “You can quote me on it.”
Also “digital signatures” is not a system, that’s a soundbyte summary. I’ll forgive your use of quotes as they aren’t actually needed there, though I doubt you used them to seem smarter than otherwise. I try not to read into punctuation.
Digital signatures IS a system that’s worked well for over 20 years. If you are ignorant about them then it may only seem like a sound bite.
I won’t insult someone who wouldn’t understand…
“Digital signatures” is two words and not a system.
It doesn’t solve all iterations of this problem alone.
“Duck and cover is a SYSTEM!”
Expert in a field
Lol, yes words have meaning and meanings are expressed with words.
The system of Digital Signatures use PKI which does work.
Not solving ALL ITERATIONS isn’t a problem. If you’re looking for a solution for everything in all situations, then you’ll be paralyzed to do anything.
Digital signatures as a system are plenty good to handle this.
Until someone gets ahold of the key or corresponding cookie via compromise, then you’re back to square one without xFA alternative supplemental verification.
Um, keys stored in hardware aren’t easily stolen. Cookies aren’t part of it. So many people who don’t use digital signatures seem to chime in.
Cookies are often used equivalently to digital signature as are stolen keys. 1 dimensional security is 1 dimensional.
No, cookies are not used in ANY implementation of digital signatures defined by NIST or any legit standard.
You’re thinking authentication, which is not the same as digital signatures.
Sure, if the random noob sys admins on the Internet were tasked with building a system using digital signatures for the integrity of EDRs, yeah they would screw it up and do something stupid. But standards exists, and digital signatures have decades of proven robustness.
Great observation. Wish that I had said it.
This is the same observations many people make. If it were that easy, it would never have been a problem.
That’s almost a tautological argument isn’t it? Yet not all known easy things are done ahead of time. Some problems seem to require an exploit or failure before the calculus of addressing it takes the urgency required. The solution may be entirely simple and even known beforehand. That doesn’t mean it will happen beforehand.
More like like simple psychology. Armchair engineers on the Internet think they could do it better. Oversimplifying this major problem without reading the full story.
The two articles explain clearly why the simple proposed out of band follow-up is not practical.
Something being described as impractical does not make it non-simple, nor a non-solution potentially should those assumptions of practicality (based on an article or common practices at the time, whatever) be rendered moot. What is practical to business interests is often then impractical to security minded paradigms. Depending on which altar you worship at the current schema is “impractical” also.
Shouldn’t law enforcement agencies and police departments at all levels, federal, state and local be required to have their internal IT systems meet a minimum standard of security? How about having local and state police comply with one of NIST’s frameworks before they can receive any federal funds or grants from the DoJ? My guess is that there are many small police departments with gaps in their security that are making these fake EDRs possible. They would feel ashamed and embarrassed if word got out that robbers and thieves circumvented weak or non-existent door window locks to brake into their police stations. And the argument is lame if they argue they can’t afford the resources needed. How much money do they spend on expensive SWAT team equipment?
It’s not just the big mainstream social media portals. Users of Nextdoor have reported lots of scams addressed to their email, postal mail box or robocalls that often have their foreshortened name, codename, or even first name and last name initial which they use as their Nextdoor handles. People’s willingness to post their picture as part of their Nextdoor identity has led to stalking for women.
Digital Signitures will not help very much if the people stealing this information are using hacked LEO accounts. Since the signitures will be valid, there is no way for the company to tell that the are fake
It wholly depends on how digital signature are implemented. If signing cert keys are stored on a platform accessible by just logging into an account, then yeah it’s not going to help much.
All the implementations I’ve seen personally have been secured on smart cards. Signing is done by unlocking the private signing key with a PIN too. So even if not stored on secure hardware like a smart card, it’s two factor. Trying to brute force a PIN will lock it out too.
The point is, following secure standards like NIST and others can help avoid the pitfalls of weak implementations.
What about requiring that these requests be filed only from a dedicated mini-tablet or validated from a USB key – something that is locked away until needed.
Except a follow-on phone call or other sanity check 3rd auth method, with 4th / 5th through Nth remaining an algorithmically guarded secret for exceptional situations. “Obviously nested authentication is impractical and therefore, by business logic, entirely impossible.”
Why is nested authentication impractical or as you say impossible?
That’s as someone else suggested above. I rephrased with sarcasm, you (properly) detected it. It’s not impossible but they believe it’s impractical. I think it’s necessary and unavoidable. How exactly they go about validating it is the sausage making but absent some other system this is just going to keep happening until they do.
You detected sarcasm successfully
Hacking a LEO account from some local police department run system, is a lot easier and more common than hacking the PKI used for digital signatures. Digital signatures would be signed by certificate authorities at the state level and those would be signed at the federal level.
It would be similar to how LEO at the local level have to log into the FBI database to run national criminal checks. There should be 2FA required to log in and sign with a digital signature. Preferably they will be assigned a PIN protectedd hardware token which is where signing keys should be stored.
This is what you get when you don’t require a court to order the release of private information. This, and out of control law enforcement, that is.
nobody cares enough to do the right thing that has the power to – which is why they are in power. To do for themselves.