Apple, Google and Microsoft announced this week they will soon support an approach to authentication that avoids passwords altogether, and instead requires users to merely unlock their smartphones to sign in to websites or online services. Experts say the changes should help defeat many types of phishing attacks and ease the overall password burden on Internet users, but caution that a true passwordless future may still be years away for most websites.
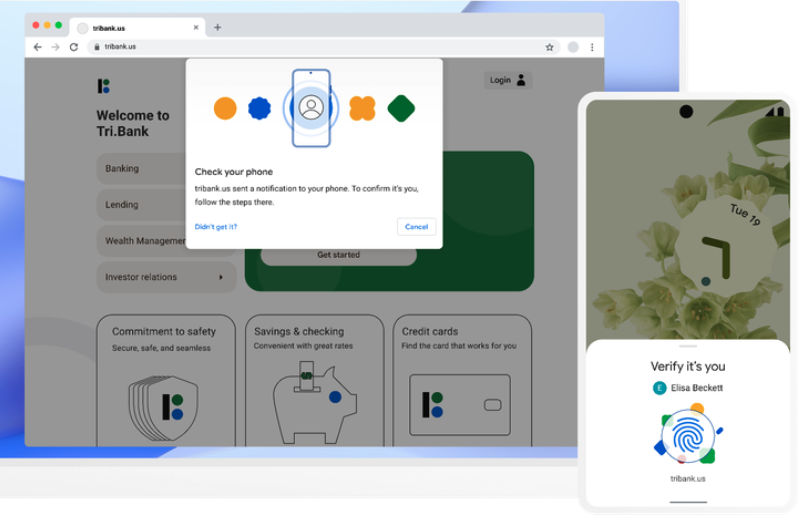
Image: Blog.google
The tech giants are part of an industry-led effort to replace passwords, which are easily forgotten, frequently stolen by malware and phishing schemes, or leaked and sold online in the wake of corporate data breaches.
Apple, Google and Microsoft are some of the more active contributors to a passwordless sign-in standard crafted by the FIDO (“Fast Identity Online”) Alliance and the World Wide Web Consortium (W3C), groups that have been working with hundreds of tech companies over the past decade to develop a new login standard that works the same way across multiple browsers and operating systems.
According to the FIDO Alliance, users will be able to sign in to websites through the same action that they take multiple times each day to unlock their devices — including a device PIN, or a biometric such as a fingerprint or face scan.
“This new approach protects against phishing and sign-in will be radically more secure when compared to passwords and legacy multi-factor technologies such as one-time passcodes sent over SMS,” the alliance wrote on May 5.
Sampath Srinivas, director of security authentication at Google and president of the FIDO Alliance, said that under the new system your phone will store a FIDO credential called a “passkey” which is used to unlock your online account.
“The passkey makes signing in far more secure, as it’s based on public key cryptography and is only shown to your online account when you unlock your phone,” Srinivas wrote. “To sign into a website on your computer, you’ll just need your phone nearby and you’ll simply be prompted to unlock it for access. Once you’ve done this, you won’t need your phone again and you can sign in by just unlocking your computer.”
As ZDNet notes, Apple, Google and Microsoft already support these passwordless standards (e.g. “Sign in with Google”), but users need to sign in at every website to use the passwordless functionality. Under this new system, users will be able to automatically access their passkey on many of their devices — without having to re-enroll every account — and use their mobile device to sign into an app or website on a nearby device.
Johannes Ullrich, dean of research for the SANS Technology Institute, called the announcement “by far the most promising effort to solve the authentication challenge.”
“The most important part of this standard is that it will not require users to buy a new device, but instead they may use devices they already own and know how to use as authenticators,” Ullrich said.
Steve Bellovin, a computer science professor at Columbia University and an early internet researcher and pioneer, called the passwordless effort a “huge advance” in authentication, but said it will take a very long time for many websites to catch up.
Bellovin and others say one potentially tricky scenario in this new passwordless authentication scheme is what happens when someone loses their mobile device, or their phone breaks and they can’t recall their iCloud password.
“I worry about people who can’t afford an extra device, or can’t easily replace a broken or stolen device,” Bellovin said. “I worry about forgotten password recovery for cloud accounts.”
Google says that even if you lose your phone, “your passkeys will securely sync to your new phone from cloud backup, allowing you to pick up right where your old device left off.”
