The U.S. Department of Justice (DOJ) today said they arrested the alleged operator of 911 S5, a ten-year-old online anonymity service that was powered by what the director of the FBI called “likely the world’s largest botnet ever.” The arrest coincided with the seizure of the 911 S5 website and supporting infrastructure, which the government says turned computers running various “free VPN” products into Internet traffic relays that facilitated billions of dollars in online fraud and cybercrime.

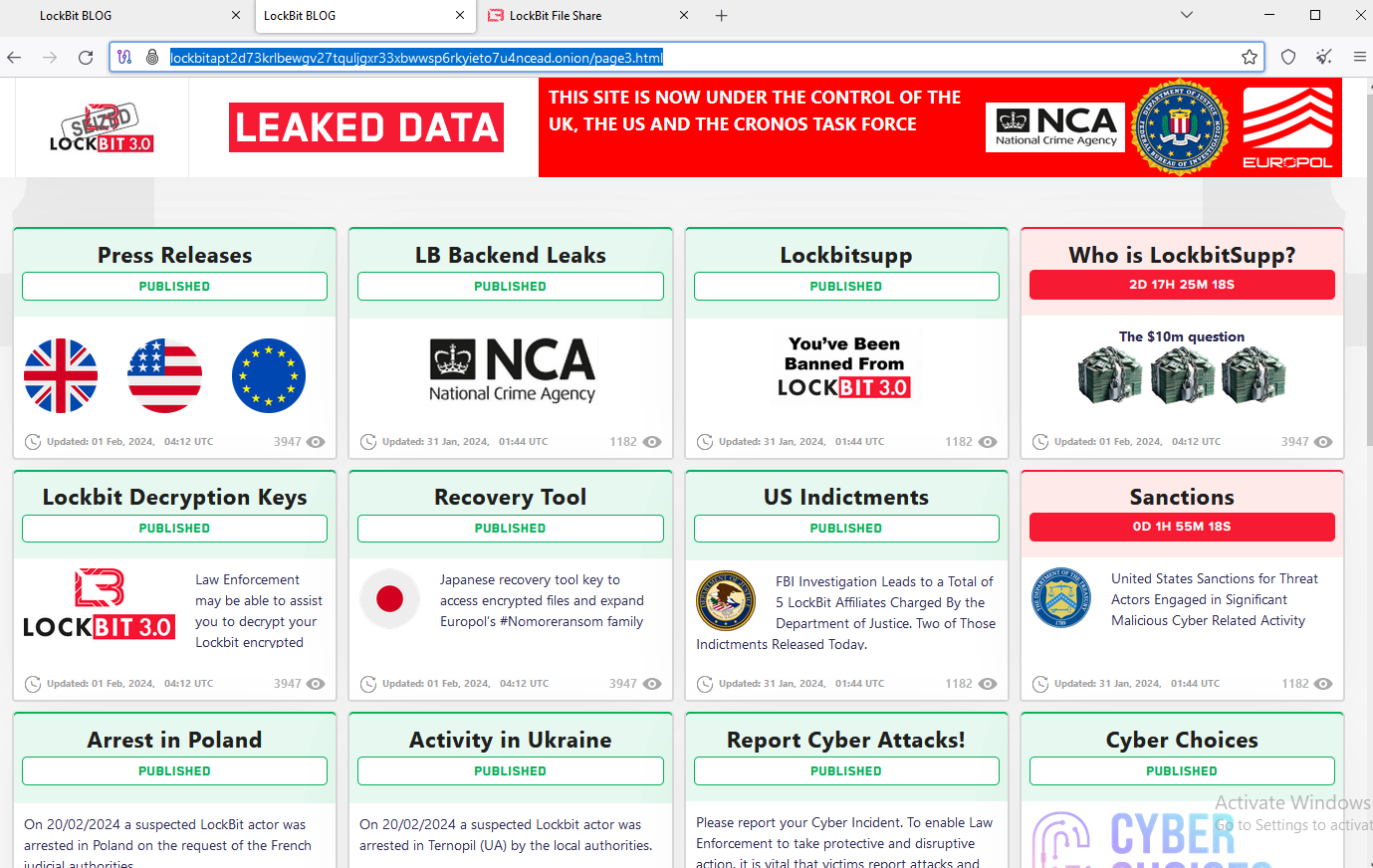
The Cloud Router homepage, which was seized by the FBI this past weekend. Cloud Router was previously called 911 S5.
