Adobe and Microsoft have each released security updates to fix critical security flaws in their software. Microsoft issued seven update bundles to fix at least 10 vulnerabilities in Windows and other software. Separately, Adobe pushed out a fix for its Flash Player and AIR software that address at least three critical vulnerabilities in these programs.
![]() A majority of the bugs quashed in Microsoft’s patch batch are critical security holes, meaning that malware or miscreants could exploit them to seize control over vulnerable systems with little or no help from users. Among the critical patches is an update for Internet Explorer versions 9 and 10 (Redmond says these flaws are not present in earlier versions of IE).
A majority of the bugs quashed in Microsoft’s patch batch are critical security holes, meaning that malware or miscreants could exploit them to seize control over vulnerable systems with little or no help from users. Among the critical patches is an update for Internet Explorer versions 9 and 10 (Redmond says these flaws are not present in earlier versions of IE).
Other critical patches address issues with the Windows kernel, Microsoft Word, and Microsoft Exchange Server. The final critical bug is a file handling vulnerability in Windows XP, Vista and 7 that Microsoft said could allow remote code execution if a user browses to a folder that contains a file or subfolder with a specially crafted name. Yikes. Updates are available through Windows Update or via Automatic Updates.
![]() Adobe shipped a Flash Player update for Windows, Mac, Linux and Android installations of the software. The appropriate new version number is listed by operating system in the chart below. Adobe says that Flash Player installed with Internet Explorer 10 for Windows 8 and Google Chrome should be updated automatically; on Windows the latest version should be 11.5.502.135, and Chrome users on Windows, Mac or Linux who have the latest version of Chrome (v. 23.0.1271.97) should have version 11.5.31.5 installed.
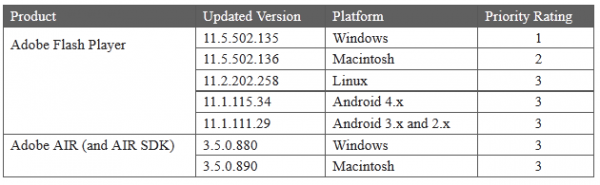
Adobe shipped a Flash Player update for Windows, Mac, Linux and Android installations of the software. The appropriate new version number is listed by operating system in the chart below. Adobe says that Flash Player installed with Internet Explorer 10 for Windows 8 and Google Chrome should be updated automatically; on Windows the latest version should be 11.5.502.135, and Chrome users on Windows, Mac or Linux who have the latest version of Chrome (v. 23.0.1271.97) should have version 11.5.31.5 installed.
Most users can find out what version of Flash they have installed by visiting this link. Adobe urges users to grab the latest updates from its Flash Player Download Center, but that option pushes junk add-ons like McAfee VirusScan. Instead, download the appropriate version for your system from Adobe’s Flash Player Distribution page.
Updates for Adobe AIR are available from this link.
If all of this updating nonsense has your head spinning, or if you are the unofficial or de facto tech support person for your friends and family, consider installing a free update management product like Secunia’s Personal Software Inspector (I prefer the 2.x version) or FileHippo’s Update Checker, either of which can make it far easier to stay on top of the latest security patches for important software.
As always, if you experience problems or issues installing any of these updates, please leave a note about in the comments below.




The following sites are also good to keep the browser up to date:
https://www.mozilla.org/en/plugincheck/
https://browserscan.rapid7.com/
I updated Flash for both IE (ActiveX) and Mozilla (plugin). Just to verify that both versions were operable, I ran one of my favorite Youtube videos under IE and Firefox. When the video was running under each browser I moved the cursor over the video and did a right click to get the About information. Both actions reported a level of 11.5.502.135. Good, installation successful. Later, just for kicks, I used https://www.mozilla.org/en/plugincheck/ to check the plugin. I got Shockwave Flash 11.5 r502, Outdated Version. Does anyone else get these results?
🙁 – i do too. you could file a bug in bugzilla.mozilla.org if you want to get involved.
I just ran Plugincheck. The problem has been corrected: STATUS: 11.5.502.135
@Old School
Yes, I get the same results checking Firefox plugins after doing the update properly; says I have the exact same old outdated version as you.
Unlike, say, Flash Player, the download page for Adobe AIR does not fully specify the dot-release. The most recent one is 3.5.0.880 from Brian’s link as indicated in the grid above. For Win7/Vista, the Programs & Features in Control Panel will tell you the installed version.
