The number of financial and confidential records compromised as a result of data breaches in 2010 fell dramatically compared to previous years, a decrease that cybercrime investigators attribute to a sea-change in the motives and tactics used by criminals to steal information. At the same time, organizations of all sizes are dealing with more frequent and smaller breaches than ever before, and most data thefts continue to result from security weaknesses that are relatively unsophisticated and easy to prevent.
 These are some of the conclusions drawn from Verizon‘s fourth annual Data Breach Investigations Report. The report measures data breaches based on compromised records, including the theft of Social Security numbers, intellectual property, and credit card numbers, among other things.
These are some of the conclusions drawn from Verizon‘s fourth annual Data Breach Investigations Report. The report measures data breaches based on compromised records, including the theft of Social Security numbers, intellectual property, and credit card numbers, among other things.
It’s important to note at the outset that Verizon’s report only measures loss in terms of records breached. Many businesses hit by cyber crooks last year lost hundreds of thousands of dollars apiece when thieves stole one set of records, such as their online banking credentials.
The data-rich 74-page study is based on information gleaned from Verizon and U.S. Secret Service investigations into about 800 new data compromise incidents since last year’s report (the study also includes an appendix detailing 30 cybercrime cases investigated by the Dutch National High Tech Crime Unit).
Although the report examines the data from more breaches in a single year than ever before (the total Verizon/US Secret Service dataset from all previous years included just over 900 breaches), Verizon found that the total number of breached records fell from 361 million in 2008 to 144 million in 2009 to just 4 million last year.
A good portion of the report is dedicated to positing what might be responsible for this startling decline, but its authors seem unwilling to let the security industry take any credit for it.
“An optimist may interpret these results as a sign that the security industry is WINNING! Sorry, Charlie”, the report says. “While we’d really like that to be the case, one year just isn’t enough time for such a wholesale improvement in security practices necessary to cut data loss so drastically.”
The study suggests a number of possible explanations. For example:
-There were relatively few huge data heists. Those which had been responsible for the majority of the breached records in the past few years were breaches involving tens of millions of stolen credit and debit cards. Those high profile attacks may have achieved fame and fortune for the attackers, but they also attracted a lot of unwanted attention. Many of the past megabreaches ended in the capture and arrest of those responsible, such the case of Albert Gonzales, the former Secret Service informant who was sentenced last year to 20 years in prison for his role in the theft of 130 million credit and debit card numbers from card processing giant Heartland Payment Systems. “Those that wish to stay out of jail may have changed their goals and tactics to stay under the radar,” the report notes. “This could be one of the chief reasons behind the rash of ‘mini breaches’ involving smaller organizations.”
 -Megabreaches of years past flooded criminal underground markets with so many stolen card numbers that their value plummeted. Criminals’ attention may have turned to stealing other lower profile data types, such as bank account credentials, personal information and intellectual property. In other words, criminals might opt to let the markets clear before stealing more huge quantities or selling what they already had purloined. “It’s worth noting that a lot of the cards that were stolen over the last few years in these megabreaches probably are going to start expiring soon,” said Bryan Sartin, director of investigative response at Verizon Business. “So we could be in a holding pattern right now.”
-Megabreaches of years past flooded criminal underground markets with so many stolen card numbers that their value plummeted. Criminals’ attention may have turned to stealing other lower profile data types, such as bank account credentials, personal information and intellectual property. In other words, criminals might opt to let the markets clear before stealing more huge quantities or selling what they already had purloined. “It’s worth noting that a lot of the cards that were stolen over the last few years in these megabreaches probably are going to start expiring soon,” said Bryan Sartin, director of investigative response at Verizon Business. “So we could be in a holding pattern right now.”
