Last year, a top official from big-three credit bureau Experian told Congress that the firm was not aware of any consumers that had been harmed by an incident in which a business unit of Experian sold consumer records directly to an online identity theft service for nearly 10 months. Today’s post presents evidence that among the ID theft service’s clients was an identity theft and credit card fraud ring of at least 32 people who were arrested last year for allegedly using the information to steal millions from more than 1,000 victims across the country.
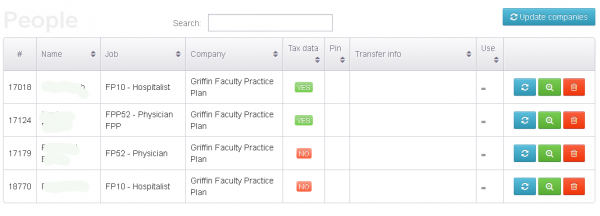
On March 31, 2014, 26-year-old Idris Soyemi of Brooklyn, New York pleaded guilty in a New Hampshire court to one count of wire fraud. In Soyemi’s guilty plea hearing, the prosecutor laid out how Soyemi on several occasions bought Social Security numbers, dates of birth and other personal information from an online identity theft service run by guy named Hieu Minh Ngo.
Ngo is a Vietnamese national who for several years ran an online identity theft service called superget.info. Shortly after my 2011 initial story about his service, Ngo tauntingly renamed his site to findget.me. The Secret Service took him up on that challenge, and succeeded in luring him out of Vietnam into Guam, where he was arrested and brought to New Hampshire for trial. He pleaded guilty earlier this year to running the ID theft service, and the government has been working on rounding up his customers ever since.
According to Soyemi’s guilty plea transcript (PDF), U.S. Secret Service agents seized control over Ngo’s email account in February 2013 and used it to interact with his customers. Posing as Ngo, the undercover agent reached out to Soyemi and wrote, “I’m back. You doing tax refund or credit card?”, asking Soyemi whether he was buying personal data on consumers to set up new lines of credit in their names or to file fraudulent tax refund requests with the IRS — a rapidly growing form of cybercrime. Soyemi responded, “I do credit cards but can you tell me about tax refund?” (if you missed last month’s story about an Ohio man who’s accused of using Ngo’s service to file at least 150 fraudulent tax refund requests with the IRS, check that out here).
Interestingly, Soyemi was part of a huge network of nearly three dozen people who were rounded up last year and charged with taking out new credit cards in victims’ names and then using the cards to make millions of dollars in retail purchases that were then fenced on the black market. From an April 2013 story in the Jersey Journal:
“The leaders of the group, authorities say, purchased the identities of unsuspecting victims from online brokers, who got the information from computer hackers across the United States….”
“In a process known as ‘punching,’ electronic account information from the cards’ magnetic strips would be transferred onto counterfeit cards, which were provided to “strikers” who conducted the purchases at retailers all over the Eastern Seaboard, authorities say…”
….”The investigation has identified nearly 1,000 victims across the country and millions of dollars in phony transactions, authorities say.”
“Authorities say the suspects spent the proceeds on luxury cars, high-end jewelry and other lavish expenses. Some of the money was additionally sent to accounts in Nigeria, authorities say.”
Further tying this group to Ngo’s service is a four-count indictment (PDF) lodged against another man named in that identity theft ring roundup by the New Jersey prosecutor’s office: Oluwaseun Adekoya, 25, of Sewaren, NJ. Adekoya’s indictment makes numerous references to his alleged purchase of hundreds of consumer records from an online identity theft service that was taken over by U.S. Secret Service agents in February 2013 (recall that in Soyemi’s guilty plea hearing government prosecutors said that in that same month undercover Secret Service agents assumed control of the email account tied to Ngo’s identity theft service). Continue reading