Apple and Microsoft likewise have cloud backup solutions that customers using those platforms could use to recover from a lost mobile device. But Bellovin said much depends on how securely such cloud systems are administered.
“How easy is it to add another device’s public key to an account, without authorization?” Bellovin wondered. “I think their protocols make it impossible, but others disagree.”
Nicholas Weaver, a lecturer at the computer science department at University of California, Berkeley, said websites still have to have some recovery mechanism for the “you lost your phone and your password” scenario, which he described as “a really hard problem to do securely and already one of the biggest weaknesses in our current system.”
“If you forget the password and lose your phone and can recover it, now this is a huge target for attackers,” Weaver said in an email. “If you forget the password and lose your phone and CAN’T, well, now you’ve lost your authorization token that is used for logging in. It is going to have to be the latter. Apple has the infrastructure in place to support it (iCloud keychain), but it is unclear if Google does.”
Even so, he said, the overall FIDO approach has been a great tool for improving both security and usability.
“It is a really, really good step forward, and I’m delighted to see this,” Weaver said. “Taking advantage of the phone’s strong authentication of the phone owner (if you have a decent passcode) is quite nice. And at least for the iPhone you can make this robust even to phone compromise, as it is the secure enclave that would handle this and the secure enclave doesn’t trust the host operating system.”
The tech giants said the new passwordless capabilities will be enabled across Apple, Google and Microsoft platforms “over the course of the coming year.” But experts said it will likely take several more years for smaller web destinations to adopt the technology and ditch passwords altogether.
Recent research shows far too many people still reuse or recycle passwords (modifying the same password slightly), which presents an account takeover risk when those credentials eventually get exposed in a data breach. A report in March from cybersecurity firm SpyCloud found 64 percent of users reuse passwords for multiple accounts, and that 70 percent of credentials compromised in previous breaches are still in use.
A March 2022 white paper on the FIDO approach is available here (PDF). A FAQ on it is here.




Security professionals know SANS, and they know they are not shills for big tech companies. They are agnostic and only promote good security practices.
If you don’t know what SANS is, then you may not have an informed opinion here.
Here is the official position of SANS.
Password Compromise
• Password compromise remains one of the most sought-after and
effective access methods used by penetration testers
– This includes password cracking, spraying, reuse, and others
• This should not still be the case… Turn on Multi-Factor
Authentication! (MFA)
– Microsoft stated, “Based on our studies, your account is more than
99.9% less likely to be compromised if you use MFA.”
– Mark M. of Microsoft stated that as of October 2019 only
8.2% of Azure AD accounts were using MFA
– Solutions such as the FIDO2 standard and solutions such as
YubiKeys can greatly increase MFA security
“Password cracking techniques were covered in Book 2; however, we want to continue looking at the topic
through the eyes of a penetration tester. Password compromise can come in many forms, from cracking and
guessing to reuse and spraying. We will take a look at a couple of these on the upcoming slides. The important
thing to know, from a defensive perspective, is that proper use of Multi-Factor Authentication (MFA) using
solutions based on the FIDO2 standard, such as YubiKeys, can greatly improve your security. There are MFA-
bypass techniques through the use of reverse proxy servers; however, hardware-based solutions prevent those
techniques from working. Check out Yubico’s FIDO2 standard implementation using YubiKeys here.”
This is the general consensus in the field of cyber security.
If you disagree, you will need to explain why you think that the general consensus in the world of cybersecurity is wrong.
Why not use GRC.com ‘s SQRL?
Is this supported by 800 pound tech gorillas?
From technically savvy users:
Yubico recommends (basically requires) you to purchase two of their devices in order for the first one to work properly….and
I am a computer fan, who like to try products like this, and see if they can serve me, and also to review them.
The first point to note is that although it is not technically necessary, the purchase of another identical key is almost mandatory. When we buy a physical key to store passwords and algorithms, we have a lot of security in them, but if they are lost, broken or hit, all passwords are gone forever. If you make the mistake of having a single copy, you will have a big problem, hence the purchase of a pair always. Considering this, if you only have the money to buy one, I do not recommend that you buy it. If you really need that security, raise money first for a couple, and then go ahead.
And finally, I can’t advise buying the product if you have iOS as an operating system, nor if your goal is to use it as a Smart card, nor for native Windows compatibility, nor to buy a single unit. if your case is not among these, then I recommend it. I had to return it.
