Microsoft on Tuesday released software updates to fix 60 security vulnerabilities in its Windows operating systems and other software, including a zero-day flaw in all supported Microsoft Office versions on all flavors of Windows that’s seen active exploitation for at least two months now. On a lighter note, Microsoft is officially retiring its Internet Explorer (IE) web browser, which turns 27 years old this year.

Three of the bugs tackled this month earned Microsoft’s most dire “critical” label, meaning they can be exploited remotely by malware or miscreants to seize complete control over a vulnerable system. On top of the critical heap this month is CVE-2022-30190, a vulnerability in the Microsoft Support Diagnostics Tool (MSDT), a service built into Windows.
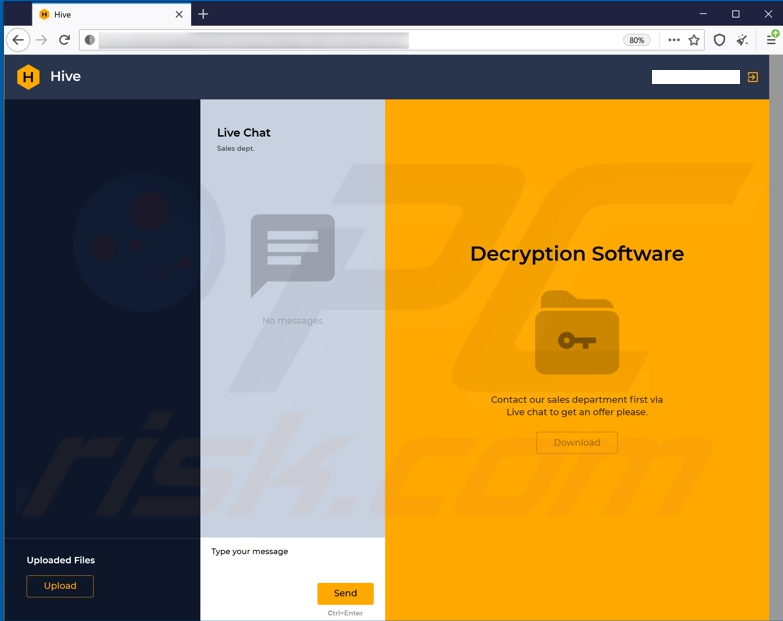
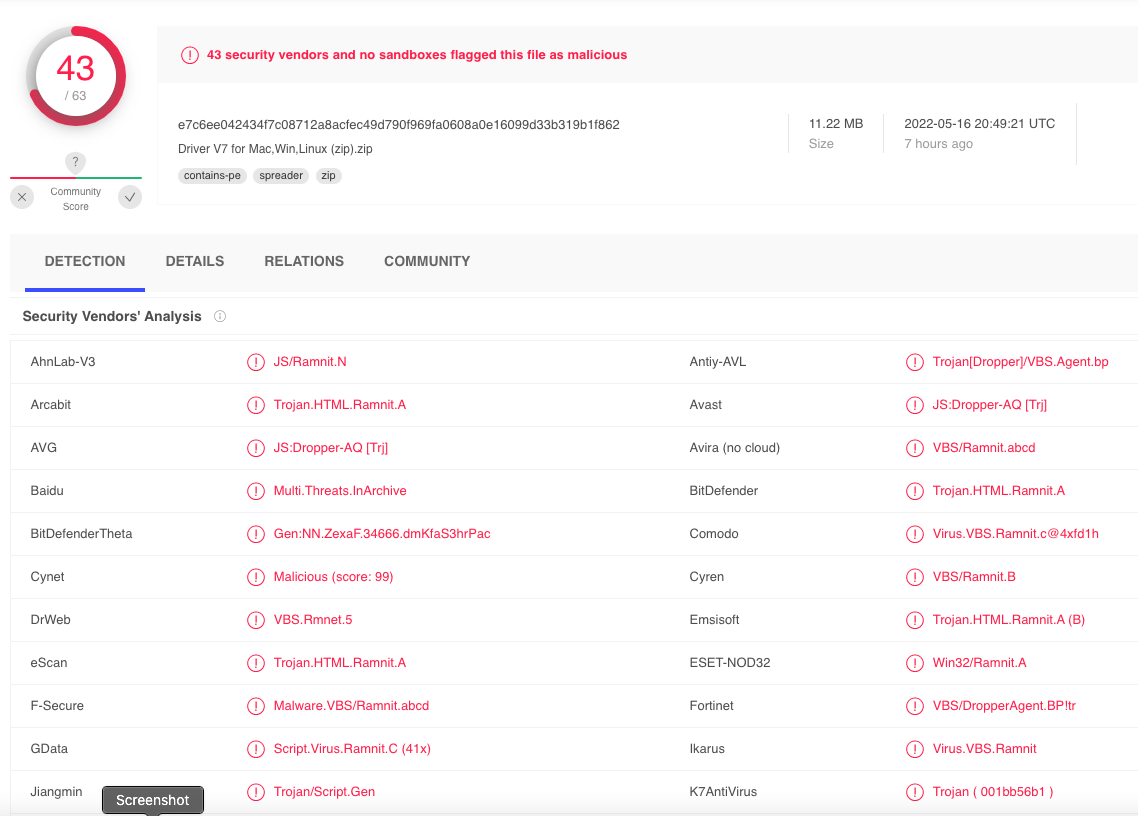
Dubbed “Follina,” the flaw became public knowledge on May 27, when a security researcher tweeted about a malicious Word document that had surprisingly low detection rates by antivirus products. Researchers soon learned that the malicious document was using a feature in Word to retrieve a HTML file from a remote server, and that HTML file in turn used MSDT to load code and execute PowerShell commands.