On May 24, authorities in Singapore arrested the alleged creator and operator of 911 S5, a 35-year-old Chinese national named YunHe Wang. In a statement on his arrest today, the DOJ said 911 S5 enabled cybercriminals to bypass financial fraud detection systems and steal billions of dollars from financial institutions, credit card issuers, and federal lending programs.
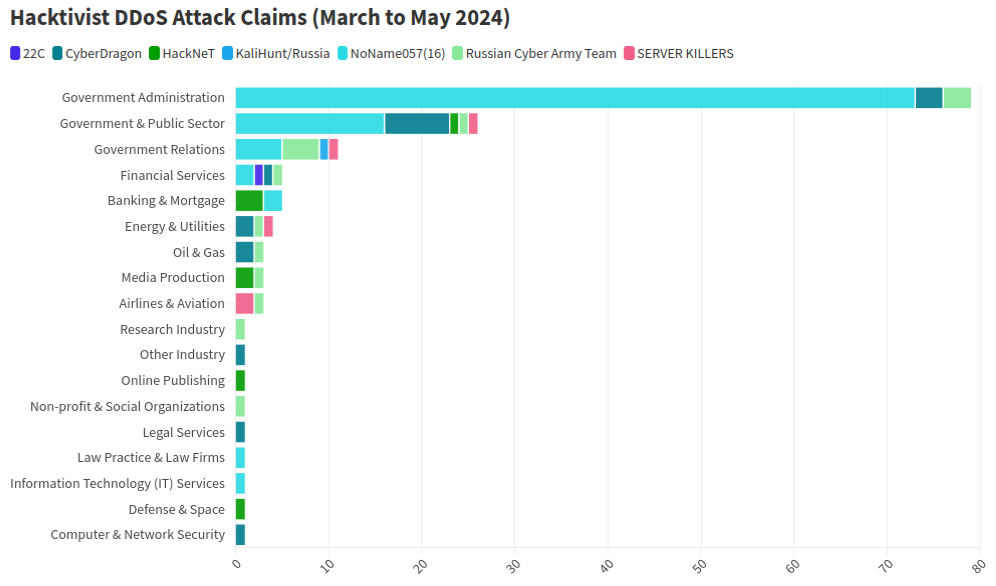
For example, the government estimates that 560,000 fraudulent unemployment insurance claims originated from compromised Internet addresses, resulting in a confirmed fraudulent loss exceeding $5.9 billion.
“Additionally, in evaluating suspected fraud loss to the Economic Injury Disaster Loan (EIDL) program, the United States estimates that more than 47,000 EIDL applications originated from IP addresses compromised by 911 S5,” the DOJ wrote. “Millions of dollars more were similarly identified by financial institutions in the United States as loss originating from IP addresses compromised by 911 S5.”