Now we are talking $90-$150. All this crap talk of ONE $45 YubiKey is disingenuous at best. Shame on the ‘experts’ here. In a huge twist of irony Amazon reviews are superior.
What if a ‘guest’ has physical access to to your computer with inserted dongle? What if they have a keystoke logger installed? I’d bet 1000:1 the NSA/FBI has national securitty backdoor access to it all. Maybe this is why the CCP just outlawed all foreign computers.
I’ve been using Yubikeys for years, and I share the recommendation that you buy at least two.
However, you don’t need two of the full-featured yubikey’s. I bought one black $45 yubikey and one blue $25 FIDO/U2F security key. $70 total.
The black one has all the features and a bunch of other auth key types I can store. These keys are the ones I can back up on paper (chalresp) or as a file (pub/private keys), so no need for a 2nd yubikey for those. The WebAuthN, FIDO, U2F keys cannot be backed up on anything other than another token, so that’s what the cheaper blue yubikey is for.
Even without the blue yubikey, I only use FIDO auth on website that have recovery codes that can be printed out and stored as a backup in a safe.
So if you know what you’re doing, you don’t actually need two yubikey’s. It is still recommended for ease though.
Apple and Microsoft are also members of the FIDO Alliance, so iOS devices will be able to function as FIDO keys too.
If you authenticate to important sites like banks using a security key… DO NOT LET GUESTS USE THE COMPUTER if you leave it inserted. Simple common sense.
Keystroke loggers only work on the static password function of the yubikey. The YubicoOTP, chalresp, FIDO, etc… all work using mechanisms that prevent keylogging replay attacks.
Can’t really talk to the nation-state backdoor access. All I know is that it is MUCH easier to backdoor your stuff if you don’t use hardware security keys. CCP outlawing foreign computers, and the US outlawing some of theirs, is trade-war thing done for economic security.
We understand, you come here to spam about yubikeys. Take a break.
Yubikeys were mentioned by name in the original post. Heaven forbid we talk about security keys on a security blog.
LOL if this were the first time, breathless self-involved advertisement as “security”?
It’s not like Yubico is going to send you free keys just for waving pom poms 24/7.
Why not just start your own blog? You don’t have to pretend to be on Brian’s level.
No one would need bother explaining how it won’t save you from a compromised
access point, you can just pretend defense against keyloggers = pro bees knees.
Noobs could seek your “knowledge” (of marketing and repetition) there instead.
You could put ads for yubikey in blink tag and spam them to your heart’s content
just to ward off the obvious critiques that it’s your single constantly bleated refrain
on security (in depth) from an endlessly pontificating layman slash yubi-stan.
Mealy,
Don’t pretend this has anything to do with Yubikey. The #1 FIDO key on the market (#notspon) being the defacto security device, compared to the very topic of this FIDO article, is perfectly in scope.
The reality is you’ve been cyber stalking me for months. I live rent free in your head. It’s still amuses me.
Every comment you make is devoid of any actual argument. And you spam conversation threads that you’re not a part of. So your existence is kinda sad as you’ve got nothing to contribute other than to say, “I comment too much”.
Your attempts at censorship are pretty sad and I feel sorry for you that you’re so obsessed with me. I’m sure that if I made a blog, you’d be my first subscriber.
As if there’s no middle ground between spamming constantly and censorship, as if you hadn’t been caught impersonating existing handles already. If you made a blog we’d be ABLE to at least avoid your voluminous BS. You agree it doesn’t require advertising, so STOP ADVERTISING IT CONSTANTLY. Yes, you were caught being a troll here and Yubikeys have their place, both are true. Your spams are excessive. No I’m not the only one to say so. Dial it back, let other people get a word in edgewise from time to time if it kills you. This isn’t your blog kiddo.
Mealy,
Nobody is impersonating anyone’s real name here. Although You change your handle for every comment, you don’t “own” any of them. You certainly don’t own Anon or any derivatives.
You are the only one upset about your so-called grievances here.
“let other people get a word in”? You do realize that your spamming can’t actually block others from commenting. That’s not how blogs work, so the only thing attempting censorship, is YOU by suggesting someone else refrain from expression based on your own limits of what you want to read when you scroll down.
Every comment you make is devoid of any actual argument. And you spam conversation threads that you’re not a part of. So your existence is kinda sad as you’ve got nothing to contribute other than to say, “I comment too much”.
