A security breach at a Web portal for the U.S. Department of Homeland Security has exposed private documents and some financial information belonging to at least 114 organizations that bid on a contract at the agency last year.
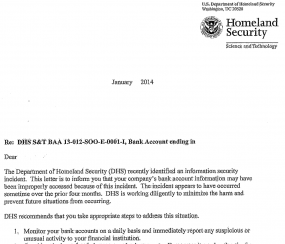 “This letter is to inform you that your company’s bank account information may have been improperly accessed because of this incident,” reads a letter sent to affected organizations earlier this month by DHS privacy officer Christopher Lee. “The incident appears to have occurred sometime over the prior four months.”
“This letter is to inform you that your company’s bank account information may have been improperly accessed because of this incident,” reads a letter sent to affected organizations earlier this month by DHS privacy officer Christopher Lee. “The incident appears to have occurred sometime over the prior four months.”
The letter was sent to organizations that bid on a 2013 contract to help DHS’s Science & Technology division develop new communications technologies for first responders. According to DHS, the documents were downloaded from a department Web portal by unauthorized persons outside of the agency, although it hasn’t yet determined the cause or source of that access.
A spokesperson for DHS said that as a result of this unauthorized access, 520 documents including white papers/proposals, decision notification letters, documents regarding contract and award deliverables and other supporting materials were improperly accessed. That person said that of the approximately 114 organizations that were potentially impacted, only 16 had bank information in potentially accessed documents, and all were promptly notified by S&T. Additionally all affected companies are being provided a list of their accessed documents for their specific determination of business sensitivities and impacts, DHS notes.
The portal in question is run by Herndon, Va. based REI Systems Inc. The company declined to comment for this story, so it remains unclear whether the unauthorized access at REI Systems was limited to the DHS data, or if it affected other REI government projects. According to this page at REI’s Web site, the firm provides similar technology services to the Department of Health and Human Services, the Department of Justice, the General Services Administration, the Internal Revenue Service, NASA, and the Federal Aviation Administration, among others.




Here it is
The documents were downloaded from a department Web portal by unauthorized persons outside of the agency, although it hasn’t yet determined the cause our source of that access.
end of story .
eh, you never know. Watergate started with a burglary.
Last Sentence, third paragraph:
“determined the cause our source of that access”
I believe that should be “cause or source”.
Regards,
dtb
The best part:
“The incident appears to have occurred sometime over the prior four months.”
“all were promptly notified”
Since when does “promptly” mean “four months later”? Perhaps they should have said ‘No later than fours months after your bank account was emptied.”
And the scary part is these yahoos keep the entire country’s population’s personal info. In multiple places. All with the same safe, secure level of access. I feel safer already.
The breach occurred within the past four months. As soon as the breach was discovered, they promptly notified the affected parties.
Not sure how that is confusing.
They should rename themselves “Department of Homeland”, and just remove the “Security” portion altogether.
Perhaps the “Department of Redundancy Department” would be even more apt.
Indeed.
truly funny. maybe they should call the nsa or google. i am sure they must have every possible piece of evidence . . . to find the culprits. what does DHS really do?
These are the same people (Homeland) who take all of your most personal details in order to join the program to bypass security lines at the airport.
How comfortable does that make you feel?
It would be helpful and probably instructive to know how this, and other sich thefts, were discovered. Web server log? Other log? Something totally different? I’d ask the same about the Target and Neiman-Marcus thefts.
Four months from compromise to detection is par for the course according Verizon’s 2013 DBIR (66% of breaches took months or more to detect). Not sure why we would expect that DHS would be any different at detecting a breach than anyone else.
I think it looks worse on an organization who’s supposed to be in the business of security, myself.
If you consider the qualifications of the people Obama has selected for his administration, competence isn’t on the list.
Fair to ask – why kind of idiot leaves such info on a web portal? If anyone should know better you would think it would be the bunch at Homeland Security…
Maybe the same kind that spells ‘what’ as ‘why’?
I wouldn’t trust any of the alphabet agencies after the Snowden Leaks, and now the D.H.S. is reporting a breach of private documents and some financial information. WTF I think the “gumshoe” needs to look into this some more
Couldn’t happen to a nicer bunch of people: i.e. the predators who would contract to aid and abet DHS, the second-biggest predator in the world (next to the Pentagon).
Just another example of poor data management. Consumers (and businesses) are required to endure various machinations (username/password/MFA/tokens, etc.) while their data is flying in the wind due to unprepared hosts of their data.
Pardon my ignorance, but whenever I envision “tight security”, the government is the first entity that comes to mind. I expect retailers to suffer data breaches, but when it happens to a government agency, I’m always shocked. Not too sure where folks are missing the mark, but if there is a need for an expanded security budget, then increase it, by all means.
Let’s see. Healthcare.gov was a catastrophe. Now we learn the government agencies with the most information about us and our enemies are also compromised. Funny how the Obama administration expertly uses systems to beg his supporters for donations but I haven’t heard they have had any problems.