I wanted to mention that I use Google Chrome (Beta Channel version) v24.0.1312.35 as a secondary browser. It shows that it is using Pepper Flash version 11.5.31.110. Since this is higher than Adobe’s recommended version for Chrome (Stable Channel) of 11.5.31.5, it appears that this security update is already present in this version.
I have experienced no issues with installing any of Microsoft security updates on Windows XP SP3, Windows Vista 64 bit SP2, Windows 7 64 bit SP1 or Windows 8 Pro 64 bit.
Thanks.
My thanks as always to Brian for keeping us informed of important security updates. Happy Holidays everyone.
The automatic Flash update facility provided by Adobe is useless. I have seen systems which have not been updated weeks after the new version became available. The only way one can guarantee using the latest Flash is to download and install manually. Is it important or is it important?
Mr Krebs’ vigilance is most helpful. His web site is my primary source of information on software updates or security issues.
Hi Chris,
The Adobe Automatic Update worked great for me on all of my Windows systems. I actually have 8 instances of Flash Player installed across my physical and virtual machines. All updated automatically, some within a few hours and the remainder the next morning (Wednesday morning).
However, there is an exception to the rule of how Adobe’s automatic updater works. I won’t explain here since I would be repeating myself but I discuss it in full in the comments section of the following Sophos blog post:
http://nakedsecurity.sophos.com/2012/11/07/critical-flash-updates-delivered-early-be-sure-to-update-now/
My apologies for providing a link to another security website but this information should address your concerns. If I can provide any further clarification, please let me know and I will post my answers here in the comments section of Brian’s article.
I hope this helps. Thank you.
I wasn’t having much luck either Chris; until this patch Tuesday. When I logged on to the Admin account to update, I immediately got a never-before-seen Adobe alert that the new flash update was installing. Quite frankly I thought it was fake alert, so I had to return to this article to verify the version number.
Apparently THIS time the auto-updater worked. File Hippo didn’t even have a chance to scan it before it was patched! FH did have two other updates to other apps on my PC though, and after patching Windows, a Secunia PSI scan confirmed there were no other vulnerable applications present.
IE update is for IE8 also. MS doesn’t tell you that part but its there.
Plus Java has updated current version is 6update38
Hi John,
In the security bulletin MS12-077, IE 6, IE 7 and IE 8 are mentioned:
http://technet.microsoft.com/en-us/security/bulletin/MS12-077
The vulnerabilities only affect IE9 and IE 10 but IE 6 – 8 were given the update as a defense in depth measure to prevent the same flaw being exploited in future using a different method/means.
This is mentioned by Microsoft in the following blog post:
http://blogs.technet.com/b/msrc/archive/2012/12/11/it-s-that-time-of-year-for-the-december-2012-bulletin-release.aspx
It is also mentioned in the following links:
http://www.h-online.com/security/news/item/Microsoft-s-patch-package-includes-critical-Word-fix-1766834.html
http://blogs.csoonline.com/application-security/2492/microsoft-december-2012-security-update-fixes-holes-internet-explorer-word
http://blogs.csoonline.com/application-security/2482/your-december-2012-patch-tuesday-preview
I hope this helps. Thank you.
Brian, in case you missed out.
Oracle released Java RE 7update 10 and Java 6
update 38. Regards
Odd. I did all the Windows updates on Dec. 11 and was successful, but today, Dec. 20, I was prompted to install 2783534. This page http://technet.microsoft.com/en-us/security/bulletin/ms12-078 indicates it was “updated” today. I suppose that update was why I got it today.
Those are called “out of band” updates. Microsoft is not locked into the “patch Tuesday” way of doing things. I got one today too.
It is also not that uncommon to have unsuccessful updates. Sometimes one must either restore to an earlier date to do a successful install of MS updates; or uninstall previous updates and start over again, or restore from backup to get them going properly. It is all a pain in the patoot. But what are you going to do when MS continues to use us as guinea pigs for their patch process??
I’ve also had to totally re-install the operating system to get the darn things to update properly – Your Mileage May Vary(YMMV)
Hi JCitizen,
I think you are confusing the term “out of band.” An out of band patch is issued outside of the normal Patch Tuesday to fix a critical / emergency issue usually a zero day flaw in a Microsoft product that is actively being exploited or has a very strong chance of being exploited before the next patch cycle.
The patch issued yesterday is to fix a compatibility issue with a recent Kernel Mode Driver security update. Microsoft did not issue an MSRC blog post stating this was an out of band update. The updated documentation to MS12-078 also makes no mention of an out of band update; they call it a re-released update, which happens routinely many times per year (although I realize it shouldn’t happen at all). In addition, these flaws are not yet being exploited in the wild.