I still feel sorry for you that you’re so obsessed with me.
Yubikeys were mentioned by name in the original post. Heaven forbid we talk about security devices on a security blog.
I am not sure how the condescending attitude of “So if you know what you’re doing, you don’t actually need two yubikey’s” helps to win and influence people to understand and start embracing FIDO security keys. If fact you do not need any “yubikey’s”, what you need are security keys that support the FIDO2 protocols for the functionality discussed in this blog post.
If everybody, sadly including the SANS comment post above, would stop pushing the “Yubikey” term or using it incorrectly it would make it easier for those less technical to understand the landscape. “Yubikey” is a brand name of a series of security keys from a company name Yubico which are multi-protocol (e.g., FIDO2, OTP, …..) and have a wide range of form factor (e.g., normal, small, nano) and connectivity interface options (e.g., USB-A, USB-C, Lightning, NFC).
For most the expense of these keys ($45-$60) is unnecessary, unless the form factor or connectivity option is desired not provide by the less expensive ($25-$ 29) Yubico “Security Key Series” (i.e., the blue key) which only supports the FIDO2 protocol with NFC and either USB-A or USB-C connectivity. Or some other less expensive vendor offering.
There is no such thing as a “blue yubikey”, it is a Yubico Security Key Series, and yes that is another confusing term, but if you send somebody to find a “blue yubikey” they will not find it and give up or think they need to spend twice the money.
I did not mean that as condescending. I meant it as “if you do a bit more research into how it works”.
The OP was specifically talking about Yubikey products and their specific pricing. Yes there are others in the market but that isn’t the topic.
I reread the SANS comment above, and have taken a few SANS courses. “Solutions such as the FIDO2 standard and solutions such as YubiKeys can greatly increase MFA security”
It’s the “such as” that is important. SANS does of course mention the most popular vendor in any space by name. They do that for all security solutions. That’s how they stay relevant, by giving real world examples. They mention the most popular IDS, EDR, Open Source tools, etc.
Yes, the official name for the blue yubikey is much longer so of course it’s going to be referred by the short hand. Yubico only colors 1 of their product lines blue. So its fair to just call it the blue yubikey. Maybe its confusing for the color-blind. If anything calling it a “Security Key Series” is more confusing because technically they are ALL security keys.
Thanks for the extra info about Yubikeys. But be careful, as you’ll be called a shill for continuing to discuss them.
If to deploy a new technology everybody needs to “do a bit more research into how it works’ it will never be mainstream. I understand why everybody uses the yubikey term, it is easy, but it causes confusion and impedes the deploy of the technology. For a 1,000-person company looking into rolling out FIDO2 security keys the cost difference between Yubico’s Security Keys and YubiKeys is $25K, often enough to not “do a bit more of research”. I have experience talking thru several companies and countless individuals on this subject so yes, it is a pet peeve. You can be part of the solution or part of the problem your choice.
Yes, SANS added the “such as” phase before YubiKeys but they could have used the phrase “a Yubico’s Security Key”. Oh, sorry that is an extra two words.
Luckily, only the Security Engineers and Architects need to “do a bit more research” for enterprise solutions to be mainstream. We’re the ones that get sent to the RSA Conference each year to evaluate the new technologies. We do the research for our companies and get paid to understand so the c-suite doesn’t have to. In the example of a company looking only for FIDO2 but not GPG, PIV or other methods, yes, the cheaper key is the choice. Going back to the original comment about needing 2 keys because of not understanding the recovery/backup options, the correction is warranted precisely as you say, being a part of the solution and not allowing misinformation to spread.
For individual consumers, it’s unfortunately up to blogs like this to educate consumers.
I get that the semantics is a pet peeve of yours. I’ve got plenty of my own. Keep the knowledge flowing.
Clearly we need to adopt Steve Gibson’s SQRL https://www.grc.com/sqrl/sqrl.htm
That guy is a bloviating, self-promoting con artist. He wrote one good thing, one time(Spinrite), but it doesn’t really work on modern hardware, but he continues to sell it and continues to self-promote shamelessly. He is not someone I would trust to take my garbage out, much less design my password system.
SQRL also requires an app to be installed, and requires persistent Internet on the phone. No signal, no worky.
In 20, nobody adopted SQRL, while FIDO2 has succeeded.