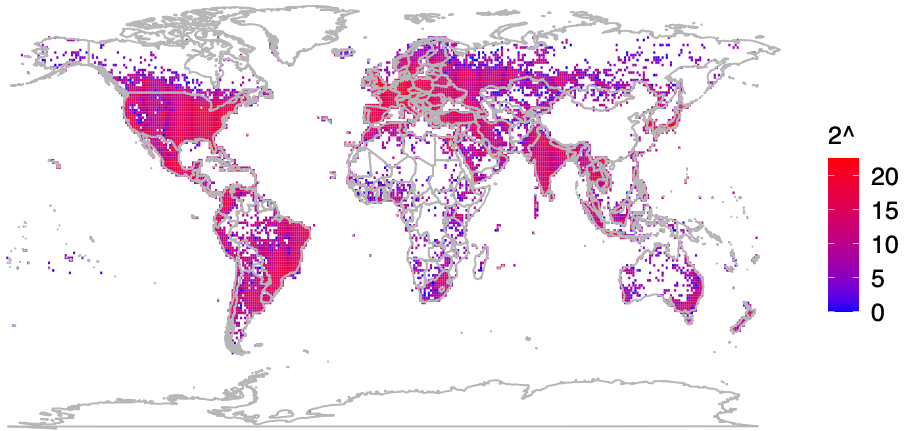
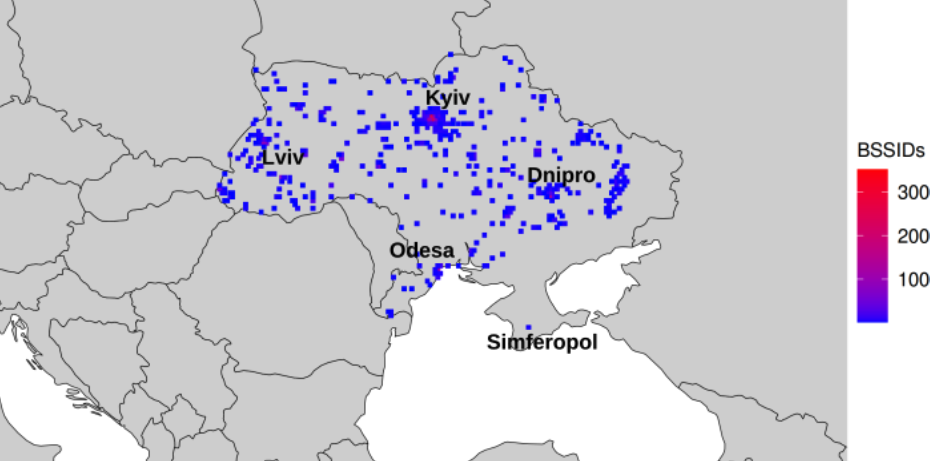
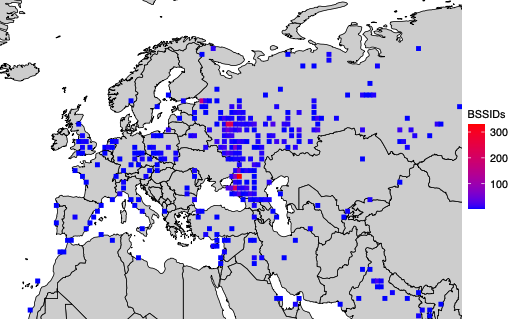
From 2015 to July 2022, 911 S5 sold access to hundreds of thousands of Microsoft Windows computers daily, as “proxies” that allowed customers to route their Internet traffic through PCs in virtually any country or city around the globe — but predominantly in the United States.
911 S5 built its proxy network mainly by offering “free” virtual private networking (VPN) services. 911’s VPN performed largely as advertised for the user — allowing them to surf the web anonymously — but it also quietly turned the user’s computer into a traffic relay for paying 911 S5 customers.
911 S5’s reliability and extremely low prices quickly made it one of the most popular services among denizens of the cybercrime underground, and the service became almost shorthand for connecting to that “last mile” of cybercrime. Namely, the ability to route one’s malicious traffic through a computer that is geographically close to the consumer whose stolen credit card is about to be used, or whose bank account is about to be emptied.