“What makes this new MS Word vulnerability unique is the fact that there are no macros exploited in this attack,” writes Mayuresh Dani, manager of threat research at Qualys. “Most malicious Word documents leverage the macro feature of the software to deliver their malicious payload. As a result, normal macro-based scanning methods will not work to detect Follina. All an attacker needs to do is lure a targeted user to download a Microsoft document or view an HTML file embedded with the malicious code.”
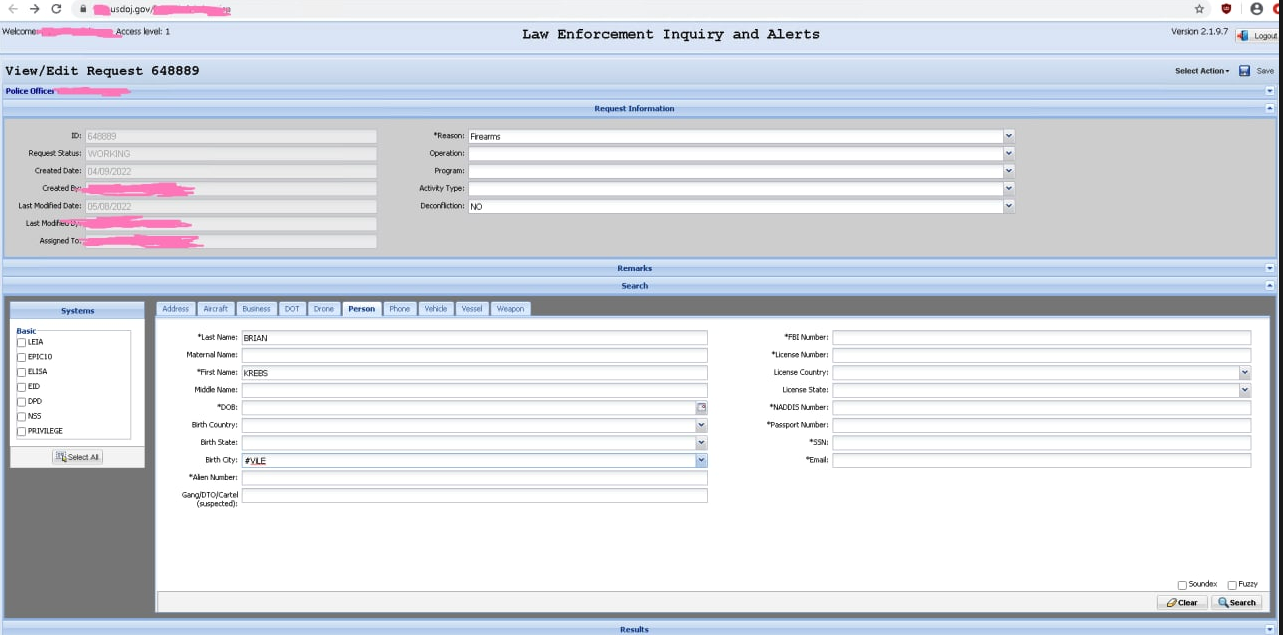
Kevin Beaumont, the researcher who gave Follina its name, penned a fairly damning account and timeline of Microsoft’s response to being alerted about the weakness. Beaumont says researchers in March 2021 told Microsoft they were able achieve the same exploit using Microsoft Teams as an example, and that Microsoft silently fixed the issue in Teams but did not patch MSDT in Windows or the attack vector in Microsoft Office.
Beaumont said other researchers on April 12, 2022 told Microsoft about active exploitation of the MSDT flaw, but Microsoft closed the ticket saying it wasn’t a security issue. Microsoft finally issued a CVE for the problem on May 30, the same day it released recommendations on how to mitigate the threat from the vulnerability.
Microsoft also is taking flak from security experts regarding a different set of flaws in its Azure cloud hosting platform. Orca Security said that back on January 4 it told Microsoft about a critical bug in Azure’s Synapse service that allowed attackers to obtain credentials to other workspaces, execute code, or leak customer credentials to data sources outside of Azure.
In an update to their research published Tuesday, Orca researchers said they were able to bypass Microsoft’s fix for the issue twice before the company put a working fix in place.
“In previous cases, vulnerabilities were fixed by the cloud providers within a few days of our disclosure to the affected vendor,” wrote Orca’s Avi Shua. “Based on our understanding of the architecture of the service, and our repeated bypasses of fixes, we think that the architecture contains underlying weaknesses that should be addressed with a more robust tenant separation mechanism. Until a better solution is implemented, we advise that all customers assess their usage of the service and refrain from storing sensitive data or keys in it.” Continue reading