Personally, the biggest issue I have with this approach is that the so called phone that we need to use – Nearly all of them run on Android. That’s lack of choice.
The only option – Apple products are extremely costly for a normal person.
Under such condition, I find myself suggesting against any attempts to standardize any infrastructure (specially website/app login) via phone. Until we have more options in terms of phone OS, we should not push for this.
Android has 80% of the market. Apple has nearly the rest, and Microsoft has smartphones too.
All are members of the FIDO Alliance.
The options are there and its not going to get any more diverse.
Like flavors of Linux, there is still choice in hardware for smartphones running Android.
If you want to wait for diversity, you’ll never see it. In the mean time, phishing passwords have been the cause of so much data loss. It would be stupid to stay with passwords alone just because you don’t like the number of companies offering smartphones.
If I am perfectly aware, there are no Microsoft phones any more. There’s just Android and iOS. And most working folks cannot afford an Apple device.
It’s Android. And, that’s it.
I think, applying this without having options else than android too shallow and short-term thinking. We need to have other OS’s in the market before we implement something so serious. (My views)
https://en.wikipedia.org/wiki/Linux_for_mobile_devices
Adding to my comment above – replacing passwords (multiple for multiple websites) with a single phone-based authentication is much like a “facility that makes life easier by implementing constraints”. It may look lucrative for now. But such types of consolidation can easily become an exploitable asset. I might be reading too much into it – but such a powerful asset that’s run over the only available OS (Android) sounds creepy. I would have had no issues, if there were 10 or even 5 different Phone OS that a normal, IT illiterate person could afford. But in this case, where there’s no choice of OS, and you are about to give that device the power to unlock all your accounts!!! We should postpone such an endeavor until enough alternatives to Android are available. Such are my thoughts.
FIDO doesn’t need a smartphone to run on. You have choice. Yubikey is the most popular FIDO device right now, but there are dozens of competing FIDO devices.
Being able to use FIDO over Bluetooth LE on your smartphone ADDS MORE options to the field. If you don’t even own a phone, you can still use this secure authentication method.
This is not capable of “unlocking all your accounts”. Read the article and read up on the technology. The user still has to opt into what accounts they want to use their phone (or other FIDO hardware token). The way FIDO works, it cannot just automatically find all your online accounts and start replacing your passwords.
Postponing secure authentication options for online banking websites is a dumb idea. We needed this years ago.
I might have been misread “when I say “unlocking all your accounts”. I meant all the accounts you choose to select. I have looked for banks that accept FIDO device based authentication. And, I have had null success.
In the end, at least outside the US – the final product would turn out to be an Android that’s capable to unlocking your account. And if my experience is correct, many many people will give full control to their devices. [When designing technology for the public, we need to consider that they will always choose the easiest option.)
About YubiKey, it costs over $100 at my place. This too is too costly for a normal person. And, it’s costlier than most Andriod based phones that members of the public can afford to buy. And, about those competing devices – Never heard of them. And, I have looked seriously. [Kindly, refrain from quoting more examples.]
The point, my dear, that I am putting up here is – We should not force a constraining-control-based-technology-infrastructure element over the members of public, unless the tech that they would need for utilizing it is free of monopoly control. (such are my views)
With this switch, we might end up with a bigger mess than we are already in.
Yes, the important distinction is “choice”. People can choose what accounts they want to have more secure but less convenient. 99% of your online accounts will probably never need multi-factor authentication. But banking and other critical websites should.
https://2fa.directory/int/#banking
This will help you look more effectively for Banks with hardware token login capability.
Your point about hardware tokens being much more expensive, especially in countries that have import restrictions on encryption devices, is well taken. It makes sense that this new technology might be out of reach for billions of people worldwide. Even the cheaper android-based phones that you could afford, likely will not have the hardware security chip for many years.
So forget Yubikey or Apple phones or even Android, because it seems you could not afford ANY device capable of this security.
But that’s good news for you. Because that means nobody will ever Force this on you. No company will risk losing the business of billions, or risk such a loss of ad revenue.
Take for example OAuth “login with Facebook/Google/etc.”. It’s been around for over a decade, but no website forces you to use it. You don’t need to be fearful that they aren’t hearing you. They understand that billions of people don’t have a Facebook account, or billions of people don’t have a modern smartphone.
