Experts in the United States and Europe are tracking a marked increase in ATM skimmer scams. But let’s hope that at least some of that is the result of newbie crooks who fail as hard as the thief who tried to tamper with a Bank of America ATM earlier this week in Nashville.
Nashville police released a series of still photos (which I made into a slideshow, below) that show a man attaching a card skimming device to a local ATM, and then affixing a false panel above the PIN pad that includes a tiny video camera to record victims entering their PINs. According to Nashville NBC affiliate WSMV.com, this scammer’s scheme didn’t work as planned: The card skimmer overlay came off of the ATM in the hands of the first customer who tried to use it.
As you can see in the image montage, the first would-be victim arrives less than seven minutes after the thief installs the skimmer. The story doesn’t state this, but the customer who accidentally pulled the card skimmer off of the ATM actually drove off with the device. Interestingly, the fraudster returns a few minutes later to salvage what’s left of his kit (and perhaps his pride).
As lame as this ATM skimming attempt was, a few aspects of this crime are worth highlighting because they show up repeatedly in skimming attacks. One is that the vast majority of skimming devices are installed on Saturdays and Sundays, when the crooks know the banks will be closed for at least a day. As a result, you have a much higher chance of encountering a skimmer if you regularly use ATMs on a weekend.
Second, the thieves who install these fraud devices very often are lurking somewhere nearby — to better keep an eye on their investments. If you ever happen to discover a skimming device attached to an ATM, just remember that while walking or driving off with the thing might seem like a good idea at the time, the miscreant who put it there may be watching or following you as you depart the ATM area.
Once or twice a month I am interviewed by various news outlets about ATM skimming attacks, and I’m nearly always asked for recent figures on the incident and cost of these crimes. Those stats are hard to come by; I believe the last time the U.S. Secret Service released figures about the crime, it estimated that annual losses from ATM fraud totaled about $1 billion, but that was for 2008.
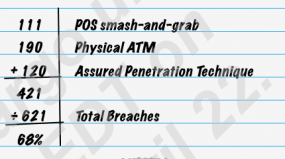
Today’s figures are almost certainly higher. On Tuesday, Verizon Enterprise Solutions released its annual data breach investigations report, a deep dive into more than 620 data breaches from the past year. Interestingly, this year’s report shows that of the Top 20 Threat Actions the company tracked across all of the breaches from 2012, physical tampering was the most frequent cause — present in more than 30 percent of all incidents detailed in the report.
“Physical tampering is our way of categorizing the installation of a skimming device, and that was the number one threat action out of everything we looked at,” said Wade Baker, managing principal of RISK intelligence at Verizon. “If you look at the last two [Verizon annual] reports, a large majority of the data set was the point-of-sale intrusions at small organizations such as retail establishments and restaurants, and those are actually a much smaller portion of our data set this time.”




![After migrating the data from Exposed.su to Exposed.re, the curator added [Swatted] notations.](https://krebsonsecurity.com/wp-content/uploads/2013/04/Fotor0417131216-600x450.jpg)