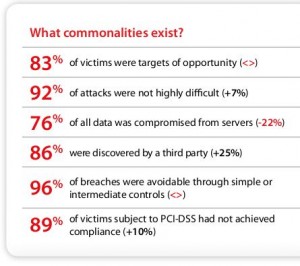
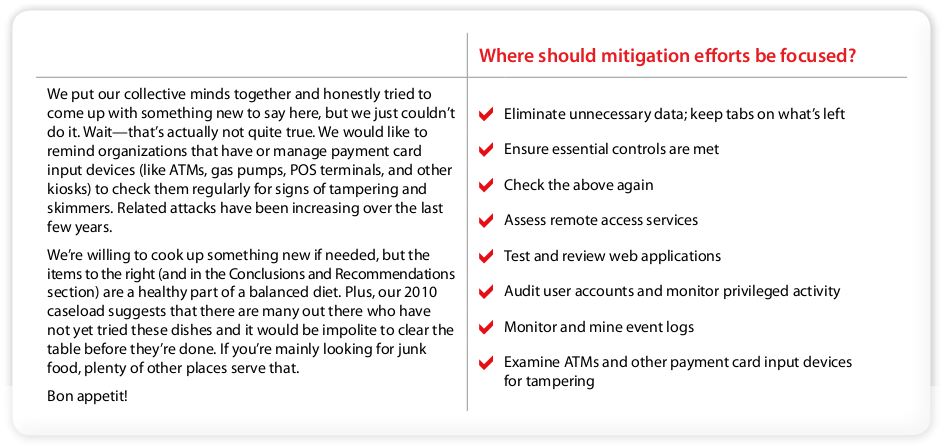
Not that thieves aren’t still interested in stealing payment card data, they’re just not doing it in megaheists. Verizon’s results show that the theft of payment card data maintains its predominance across the combined caseload, accounting for 98 percent of records breached and stolen in 78% of all breach incidents. Also, nearly one-third of all breaches examined in the report involved activities that require physical proximity; the majority of those involved ATM and gas pump credit card skimmers, or compromised point-of-sale terminals at retail establishments.
 “ATM and gas pump skimming is conducted largely by organized criminal groups and one ‘spree’ can target 50 to 100 different business locations,” the report stated. “These attacks have been occurring for years, but are on the rise in many areas according to both public reports and the caseload of the Secret Service.”
“ATM and gas pump skimming is conducted largely by organized criminal groups and one ‘spree’ can target 50 to 100 different business locations,” the report stated. “These attacks have been occurring for years, but are on the rise in many areas according to both public reports and the caseload of the Secret Service.”
If e-thieves aren’t as inclined to go after the giant data hauls, then whom are they targeting? Readers who are familiar with my coverage of the seemingly incessant online banking account takeovers targeted at small to mid-sized businesses already know the answer: Verizon’s report cites a “virtual explosion in breaches involving smaller organizations,” last year.
“It appears that cybercriminals are currently satisfied with compromising Point of Sale (POS) systems and performing account takeovers and Automated Clearing House (ACH) transaction fraud. There has been an increase in these areas in 2010. In relation to prior years, it appeared that there were more data breaches in 2010, but the compromised data decreased due to the size of the compromised company’s databases. This shows willingness in the cybercriminal underground to go after the smaller, easier targets that provide them with a smaller yet steady stream of compromised data.”
As it has done in previous reports, Verizon continues to downplay the importance of some of the biggest buzzwords driving the security market today, including “cloud security,” “mobile security” and “Advanced Persistent Threat.”
Concerning the recent media attention to security companies warning about the nascent threat from computer crooks targeting mobile devices, the report states:
“While we acknowledge the growth of mobile computing and the increasing attractiveness of the platform to potential threats, we also must acknowledge that again this year we have no representation of smartphones or tablets as the source of a data breach.”
Addressing the security problems raised by moving data “to the cloud”:
“We have yet to see a breach involving a successful attack against the hypervisor. On the other hand, we constantly see breaches involving hosted systems, outsourced management, rogue vendors and even [virtual machines] (though the attack vectors have nothing to do with it being a VM or not). It’s more about giving up control of our assets and data (and not controlling the associated risk) than any technology specific to The Cloud.”
