New research suggests that companies behind some of America’s best known consumer brands may be far more effective at fighting cybercrime than any efforts to enact more stringent computer security and anti-piracy laws.
Recent legislative proposals in the United States — such as the Stop Online Piracy Act — have sought to combat online trafficking in copyrighted intellectual property and counterfeit goods by granting Internet service providers and authorities broader powers to prosecute offenders, and by imposing stronger criminal penalties for such activity. But recent data collected by academic researchers suggests that brand holders already have the tools to quash much of this activity.
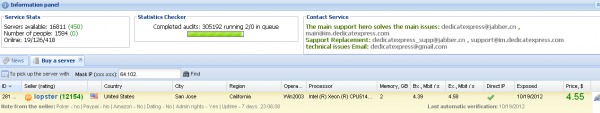
Over the past two years, a team of academic researchers made hundreds of “test buys” at Web sites from 40 different shady businesses peddling knockoff prescription drugs, counterfeit software and fake antivirus products. The researchers, from George Mason University, the International Computer Science Institute, and the University of California, San Diego, posed as buyers for these products, which tend to be promoted primarily via hacked Web sites, junk email and computer viruses.
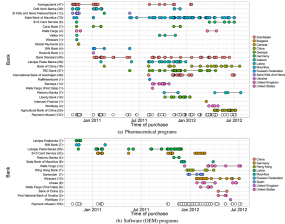
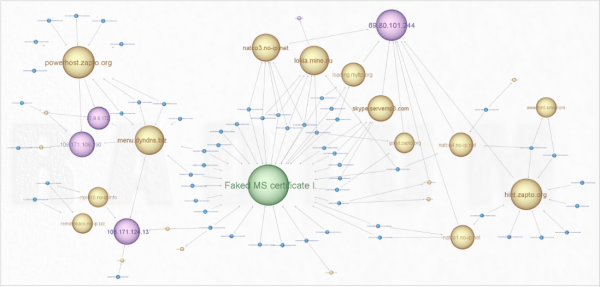
Test buys showed relationships between 40 affiliate programs and 25 banks, although a majority of the transactions filtered through a handful of banks in Azerbaijan, China, Georgia, Latvia, and Mauritius.
The test buys were intended to reveal relationships between the shadowy merchants and the banks that process credit and debit card transactions for these businesses. Following the money trail showed that a majority of the purchases were processed by just 12 banks in a handful of countries, including Azerbaijan, China, Georgia, Latvia, and Mauritius.
The researchers said they submitted the test buy results to a database run by the International AntiCounterfeiting Coalition, (IACC), a Washington, D.C.-based non-profit organization devoted to combating product counterfeiting and piracy. Several pharmacy and software vendors and IACC members whose trademarks were infringed in those transactions (the researchers said non-disclosure agreements prohibit them from naming the brands) used the data to lodge complaints with Visa (only Visa-branded debit cards were used to make the test buys).
Contracts between the banks and Visa and MasterCard stipulate that merchants are prohibiting from selling goods and services that are illegal in the country into which those goods or services are being sold. The credit card associations have a standard process for accepting complaints about such transactions, in which they warn the online merchant’s bank (including a notice of potential fines for noncompliance). After a complaint about such activity, the merchant’s bank conducts its investigation, and may choose to contest the issue if they believe it is in error. But if the bank decides not to challenge the complaint, then they will need to take action to prevent future such transactions, or else face an escalating series of fines from the card associations.
The researchers noticed that in case after case, merchant accounts that were used in fraudulent activity for some extended period of time before they filed a complaint with the IACC generally stopped being used within one month after a complaint was lodged. Neither Visa nor the IACC responded to requests for comment on this story.
Stefan Savage, a professor at UCSD’s Department of Computer Science and Engineering, said the data suggests that the private sector can have a major impact on cybercrime merely by going after the funding for these operations.
“It doesn’t require a judge, a law-enforcement officer or even much in the way of sophisticated security capabilities. If you can purchase a product, then there’s a record of it and that record points back to the merchant account getting the money,” Savage said. “Visa and MasterCard frown on sales of illegal purchases made on their networks and will act appropriately on complaints from brandholders based on undercover purchases.”
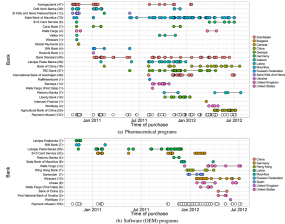
Savage said it doesn’t take concerted action by all of the affected brands to have a major impact on the rogue businesses that incentivize this type of commerce. On the contrary, he said one software brandholder pursued the merchant banks tied to all of the group’s test buys for its products with such a ferocity and swiftness that it virtually shut down the market for pirated brand name software [a.k.a “OEM”] overnight.
“This vendor went after everything. They did it so quickly — and not only for their own products — that it all but shut down the entire OEM ecosystem,” Savage said. “A couple of [OEM affiliate programs] survived by getting rid of that company’s brand, but in the beginning, when people had no clue what’s going on, it shut down the entire business for everyone.”
FINES ‘RAINING DOWN ON MERCHANTS’
The researchers note that in mid-2011, Visa made a series of changes to their operating regulations that seem designed to specifically target on-line pharmacies and sellers of counterfeit goods. First, sales of goods categorized as pharmaceutical-related were explicitly classified as “high risk” (along with gambling and various kinds of direct marketing services), and acquirers issuing new contracts for high-risk e-commerce merchants required significantly more due diligence (including $100M in equity capital and good standing in risk management programs). Also, the new documents explicitly call out examples of illegal transactions including “Unlawful sale of prescription drugs,” and “Sale of counterfeit or trademark-infringing products or services,” among others. Finally, these changes include more aggressive fine schedules for noncompliance.
Some of the best evidence of the success of the test buys+complaints strategy comes directly from the folks operating the affiliate programs that reward spammers and miscreants for promoting fake antivirus, pirated software and dodgy pill sites. In June 2012, a leader of one popular pharmacy affiliate program posted a lengthy message to gofuckbiz.com, a Russian language forum that caters to a variety of such affiliate programs. In that discussion thread, which is now some 234 pages long, the affiliate program manager explains to a number of mystified forum members why the pharmacy programs have had so much trouble maintaining reliable credit card processing. Continue reading →
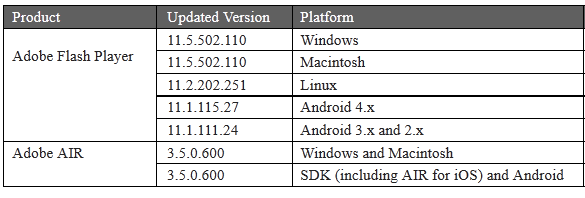
![]() Of note in these patches is a critical update for Internet Explorer 9 that fixes three flaws in IE (these bugs do not exist in older versions of IE, according to Microsoft). Other critical updates address extremely dangerous flaws in core Windows components, such as the Windows shell and Windows Kernel; these vulnerabilities are present in nearly all supported versions of Windows.
Of note in these patches is a critical update for Internet Explorer 9 that fixes three flaws in IE (these bugs do not exist in older versions of IE, according to Microsoft). Other critical updates address extremely dangerous flaws in core Windows components, such as the Windows shell and Windows Kernel; these vulnerabilities are present in nearly all supported versions of Windows.