While Microsoft customers can be considered “guinea pigs” these updates are never released without testing. Even emergency updates for issues being actively exploited go through some validation before release. They will never intentionally release an update to potentially 1 billion customers that will cause an issue for them, however humans aren’t perfect and they do make mistakes. Kudos to Microsoft to resolving this issue so fast and before the Holidays.
Thanks and Happy Holidays.
Thanks JimboC for the correction on my semantics. I still call them all “out of band’ just out of (bad) habit. 🙂
Oh! And Merry Christmas to you all too!
Samsung told me there was no way to install the latest version of Flash Player 11 for Windows 8…Can’t believe there is no way not to download such required download?
Does anyone have a fix for that? I can’t play any games due to this problem????
Thanks & Happy 2013!
With Internet Explorer 10 you may not need flash anyway. I keep reading that almost 85% or more of the internet has switched to HTML-5, so using flash is redundant.
Maybe someone else can interject here!
Hi KaKa,
JCitizen is right. Most sites now work without Flash Player by using HTML 5.
Windows 8 already includes Flash Player 11.3 (11.3.377.15) for IE 10 (both the desktop and Modern UI versions). This version is updated by Microsoft on as necessary basis. Such updates are announced in the following security advisory:
http://technet.microsoft.com/en-us/security/advisory/2755801
You cannot install the ActiveX version of Flash Player for IE on Windows 8 since it isn’t necessary and is integrated as mentioned above.
I realize this is the not the latest version i.e. 11.5 but it should still serve most of your purposes.
For the list of changes introduced by 11.4 and 11.5 (respectively), please see the following links:
http://helpx.adobe.com/flash-player/release-note/fp_114_air_34_release_notes.html
http://forums.adobe.com/message/4913847#4913847
I have installed Firefox 17.0.1 on Windows 8 64 bit and then installed Flash Player 11.5.502.135 (the plugin version) and it worked fine for me (you could also use Google Chrome for this). I obtained the Flash Player for Firefox from the Flash Player Distribution page linked to by Brian above.
If you wish to view YouTube videos using Flash you will first need to opt-out of the YouTube HTML 5 trial using the following link:
http://www.youtube.com/html5
Then visit the video you were trying to view and Flash should play it.
I hope this information is of assistance to you. Thank you.
Thanks JimboC:
I was hoping someone would come to his(or my) rescue! 🙂
You are both very welcome.
On my Macs, I allowed the Flash auto-updater mechanism to update the system a couple of times, and it seemed to work. Then the last time it told me it had an update, I had a closer look.
I can’t speak for the Windows experience, but think about what you see on a Mac: You’re browsing, and a new window pops up telling you a Flash update is available – click here to continue. You click, something happens in the background, and then another window appears (the installer), again asking you to click to continue. The installer runs, and your system is updated,
At a high level, how is this different from any of a thousand attacks that induce people to install malware on their system? Just because a window *looks* as if it came from Adobe, doesn’t mean it actually *did* come from Adobe. The first level window would be trivial to spoof. The second is a bit trickier, if you’re observant because it runs a separate program (the installer) whose icon you can see. But that can probably be faked, too.
On the one hand, the auto-update mechanism fixes the problem of people not updating Flash as vulnerability after vulnerability appears. But on the other, it’s teaching people to accept modifications to their system based on a simple window popup in their browser. Once malware writers realize this, we’ll certainly see it used as an installation mechanism.
Ironically, Chrome’s completely interaction-free update mechanism is immune to this kind of attack, as it provides nothing at the UI level that an attacker could simulate.
Personally, I’ve decide to use the updater as a notification mechanism and have gone back to the old-style “download from Adobe” technique to do the actual installation.
— Jerry
Very good point Jerry;
For me on Vista x64, the updater has been silent. I run as a limited user all the time, so once in a while the updater won’t work until I sign in as administrator. I’m not sure why this is not seamless every time; but at least it updates very rapidly soon after logon. Sometimes it takes long enough File Hippo will alert to the need to update; but after a minute or less, a re-scan has that flash alert disappearing.
All I can say is when various apps pop up for updating, it pays to stop and look, and be critical of the appearance of the popup. Most of the time fake alerts always give themselves away because the spelling, install certificate, or appearance is all wrong. Also a good HIPs will do a better job of telling the true identity of the process underway. Of course Macs may not have any 3rd party HIPS at all. I’m not familiar with what is available for Macs.