Regarding Advanced Persistent Threats (APTs), Verizon says:
“APTs deserve some special treatment here. Some will remember that we voiced concern in the 2010 DBIR and subsequent blog posts over the APT hysteria sweeping the security community. We still believe that a ‘scope creep’ exists in the definition of APT. The term’s originators use it primarily in reference to state-sponsored attacks from the People’s Republic of China. Others use it to describe any threat possessing above average skill and determination. The logical outcome of the former is to seriously assess and seriously address security posture within government agencies and the defense industrial base (which is right and good). The logical outcome of the latter is to conclude that ‘everyone is a target’ of APT (which is an oxymoron and leads to irrational fears about the boogeyman while common thieves clean you out of house and home). It is simply not possible for everyone to be a target. It is undoubtedly true (based on investigative experience) that some are the target of state-sponsored attacks (originating from China and/or elsewhere). It is also undoubtedly true (also based on experience) that some who think they are victims of APTs are really the victims of organized criminals, hacktivists, glorified script kiddies, and their own mistakes. Because ‘APTs’ (any definition) are real, it’s time we get real about defining and defending against them.”
The Verizon report is chock full of other interesting findings. Here are a few that I found fascinating:
- 50 percent of breaches involved some type of hacking. A whopping 71 percent of attacks in the hacking category were conducted through remote access and desktop services, such as pcAnywhere and RDP. The businesses most commonly hit via insecure remote access and desktop services were in retail and hospitality industries.
- Just five distinct vulnerabilities were exploited across the 381 breaches attributed to hacking. And two of the five were flaws for which there have been patches available for more than two years.
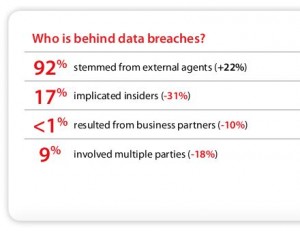
- Only17 percent of breaches last year implicated insiders. Eighty-eight percent of internal breaches involved regular employees or end users. System and network administrators stole far less information than regular employees.
A copy of the report is here (PDF). Check it out and share your thoughts in the comments section below. If you’re interested in reading last year’s report, I profiled it here.




I have a Verizon email account because I use FIOS for my broadband access. I suspect someone has been hacked into Verizon.com for the past couple of years. For the past two years, I have received multiple, daily spam messages at my Verizon address, even though I NEVER originate (send) anything from it (I use an online service for all my email.) I believe the spammers got my address at Verizon.com.
I had a situation similar to yours. Several years ago, I got a verizon email account after I installed DSL. I noticed after a short while that I was getting email from from addresses different from mine. I have no idea how they landed in my email box. Anyway I got these messages almost daily. I, too, never originated email from that account, nor did I give that email address out to anyone. So I never use my verizon account, nor do I log in to it.
My experience suggests it’s a simple dictionary attack. When we got a Verizon account, one family member chose a simple combination of letters (not a name/word) for the username. Another included a punctuation mark in the middle of the letters. The username with the punctuation mark in it gets no spam despite being used regularly; the one composed only of letters got spam almost from day one, despite rarely being used.
As far as getting email not addressed to you, that is what you will see if your address is added as a “blind carbon copy,” or BCC. Spammers using BCC can send a single email to a long list of email addresses, but the recipients can’t see the other email addresses or even their own.
It is nothing new that spammers can find your never-used Email address. They just send to every-possible-user @ yourISP . The email addresses accepted by the server are considered valid.
Another possible scenario is that Verizon email accounts are all opt-out: a marketing checkbox that was never shown to you at sign up; you have to go into account settings to find it and turn it off.
And of course, it’s also possible that there was a breach or insider that leaked Email addresses.
Another possiblility is that somone found one or two email addresses that are “broadcast” addresses – they force the email server to retransmit the email to whole blocks of configured email addresses
Tough to trend breaches, especially considering the Epsilon and Texas Comptroller breaches.
