User-friendly and secure. Hardly anyone would pick either word to describe the vast majority of wireless routers in use today. So naturally I was intrigued a year ago when I had the chance to pre-order a eero, a new WiFi system billed as easy-to-use, designed with security in mind, and able to dramatically extend the range of a wireless network without compromising speed. Here’s a brief review of the eero system I received and installed a week ago.

Three eero devices designed to create an extended range “mesh” wireless network without compromising speed.
The standard eero WiFi system comes with three eero devices, each about the width of a square coaster and roughly an inch thick. Every individual eero unit has two built-in WiFi radios that are designed to hand off traffic with the other two units.
This two-radio aspect is important, as most consumer devices that are made and marketed as WiFi range extenders or “repeaters” contain only one radio, and thus end up halving the speed of the repeated WiFi signal.
The makers of eero recommend one device for every 1,000 square feet, and advise placing one device no further than 40 feet from another. Each eero has two ethernet ports in the back, but only one of the eeros needs to be connected directly into your modem with an ethernet cable. That means that a 3-piece eero set has a total of five available ethernet ports, or at least one open ethernet port at each eero location.
Most wireless routers require owners to configure the device by using a hard-wired computer or laptop, opening a browser and navigating to a numeric Internet address to enter some default credentials. From there, you’re on your own. In contrast, the eero system relies on a simple mobile app for setup. The app asks for your name, email address and mobile number, and then sends a text with a one-time passcode.
After you verify the code on your mobile device, the app prompts you to pick a network name (SSID) and password. The device defaults to WPA-2 PSK (AES) for encryption — the strongest security currently available.
Once you’ve assigned each eero a unique location — and as long as the three devices can talk to each other — the network should be set up. The entire process — from placing and plugging in the eeros to setting up the network — took me about five minutes, but most of that was just me walking from one room or floor to the next to adjust the location of the devices. Continue reading



 The bulk of the security holes plugged in this month’s Patch Tuesday reside in either Internet Explorer or in Microsoft’s flagship browser — Edge. As security firm Shavlik
The bulk of the security holes plugged in this month’s Patch Tuesday reside in either Internet Explorer or in Microsoft’s flagship browser — Edge. As security firm Shavlik  Last week, this blog
Last week, this blog 
 As
As  The number is more than double the figures the IRS released in August 2015, when it said some
The number is more than double the figures the IRS released in August 2015, when it said some 
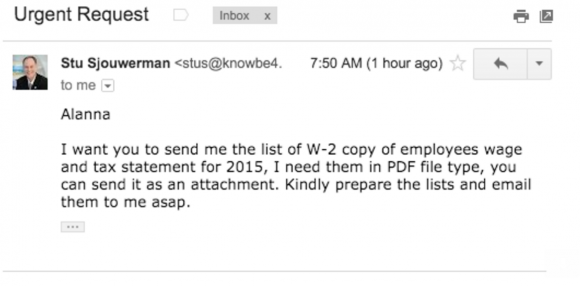
 Stu Sjouwerman, chief executive at security awareness training company KnowBe4, told KrebsOnSecurity that earlier this week his firm’s controller received an email designed to look like it was sent by Sjouwerman requesting a copy of all employee W-2 forms for this year (full disclosure: KnowBe4 is an advertiser on this site). The email read:
Stu Sjouwerman, chief executive at security awareness training company KnowBe4, told KrebsOnSecurity that earlier this week his firm’s controller received an email designed to look like it was sent by Sjouwerman requesting a copy of all employee W-2 forms for this year (full disclosure: KnowBe4 is an advertiser on this site). The email read: