Among the more plunderous cybercrime gangs is a group known as “Carbanak,” Eastern European hackers blamed for stealing more than a billion dollars from banks. Today we’ll examine some compelling clues that point to a connection between the Carbanak gang’s staging grounds and a Russian security firm that claims to work with some of the world’s largest brands in cybersecurity.
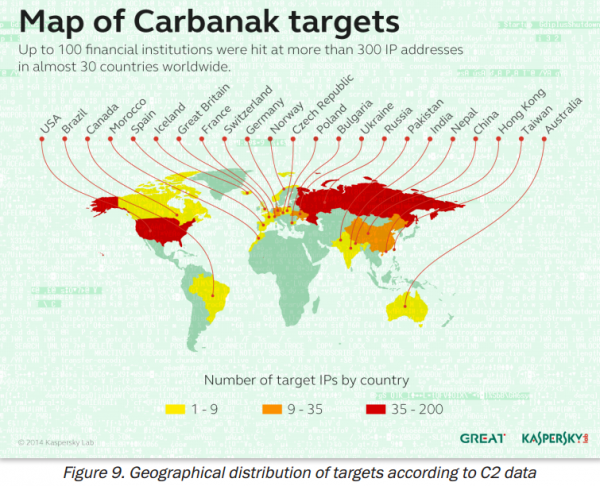
The Carbanak gang derives its name from the banking malware used in countless high-dollar cyberheists. The gang is perhaps best known for hacking directly into bank networks using poisoned Microsoft Office files, and then using that access to force bank ATMs into dispensing cash. Russian security firm Kaspersky Lab estimates that the Carbanak Gang has likely stolen upwards of USD $1 billion — but mostly from Russian banks.
I recently heard from security researcher Ron Guilmette, an anti-spam crusader whose sleuthing has been featured on several occasions on this site and in the blog I wrote for The Washington Post. Guilmette said he’d found some interesting commonalities in the original Web site registration records for a slew of sites that all have been previously responsible for pushing malware known to be used by the Carbanak gang.
For example, the domains “weekend-service[dot]com” “coral-trevel[dot]com” and “freemsk-dns[dot]com” all were documented by multiple security firms as distribution hubs for Carbanak crimeware. Historic registration or “WHOIS” records maintained by Domaintools.com for all three domains contain the same phone and fax numbers for what appears to be a Xicheng Co. in China — 1066569215 and 1066549216, each preceded by either a +86 (China’s country code) or +01 (USA). Each domain record also includes the same contact address: “williamdanielsen@yahoo.com“.
According to data gathered by ThreatConnect, a threat intelligence provider [full disclosure: ThreatConnect is an advertiser on this blog], at least 484 domains were registered to the williamdanielsen@yahoo.com address or to one of 26 other email addresses that listed the same phone numbers and Chinese company. “At least 304 of these domains have been associated with a malware plugin [that] has previously been attributed to Carbanak activity,” ThreatConnect told KrebsOnSecurity.
Going back to those two phone numbers, 1066569215 and 1066549216; at first glance they appear to be sequential, but closer inspection reveals they differ slightly in the middle. Among the very few domains registered to those Chinese phone numbers that haven’t been seen launching malware is a Web site called “cubehost[dot]biz,” which according to records was registered in Sept. 2013 to a 28-year-old Artem Tveritinov of Perm, Russia.
Cubehost[dot]biz is a dormant site, but it appears to be the sister property to a Russian security firm called Infocube (also spelled “Infokube”). The InfoKube web site — infokube.ru — is also registered to Mr. Tveritinov of Perm, Russia; there are dozens of records in the WHOIS history for infokube.ru, but only the oldest, original record from 2011 contains the email address atveritinov@gmail.com.
That same email address was used to register a four-year-old profile account at the popular Russian social networking site Vkontakte for Artyom “LioN” Tveritinov from Perm, Russia. The “LioN” bit is an apparent reference to an Infokube anti-virus product by the same name. Continue reading




 First off, if you have Adobe Flash Player installed and haven’t yet hobbled this insecure program so that it runs only when you want it to, you are playing with fire. It’s bad enough that hackers are constantly finding and exploiting zero-day flaws in Flash Player before Adobe even knows about the bugs.
First off, if you have Adobe Flash Player installed and haven’t yet hobbled this insecure program so that it runs only when you want it to, you are playing with fire. It’s bad enough that hackers are constantly finding and exploiting zero-day flaws in Flash Player before Adobe even knows about the bugs.
![Exposed[dot]su was built with the help of identity information obtained and/or stolen from ssndob[dot]ru.](https://krebsonsecurity.com/wp-content/uploads/2014/03/exposed-su-600x462.png)



 Owned by Santa Clara, Calif. based networking giant
Owned by Santa Clara, Calif. based networking giant 