Brian,
You got a shout-out from Threatpost’s Podcast on this: http://threatpost.com/sites/default/files/digital_underground_79.mp3
The crooks, the users of stolen data, use a different metric to measure the state of WWW security–HOW MUCH MONEY THEY MADE IN 2010.
You’re absolutely right, Kevin. And I called that out pretty early on in this blog post. Still, I think some of the data is interesting, and the report itself goes beyond the number of breached records into how some of these attacks were perpetrated, which I suspect is probably of interest to a lot of readers here.
My post was lazy. But quick!
I needed to qualify it. It seems likely that ‘the take’ for 2010 is the end result of earlier infiltrations. For instance from 2009 or earlier. So it would be interesting to see if the lower number of events in 2010 leads to a lower ‘take’ in 2011.
I thought of this even while posting, so the incomplete post is a “Duh” moment.
@ Brian,
There is another explanation for the figures which is “buy back”.
That is those that take the data figure that more money is to be made selling the data back to the owner without ever releasing it.
Ian G over at Financial Cryptography did a post just recently on this,
https://financialcryptography.com/mt/archives/001310.html
Interesting post, Clive, thanks for linking to it. Yes, the financial institutions traditional have done a lot of buying back their information via third parties, though they won’t ever acknowledge that.
Clive’s link generates a message: “The site’s security certificate is not trusted!” in both IE and Chrome, although neither browser gives this message for FinancialSecurity.com’s main page. Trying to open the article from there results in the same message.
Interested minds would like to read the post and learn more, but haven’t you taught us not to open pages when we see that warning?
Sorry, I meant FinancialCryptography.
Yeah, when you get to a site like that it’s usually just someone who has self-signed their cert. Rather than accept the dodgy cert, I generally just change the URL from https to http, and it usually then lets me see the content without adding a cert that has no information in it.
@ JBV,
Agh yes the issue of certificates.
As Brian notes a lot of people have given up on many of the CA’s and gone “self sign”.
Having pulled out a lot of the root certificates for CA’s in my browsers, I see the “unknown source” message very very often and have forgoton about it for some sites, and actually check through the cert for sites I’m new to.
This is in part due to a number of “suspect” root certs getting bundeled with browsers, it is an open question as to if SSL certs actually mean anything about the sites trustworthyness or not these days, and I’ve opted to get warnings and check myself (which is not an option I’m recomending for others).
I do this because I don’t do any financial transactions or any other activites online where the validity of a certificate maters (kind of makes me a modern day Luddite 8)
So sorry for not putting a warning in with the link.
@ Brian,
OFF Topic but also might be of interest to you and quite a few of your readers.
Computer World has an article up on “Hardening”, as a technique it’s kind of gone out of fashion in recent times, however now even Microsoft are Recomending it, it might come back into fashion on a desktop near you 😉
http://m.computerworld.com/s/article/355030/Forging_a_Virtual_Steel_Wall?taxonomyId=17&pageNumber=1
Oddly it is an activity I never stopped doing because it has other advantages over and above security in some circumstances (ie light weight systems with limited resources).
The buying back of information has me gobsmacked.
First, we are talking about data. [/sarcasm] Is there some kind of DRM-protection associated with this data to prevent copying? [sarcasm/] Who’s to say that the thief and/or 3rd party will not just sit on the data for some months.
Second, how could one ever trust a so-called 3rd party? They may simply be the ‘good miscreant’ part of a ‘good miscreant, bad miscreant’ scheme, with the miscreants responsible for the data theft being the ‘bad miscreants’.
Better to acknowledge the data theft publicly, notify law enforcement, notify potentially impacted parties and make necessary improvements to prevent a repeat.
@ Rabid Howler Monkey,
Gob smacked or not buyback is part of the reality of life.
Only we normaly call it a “blackmail pay off”.
It will get dressed up as some kind of “security consultation” or some such and just end up on the balance sheet as such, knocking down some of the profit and thus tax take.