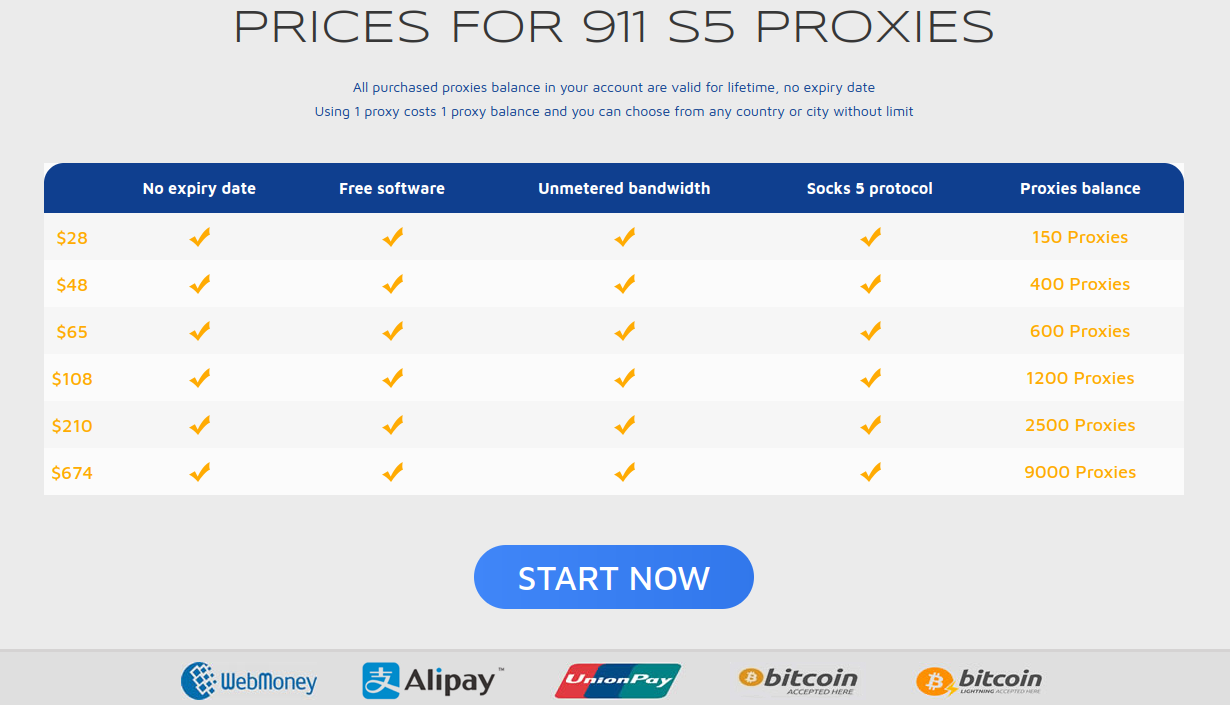
The prices page for 911 S5, circa July 2022. $28 would let users cycle through 150 proxies on this popular service.
KrebsOnSecurity first identified Mr. Wang as the proprietor of the popular service in a deep dive on 911 S5 published in July 2022. That story showed that 911 S5 had a history of paying people to install its software by secretly bundling it with other software — including fake security updates for common programs like Flash Player, and “cracked” or pirated commercial software distributed on file-sharing networks.
Ten days later, 911 S5 closed up shop, claiming it had been hacked. But experts soon tracked the reemergence of the proxy network by another name: Cloud Router.
The announcement of Wang’s arrest came less than 24 hours after the U.S. Department of the Treasury sanctioned Wang and two associates, as well as several companies the men allegedly used to launder the nearly $100 million in proceeds from 911 S5 and Cloud Router customers.
Cloud Router’s homepage now features a notice saying the domain has been seized by the U.S. government. In addition, the DOJ says it worked with authorities in Singapore, Thailand and Germany to search residences tied to the defendant, and seized approximately $30 million in assets.

The Cloud Router homepage now features a seizure notice from the FBI in multiple languages.
Those assets included a 2022 Ferrari F8 Spider S-A, a BMW i8, a BMW X7 M50d, a Rolls Royce, more than a dozen domestic and international bank accounts, over two dozen cryptocurrency wallets, several luxury wristwatches, and 21 residential or investment properties. Continue reading