“With this switch”
Perhaps that’s the easiest solution. Stop thinking of this as a switch. It’s an option. An option you’ll never need to choose. Just let the rest of the world have that option and decide for themselves if they can afford the enhancement in security.
“Spam”
Adults having a conversation. Why are you cyber stalking?
I feel like the “all eggs in one basket” approach is kind of what gets us here in the first place, and this sounds like more of the same.
If eggs are accounts, and authentication methods are baskets… then this is ADDING another basket. It’s optional, use it if you want.
If spamming about this is optional, just stop.
Mealy, repeated misinformation deserves repeated correction. Otherwise the Q crowd that flooded this article’s comment section with disinformation, succeeds in spreading.
You don’t need to let your fascination and personal grudge with me cause you to side with conspiracy theorists, just because you don’t like me. 🙂
The assertion this will not be forced is comical. Try to obtain an AppleId without a phone number. You will fail.
If one has an iMac and would like to update Apple program, or download a driver, you will be forced to obtain an AppleId and forced to provide a phone number to obtain said AppleId.
The future is already here. Where a Chinese subject is, is where we all will be shortly.
And what happens if you’re in a location that doesn’t get cell reception or you’re not allowed to take your cell phone? Government facilities, research facilities, a lot of locations do not allow cell phones, or you’re in a part of the building that gets lousy cell reception. So a website comes up asking for you to do something on your cell phone and you have to run outside to get to your phone before it times out?
FIDO does not require cell reception. No Internet needed on your phone at all. It communicates over Bluetooth LE to the computer running the web browser.
If your in a SCIF and can’t bring in a phone, then you would not use a smartphone at all. They typically issue USB Hardware tokens or RSA OTP tokens that they clip on your badge lanyard.
It’s all been thought of already, and done for years.
https://www.youtube.com/watch?v=oTUgaZCtbNE
Good summary.
This concept scares me. Or should do if I were not so old. I will be tied to both my email (which every financial institution I deal with uses to validate my existence) and a phone/phone number. I am old enough to remember when it was possible to live my life free of these encumbrances. A pen and paper somehow got me through most of life’s challenges. Even software (called “computer programs” and not “apps”) was a tool and not a means for controlling me. The more we are reliant on this stuff the more reliant we need to me. Look at the number of patches that come out from MS on one Tuesday a month. We are babies sucking at the tits of MS for all of our needs. Now we can even look forward to having “the mark of the beast”, a chip in my hand that I am sure will one day replace many of the functions in the phone that I need now. (Decide for yourself if the religious allusion there is appropriate. For something that was written 2,000 years ago, I think it was kind of a smart observation.) I am lucky in that I likely have 10 years or less left to live. Hopefully not so long that I have to participate in the zombie societies being created now or to die in a nuclear holocaust.
Right there with ya. At the moment all my banking is still available in person. I have it restricted to NO internet access at all. They don’t even have my Email, as I don’t consider that secure, at least not enough to put my life’s savings at risk.
I expect within another generation, people will be so held to standards and processes, life will be a compliance session, we are closer to 1984 than anyone would like. But I’m sure the future generations will be told that we were savages, and their compliance makes them better.
None of this is tied to a phone number.
You could have a phone w/o cellular service and it should still be usable.
And you’ll have the ability to set up a backup of sorts. You should be able to put recovery keys for the account that’s protecting your systems into an actual bank vault.
In case you lose your phone, or in case of your death (we all will die, so this is something that should be planned for), the info in the bank vault should enable someone to regain access to the system and then authenticate to accounts.
I kinda like that. It doesn’t make the task too much harder, it adds some extra level of security. Why not?
It’ll be a matter of habit, of course, but it is fine 🙂
As a bonus, this new technology is also GREAT for traffic correlation analysis, i.e., tracking all of your activity online.
How’s that gonna happen? This new technology works without the phone connecting to the Internet. And there is no way for Google or Apple (whomever you use to sync between devices) to even know when or how the keys are being used. So how would tracking online activity even be possible?
Your blog is very informative for me i got many things from your blog and it is very useful information,
GTU
Looks like SoloKeys might be using OpenSK
https://nakedsecurity.sophos.com/2020/02/03/google-launches-open-source-security-key-project-opensk/
A follow up article on where OpenSK done in the past two years might be a good one.
Love this! I am so done with passwords. They’re unsustainable.
I never save important passwords on my phone.