However it will cost the company a lot less than having their lack of security highlighted as many small companies don’t have the resources to “wether the storm” of “consumer choice”.
I don’t like it but like all “protection racketeering” you have to accept it exists, and thus try and deal with it rationally.
Realisticaly I expect it to become a major MO for cyber-criminals as the risk is less and the ROI on their effort greater.
The simple fact is the reason it’s possible is the executives of these companies have made a business choice based on cost, they have for whatever reason chosen to leave data in a place where external enterties can get access to it…
Let me put it another way, most companies don’t have filing cabinets of confidential information in paper documents sitting in an unmaned foyer for passers by to look at and copy at their leisure, do they?
So why should they effectivly do this with electronic records?
Brian,
Is that first graphic (who is behind the data breaches?) saying that outsiders initiated the breach but in some cases had inside help? I’m not sure how to interpret the 92%+17% sum.
Thanks,
Steve
Call me crazy and correct if I missed something but (I didn’t have time to read it in complete detail) from my skip:
1) Breaches are up
but the report only seems to focus on records compromised.
Isn’t that a bit simplistic of a metric anyways? The report doesn’t answer (and probably no one):
1) Attackers are going after small to medium sized businesses that have either under-estimated or neglected security. If so, I wonder how many businesses out there have already been breached and don’t even know.
2) They’re just tracking records but what of attacks in which records were NOT the primary target. I’ll choose the most obvious recently: RSA
At the end of the day, if I compromise 100 million records which give me access to 10 cents per record instead of compromising 1 item that gives me the keys to the castle…
As they say, it’s not necessarily about quantity but of quality.
They focus on records because it’s a report about data breaches, not intrusions in general.
Stats from phishtank.com show a significant decrease from 20009 to 2010 in the “median time to verify” a suspected phishing site.
I would think this would reduce the number of people falling for scams as browsers, such as firefox, which use their service would put up a “Suspected Web Forgery” warning page much earlier.
Here is a comparison by month since 2009 of “median time to verify” rounded to the nearest hour.
jan 2009:26 2010:12 2011:02
feb 2009:13 2010:08 2011:04
mar 2009:10 2010:05 2011:02
apr 2009:20 2010:05
may 2009:38 2010:04
jun 2009:50 2010:07
jul 2009:36 2010:05
aug 2009:29 2010:04
sep 2009:22 2010:04
oct 2009:08 2010:04
nov 2009:11 2010:03
dec 2009:09 2010:03
I think the first explanation is correct: they are keeping their heads down. We just saw a string of busts of high profile, very successful crooks. The Feds just took out many of the best in the business. The heat is on. They also successfully infiltrated carder markets. If I was an online crook, I’d feel a bit paranoid when looking for the “usual” take. I’d move to doing something else to distance my from the heat.
That skimming is the highest is totally believable. Skimming is one of the ideal online crimes because it keeps the person far from the action, especially the ring leader. It also has minimal financial investment & requires almost no technical skill. Have a few crooks install some wireless skimmers for a few minutes of exposure. They just need to be near it here and there to get the data. The leader sells the data online and picks it up directly or via proxy at Western Union. Many sales will be for multiple cards, perhaps dozens, reducing number of risky transfers to be made.
Crooks have also shifted to other types of crime that don’t necessarily involve stealing records. Compromising ACH systems is very profitable and doesn’t require selling anything except a job offer to a money mule on craigslist. 😉
Scareware is on the rise and AV systems are poorly detecting the web-based social engineering variety. There is less legal risk too. For instance, D’Souza sold scareware that claimed in an online ad that the PC was infected & did nothing when installed. Sold it to 1 million people for about $40 a pop. The punishment? His business was fined $8 million for false advertising and closed down. [(1mil * $40)-operarting_costs] – $8mil fine = enough money to buy a beach house, a Bugatti, a few franchises, and retire. I think I’m in the wrong business.